Latest I.T News and Insights
We believe that sharing knowledge results in better outcomes for us and our customers.
Book a Consultation
The top small business cyber security threats
By Lanrex on 10/11/22 12:18 PM
It’s challenging to be across the ever-evolving cyber security landscape when you’re a small business with time and resource constraints. This makes it even more challenging to get clear on what kinds of measures and systems you need to have in place to help minimise potential cyber security threats.
Even so, making sure you have a cyber security plan in place is one of the best ways to help protect your team, customers and your business. Luckily, having an awareness of the importance of cyber security measures is the first step toward better understanding the cyber security landscape.
4 cyber security risks to manage
Let’s uncover the cyber threats your small business needs to have awareness of, to help you stay informed as well as gain a better understanding of what you can do to safeguard your business.
1. Phishing scams
Have you ever heard about someone receiving an email or text that they thought was legitimate but was actually from a person pretending to be someone they knew? This is a phishing scam, and is one of the most frequent types of cyber security threats. Phishing scams are popular with cyber criminals, as it’s easier to trick someone into clicking on a malicious link than it is to break through a computer’s defences. Luckily, they are also straightforward to prevent.
What you can do to protect against phishing scams:
- If you think a message or text might be from a trusted organisation (such as your bank or a supplier), use an official contact method you can trust.
- Search for the official website or phone number. Don’t use links or contact details in the message you have been sent in case they are fraudulent.
- Ensure your staff is aware of this cyber security threat, so they can identify and prevent phishing attempts.
2. Ransomwear infections
Ransomware is malicious software that prevents access to computer systems or files unless a sum of money (a ransom) is paid. It basically turns the power of encryption (designed to protect your files) against you by taking your files hostage. This means you might get locked out of important documents, spreadsheets, photos and videos, and other sensitive files. Plus, an infected PC can spread the ransomware to other devices on your network.
What you can do to protect against ransomwear:
- Frequently backup sensitive and important data.
- Turn on automatic updates for your operating systems, software and apps.
- Use multi-factor authentication when you can.
- Secure devices (including servers) and any internet-exposed services on your network.
3. Personal laptops, tablets and smartphones
If your team uses personal devices like laptops, tablets, and smartphones to access company information and applications, it’s important to have protections in place. While it’s convenient, this influx of personal devices brings an increased risk of viruses, hacks, and data leaks. In fact, each device that can access company information is an additional endpoint that cyber criminals can try to breach.
What you can do to protect personal devices:
- Control access privileges to company data.
- Delete company data and remove access from a device when a staff member leaves.
- Invest in endpoint and mobile protection.
4. Sensitive information
Data and the devices that data is on, is now constantly in motion and on the move. Laptops can be stolen, tablets get lost, and phones are sometimes left in taxis and planes. Whenever those items go missing, the business data on them is at risk – whether it be confidential business data or customer information.
What you can do to protect your sensitive data
- Put in place access controls for digital files and folders.
- Make sure passwords are not shared between team members.
- Remove access, delete accounts and/or change passwords when an employee exits the company, or if you change providers.
Better protect your business from cyber security breaches
When you’re busy taking care of business, handling IT needs for a small business can fall by the wayside amid all the other responsibilities. Fortunately, there are comprehensive cyber security solutions available that, once implemented, can help to reduce the likelihood and impact of some of these common cyber security threats.
When you’ve got your security handled, you’ll have additional time to focus on growth, innovation, and to find more ways of creating value for your clients.
Ready to get your cyber security handled?
Ready to find out if your small business has the required measures in place to manage the current cyber security landscape? Register today for a complimentary cyber security audit and let’s get started. Together we will review your IT infrastructure, access any key threats or vulnerabilities, and recommend implementing strategies and solutions that can significantly reduce your risk of compromise.
Lanrex Named a Finalist for the 2022 ARN Innovation Awards
By Lanrex on 8/09/22 5:40 PM
Lanrex, a leader in I.T and managed services for over 35 years, is proud to have been named a finalist for the 2022 ARN Innovation Awards, an award which celebrates innovation and excellence across the technology sector in Australia.
It is a distinct honour to be a finalist out of more than 480 nominees that were considered for the award, and we are excited to see how far our cutting-edge I.T solutions can take us in the coming years.
Lanrex has always been an organisation that is committed to delivering technology solutions with a difference. We strive to be at the forefront of innovation and offer our clients the very best in I.T managed services.
This award is recognition of our commitment to delivering innovative solutions that make a difference to our clients' businesses.
We would like to take this opportunity to thank our employees who have made our success possible by working tirelessly to deliver the high level of service our clients have come to expect from us. We would also like to thank our clients for their unwavering support. We could not have been nominated for this prestigious award without you all.
We are looking forward to the ARN Innovation Awards ceremony and we hope to bring home the award.
Thank you for your support, and congratulations to all the finalists!
Image by ARN via www.arnnet.com.au
How Your Team Can Work from Home Seamlessly
By Lanrex on 17/08/22 4:54 PM
Businesses are experiencing profound changes as employees’ transition to hybrid work environments following COVID-19. Hybrid work environments are about adapting to how teams work best and creating experiences that reach everyone. The future of work will centre around how people connect with secure, smart technology.
In response to the pandemic, cloud-based and AI-powered networking technologies are the driving force behind business recovery plans as they begin to take shape.
According to a global survey of 2,400 IT decision-makers (ITDMs) commissioned by Aruba, a Hewlett Packard Enterprise company, Network as a Service Adoption is set to accelerate by 38% within the next two years as businesses adapt to COVID-19.
To learn more about how Aruba is helping to architect the Hybrid Workplace, watch this video now.
Whatever type or size of business you run, Lanrex are confident that you will benefit from our expertise. Learn more.
Ransomware attacks – 5 strategies to safeguard your business
By Lanrex on 17/08/22 4:53 PM
Australian businesses must fight back against the rising sophistication and frequency of cyber threats such as ransomware.
The prospect of a ransomware attack strikes fear into the hearts of many business owners – with good reason.
For 2020-21, the Australian Cyber Security Centre (ACSC) reported that it had received more than 500 ransomware cybercrime reports, a rise of 15 per cent. Such attacks involve criminals hacking into a business’s computer systems and locking up devices, files and data until a ransom is paid. In what is being called “double distortion”, the fraudsters are increasingly also threatening to release sensitive data or information about businesses to the world.
Just this year, at least seven Australian businesses were reportedly hit by the same ransomware, known as REvil, that shut down operations at meatworks company JBS Foods. Many more attacks go unreported, highlighting the importance of taking the following measures to protect your business.
1. Stay alert to possible attacks
Ransomware and malware attacks often occur because of simple errors within businesses, including employees clicking on unexpected attachments in phishing emails and operating unpatched systems. So, the imperative is for staff to receive basic training about cyber threats and to be cautious when dealing with external parties. Part of that education should be around better knowledge of email and mobile platforms that could be exposed to cybersecurity threats, while conducting regular reviews of data systems is a must.
2. Ensure you have backups of key technologies and data
The key bargaining tool for ransomware attackers is seizing control of a business’s critical technology and then trying to extort the operation for its return. However, if a business has independent or off-site backups of files and data, it minimises the threat from the fraudsters and gives the business more options in the event of an attack.
3. Insist on multi-factor authentication
A smart way to increase business resilience and reduce the threat of phishing and malware is using multi-factor (MFA) or two-factor (2FA) authentication. This means your business requires additional information on top of a username or password to grant access to systems such as Office 365 and Google app administrator accounts, as well as virtual private networks and remote desktops. Fingerprints and codes sent through text messages are common additional forms of ID.
4. Have a plan in the event of an attack
Taking a head-in-the-sand approach to ransomware attacks is fraught with danger. In addition to backing up data, business owners and managers should have a blueprint if the worst happens and fraudsters do target their business. One obvious question that needs answering is whether you should pay a ransom or not. The ACSC advises against paying a ransom because it does not guarantee that a victim’s files will be restored, and it does not prevent the release of any stolen data. However, the circumstances for each business may be different and a well-considered response is essential.
5. Get an independent assessment of your risk exposure
Last, but not least, think seriously about getting an independent technology expert to identify any network weaknesses in your business. Smaller firms, in particular, may not have access to internal technology expertise, and external consultants are more likely to be up to speed with the latest ransomware and cybersecurity threats. Given that British IT security company Sophos has revealed that the global average cost to fix a ransomware attack is about US$761,106, getting expert help is likely to be money well spent.
Ransomware attacks are one of the biggest threats for business owners and managers. So contact us today to get advice on how to protect your operations from cyber threats.
Core Tech and Lanrex Merger Announcement
By Lanrex on 5/07/22 4:05 PM
As some of you may not be aware, Core Technology Partners has officially merged with Lanrex. Moving forward, we will be offering I.T managed services under the brand name “Lanrex”, dropping the name “Core Technology Partners” altogether. However, you can still expect the high quality of managed services that Core TP is known for.
The merger was successfully completed on 22nd April 2022.
Lanrex is a managed services provider founded in 1987. They have been a leader in I.T and Managed Services for thirty-five years.
The merger brings together over 30 years of combined industry experience, as well as strategic vendor alliances, strengthened service offerings, and enhanced project services capabilities.
Most importantly, the merger means that our leadership capabilities will also be improved, allowing us to come up with even better solutions to address the constantly evolving I.T challenges faced by SMBs.
We are excited for this step forward in executing our vision for growth as outlined in our V/TO (Vision, Traction Organiser). Initially, members of the current Leadership Teams will form the new leadership team. We have come together and created a combined V/TO (Vision, Traction Organiser) - with a single unified set of values.
Both organisations have relocated into new corporate headquarters, located at Suite 1.03, Level 1, Talavera Corporate Centre, Building C, 12-24 Talavera Road, Macquarie Park, NSW, 2113.
How to Create a Security Policy for Your SMB
By Lanrex on 25/06/22 4:43 PM
IT security policies are the foundation of an organisation’s overall security program. They exist to educate employees and guide behaviour, in addition to protecting the business and adhering to compliance regulation.
Without a proper security policy in place, you’re putting your company’s physical and digital assets at risk of various threats. This is one of the reasons why many successful SMBs have developed and implemented comprehensive IT security policies. To add to that, most successful SMBs go out of their way to regularly update their policies to make sure that they can still combat evolving cybersecurity threats.
If you still don’t have an IT security policy in place for your organisation, follow these best practices for developing one with your IT service provider.
1. Identify Roles and Responsibilities
First, figure out who currently has access to critical data, infrastructure, and applications. Note your findings and then assess whether or not each person needs the access they’ve been granted. Then, you can begin to limit or reinstate permission to access sensitive information and assets. For example, system administrators should have access to things that contractors should not. You want to make sure there will be no uncertainty about who has access to what.
2. Define Data Retention Parameters
You’ll also need to implement a document retention policy. These types of policies are especially important in certain regulated industries that require specific retention parameters. Defining a data retention policy is critical because there’s an increased risk of data being stolen or compromised when it’s kept beyond those defined dates.
3. Verify Robust Encryption Technology Is Being Utilised
Setting standards for encoding your information is another important part of a security policy. Implement high grade encryption technology to secure data stored in the cloud, and use SSL (Secure Sockets Layer) encryption technology for data in transit.
To make your security policy even stronger, ask your IT service provider to look for a data protection solution that uses private key encryption (PKE) technology.
4. Involve Staff in Policy Creation
Try to involve your staff in policy development, including those outside of IT. Making the process more collaborative and transparent for everyone has its advantages. For example, when staff are made to feel they are part of the policy creation process, they are more inclined to understand, accept, and follow the guidelines that are put in place. Furthermore, they can provide helpful insights on what’s needed to improve security within the organisation.
5. Adhere to Compliance Regulations
When developing a security policy, be sure to meet your industry’s compliance regulations. Certain industries are more regulated than others, but you should always stay informed about any pertinent regulations and make sure your security policy addresses all issues necessary to help your SMB stay compliant.
ATO, the Australian Tax Office for example, has five record keeping rules about what records you must keep and for how long. An IT service provider can help you determine what backup and storage options best suit your business to fulfil this obligation, especially in case of any system failures.
6. Set Clear Penalties for Non-Compliance
Cyber security is not a joke. A single instance of non-compliance can put your whole business at risk. Be sure to set and communicate clear penalties for any staff member who doesn’t comply with the security policy. These could be anything from formal warnings to dismissal, depending on the severity of the offence. By having a set process for dealing with non-compliance, you can ensure that everyone takes the policy seriously and that there are consequences for not following it.
Developing a Strong Cyber Security Policy with Lanrex
With cyber crime becoming an increasingly serious threat, it’s not a question of if businesses need security, it’s a question of what level of security they need. Keeping this in mind, you should reach out to your IT service provider about data security to make sure your business is properly protected.
It’s also important to start educating your employees about the importance of cyber security as soon as possible because new cyber threats emerge every day. Be proactive and start talking about it now instead of waiting until after your company experiences a severe data breach or malware infection. Don’t wait until it’s too late. Contact us to explore Lanrex’s cyber security solutions today.
Congratulations Jodie Korber, Managing Director at Lanrex on becoming a finalist at ARN Women in ICT Awards
By Lanrex on 15/06/21 8:30 AM
ARN is proud to announce the finalists of the new-look Women in ICT Awards (WIICTA), housing a record-breaking number of submissions in what will be the largest celebration of female excellence within the technology channel across Australia.
Representing the entire Australian ecosystem, 205 finalists (185 individuals and 20 companies) make the shortlist from a pool of 120 organisations and more than 340 nominations, spanning partner, telco, vendor and distributor businesses.
“ARN congratulates Jodie Korber, Managing Director at Lanrex on becoming a finalist in the Innovation category for the Lanrex 4 Stage Essentials,” said Cherry Yumul, vice president of Strategic Partnerships and Innovation at IDG. “We applaud your standout contribution in helping to set an industry benchmark for female achievement across Australia.
“This year WIICTA has generated a volume and calibre of nominees never been seen nor conceivable before. This is an encouraging sign of a positive trend that gender diversity is high on the corporate agenda of more and more businesses in Australia.
“Not to tick a box or meet a quota but evidently to bring in alternative viewpoints for problem-solving and different leadership styles for competitive advantage, in turn delivering better returns.”
Reflective of a diverse technology network, candidates range from large-scale consultancy giants and global system integrators (GSIs) to emerging start-ups in Perth, Melbourne and Sydney, alongside leading managed service providers, born-in-the-cloud players, specialist solution consultants and boutique digital agencies.
Within this standout group of finalists, female leaders are located across the entire country spanning multiple states and territories, including New South Wales, Victoria, Queensland, Western Australia, Tasmania and the Australian Capital Territory.
All career stages are in the spotlight from graduate-level entrants to well-established CEOs, in addition to inspiring entrepreneurs, creative thinkers and technical experts, as well as talent rising through the ranks and consistent high-performing individuals. This is also supported by both individual and company champions of D&I initiatives.
Collectively, WIICTA in 2021 stands tall as the leading forum for setting the industry benchmark for female achievement across Australia.
Shaped by the feedback of more than 50 leading female technology executives, WIICTA – now in its 10th year of running – will honour the channel across eight categories, spanning Innovation, Technical, Entrepreneur, Graduate, Rising Star, Shining Star, Achievement and D&I Champion (Company and Individual) awards.
The winners will now be selected by an executive panel of more than 150 industry judges – acknowledging creativity, innovation and excellence – before being announced at a celebration lunch at Hyatt Regency Sydney on Friday 23 July.
Additional information:
ARN article: https://www.arnnet.com.au/article/688980/arn-unveils-record-breaking-number-finalists-new-look-women-ict-awards/
Women in ICT Awards website: https://www.arnnet.com.au/wiicta/
4 Tips For Teaching Employees About Ransomware
By Lanrex on 18/11/20 7:45 AM
Ransomware is now considered a fact of life in today’s cyber security landscape, but that doesn’t mean SMBs are protecting themselves from a potential ransomware attack or even know it’s a possibility. Often, users only recognise a ransomware threat after it’s too late. In February 2018, according to Osterman Research and Barracuda there was one phishing attempt in every 3,331 emails and one piece of malware for every 645 emails. And falling for one of these emails can be costly.
According to IBM’s Data Breach Report 2021, the average cost of a ransomware attack is $4.62 million (up from $4.44 million in 2020), and the average breach lifecycle is 287 days (up from 280 days in 2020). This means that not only are ransomware attacks becoming more expensive, they’re also taking longer to resolve.
SMBs need to start protecting themselves from the growing threat of ransomware. Becoming educated about the threat of ransomware and learning these important tips is an important first step.
1. Put Technical Safeguards in Place
As a best practice, have an intrusion-prevention system and security software running on your computers. This should include antivirus software, firewalls, and spam filters. Then, make sure all security patches are up to date, and deploy new patches on a regular basis.
It’s also critical to have a backup solution in place and frequently test the backups running on your systems to make sure they’re working properly. If you’re hit with ransomware, you’ll want to restore operations as quickly as possible, and having a recent backup to recover from will save you both time and money.
2. Ransomware Training
Even with technical safeguards in place, it’s employees who are ultimately at risk of exposing a business to ransomware. User error, such as clicking on an infected online advertisement, pop-up window, or attachment in a spam email, is often to blame for inviting ransomware into a computer. Therefore, educating your employees and system users is the most important line of defence.
Talk with your employees about ransomware and educate them on what it is and how they can help defend the business. Try getting the whole staff together for a training session and bring lunch to make it a Lunch-and-Learn event.
As a best practice, you should require all new employees to complete the training and offer it on an ongoing basis to avoid information being missed. If you don’t have the resources to put this type of training together, talk to your IT service provider. They should be able to run a program like this for you or provide other educational materials.
3. Provide Examples to End Users
The most effective way to educate your employees on ransomware is to show them examples of what it looks like, so they’ll know the warning signs and be able to identify a suspicious message or attachment before they click on anything. For example, you can share with them a Phishing Quiz, which includes examples of infected and legitimate emails and provides explanations of how to tell the difference.
Once ransomware has infected a computer, a message is displayed on the screen letting the user know their machine has been compromised.
It’s helpful to share this type of information with employees as well so that, even if it’s too late, they’ll know to alert management and ask for help.
4. Encourage & Respond to Feedback
Oftentimes, employees will find less secure workarounds to accomplish their tasks because the company’s systems are too restrictive. Maybe they feel they can get their work done faster if they bypass the company firewall to access a website that’s been blocked or download an application that isn’t allowed. Or maybe they’ll save sensitive files to a personal USB drive because they can’t access them from home or on their mobile device.
Encourage your employees to come to bring these types of concerns to your attention so that you can work together to find solutions that will meet their needs without compromising security. In order for your employees to feel comfortable coming to you with questions or concerns, you need to set up an open-door policy and foster an environment where feedback is always welcome.
How Lanrex Can Help
Lanrex connects businesses with the right technology to ensure they can safely navigate the changing landscape. Lanrex’s three cyber security packages provide all the basic protection plus the option to choose additional security features that give them the right fit for their cyber security needs.
Contact us to explore Lanrex’s cyber security solutions today.
4 Common Cyber Security Mistakes To Avoid
By Lanrex on 10/11/20 9:57 AM
With massive data breaches making headlines on a regular basis, it’s hard to ignore the fact that data security is becoming increasingly important. Unfortunately, there are still far too many SMBs that don’t understand just how serious the threat is—and that can be dangerous.
The IT Security Threat to SMBs
Recent research demonstrates that the growing cyber security threat isn’t a trend that only affects big, national companies. It’s just as serious—if not more damaging—for small businesses to not be prepared, because data breaches and cyber attacks are real possibilities for them.
According to Ponemon Institute’s 2017 State of Cybersecurity, cyber attacks affected 61 percent of SMBs in the past 12 months, and the number of data breaches reported each year continues to climb.
If that’s not alarming enough, on average, these companies lost more than 9,350 individual records as the result of a breach.
Educating Yourself and Your Employees
Knowing what you’re up against is half the battle. If you own a small- to medium-sized business, you need to learn and be aware of current cyber threats, so you can fully protect your organisation. It’s also crucial to share relevant cyber security information with your employees, so they understand their part in helping keep the company safe.
Security is all about protecting data and preventing data loss, which used to only mean protecting your data from natural disasters and general user error. But now cyber security is an even bigger threat to companies than ever before, and you need to make sure you’re adequately prepared to deal with it, if it does happen.
The preventive steps you take can mean all the difference to the survival of your organisation.
Common Cyber Security Mistakes
Bad habits are hard to break, and that’s especially true when it comes to small businesses and cyber security. After all, it’s easy to think “that will never happen to me,” and let things slide, but this could end up creating real security problems that can be difficult to overcome.
Here are a few common errors you should try to avoid:
1. The Post-It Full of Passwords
Take a walk around the office and you’ll likely find at least a few desks with Post-It notes full of passwords stuck to the bottom of a computer monitor. Yes, it’s convenient, but it also provides easy access to sensitive information to people who shouldn’t have it—like disgruntled employees or a thief during a break-in.
The Fix: Explain to your employees why this is a bad idea, and give them some ideas on how to manage passwords safely. It might also be worth investing in a password manager site or app that stores encrypted passwords online. This can be a real lifesaver if your organisation tends to work with many websites and applications.
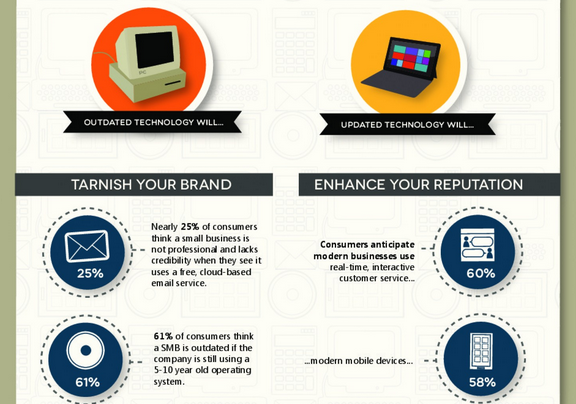
2. Outdated Operating Systems
Technology plays an important role in every business, but it’s often not the priority. That’s how things like updating operating systems slip through the cracks or get ignored until they become a serious security threat. For example, do you still have systems running on Windows XP or Windows Server 2003? Failing to update your operating system can be a serious security vulnerability, making you at greater risk of more advanced cyber threats.
The Fix: If you’re still running outdated operating systems, it’s time to transition to something more secure. A managed service provider can help you migrate your current system to a more secure platform, keeping track of critical updates and patches going forward so your system always stays up-to-date and continues to run smoothly.
3. Non-Existent or Old Security Software
Just because you’ve invested in a firewall or installed antivirus software does not mean your system protection should end there. If you don’t keep up with software updates and patches consistently, you aren’t nearly as secure as you think.
The Fix: Find out if you have the subscriptions and updates you need to keep your firewall and antivirus software as updated and as secure as possible. Many security apps come with a free trial period that is set to expire. Failing to get a subscription after can put you at risk. It’s also a good idea to reach out to a managed service provider who can oversee your security software and ensure you always have the latest version going forward.
4. Old Employees Still Having Access
Lax password policies and passwords that don’t expire create another security concern for SMBs. If you don’t set passwords to expire regularly, there’s a good chance a number of former employees still have access to your system. That doesn’t necessarily mean any of them will do something malicious, but why take the risk?
The Fix: Set up a solid password policy, and have passwords expire every 90 days. Yes, employees might think it’s a hassle at first, but the improved security will be worth it. While you’re at it, teach your employees the best practices for choosing a strong password that’s easy to remember but hard to guess.
How Lanrex Can Help
With as high as 81% of all cyber security breaches happening to SMBs, you need a managed service provider like Lanrex who can help you identify risks to your business, guide you in creating an effective cyber security strategy and be with you step by step to help you respond and recover.
Contact us to find out more about Lanrex’s cyber security solutions and how these can help you grow your business securely.
The Dangers of Malware to SMBs
By Lanrex on 30/10/20 2:39 PM
A cyber attack can cripple any business no matter how big or small. Nowadays, 60% of small businesses that experience cyber attacks can suffer long-term damage, with many of them going out of business within six months.
One cyber threat that is increasingly damaging to businesses today is malware, which can invade and disable critical computer systems, networks, and other IT devices.
In this article, we’ll explore what malware is, the types to look out for, and what any business can do to protect themselves for getting infected with malware .
What is Malware?
The term malware translates quite literally to ‘malicious software’. It's an all-encompassing term that includes viruses, ransomware, worms, spyware, adware, and generally any software that is used to obtain sensitive information without a user’s consent.
Malware disrupts computer systems in a variety of ways, such as by restricting access, encrypting files, corrupting data, stealing personal information, or slowing the system down.
Malware can infiltrate your system through unsecure downloads, email attachments, advertisements, or any type of security vulnerability in a system. After an infection occurs, a system may continue to function but may slow down and start to show signs of the attack, such as more pop-ups and random display messages. In some instances, spyware will continue to thrive in your system without ever being noticed, unless you have a good security software installed.
It’s important to stay updated with the latest security threats.
Types of Malware You Need to Know About
- Adware - A type of malware that displays advertisements on your computer and collects data about your browsing habits without your consent
- Keylogger - Malicious software that tracks the keystrokes on a computer and transmits the data to another location so it can be used to detect usernames and passwords that are typed on a computer.
- Ransomware - A software that locks a computer and retains control until the user pays a certain amount of money.
- Rootkit - A type of software designed to open a backdoor into areas of the operating system that are not supposed to be available, masking its presence while doing so. It is used to deploy other types of malware.
- Spyware – A software designed to steal user data such as website logins and passwords or proprietary information and trade secrets from machines it has infected.
- Trojan – A malicious software that seems legitimate but contains other software that attacks the system in some way after tricking a user into activating it.
- Virus – A type of malware that attaches itself to an application and then spreads to other programs and computers on the same network through an infected host file, causing a variety of damage when the application is run.
- Worm – A software that infects a computer and then replicates itself from system to system on its own without the help of a host file.
Protecting Your Business from Malware
The key to protecting your business from malware is to use a layered security approach that ensures there are no gaps in your security that can allow cyber criminals to get through. It’s essential to take a close look into your current security software to assess any gaps and evaluate how effective they are. It’s also important to have a clear understanding of your company’s workflows to determine the need for encryption, firewalls, authorisation levels, and password management.
Most cyber criminals take advantage of software vulnerabilities in outdated software, so businesses must continually update their systems to ensure they have the latest security patches that can address new and emerging threats.
Lastly, nothing works more effectively than ensuring everyone in your organisation is made aware of security threats that are damaging to any system. Regular staff training on cyber security threats and best practices goes a long way in helping them dealing with phishing emails, social engineering methods, and proper password protection.
Let the team at Lanrex help you craft a solid cyber security strategy to ensure your business stays on top of emerging threats.
Get in contact to explore Lanrex’s cyber security solutions today.
Bright & Duggan: Refining Your IT Strategy for Business Success
By Lanrex on 4/08/20 2:29 PM
Bright & Duggan is Australia's market leader and employer of choice in the strata and property industry. Established in 1977, they have experienced significant growth from just two employees and a home office to over 200 employees across multiple locations. They've spent 40 years developing and customising products and services to meet customers needs and have established a unique portfolio that now includes over 2,000 schemes ranging in size from two lots to estates with over 1,600 lots.
The Business Need
“We needed to invigorate our thinking and see technology as a requirement for the success of our business.”
—Bright & Duggan
Technology had not been front of mind for Bright & Duggan. IT was viewed as a business cost and the company used domestic grade equipment purchased from places like JB Hi-Fi rather than investing in Enterprise solutions. However, buying it cheap ended up producing more cost and risk to the business as it impacted productivity from downtime caused by server crashes. This led to 3–4 hours of downtime on each occasion and added lost hours for maintenance, with staff largely unable to work. With important data not being backed up, this posed a huge risk to the business.
Overall, there was a general lack of understanding about IT and the opportunity for positive impact at Bright & Duggan. Whilst they had three full-time team members dedicated to IT, their overall approach was simply not best practice. The lack of asset management meant there was no visibility or performance management of hardware and software infrastructure. The team at Bright & Duggan were running old software versions, which impacted performance and put the business at risk of not meeting data and security compliance.
Having to deal with different IT platforms, various software applications, and the lack of cloud solutions made it difficult to collaborate across multiple locations.
Bright & Duggan’s lack of IT investment impacted their overall performance, which limited them from meeting their growth demands. They had simply outgrown their current system which was time-consuming and led to costly infrastructure maintenance.
Key Challenges
Bright & Duggan needed to develop an overarching IT strategy to build a truly integrated property network for their group. This entailed documenting a group strategy, which included key stakeholders, business units, brands and operation managers. This can help bring people on the journey to enthusiastically support the strategy. They also needed to establish a clear direction for their IT strategy to increase profitability and market share and create a unique differentiation for Bright & Duggan as a brand.
Bright & Duggan had to consolidate technology into one platform to modernise it and keep it relevant. A tech audit was undertaken to create a diagram of the current infrastructure and solution and create recommendations. With the efficiencies of one platform, Bright & Duggan were able to remove the risk from outdated, non-compliant software and hardware and leverage best-of-breed technology for better competitive advantage.
Bright & Duggan were dedicated to offering a positive and consistent customer experience, which was unrivalled by competitors. To improve sales outcomes and streamline redundant processes, new opportunities needed to be captured and well-defined. Bright & Duggan had to modernise their comms capabilities for their customers and capture all communication and scheduling in one system, which then enabled them to respond to customers in a timely manner and minimise complaints for delayed response times. They wanted to capture customer satisfaction in real-time, measure and reward staff success and resolve issues before they escalated.
Employee Engagement was also another core focus for Bright & Duggan. They wanted to reclaim the work-life balance in their industry by providing their staff with a fully functioning mobile office so they could work on the go. Bright & Duggan also wanted to develop and attract a team of A Players and supply them with the necessary tools and connectivity to excel at their jobs. They also wanted to create a portfolio dashboard that would enable their team to manage their own capacity proactively and forecast customer demands and schedules to match team capacity.
Lastly, Bright & Duggan wanted to continue with their acquisition strategy to grow and diversify their national property network.
The Solution
Lanrex used its proven 4-stage Business Diagnostic approach with Bright & Duggan and ran Tech Workshops with stakeholders and team members to produce a technology vision, with findings and recommendations that were linked to Bright & Duggan’s business objectives.
Lanrex was able to consolidate all the multitude of IT components and requirements to connect them into common themes and business initiatives such as:
A Modern IT Platform
- Business systems operating from the latest version.
- Specialised software implemented to manage HR processes as well as customer relationship management processes.
- Standardisation of technologies in each office including phone system, wireless access, network connectivity and end user devices.
Paperless Office
- Centralised repository for documents and emails.
- Annotation software for online documents.
- Ability to capture electronic signatures.
- Compatible hardware such as dual monitors, touch screens, etc.
- Reliable and fast scanning facilities.
- Replace paper communication with online communication e.g. emailing levy notices.
- Streamlined workflows to support paperless work practices.
Collaborative Workspaces
- Online Web conferencing software, to make it simple and cost-effective to collaborate online with colleagues and customers. Participants can view the same screen as the host or examine selected documents.
- Online Video conferencing for boardrooms by taking advantage of the cameras that are now built into most office computers and nearly all mobile devices, and face-to-face video calls and group meetings without leaving the office for more effective collaboration. The technology can also be used for webinars, training and presentations.
- Office/mobile phones, that enable team members to solidify relationships, coordinate schedules and privately discuss issues and concerns.
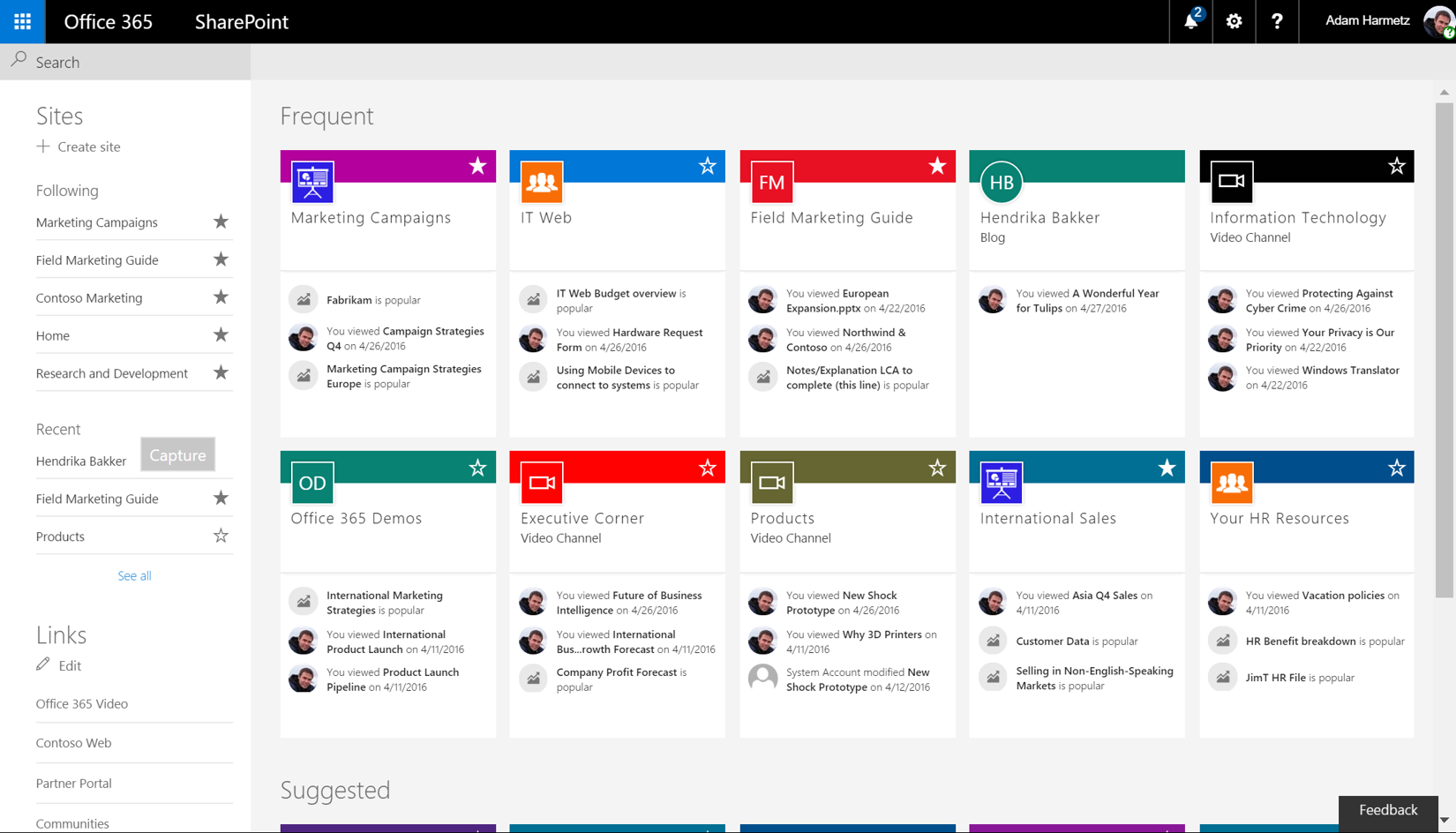
- Microsoft Office 365.
Better Mobility
- Anywhere Access - The combination of devices, software and management tools that provide the function and capability for employees to perform business functions from any location, at any time.
‘It sounds simple but it was when we were able to get email and access to other tools we needed on our mobile devices. It was a small change that had such a big impact on our work life balance. It meant we could respond quickly to customer issues without having to rush back into the office to sort it out’.
Key Results
As a result, Bright & Duggan’s teams can now work on the go, making collaboration much easier across multiple locations. They now have the scalability they need for acquisition growth and are enjoying greater efficiencies across the organisation from using just one IT platform.
Bright & Duggan reports that they now have consistency in the whole team experience with the same platform, making it easier for them to train their employees on the new system, so they can use it effectively. With Lanrex as their MSP, IT support was no longer reliant on one internal person and they now have access to a specialised IT team for support.
Lanrex helped Bright & Duggan create a disaster recovery plan and better control over their IT security, so that in the event of a disaster, they would have the capacity to manage the impact of any significant threat to the business.
Testimonial
“Before our investment in IT and working with Lanrex, an occurrence like COVID-19 would have been severely detrimental to our business. Our business would have ground to a halt. Instead we were already remote working and able to operate as business as usual.
Fast forward to COVID-19, we were able to respond rapidly to deploy our entire business to remote working. With Lanrex as our outsourced IT Helpdesk we had the added comfort knowing they were ready and available to help our team directly with any issues.
Although you need to invest money to look after your IT properly, cost savings were achieved in our reduced downtime, and the reassurance of Business Continuity. We were losing business productivity of at least 15 business days a year in downtime due to IT issues. When you add up our staff salaries that’s more than a million dollars a year.” — Bright & Duggan
5 Tips to Help Your Employees Stay Connected and Productive
By Lanrex on 24/03/20 3:57 PM
The COVID-19 epidemic has brought on a revolution in workforces today as social distancing calls have made teams adapt to a remote work arrangement. As a result, many team leaders and managers have adjusted to working from home and managing remote team members.
This can pose a few challenges for those who may have not done this before. If this is you and you find yourself in unchartered waters, here are a few tips from Lanrex to boost efficiency and help make things run a little smoother for your team.
- Communicate Effectively
One of the biggest changes from an office to a remote work setup is not having the ability to round up the team in person for your usual stand-up meetings. Rather than walk straight over to someone’s desk to check up on a project, all communication will now be done via email, chat, or video conferencing.
This is why it’s important for you and your team to set up some ground rules as to how to stay connected and continue talking to one another even through chat.
With social distancing, it’s important to ensure team members don’t feel isolated and the lines of communication always remain open.
Here are some apps that have worked well for remote teams:
- Instant Messaging — Microsoft Teams, Slack or Skype
- Video Conferencing - Microsoft Teams or Skype
- Phone apps - WhatsApp
- Project Management — Trello, Slack, Monday
It’s important to note that meeting structures will have to be adjusted in a remote work setup so be clear with your team on how to ensure everyone is across projects, deadlines and tasks. Flexibility is the key and if one method does not work for some, it is important to find ways to address this and provide alternative options.
- Keep Collaborating and Engaging
It is crucial for managers and team leaders to continue fostering an environment where the team can reach out to one another, ask questions and stay engaged even if it is off-site. Luckily, today’s technology offers a myriad of tools that can be used to promote engagement through group chats or video calls created in Microsoft Teams, Yammer Slack or Skype.
Having a daily check-in which can be done either as a team or one-on-one via video goes a long way to strengthening that connection you have with your team.
Daily stand-ups and WIP meetings should also be set up virtually to give your team the same structure that they may have been used to at the office. It is important to set up a schedule for this daily or weekly to ensure the team has a structure to follow where they can share ideas and contribute no matter where they may be based.
When your team dials in, they can take turns presenting and sharing screens or they can also make use of a dedicated channel to pin their ideas to. This should allow everyone to comment, give feedback and ask questions as needed. This can be done through a quick call via Microsoft Teams or Skype.
Celebrating daily and weekly wins through these activities give you the space to boost employee morale and remind them that their efforts are appreciated.
- Facilitate Meetings Better
While remote meetings can be fun, keeping everyone engaged and focused on the agenda can be challenging when done online. This is why having a clear agenda outlined ahead of time and choosing a dedicated facilitator to take the lead is crucial.
Create a shared document that people can access to add their notes in.
Ask people to contribute to the agenda and raise concerns if needed.
Remind everyone to mute their microphones during the meeting to minimise distracting noises
As much as possible, ask everyone to turn on their videos to continue connecting with everyone.
Although this may take a bit of an adjustment, it gets easier the more you continue to stick to these best practices every week.
- Keep Life & Work Separate
The key to successfully maintaining work-life balance at home and maximising productivity is by having the right focus at hours of the day when you should be working.
Adopting an ‘at-work’ mindset means setting a time when distractions should be avoided and when you should be taking breaks. As a manager, you should emphasise this with your team so everyone can work on the same rhythm and avoid burnout.
As majority of businesses have shifted to a work-from-home setup, you’ll also need to consider how some team members will have to contend with children and other family members at home. Consider how some team members may be working in the same room as their partner or child. You’ll need to consider this and help your team establish a work area where they will not be interrupted to maximise productivity.
- Manage Expectations with Your Teams
Managers need to set realistic expectations with their team in terms of work. This includes setting clear guidelines on the scope, target dates and deliverables for each task or project that they may be working on. By stating what the goals are and the reasons behind them, your team is in a better position to understand what success looks like.
Lanrex: Empowering Remote Teams with the Right Technology for Success
A lot is going on in the world right now and teams are adjusting to a completely different environment whilst working from home. However, by implementing these guidelines and setting clear expectations with your team, you can help make the transition of working from home easier.
If you want to make sure your team is equipped to handle the demands of telecommuting, get in touch with Lanrex today.
Your Guide to Cybersecurity Training for Your Employees
By Lanrex on 14/11/19 6:46 PM
An employee clicks on an email from their bank — they need to download new credentials. Suddenly, their system is frozen. And just as suddenly, your system is frozen. The new credentials were malware, sent by a cyberattacker, intended to look like an authentic banking email. Since your employee’s device was plugged into your network, your entire network has fallen prey to ransomware.
What’s your next step?
If you’re like many ransomware victims, you’re now in the position of having to either lose much of your data or pay tens of thousands of dollars in ransom.
Cybercrime is currently costing the Australian economy $1 billion a year and is expected to cost $6 trillion globally by 2021. The costs aren’t the ransom alone: it’s also going to take time to recover your data.
Employees can make mistakes. They are more likely to make mistakes if they aren’t aware that they’re making them. Cyber awareness has to be baked into a company from the top down, and cybersecurity training has to be thorough, consistent, and up-to-date.
If employees don’t know what to look for, they can’t identify threats — and there’s only so much a cybersecurity solution can do.
Here’s why security awareness training is so critical.
The Business Case for Employee Cybersecurity Training
Often, training is only completed as employees are on-boarded or sporadically when security events occur. This is not frequent enough. There are many benefits to regular employee cybersecurity training.
Through regular cybersecurity training, employees can both identify and react to threats. Reaction time matters: the faster a threat is identified and mitigated, the less damage it can do.
Employees will feel a greater level of awareness regarding safety and security measures. They will be more confident in managing their security because they know the company’s security protocols.
This will improve the way employees relate to their computer systems. Rather than shying away from computer-intensive tasks, they will feel confident and capable.
Ultimately, regular cybersecurity training has the following impact on business:
- Achieve better uptime. Data breaches and disruptions can take your business down for hours. A single data breach disruption can cost a company millions of dollars in lost revenue, depending on how reliant the company is on its network to continue processing transactions and information. The fewer data-related events, the more uptime the company can achieve.
- Reduce costs and overhead. Every data breach, no matter how small, is expensive. You will be able to reduce IT costs and overhead by protecting your data. Teaching your employees proper security will also reduce the amount of time your IT team needs to spend on tasks such as removing adware or malware from systems or resetting lost and forgotten passwords.
- Control and protect the organisation’s data. An organisation’s data is everything today, but it can be on hundreds or thousands of devices. With the Internet of Things and mobile device management, organisations need to be even more protective of the data that they are in charge of. A combination of employee training and technology is a powerful way to control and protect data.
- Adhere to internal policies. Internal policies keep the organisation safe from major security events. It also keeps the operations from moving slowly. Consistent internal policies will prioritise both efficiency and security.
- Comply with all relevant laws and regulations. Many industries are facing data privacy laws and regulations. A violation can lead to millions of dollars’ worth of fines. Security training helps with laws and regulations as well as security.
- Contain threats. When threats do emerge, they need to be addressed immediately. An organisation that can secure and contain threats immediately is an organisation that will not suffer an excessive amount of damage before mitigating the threat.
Implementing cybersecurity training is a step towards building a better and sustainable culture of security.
This is more than just about reminding your employees to regularly change their passwords. As Tim Ferris says, “Culture is what happens when people are left to their own devices.” Therefore embedding a culture of security means helping your employees understand and embrace their role in keeping your organisation safe.
Topics Covered in Cybersecurity Training
Cybersecurity is growing more complex every day, and security awareness training has a lot to cover. This is one of the major reasons that cybersecurity training has to be handled regularly.
Amongst other things, cybersecurity training covers:
Corporate Data Responsibility
What responsibilities do employees have to protect the company’s data? What responsibility does the company hold to its clients, vendors, and employees? Underscoring the importance of company data responsibility helps: it gives employees a sense of accountability and a measure by which to gauge the seriousness of the security efforts.
Document Management
Today’s documents can include a large quantity of personally identifiable information, confidential data and intellectual property.
Employees should understand how to manage their documents, including how to securely share them. They should be able to identify issues that may indicate that something is wrong: if documents are loading slowly, go missing, or are being accessed by unauthorised persons outside the organisation, consideration needs to be given that there could be a problem.
Data Incident Reporting SOP
What do employees do when they identify an incident? If an employee isn’t told what they should specifically do during a data incident, they may worry that they aren’t doing the right thing. They may hesitate to notify anyone of the incident, or they may assume that someone else has already taken care of it.
When it comes to security, reporting is critical: many data breaches and disruptions are ignored and consequently can get worse.
Password Security
Employees today often have it drilled into their heads that they need to create long, complex passwords. Still, they tend to reuse passwords or use similar passwords because it’s simply easier to remember. Employees need to be given tools such as password managers and password generators if they’re to be expected to manage their passwords securely.
Authorised Software Downloads
Employees will often download and install software that’s meant to make their job easier, such as a PDF viewer that’s lightweight and easier to use than an internal PDF viewer.
While this solves a problem for them immediately, it can open up a company to substantial risk. Third-party applications are one of the most common sources of data breach and disruption. Employees should be directed to only use the authorised software packages.
How to Identify and Report Cybersecurity Threats
Do employees know how to describe a threat when they see one? Simply having the language and terminology needed to adequately describe a threat can go a long way toward resolving it.
Email, Internet, and Social Media Policies
Quite frequently, cybersecurity events are caused by poor email usage, web browsing, and social media. Attachments can be sent through email and social media, and files can easily be downloaded from the web.
Employees need to be aware of the threats, as well as the hallmarks of these threats. If they compromise a personal device, such as a laptop or a smartphone, they run the risk of compromising a network of devices.
Computer and Mobile Device Mobile Device Policies
More employees than ever are using their personal devices for work, which can be beneficial. It improves a company’s efficiency by leaps and bounds. Unfortunately, it can also present some security risks, as an employer can never know how secure an employee’s personal devices are.
Through rigorous mobile device management policies, it becomes easier to secure an employee’s devices.
Social Engineering and Phishing
Social engineering and phishing thrive on employees being in the dark about their company’s security policies.
A social engineering attack begins with an attacker, who can look like anyone, using great social skills to interact with an employee. The attacker would gain the employee’s confidence so they could acquire company information only employees would know.
Phishing, on the other hand, is a kind of social engineering that uses email or malicious websites to acquire personal information. In March 2019, Evaldas Rimasauskas pleaded guilty to wire fraud after helping to orchestrate a scheme that misled tech giants Facebook and Google into paying him more than $100 million over the course of two years. The scam involved sending phishing emails to employees from a fake business Google and Facebook do business with Taiwan-based Quanta Computer.
There is no business too large or small for these scammers, therefore all employees should be educated on the signs of social engineering attacks and phishing emails.
The First Steps: How to Make Your Team Care about Cybersecurity
Cybersecurity matters. But your team will probably be focused on getting their jobs done. Often, IT security can seem to present a barrier to their jobs, and they may not properly understand how important cybersecurity is to the business. Training doesn’t just tell them how to secure their systems. It tells them why they should.
So how can you get started?
Both new staff and those who have been in the company for some time need to go through a standardised cybersecurity training. With this, third-party training is ideal.
When training is done internally, there can be gaps that remain because there is no one to notice them. Further, business processes and the culture of security can drift over time because there is no external reinforcement. Training has to be regularly updated, which is something that internal staff often don’t have the chance to do. A third-party that specialises in cybersecurity training can help.
Finally, gamifying employee training helps get the message stick. By rewarding cybersecurity trained employees and departments that go without major security events (or finding security events), you can show that the company truly does value improved security and that it values the employees who are trying their best.
Conclusion
Most businesses run under a false sense of security. They assume that because they haven’t yet experienced a major security issue, they won’t experience one at all. But it’s just a matter of time. Every company, regardless of how small or how large, is vulnerable to major security events. The best thing you can do is prepare.
Through regular cybersecurity training, you can ensure that all of your employees are on the same page and that they are committed to helping keep your organisation safe. You can prevent costly, time-consuming data breaches and data disruptions from occurring.
Ensure you have the right technology and your staff have the right training. Contact Lanrex today to learn more.
What Are the Implications of a Data Breach in Your Organisation?
By Lanrex on 14/11/19 6:33 PM
Modern-day companies revolve around their data. But with that data comes responsibility. Your company likely archives large amounts of information: data about customers, bank accounts, intellectual property, and more. When this information is stolen by an outside intruder, it’s known as a data breach.
Data can be exposed in several ways. It can be uploaded to other servers and systems, shared on the dark web, or used for identity theft.
Today, there are entire companies dedicated to hacking into organisations and breaching their data. They reside in other countries and are generally untouchable; they can continually attempt to crack into businesses because there are no repercussions for them.
This has led to some highly publicised data breach events. In May 2019, Canva reported a security event, which impacted an incredible 139 million users.
This morning we’ve been alerted to a security incident that enabled access to a number of usernames and email addresses. As soon as this happened, we remedied the issue and alerted the authorities. To be overly cautious, we’d recommend changing your password.
— Canva (@canva) May 25, 2019
https://twitter.com/canva/status/1132086889408749573
Usernames and email addresses were breached. The Australian consumer-facing digital design store subsequently urged it’s clients to change their passwords to protect themselves.
And it’s not just businesses that are at risk. In December of 2018, a Victorian government employee directory was reportedly accessed, revealing the information of 30,000 employees. This data breach leaked emails, job titles, and work phone numbers — all information that could be used for phishing attempts and social engineering.
But what do these types of data breach mean for a business?
Major Implications of a Data Breach
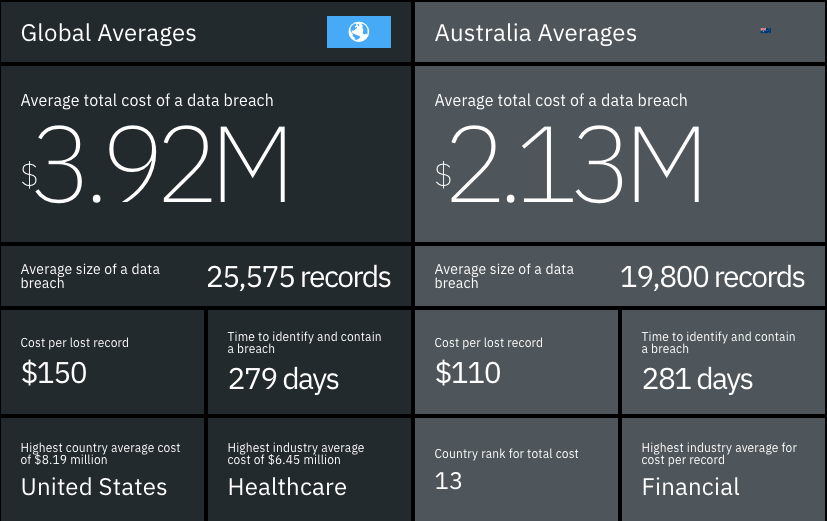
Data from 2019 Cost of a Data Breach Report by IBM Security and Ponemon Institute.
Many businesses aren’t concerned about data breaches until they happen. It’s something that they might think about occasionally, but not something that they feel they need to protect against.
A major data breach can happen overnight, leaving a company struggling to recover. What happens then?
A lot of expenses. Here are just some of the expenses that are usually attached to a data breach attack:
- Fines and penalties. If your security isn’t up to the standards required within your industry, you could be facing serious legal issues. Government agencies are cracking down on the fines and penalties issued to companies that are negligent with their security measures. Some industries, such as legal fields and medical, have additional security requirements.
- Ransom. Ransomware will lock down your system and your data until you pay the (generally untraceable) ransom. If you don’t pay the ransom, you can’t access your data. Your only option may be a full restore from backup. Without data, you may be unable to operate your business. Small businesses are more frequently targeted as they are typically less cyber security aware, do not have the same level of protection that a large enterprise may operate (although these large enterprises are themselves still not immune) and have a heavy reliance on immediate access to their data. The ransom amount can range from tens of thousands up to millions of dollars.
- Investigation costs. When a data breach occurs, you need to investigate what happened and how to prevent it from happening again. These investigation costs can be considerable as it requires complex levels of digital forensics. The more complex your network is, the more expensive this will be.
- Insurance issues. Your cybersecurity insurance should pay out in the event of a data breach or data attack. If you don’t have cybersecurity insurance, you may need to pay out for these costs upfront. If you do, your insurance premiums may increase.
- Recovery costs. You will need to recover your data and fix your technology, which requires a significant amount of labour and additional expenses. Your recovery costs will vary depending on the depth of the breach.
- Lawsuits. Customers, vendors, and even employees may sue your company for having their data breached. This is especially true if your company was negligent in handling their data, but even if you are not ultimately responsible, you will still have legal fees associated with defending your case.
- Revenue loss. Your primary revenue loss will be due to downtime when work and resources are affected. If you rely significantly upon your systems for things like transactions, you may have a significant opportunity cost. Ultimately, a data breach is more than just data theft; it’s about the costs that are associated with it. The average cost of a data breach in Australia is $2.13 million, for an average of 19,800 data records.
- Brand damage. Negative press about data breaches can lead to losing existing clients and difficulty in securing new business. It may require investment in marketing and advertising capital to recover and strengthen your brand. In the meantime, it’s difficult to continue building momentum when you’ve lost potential business. Rebuilding trust will take time, both among clients and key stakeholders.
Grow Your Business Securely
The cost of a data breach is significant, but you can protect your business through proactive security management.
By regularly auditing your security solutions and upgrading to newer solutions, you can grow your business securely and avoid the worst scenarios surrounding data breach attacks. Even if a data breach does occur, having better technology and business processes will help to reduce the costs.
Not only do you need thorough cybersecurity training for your employees and your IT personnel, but you also need next-generation cybersecurity solutions. Modern cybersecurity solutions can leverage artificial intelligence and machine learning to identify potential data breach attacks.
Cyber-attackers are now using highly sophisticated solutions which are being constantly refined. All businesses need to be able to turn their technology against them.
When you have your data stolen, there’s nothing you can do to “get it back.” While you may still have data on your side, the data is already out. It can be replicated thousands of times and spread far and wide. Your customers, employees, vendors and key stakeholders may have their data exposed and have no control over their personal damage.
To avoid the situation entirely, businesses need to have cybersecurity procedures and processes in place. Discover how Lanrex can help you grow your business securely.
8 Mistakes NFP's Make When Choosing a CRM
By Lanrex on 9/09/19 4:23 PM
It is not uncommon for many NFPs to operate their Constituent Relationship Management (CRM) processes from simple spreadsheets or a loosely connected combination of tools. This will work but only up to a point.
As the organisation grows, this basic approach becomes more difficult to manage and typically creates unnecessary complexity and can lead to mistakes.
Transitioning to a fully-fledged CRM tool may be a disruptive experience for your organisation. But when done right, it can lead to lasting improvements that will help to drive the results you need.
A well-designed CRM will provide your end-users with a powerful new tool that will dramatically impact the way they work by allowing them to work smarter, not harder.
However, getting to this point can be challenging without a clear and effective strategy.
Here are eight core points that NFPs frequently overlook when choosing a CRM.
1. Not Knowing Why They Need a CRM
One of the more common mistakes companies make in choosing a CRM is not knowing what they need from it and how it can improve their overall operations. Without first defining the ’why’, you may opt for a solution that is overly complicated or implement a CRM that is not used to its full potential.
As a result, you may end up investing a significant amount of time and money on something that does little to improve process efficiency and could, in fact, create more problems than the solution was originally intended to solve.
For best results:
- Make a list of all the problems you need a CRM to solve.
- Expand that list by including priority key features that you need.
- Weigh that list against each CRM on an individual basis.
- Take advantage of any free trials that may be available, thus allowing you to run tests to make sure you’re getting something that aligns with your objectives and the immediate needs of your end-users.
2. Having No Organisational Plan for CRM Implementation
Before setting up to deploy a CRM, it is vital to ensure that all processes are aligned with your organisation’s long-term goals and business strategy.
Successful CRM adoption within your business must be underpinned by a carefully considered implementation. META Group reports that without an effective implementation plan, 90% of businesses will not be able to show a positive return on their CRM tool.
Finding the right CRM is a process that entails finding a solution that works best for your organisation and understanding how you can deploy the specific CRM across your organisation to achieve the results you’re after in the fastest and most efficient way possible.
Knowing these two key points beforehand is crucial to your success. Outlining how you can successfully implement the system throughout your organisation to minimise disruption is imperative before jumping straight into it.
3. Not Understanding End Users’ Needs & Failing to Involve Them in the Process
It doesn’t matter what type of organisation you’re running or what goals you’re trying to accomplish; if you’re investing in something that will cause a significant disruption to end-users, you need to involve them in the process.
Before looking at serious candidates for potential systems, ensure that you understand your end-users’ needs and pain points. Conduct surveys and have discussions with them and make them a critical part of the process. Consider not only what any particular CRM will do for your organisation, but the impact on your end users. If they have questions and concerns, make it your priority to address them.
By putting your end-users at the centre of this initiative, you will be able to choose a solution that meets their needs in as much as yours. In turn this will greatly improve user adoption.
4. Rushing to Get “Out of the Box“ Too Quickly
Many non-profits choosing a CRM make the mistake of being “oversold“ on the out-of-the-box functionality of the solution, without understanding if there is a specific need to make adjustments or customise.
They often commit to an ‘off the shelf’ solution that doesn’t necessarily meet their business needs or growth. A CRM’s functionality needs to act as a solid foundation upon which something larger and more impressive will be built.
Every NFP is unique and solutions that work for others may not necessarily be what you need. Therefore, it is crucial to choose a CRM solution that aligns with your business requirements.
5. Choosing a CRM That Cannot Scale
Another common mistake involves choosing a solution that may work perfectly today without considering your future needs and requirements.
The right CRM solution should be able to grow with your organisation. Choose one that fits your needs and, at the same time, gives you the flexibility to evolve and re-align solutions when necessary.
Your infrastructure should always be considered a “work in progress“, and your CRM solution needs to be capable of expanding to meet any new requirements that arise — regardless of what or when they happen to be.
If your CRM can’t scale, it will quickly stop propelling your NFP forward and potentially hold you back.
6. Only Thinking of Social Media Integration as an Afterthought
According to a recent survey on consumer behaviour, 67% of consumers have interacted with a business through social media.
In an effort to be more donor-centric, you need to be actively listening to and engaging with your target audience, and the right CRM solution will help you do just that.
If one of your goals as an NFP is gaining valuable insights and creating lasting relationships with your donors, using a social media CRM tool and integrating it into your overall strategy is crucial to drive success.
7. Failing to Embrace a Cloud-Based CRM Platform
Established non-profits in particular, often assume that any solution they invest in should be local rather than cloud-based. Many of them are hesitant to fully adopt a cloud-based CRM because of security concerns.
This is a common misconception because the level of security in cloud service providers today is much higher when compared to local IT. They also provide automatic back-up and data recovery plans to ensure you have the reliability, mobility and security you need to truly scale your organisation.
8. Not Worrying about Breaking Down Silos until It’s Too Late
Don’t invest in something that is going to live in a vacuum. A CRM is about to become a powerful cornerstone of your non-profit organisation, but to unlock it’s full potential, it needs to be properly integrated with your current systems.
This includes:
- Your other standard organisation apps
- Any productivity apps that your end-users rely on
- Other critical functions of your organisation such as email
- It should also have an open API so that you can continue to deeply customise and integrate your CRM into other areas of your organisation moving forward.
If you fail to properly integrate your CRM with the rest of your infrastructure, you’ll likely end up with more roadblocks that can create further problems along the way. Any critical insight will continue to be locked off from various areas of your organisation, and people will be unable to act on it — thus putting you farther away from your goals, not closer to them.
Getting the Right CRM
Your growing NFP organisation and your constituents deserve the right kind of CRM to manage data. Spreadsheets will eventually become burdensome and ineffective. .
Whether you are a big or small organisation, the right CRM can help you nurture donor relationships better, build new relationships effectively, and achieve data integrity, amongst others.
These are the types of benefits that the right CRM platform allows you to enjoy, provided that you pay attention to the common mistakes that we’ve discussed above.
If you’d like to find out more information about avoiding risk and learning from the mistakes that nonprofits choosing a CRM often make, or if you have any additional questions you’d like to discuss in detail, don’t hesitate to contact Lanrex today.
3 Hidden Tech Issues Affecting Workplace Productivity And How To Solve Them
By Lanrex on 24/06/19 2:14 PM
One of the biggest mistakes that business owners make usually involves assuming that any tech-related issues are actually people-related issues.
You've spent a significant amount of money providing your employees with the latest and greatest that modern IT has to offer, yet your general productivity levels have stalled out. Obviously, this is a problem with the person using the tool as opposed to the tool itself, right?
Not necessarily.
Some tech-related issues are obvious, like a broken server or out-of-date software. Others, however, are less so. Yes, you may be dealing with a "people problem" in the literal sense in that your productivity isn't as high as you need it to be. But that's just a symptom. It's not the disease. The issue hidden underneath is technology-based and it's likely having a bigger negative impact than you realise.
Dealing with hidden tech issues is common in every industry. The key to mitigating risk from these areas involves knowing as much as you can about what those issues really look like.
Here are a few key things to keep in mind.
Hidden Issue #1 Your Technology is Preventing you from fully scaling your Business
This type of issue is most common in businesses that are experiencing rapid periods of growth. Your company is getting bigger, but the technological infrastructure at the heart of it all wasn't really designed with that express goal in mind. So even though the conditions of the business are changing, the tech itself isn't, thus creating a series of interconnected problems that are only getting worse over time.
Below are some of the ways this type of hidden tech issue manifests itself:
- A general lack of communication, particularly in remote areas. Communication and productivity may be fine in your main office, but collaboration with satellite officers or even employees who telecommute is essentially impossible.
- A lack of access from multiple devices. People have all the tools they need to get their work done, so long as they're using a desktop or laptop computer. If they try to work from home on a tablet or even a smartphone, things are needlessly difficult and complicated.
- Your older software was never designed to integrate with some of the newer systems and solutions that you're taking advantage of, and it shows. Employees need to spend time coming up with frustrating workarounds to get various programs to "talk" to one another, which consumes time that could be better spent elsewhere.
Thankfully, solving this particular issue is straightforward — it simply requires a careful and thorough review of your existing business processes. Overall, the technology you use in your business is supposed to support the way your people like to work. They shouldn't have to change their workflows to make up for the limitations inherent in the technology.
But the problem is as your business continues to expand, their roles and workflows naturally change.
If your technology remains stagnant and designed to support the organisation you were instead of who you are now, even simple tasks become cumbersome. By taking the time to better understand the state of your infrastructure, you can properly align your tech needs with your business strategy so you can enhance productivity across the board.
Hidden Issue #2: When Your Technology is Unable to Meet the Needs of Your Staff
Different studies have been conducted over the years that outline just how pressing of an issue employee disengagement really is. Disengaged and frustrated workers, for example, cost the United States economy an estimated $550 billion per year as they have a 60% higher rate of general errors than happy, engaged workers.
One of the major reasons that employees become disengaged in the first place is when they feel like they don't have the tools necessary to do their jobs correctly. They know what they need to do but struggle to complete simple to critical tasks and grow frustrated as a result.
This is where your technology usually becomes a problem.
Signs of this particular issue usually include but are not limited to ones like:
- You're constantly dealing with broken servers and hardware assets go down on a regular basis. This means that your employees literally cannot be productive. Every minute of downtime is a minute that your business is losing money.
- Data goes missing at the worst possible time. Your internal systems are confusing and restrictive. Employees literally cannot find the information they need to complete their tasks every day.
Most businesses can solve this issue by conducting a total technology audit of their current infrastructure. This alone can help generate an almost unparalleled level of visibility into your technology that would otherwise be unavailable to you.
If you have a total understanding of your current tech situation, you're in a better position to identify the opportunities present that you might not be taking advantage of. But more importantly, you're also able to identify the challenges that exist that are causing dips in productivity and frustrations among your workers. By then, you can essentially double down on everything that is working and fix what isn't.
What you're left with is an infrastructure that is optimised to maximise your existing assets for greater performance over the long-term.
Hidden Issue #3: Your Technology is Making You Lose Money
More than anything, your technology should be viewed as a revenue generator. Yes, staying ahead of tech trends and making sure that you're always using the latest IT requires a significant capital investment. But when leveraged properly, these IT assets should enhance productivity -— creating a positive ripple effect that impacts the quality of work your employees are doing, the amount of work they're able to complete and, ultimately, your business's revenues.
If your IT only ever seems to cost you money and doesn't seem to generate anything in return, this too is another sign that things aren't going quite the way you think. Usually, businesses deal with problems like:
- Inflexible systems that are unequipped to support business growth as it continues to evolve. There are areas of growth present and opportunities to be taken advantage of but it’s difficult, if not impossible, to find them.
- Your systems never have a chance to generate positive returns because you're always dealing with costly upgrades. You're constantly putting out money to upgrade physical assets so they never have a chance to positively impact your bottom line.
- You're always battling with risks of physical damage to old, on-site servers. You know that if something were ever to happen to your servers, your business would essentially grind to a halt. But you're not in a position to do anything about that.
To solve this problem, you need to consider the bigger picture and re-think your IT strategy, if one is present at all. A successful business cannot afford to consider IT as an afterthought.
Technology is not a "cost of doing business". In a lot of ways, it is your business. Or at least, a core component of it.
Once you know what your larger business strategy is, you're in a better position to understand the ways that you can leverage technology to support it. There will naturally be certain gaps that exist between your specific objectives and your ability to accomplish those goals. And those are the gaps that you should be trying to fill with technology, allowing your people to work "smarter, not harder" whenever they have the opportunity.
But you should also understand that there's no one right way to create an IT strategy. Every business is a bit different, which means that you need to look for ways to apply technology within the context of your own unique business.
Once you have that level of insight and understanding, you have everything you need to solve these and other hidden tech issues that you're experiencing.
The Lanrex Approach: Getting Your Business Ready for the Future
At Lanrex, we believe that while technology is undeniably important to the modern business, it's also ultimately just a platform. What that platform can do matters less than what it can do for you.
This is why we've made it our mission to help clients leverage IT to create better business outcomes over the long-term. Not only do we regularly partner with organisations of all types to help them perform thorough and accurate technology audits, but we can also review their IT strategy and assist with the optimisation of their business processes as well.
Many of our clients choose to outsource some or even all of their IT functions to us entirely for these reasons. These include not only the procurement of equipment but also connectivity (think: the Internet and unified communications), IT support, project delivery, and more.
In the end, we help people eliminate the tech problems that are holding them back so that they can take full advantage of the tech solutions that will drive them forward.
If you'd like to find out more about how you can solve your hidden tech issues and enhance your workplace productivity, or if you just have any additional questions you'd like to discuss with someone in a bit more detail, contact Lanrex today.
Sick of Failing Tech? Lanrex’s 4 Stage Business Diagnostic Can Help Make Technology Your Business Advantage.
By Lanrex on 24/05/19 2:21 PM
In other words, your organisation is totally unique unto itself - which means that you need to throw out the idea that there is some "one size fits all" approach to technology. Your long-term business strategy was built with your unique context in mind, and the same needs to be true with regards to the way technology is incorporated into that strategy.
Whenever a new client chooses to partner with Lanrex, we always try to convey this simple yet important idea as early and as often as we can. The right IT infrastructure can absolutely empower your business by putting your strategy first, by supporting your customer, and by allowing you to both address today's challenges and better prepare yourself for the ones tomorrow might hold.
In an effort to truly make technology your business advantage, you must acknowledge that nobody does what you do quite like how you do it.
The wrong IT infrastructure is ultimately just a bunch of noise. Not only will it NOT empower your business... it will likely end up holding you back.
This is the type of thing we work hard to change at Lanrex, and today we want to show you how to do it. It's actually a lot more straightforward than it sounds - it just involves four basic steps and a steady, helping hand by your side. The four steps to make technology your competitive advantage are:
- Focus on Your Business Strategy.
- Ensure Employee Engagement.
- Conduct a Total Technology Audit.
- Best Practice Benchmarking.
Step 1. Focus on Your Business Strategy
Before you even begin to develop your larger strategy for technological transformation, you need to ask yourself questions like:
- Where are you playing, and how will you win?
- What will your organisation look like in three years, compared to how it looks today?
- Where, specifically, do you see your business in five years within the context of ideas like expansion?
All of these are questions that only you can answer, but once you've done so you'll have a better understanding of the types of things you need to be thinking about before you even bring up the subject of technology.
Summary:
Even though your digital transformation is going to end with technology, it can never begin there. Your transformation should support and empower these qualities for the absolute best results.
Step 2. Ensure Employee Engagement
Any type of technological transformation always requires a complete buy-in from every last member of your organisation. This begins with the leaders at the top, yes - but if it doesn't also extend down to the most recently hired employee on the front lines of your organisation, any project you're thinking of pursuing is doomed before it's even had a chance to get off the ground.
Of course, that's not to say that digital transformation is the only reason to focus on empowering your employee engagement. Far from it. Consider the fact that, according to one recent study:
- Teams that are highly engaged tend to show profitability levels that are about 21% higher than those who are not.
- Another recent report revealed that a full 89% of all human resources leaders agree that engaged employees are one of the keys for successful outcomes.
- Employees who feel like their voice is both heard and valued are as much as 4.6 times more likely to perform their best work.
Employee engagement is an important part of how you make technology your business advantage because it once again gives you an opportunity to answer questions like these:
- What, specifically, is being required of your employees on the front lines?
- What, if anything, is currently getting in their way?
- What tools do your employees need to more effectively do their jobs?
- How can you use technological transformation to provide those tools?
Summary:
In the short term, strengthening employee engagement will absolutely help with transformational buy-in. In the long-term, it will make you a more productive, more profitable organisation capable of doing better work on the other side of that transformation.
It's a simple investment in your workforce that can pay dividends for a generation if you do things properly, which is why it's such a key part of this process.
Step 3. Conduct a Total Technology Audit
Any journey requires intimate knowledge of both an origin and a destination - and a digital transformation as significant as this one is certainly no exception. To put it another way, once you know where you're trying to go, you also need to recognise where you're starting. Only then do you have a chance to connect those two points in the most efficient, cost-effective ways possible.
This brings us to step three of making technology your competitive advantage - a total technology audit. You need to think about things like:
- What your current situation looks like from an infrastructure perspective.
- Where the opportunities that you should be taking advantage of are located.
- The challenges that currently exist that are preventing you from capitalizing on those opportunities.
At Lanrex, this is one of the many techniques we employed when we assisted a specialist underwriting agency in the creation of a new IT strategy that could help them scale and grow as their business continued to expand across Australia. After making sure that we had a thorough understanding of all of the company's important issues and requirements, we were able to come up with a system that not only supported the singular entity of the business during expansion, but that also supported and empowered its employees and their online trading platform that itself is used by more than 650 brokerage houses across the country (and counting). 
None of this would have been possible had we not taken the time to understand what their technology looked like, so we could get a better understanding of what it needed to be. There are countless examples of great IT strategies that businesses of all types can learn from, and the one thing they share in common is that none of their architects skipped this critical step.
Summary:
During this process, you must have a solid understanding of what your current technology situation actually looks like. At that point, you'll be able to identify those best practices that can help you maximize your existing assets for greater performance.
You'll also be able to learn more about the new assets you need to implement to push your entire business further down the line towards success moving forward.
Step 4. Best Practice Benchmarking
The final step of this process involves best practice benchmarking - something that again involves processes that are unique to your organisation and what you are trying to accomplish.
Now that you've identified your goals, you're in a better position to honestly reflect on how you rate in certain key areas. You now know what "leading" actually looks like, so you'll have an easier time identifying whether you're doing so yourself. This speaks to how you're doing in relation to your competitors, yes - but also how you're doing internally when referencing how you're utilizing your systems, assets and even operations.
Summary:
The only way you'll ever be able to improve is if you know what improvement actually looks like. You need to define "success" BEFORE you strive for it, or it will be a bit like trying to hit a moving target. Success isn't just external - there are always room for improvements internally, too.
The Lanrex Approach
At Lanrex, these are four key steps that we believe in deeply - to the point where we've made them each core pillars of our Lanrex 4 Stage Business Diagnostic. As a functional process, it's designed to uncover precisely where technology connects to your business. In a broader sense, it's the starting point we need to not only audit your existing infrastructure against every industry best practice available, but to also develop the actionable, insightful and forward-thinking plan that is perfect for you and everything we hope to accomplish.
How Our 4 Stage Diagnostic Works For You
After partnering with you we make sure we understand what your unique business strategy actually is before we even think about talking tech. We'll then use our extensive internal technology setup and optimization experience to help you get everything in order as far as employee engagement is concerned.
When UES International grew faster than their technology. Lanrex's strategic focus ensured they were able to scale safely.
Then, we'll take the lead with your total technology audit - helping to identify all the best places to focus on maximizing all of your existing assets for an even greater performance and return on investment than ever before. We'll finish everything off with best practice benchmarking - something that will truly show you where you stand so that together, we can help you get to where you're going.
We have data reflecting businesses of all shapes and sizes AND their optimum tech systems, assets and operations. All of this is data that we are ready and willing to leverage to your advantage.
How The 4 Stages Have Helped Businesses Like Yours
It's something that we've done for businesses all over the world time and again - like when we helped a rapidly expanding company turn slowing servers, unreliable backups and low team productivity into a brand new IT infrastructure. Not only did this allow them to enjoy a clean slate and leave all those problems in the past, but it also gave way to a competitive advantage that serves them will do this day.
We also leveraged these principles when we assisted a charity group and their cancer support experts as they successfully relocated the entirety of their IT infrastructure. By breaking what would typically be a daunting process into these series of four manageable, actionable steps, we successfully installed and migrated the client's IT system and infrastructure to their new office without any type of significant disruption to speak of.
How You Can Make Tech Your Business Advantage
These are just a few of the real life examples of these four core steps in action. Rest assured, there are many more. But in the end, remember that if you truly want to make technology your business advantage you often need to let the technology itself be your guide - and having a valued partner with years of industry experience like Lanrex certainly doesn't hurt, either.
If you'd like to find out more information about using technology to create a competitive advantage for your business, or if you have any additional questions you'd like to discuss with someone in a bit more detail, please don't delay - contact Lanrex today.
4 Surprising Ways Innovative Technology Can Boost Productivity in the Workplace
By Lanrex on 18/04/19 10:48 AM
When people think about innovative technology in a professional environment, they usually picture some sort of seismic shift that represents a massive disruption to the way things are done. The first time your office got a personal computer was likely one of those watershed moments. Suddenly, everything was separated into just two categories: before the computer and afterwards.
But most of the time, innovation is far smaller in scale than that. One day, everyone starts bringing their smartphone to work — something that doesn't seem too out of the ordinary at the time. The next day, people are communicating and collaborating like never before from a device that we now recognise as a portable supercomputer. It all started in a subtle way but the long-term impact of that innovation was enormous.
This effect is being seen again in the present day, as more and more examples of innovative technologies are finding new homes in offices and business environments around the world. But for every obvious way that IT becomes a much-needed adrenalin injection to your productivity, there are others that could easily be missed if you aren't paying attention at just the right moment.
Here are the four surprising ways innovative technology can boost productivity in your workplace you need to be considering:
- Letting AI fuel Automation.
- Use Social Networks for Less Emails.
- Innovation & Problem solving through VR.
- Work less with IoT.
The Era of AI-Fueled Automation Has Arrived
The technology behind artificial intelligence may be sophisticated, but the idea at the heart of it all is straightforward. It refers to the development of computer systems that can take tasks that would normally require human intelligence and perform them without employee interaction of any kind.
This can include but is not limited to things like visual perception, translation between languages, speech recognition, and even decision-making.
Yammer and Slack are just two of the many examples of solutions that can help you fully leverage AI to your advantage. For the past few years, Slack has been using AI to help automatically determine which of the 70 or so messages users get a day on average are the most important. Yammer operates in a similar way, helping people determine what needs their immediate attention (and what doesn't) and is even making gains in terms of sentiment analysis.
Audiences were shocked when Google revealed their eerily human sounding AI virtual caller.
If your workers are able to offload certain time-consuming, menial tasks to these types of programs, their natural engagement levels with their job will increase. Not only does this help build morale, but it's likely to increase productivity levels as well.
One recent study revealed that highly engaged teams within a business tend to be about 21% more productive than average. Those businesses also have to deal with about 28% less internal theft — this means you can enjoy significant savings on all office supplies that have a tendency to go missing as well.
As an added bonus, your employees will also love the fact that they will never have to worry about running late to a business meeting ever again. They can simply use an AI Virtual Caller to buy them enough time to make it into the office before managers even realised there was a problem to begin with.
How AI boosts productivity:
- AI is a powerful yet simple way to automate certain time-intensive administrative tasks so your employees can focus on more important things.
- As your employees’ jobs get easier, their engagement levels with your business tend to increase.
- Studies have proven time and again that engaged employees work more productively than those with low or even average levels of engagement.
The Relationship Between Social Networks and Engagement
Over the last decade, social media sites like Facebook and Twitter have become a nearly ubiquitous part of our lives. But a lot of people still don't realise that they have the potential to have just as strong of an impact on our professional lives as they do on our personal ones.
Tools like the aforementioned Slack and Microsoft Teams can be leveraged to create social networks that exist entirely within your organisation. Even at its most basic level, this can reduce the need for unnecessary emails because communication can play out as a fluid, natural conversation instead of a series of back-and-forth messages.
Both Slack and Microsoft Teams offer voice and video calling in addition to text-based messaging, have huge file storage limits per user, and can be easily integrated with hundreds of apps that you're likely already using as well.
If work-based conversations become as easy as they are frequent, your employees are much more likely to collaborate with one another on various projects. That not only improves the overall productivity levels in your office, but the quality of that work will rise as well.
Likewise, employee buy-in isn't something you have to worry about as people are already familiar with how a social network works in a larger sense. Plus, once you show them how easy it will be to organize those Friday Happy Hours, adoption will more or less take care of itself.
How Enterprise Social Networks boost productivity:
- Office social networks bring the same communication and collaboration benefits that we've been enjoying in our personal lives for years to our professional ones.
- Conversations become much more fluid and organic, as opposed to the cumbersome back-and-forth messaging offered by email.
- As collaboration increases, productivity increases as well.
Virtual Reality: Boost Both Innovation and Problem Solving
Another example of a technology that can significantly increase productivity in the workplace is virtual reality. Many organisations have been using it to help with the training and onboarding of new employees — a trend that is only going to increase as time goes on.
Imagine if you were running a construction company and you could train an employee on how to use a crane without actually putting them in physical danger. Or if you could suddenly provide hands-on experience to new workers in a wide range of different costly situations without actually needing to spend the time and money to recreate those situations in the real-world environment.
A construction worker undergoing training for a high-risk scenario.
Virtual reality can even open the door for a new level of experimentation, allowing your employees to see problems from different angles in a way that lets them try out new techniques that may have otherwise been impossible.
Not only does this application of virtual reality allow you to save money on training, but you're also leveraging more effective procedures (and potentially far safer ones too). As the quality of your training increases, so do the skills your workers bring to their jobs. At that point, the only place their productivity can go is up.
VR also has a number of fun implications for your office. Instead of leaving the office whenever they need to take a break, your workers can instead use their VR headset to experience any environment they'd like in stunning detail. Their senses won't be able to tell the difference and you don't have to worry about someone clocking in late after lunch.
How Virtual Reality boosts productivity
- Virtual reality, when applied properly, can have an appreciable impact on the ability of your employees to innovate and solve problems.
- It's a great way to improve your training procedures, creating lessons that are more effective and (in many cases) safer.
- This is a perfect opportunity to inspire meaningful change and allow people to see things from different angles that they wouldn't normally have access to.
The Internet of Things is Finally Ready for Prime Time
For years, we've been hearing about the impending onslaught of the Internet of Things — a series of billions of devices that are all connected to one another, creating and sharing data at all times. Not only has the IoT officially arrived, believe it or not, the increase in productivity it has brought with it to the workplace may have actually been understated.
Take something even as simple as note taking, for example. Instead of dividing your attention between the person speaking in a meeting and your pen moving across a piece of paper, let your virtual assistant take all the notes for you and send them straight to Microsoft Docs, Evernote or another app.
The IoT will also be a huge benefit in terms of resource management. Not only can employees better manage their schedules, tasks and project deadlines, but it also allows employers to have more visibility than ever into how work is being done in business.
 Downer are introducing a network of sensors to improve Sydney's rail system.
Downer are introducing a network of sensors to improve Sydney's rail system.
You can see which projects tend to require the most physical resources, making sure everything is allocated ahead of time to avoid costly delays. If you're a fleet manager, you can see which drivers are taking the most efficient routes and which ones may need a bit of additional attention.
The IoT is also helping people create safer workspaces too. Safety cameras and even access control systems can help preserve the security of your physical environment and specialised sensors built into the devices themselves can help ward off issues like malware and any sort of informational theft.
At this point, the Internet of Things can practically do it all — even serving as a duly elected office temperature monitor. Data can estimate the best possible temperature at any given time so your employees will spend less time fighting over the thermostat and more time behind their desks where they belong.
How IoT boosts workplace productivity:
- Many of the major benefits of the Internet of Things for businesses are less about anyone major change and are more about a series of smaller ones.
- Virtual assistants can take notes and send them directly to any program you'd like.
- Smart cameras and access control systems are a great way to improve physical security.
- The IoT is also invaluable for resource management, particularly as it relates to the allocation of physical assets and staff workloads.
Today’s Innovation: Paving the Path to the Future
In a nutshell, any one of these reasons would be compelling enough for anyone to start embracing the advantages of innovative technology with open arms. But when you consider that a few subtle IT adjustments can allow you to leverage all of these and others at the exact same time, you arrive at the core of modern ingenuity.
To put it another way, business leadership will love that employees can now do more with less, while employees will love the ease at which they can organise the occasional Happy Hour daily or weekly with colleagues. Truly, it's the definition of a win-win situation.
As an industry-leading provider of a wide range of Microsoft products like Microsoft Teams and others, the team at Lanrex understand the true power that innovative technology can bring to the table when leveraged properly. At the same time, however, we also believe that technology is ultimately just a platform. What that platform can do in a broad sense matters far less than what it can do for you — which is something we've spent years helping organisations maximise efficiency.
If you'd like to find out additional information about how innovative technology can increase productivity in the workplace or if you have any additional questions you'd like to discuss in a bit more detail, contact Lanrex today.
The Top 7 Benefits of Migrating to Office 365
By Lanrex on 10/04/19 9:41 AM
Since its initial release in June of 2011, Microsoft’s Office 365 has grown from “just another productivity suite” to one of the dominant tools in its category available today. Thanks to the way it integrates with cloud-based services, it has opened a series of incredible new doors for businesses in terms of productivity and collaboration alone.
Still, organisations that have been hesitant to make the jump into the cloud have been equally weary about embracing the next generation of Microsoft Office. In truth, there are a number of incredible benefits that your business can get by migrating to Office 365 that you likely aren’t going to be able to find anywhere else.
Out of the various options, we believe that the top 7 benefits of migrating to Office 365 are:
-
It Empowers Your Ageing Infrastructure
-
Integration With The Tools You Already Have
-
You Can Work Anywhere, Anytime, No Exceptions
-
It’s Scalable with your Business
-
Security + Control = Peace of Mind
-
Safety In High Cloud Availability and Data Redundancy
-
Maintenance-Free Operation
1. It Empowers Your Ageing Infrastructure
One of the most significant benefits of migrating to Office 365 has to do with how it allows you to save not only time but money with regards to your ageing equipment. As an infrastructure ages, costs tend to skyrocket. What you used to be able to accomplish with one solution now requires two or more. Even simple things like video conferencing become laborious and intensive.
The Girl Scouts of Colorado is just one example of an organisation that saw these benefits firsthand. The staff was able to accomplish a wide range of tasks just by migrating to Office 365, like:
-
Reducing the number of servers they had to maintain from ten to five, with three of those being virtual
-
Execute calls and web conferences without the need to go beyond Office 365.
-
Embrace instant messaging and other collaborative tools like remote desktop that allowed employees to communicate with one another and share files without requiring them to set up a VPN tunnel
In the end, they were able to save approximately $100,000 by making the jump — especially when you include staff time needed to set up and maintain alternatives.
In summary:
With a skilled managed service provider (MSP), migrating to Office 365 does not require a complete overhaul of IT but an optimisation of existing infrastructure. The Girl Scouts of Colorado saved $100,000 by migrating to Office 365 this way.
2. Integration with the Tools You Already Have
On a basic level, another major benefit of migrating to Office 365 is that it works seamlessly with the tools you’re likely already using. If your business relies heavily on Microsoft Outlook, PowerPoint, Word, Publisher, and other solutions, you don’t have to worry about relearning everything all over again.
These tools will still continue to work, and thanks to the cloud-based nature of Office 365, you can even take the results you can achieve with these tools to the next level.
In summary:
Migrating to Office 365 increases the efficiency of existing software so you can dramatically improve productivity.
3. Work Anywhere, Anytime, No Exceptions
The most obvious advantage of migrating to Office 365 is that it provides web-enabled access to just about everything. Documents, email, contacts, calendars — everything can be accessed anywhere, at any time, on any computer, smartphone, or tablet that you happen to have handy. This comes at a significant advantage for companies offering flexible work arrangements to their employees.
Carpool Agency had always used mobile solutions, but after implementing Microsoft Teams and the Office 365 productivity suite, productivity dramatically increased. The increased flexibility boosted staff morale and, as a result, improved the efficiency of the agency.
In summary:
Microsoft Teams, and the rest of the productivity suite can enable positive productivity and cultural shifts in your team.
4. It’s Scalable with Your Business
Office 365 is also highly scalable, allowing it to continue to grow and evolve as your business does the same. With Office 365, you pay for what you’re using — this means everything from embracing new solutions to adding on additional data storage as you bring on new employees are both effortless and highly cost effective.
When Japanese innovation agency, Dream Factory experienced unpredicted success with a major project, the growth led to critical infrastructure gaps being exposed. Previously, they employed several different IT systems to help them grow, but these proved only temporarily successful.
Office 365 provided Dream Factory with the scalability and flexibility they needed, while also managing to reduce overhead costs involved with managing their own systems. Now they are poised to help manage the radical success of their project and prepare for the next venture.
How Office 365 Helps:
Office 365 allows you to pay for your individual business needs, meaning nothing is wasted and everything is used. Dream Factory used Office 365 to manage an unpredicted radical high-growth project with major success.
5. Security + Control = Peace of Mind
Office 365 is also highly advanced in the realm of security. With Office 365 you get the same protection for documents, networks, and emails that’s used by the biggest enterprises in the world. Microsoft data centres further manage your data stores and are certified to meet industry standard certifications.
Built-in tools allow you to control file security on a granular level, allowing you to set permissions by employee or by their role in your organisation. Not only do you see who has what data, but you can also actively change their permissions, giving you complete control and transparency.
And if a mobile device with Office 365 connectivity is ever lost, you can wipe it remotely so that this data doesn’t fall into the wrong hands.
How Office 365 Helps:
You get world-class data security and are able to completely control and set the transparency of your company’s data.
6. Safety in High Cloud Availability and Data Redundancy
Two key benefits of working in the cloud with Office 365 is availability and redundancy. This means that you are able to access all data on the cloud as you wish, bypassing delays from server mishaps, technical breakdowns or severe disasters (e.g. fires, power outage, extreme weather etc).
This significantly decreases the possibility of suffering catastrophic data loss to the point where any particular file or collection of files would not be able to be recovered.
How Office 365 Helps:
Through Office 365’s cloud storage system, you get access to data when and where you need it while safeguarding your data in case of extreme unexpected events.
7. Maintenance-Free Operation
Speaking of high availability, Microsoft also guarantees 99.9% uptime and 24x7 online and phone support to all users. This, coupled with the guaranteed maintenance of all Office 365 servers, provides your organisation with the technology it needs without having to worry about unexpected disruptions at the worst possible time.
How Office 365 Helps:
With Office 365, you get 99.9% uptime and up to 24x7 online and phone support so you know all your important work is accessible no matter what the circumstances may be.
Empower Your Organisation’s IT with Office 365
As you can see, Office 365 is more than just a simple productivity suite. Gone are the days where the functionality of Microsoft Office worked in silos, trapped in a series of disparate applications that did well on their own but failed to rise as a completely productive set.
With Office 365, you get a comprehensive collaboration and communication tool that enables you to do your best work, anywhere, and at any time so you can work smarter, not just harder.
Office 365 empowers your employees and your entire organisation to be in the best possible position to improve business performance and outcomes across the board.
If you have any additional questions about the major benefits of migrating to Office 365, or if you’re looking for strategic insight into how you can better apply technology to accomplish your business objectives, contact Lanrex today.
How cancer support experts CanTeen narrowly escaped a tech breakdown by successfully relocating their IT
By Lanrex on 27/02/19 11:00 AM
There have been 138,281 cancer cases diagnosed in Australia in 2018. But in spite of this rapidly growing number, there is no way to ever fully prepare you when cancer strikes. This is why cancer support groups are a much-needed respite for individuals who find themselves or their family members facing cancer.
CanTeen is a charity group that supports young people dealing with a close family member’s cancer or their own. Through CanTeen, they learn to explore, deal, and come to terms with their feelings about cancer. The support group gives them a safe space to cope with these difficult emotions and helps them connect with others their age in similar situations. CanTeen also offers young cancer patients with access to specialist treatment teams.
At the heart of CanTeen and everything they do are the young people affected by cancer who need support and also offer their very own to others just like them.
CanTeen relies on the generosity of the community to continue its vital work, which also includes leading-edge research into dealing with the emotional and social impacts of cancer and aims to gain a true understanding of young people’s behaviour when cancer does happen to them.
The Business Need
To better cater to the needs of their community, CanTeen has endeavored to relocate their Sydney CBD office to Newtown. This involves cutting over to a new wide area network (WAN) and relocating their IT infrastructure to a new data centre.
Key Challenges
Fully relocating your IT infrastructure and implementing network changes and reconfigurations can be a daunting prospect, especially if you only have one system administrator as your only resource. To make it even more challenging, logistically, the IT infrastructure move and switch over had to be completed overnight as CanTeen had no backup equipment in place.
Solution
Vlad Semenikhin, CanTeen’s Systems Administrator, issued a select tender to three companies who were chosen from recommendations by CanTeen’s Citrix account manager.
Based on the responses to the tender and the presentations which were provided, Lanrex won the business to facilitate the move.
Vlad and CanTeen’s management team were both impressed with the level of professionalism and can-do spirit shown by Lanrex and it’s team towards their specific requirements. After the decision was made, Lanrex won the bid as the “suitable candidate.”
For its part, Lanrex conducted a complete risk analysis prior to the commencement of the CanTeen’s IT system migration. All essential risk mitigation was clearly and thoroughly documented. Documentation was also provided outlining Lanrex’s approach to the project.
The move was scheduled for a Friday evening with the aim of having all systems available for the Monday morning return to work.
The pack-up commenced at 6:00 pm, the move began at 9:30 pm, and all systems were successfully back online at 2:00 am on Saturday morning, without any untoward issues.
The Results
Through Lanrex’s experienced team of professionals, CanTeen’s IT system and infrastructure was successfully installed and migrated to their new office without any significant disruption to the business.
The Future
CanTeen continues to work with Lanrex on a number of projects including the upgrade of their Citrix environment from XenApp 5.0 to 7.6. This is a type of upgrade and overhaul of their IT environment which includes a brand new build.
Since CanTeen’s current IT environment was still using outdated 32-bit architecture and a Windows 2008 server, the change was long overdue.
CanTeen’s new hardware in the data centre with increased storage now provides greater efficiency and productivity.
Future projects include updating the CanTeen CRM, a move to Office 365, and changing from tape backup to backup to disk.
As CanTeen’s system administrator noted, working with Lanrex has given CanTeen a fresh start and has enabled them to continue reaching out to others who need the help of their support group.
Along with the smooth and timely relocation, Vlad was impressed with the way Lanrex performed saying,
“They were very good throughout the move. They are very willing to assist and they are always upfront and straightforward in their approach.”
To Vlad, working with Lanrex has been an overall smooth and positive experience and one that he would recommend to anyone else who may need the same level of support to empower their business to scale.
The future of SMBs: Discover 5 of the most disruptive technology trends affecting Small Businesses in 2019
By Lanrex on 13/02/19 4:56 PM
If 2018 is anything to go by, 2019 will be an enormous year for SMBs. Technology looks set to disrupt more and more industries and no one really knows what's coming next. We put together a list of the most disruptive tech trends that SMBs need to be aware of.
Download the Infographic here: Lanrex Biggest Tech Trends For Small Businesses in 2019
Our purpose at Lanrex is to help SMBs make their technology a business advantage. We want to simplify the tech talk, and implement technology that means business.
If you have any questions about the future of tech and your business, we would love to hear from you.
Yours sincerely,
Jodie, Managing Director of Lanrex.
How Australian business AgriRisk found steady ground with Lanrex when upgrading their technology
By Lanrex on 24/01/19 10:30 AM
AgriRisk was established in 1989 as one of the first specialist rural insurance brokers in Australia. The business has always paid special attention to client relationships, personal service, and targeted advice to a range of agricultural operations from large corporate and supply chain agribusinesses to the smallest family farms, seasonal contractors, agronomists, rural professionals. and supply chain businesses.
With three locations in Australia, AgriRisk offers crop and general insurances and also specialises in difficult, complex risk solutions for larger corporate agribusinesses in the non-traditional insurance market.
The Business Need
As a small to medium business, AgriRisk realised very early on that technology wasn’t their core strength. They understood that they required specialist knowledge to achieve the best results. For many years they have outsourced their IT requirements while still keeping the necessary infrastructure in-house.
In order to remain current and ensure they have the best possible solutions for their business, AgriRisk has always had a regular audit of their IT systems done by an independent consultant. It was when an audit revealed unsatisfactory issues, AgriRisk decided to look for an alternative provider.
High on their list of requirements was a provider who partnered with “best of breed” companies — a Microsoft Gold Level partner with solid hardware partnerships and networking solutions such as Cisco. Their IT provider also needed to be proactive and stay current with IT trends. They found all of these requirements in Lanrex.
AgriRisk’s Key Challenges
Having several office locations was one challenge for the business but what was more pressing was third-party specialist applications essential to AgriRisk’s operations, such as their main insurance broking platform. This application must always remain compatible with the overall IT operating environment.
IT Support & Consultancy Solution
Lanrex provided IT support and consultancy to AgriRisk, managing their day-to-day operations, reporting and resolving any issues which may arise, and giving advise on updates and improvements.
Regular IT audits have been done and since their partnership with Lanrex, no irregularities or issues have occurred. All AgriRisk staff have access to Lanrex should they experience any IT problems, which are duly recorded and included in monthly reports to AgriRisk’s Financial Controller, John Anderson.
Due to the widespread locations of their clients, AgriRisk staff members are often mobile — using tablets and smartphones to access pertinent information while on the road. Not only do they need access to AgriRisk systems, but they also need access to a range of insurers, depending on the type of insurance coverage required by the client, for information and to provide detailed quotations.
Key Outcomes & Results
The high level of service provided by Lanrex to AgriRisk is key to the longevity of their partnership, which commenced in 2008.
John Anderson commented, “Lanrex always employs good people who work hard to solve any issues, no issues are hidden away, and they are always upfront. Lanrex is proactive, discusses futures, and actively participates in where you are heading.”
Even though all staff can access their IT support, John receives monthly reports so he remains fully briefed.
The Future for AgriRisk
While cloud computing hasn’t yet been on the AgriRisk agenda, it is part of their future thinking and will depend on key applications being enabled for that environment and Lanrex will be a part of any move to the cloud.
John is happy with the Lanrex partnership and would happily recommend them to others.
“They don’t take things for granted, they keep up-to-date and they understand where key IT players are headed. While we don’t want to be crash test dummies, we don’t want to trail behind either. We are happy to take on something new when the service is proven, it must be reliable.”
Discover the secrets behind how this Australian business used an IT Strategy to scale and grow
By Lanrex on 9/01/19 9:58 AM
Established in 2004, DUAL Australia Pty Ltd is a specialist underwriting agency providing innovative insurance solutions for small to medium enterprise. DUAL specialises in accident and health, financial lines, general liability, and marine insurances. The agency also underwrites exclusively on behalf of Lloyd's, a name synonymous with insurance which has an S&P rating of A+ since the late seventeenth century.
DUAL has implemented an online trading platform enabling brokers to obtain instant quotations and bindings 24 hours a day, 365 days a year. It is regularly used by over 650 broking houses across Australia and resulted in more than 30,000 policies being transacted every year. Employing more than 80 people DUAL, has four offices across Australia in Sydney, Melbourne, Perth and Brisbane.
The Business Need for DUAL Australia
The SME Team within DUAL work with brokers on a day-to-day basis on new business opportunities. Prior to January 2016, a review of their current processes highlighted areas which could be improved, particularly the recording of phone conversations, email, and meetings with brokers. They required a more comprehensive reporting method and the implementation of an efficient workflow tool.
DUAL Australia’s Key Challenges
A number of issues had to be addressed such as:
- The ability to record and track activities done by the SME Team to realise new business opportunities
- A more efficient means of updating business opportunities recorded in Excel spreadsheets and MS Access
- The lack of a centralised database containing information about all the brokers the SME Team worked with
A Workflow Strategy Solution
Lanrex was already engaged by DUAL to provide its IT services and were consulted by Frances Land, the SME Team Leader for a possible solution to address DUAL’s revised operating requirements.
To ensure Lanrex had a thorough understanding of the important issues and requirements, DUAL’s SME team worked closely with Lanrex during the implementation, testing, and quality assurance phases.
Lanrex proposed the use of Microsoft Dynamics to help the SME Team, who needed a workflow strategy tool.
Of the services provided by Lanrex, SME Team Leader Frances Land points out:
“It is a fantastic system which meets our needs and Lanrex has provided a great response to any changes we required.”
The SME Team is now able to—
- Store and access all information about its broker firms, broker contacts, and opportunities from a centralised database
- Help managers seamlessly assign and manage opportunities
- Track and view the progress of business opportunities online using the Dynamics dashboard and via various reports
- Record their own activities using a simple interface, which also enables them to monitor their own performance.
Key Outcomes & Results
Microsoft Dynamics is integrated with DUAL’s online quoting system which provides the opportunities for the SME Team to then work with the relevant brokers and track any subsequent activities.
The solution was implemented in January 2016 and was proven to have the flexibility required to meet the needs and expectations of DUAL. The big win has been in DUAL’s new ability to establish effective workflows for the SME Team to increase their efficiency and improve their results.
The interaction with Office 365 has provided substantial integration of tasks, eliminating double handling and reducing operational errors.The Dynamics dashboard with features open to all users has also stimulated healthy competition among the team members.
Frances Land complimented Lanrex on their professionalism.
“Lanrex has a really good positive attitude. They are helpful and never short of a recommendation. We do insurance, not IT, and Lanrex has a very high level of expertise.”
The Future for Dual Australia
There’s more to come from Lanrex and Dual Australia’s partnership. Lanrex is working on a number of projects with DUAL Australia to enhance and improve not only their IT but to expand this with their overall business strategy.
Lanrex's Biggest Tech Trends for Small Businesses in 2019 [INFOGRAPHIC]
By Lanrex on 18/12/18 11:26 AM
As the year comes to a close, many are looking forward to see how they can prepare themselves for whatever 2019 will bring. While some are worried, many are excited about what new technologies are going to revolutionise their businesses for the better.
If 2018 is anything to go by, 2019 will be a year of great change. We believe being on top of these trends is crucial to sustained success, that's why we have done the hard work for you and created a comprehensive list of Lanrex's biggest tech trend predictions for 2019.
Wishing you a happy and safe holiday season from everyone here at Lanrex!
Yours sincerely,
Jodie, Managing Director of Lanrex.
Essential Field Service Technology Trends to Watch Out For in 2019
By Lanrex on 4/12/18 3:45 PM
Every few years, technology advances to a place where it is once again possible to transform your service organisation from a cost centre to a profit centre and into a virtual powerhouse overnight. Oftentimes those changes start small, with a series of trends that may not look like much on their own. However, when taken together, they represent the type of positive disruption that comes along once in a generation.
2019 is certainly shaping up to be another one of those years and we're not even there yet.
In fact, there are a number of critical field service technology trends that are nearly ready to "pop" that you should absolutely pay attention to as we move into the new year and beyond. If you don't want to count yourself among the 20% of companies who will fail in their digital transformation this year, now is the time to pay attention.
Innovation Doesn't Just Drive Field Services. It Drives Everything
Maybe the most important field service technology trend to watch out for in 2019 is also one of the most broadly defined: a constant need to find new and unique sources of innovation around every corner.
In many ways, this trend has less to do with any specific type of tech and more to do with how those resources are being applied to an organisation on a fundamental level. Even when you consider a solution as sophisticated as Dynamics 365 for Field Services, it's now within your reach to effortlessly accomplish things that were literally impossible just a few short years ago.
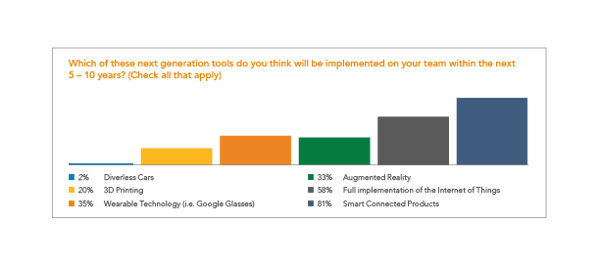
Based on that, customer expectations are changing, and your business needs to change with them. They no longer want you to do what they expect as well as you can. They're eager for you to give them something they never knew they wanted in the first place, which is why any opportunity you have to drive service innovation is one worth exploring.
With so many great technologies available, you're truly limited only by your own imagination. Rest assured, that is a very exciting position to be in.
The Era of Automation Has Arrived
Another major field service technology trend that you'll need to stay abreast of has to do with a constant push into the world of automation. With automation comes the need for greater soft skills in technicians, but that isn't necessarily something to be feared.
Automation is your perfect chance to do more with less, increasing the volume of work you're able to get done without increasing your headcount along the way.
Plus, you need to consider the breakneck pace that the industry itself is continuing to change right before our very eyes. Staying ahead of the curve is difficult when the curve is constantly changing, but by relying on automation you can make your change management processes easier and more efficient than ever before.
There are certain types of technologies that overlap with this core idea like artificial intelligence and data analytics.
But regardless of the technique you use, the end result is always the same: you're getting more for your technology budget and you're reaping the benefits of a streamlined process and better decision-making along the way.
Stop Selling Services and Start Selling Outcomes
Maybe the most important trend to pay attention to is a shift in how we think about field services to begin with. We've reached a critical mass in terms of what an organisation is able to do and instead, the competitive advantage of the 21st century is born out of how they're able to do it.
To put it another way, you need to stop selling services in the most literal sense of the term and start selling based on the value those services generate.. You need to become a true customer success organisation by making use of predictive and proactive engagement techniques.
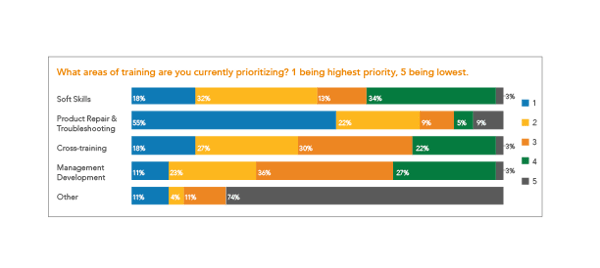
Field services organisations can no longer afford to wait for a client to have a problem, at which point they then step in and solve it. They need to take proactive steps to stop that problem from happening in the first place. Data analytics will once again play an essential role in this process, as will advanced customer relationship management tools.
This again underlines the need to rely on a solution like Dynamics 365 for Field Services that can pull all of your data together under one roof, making it available to every member of an organisation regardless of where they happen to be. Whether someone is in the office or in the car on the way to a client's location shouldn't matter — all data should be available everywhere, at all times, no exceptions.
Preparing for the Future, One Trend at a Time
At Lanrex, we understand how important it is to operate at the top of your field. It's not just about becoming the best. True success over the long-term demands that you achieve that status and keep it, which itself requires you to be as proactive about field service technology trends as possible.
Almost more so than any other industry, field services organisations cannot afford to grow stagnate. Your customers care about your ability to innovate and find new ways to make their lives easier every day, which means that you need to care about these things too.
If you'd like to find out more information about all of the most important field service technology trends to watch out for in 2019, or if you'd just like to find out more about how a trusted partner like Lanrex can help you implement Dynamics 365 for Field Services to transform your business from the top down, contact us today.
The Three Crucial Steps you need to take before a Digital Transformation
By Lanrex on 18/10/18 2:14 PM
Digital transformation is a broad term that can mean many, far-reaching things. But the start of the process is only as complicated as you make it and it is something that can absolutely work to your advantage if you play your cards right.
Yes, you're going to be making many changes to the technological foundation of your company. Yes, you're going to experience a sometimes significant level of disruption along the way. But the process itself is nothing if not logical. Provided that you start out on the right foot, you'll find that it's far more straightforward than you likely thought it was going to be and the rewards will be worth it.
Getting started with digital transformation on those terms isn't necessarily the most difficult task in the world, and luckily CEO of Lanrex and expert in technology for business, Jodie Korber has outlined the three key steps you need to take before a digital transformation.
Strategy is the Key to Digital Transformation
For the absolute best results, any digital transformation efforts should begin earnestly enough, at the strategy level. In other words, you need to be able to adequately answer the following questions before you proceed:
- What does the term "digital transformation" mean to this organisation?
- What does it actually look like, meaning what steps do we need to be taking?
- What benefits are we going to get that we don't have access to now?
- Why is it important to take these steps at this particular moment?
If you can answer those questions, you should know which direction you’re headed to — and at that point, you more or less have everything you need to get started.
"Digital transformation is about redefining a business strategy and delivering customer value, all based on the potential of digital technologies," says Jodie Korber, CEO of Lanrex.
But to get to that point, you need to have a clear understanding of your strategy as it exists today so that you can see the impact of changes in real time. You can't make any meaningful change if you don't know what change looks like, which is why beginning at the strategy phase is so critical.
The Boots on the Ground
As you begin to build out your strategy, you need to make an effort to speak to key stakeholders to understand where the problems with your current infrastructure really are. It's one thing to look at analytics and say "since we implemented X, we haven't seen the benefits in productivity and communication we thought we would." It's another thing entirely to know why that is the case.
To arrive at that insight, the solution is simple: all you have to do is ask.
Engage with all key stakeholders and find out how your current technology impacts them on a basic level every day.
- What problems are they encountering?
- What workarounds have they developed?
- What do they wish was different?
- What's preventing them from working smarter, not harder?
As you begin to speak to more and more people, you'll get a better idea of certain gaps in your existing strategy. Find out as much as you can about the problems that are on everybody's minds. What common areas and themes do these problems share?
"Digital transformation begins not with the technology, but with your business itself," adds Jodie Korber. Within the context of this particular discussion, your business and your people are one and the same.
A problem is just a question you haven't figured out the answer to yet, but the answer absolutely exists. This information shouldn't be something to be apprehensive about, it should be empowering and it should lead your way through the darkness of change. As your digital transformation is in large part designed to fill or outright eliminate those gaps, the shape that your transformation will take will more or less begin to reveal itself over time.
In terms of problem areas, "you need to identify and tackle the root causes" said Jodie Korber. "Without viable solutions built on actionable information, these problems will only repeat and compound."
The Art of Current State Documentation
Next, you need to further cement your image of where you currently stand by conducting a thorough current state documentation. By having your current business processes heavily documented in a logical and accurate way, it's far easier to evaluate key problem areas for process improvement across the board.
Not only will this once again give you a better idea of where you need to be by highlighting where you currently are, but this current state documentation will pay dividends all across the digital transformation process too.
- It'll significantly help reduce the time needed to communicate with both internal and external parties during transformation, for example.
- It'll virtually eliminate the possibility that two people will be doing the same job without realising it.
- It's a critical document that reduces the time, the effort, and the ultimate cost associated with digital transformation.
Plus, it's something that you can always refer back to in order to guarantee that you're moving in the direction you think you are. If you know where you've been and where you're trying to get to, you know how long it will take you to get from "Point A" to "Point B." At that point, it doesn't matter how long the process takes — it's going to get done, you can guarantee it.
Digital Transformation: Invest in a Better Tomorrow Today
At this point, you've done more than just get started with your digital transformation efforts. You may already have a clear roadmap outlining exactly where you're headed and, more critically, how you're going to get there. At this point, success is truly no longer a question of if but when.
If you'd like to find out more information about getting started with digital transformation or if you have any additional questions about what a solution like Dynamics 365 might bring to the table throughout this process, get in touch with Lanrex today.
Increasing Team Productivity With Technology: A Straightforward Manager's Guide
By Lanrex on 18/10/18 1:43 PM
Do you find yourself working in a more "traditional" workplace — one where collaboration is often slow and laborious? It's a question that a lot of business leaders are asking themselves these days and luckily, it's also one with an easy answer.
If the aforementioned question describes your situation, the problem isn't your people. It may be the technology they're being forced to use. In that type of situation, implementing a collaborative communications model will do more than just transform your workplace from a technological point of view. It will help your employees work together, faster, and smarter than ever before. It's an idea at the heart of digital transformation for many organisations and because of that, it's one that you'll want to pay attention to.
The process itself, however, is not as simple as flipping a light switch. It's one that must be thought out, calculated, and heavily considered at all times. Therefore, if you really want to increase your team's productivity with technology, there are a few key things you'll want to keep in mind.
1. Everything Begins With an Inventory
If you truly want to increase your team's productivity with technology, the first step you have to take involves defining what "technology" means to them to begin with.
People tend to develop their own unique ways of doing things when given enough time and more often than not these days, those ways involve various applications that allow them to work smarter, not harder. Therefore, the first step towards a successful digital transformation involves finding out what technology your team members actually like using and, more importantly, why.
- Let them tell you in their own words about why something works and what a positive difference it makes.
- Take all of this into consideration when you're making decisions moving forward. Really think about and examine the net benefit that someone gets from a particular app or solution.
- Why is it meaningful to them?
- What does it allow them to do that they wouldn't otherwise be able to?
- What would happen to them if it suddenly weren't available anymore?
Along the same lines, you also need to identify any workarounds with technology that your own team members are currently experimenting with. A workaround is something that one of your users might do — no matter how small, to get the technology to work for them instead of against them. They're essentially tricking a solution to do something it wasn't necessarily designed for or to make it easier to use, in a way that benefits them all the same.
The importance of this rests with the fact that users who create workarounds are really helping to illustrate a shortcoming with an existing solution, one that you can fix by way of digital transformation. Observe your users performing actual tasks in their work environment with a particular solution. Look for any unusual ways that the solution is being used and ask yourself "what are they trying to achieve or avoid?"
If that workaround legitimately gives them a net benefit, ask yourself how you can take that information and use it to build a better product in the future.
2. New Technology Doesn't Just Appear. It Must Be Discovered
Next, research any new technology that might be available that A) closely aligns with what your team members are trying to do and how they need to do it, and B) is legitimately better than whatever they're using right now.
Office 365 for Business, for example, is a lot more than just a productivity suite like the versions of Office we've all grown accustomed to using over the years. In many ways, it's an innovation engine and one built to empower communication and collaboration across the board.
The same is true for something like Dynamics 365, which is a state-of-the-art customer relationship management tool that can be of particular use to field services organisations in particular.
But the point is that you can't just wait for these new solutions to fall on your lap — they're not going to. You need to be proactive which requires doing as much research as possible.
3. Everything Depends on Implementation
Once you know what you need to do and why that's so important in terms of digital transformation, the next step is also the most obvious one: implementation.
To that end, you have two key options. You can choose to go with the Big Bang Method which entails doing everything all at once or the Phase in Approach, which lets you slowly make these critical changes over time. The former method is disruptive but fast, while the latter is less disruptive but naturally takes longer.
Nobody can tell you which of these two methods is the best for you. Only you can make that determination based on what your people need and, most critically, when they need it. Again, solicit their opinion and weigh the pros and cons together. If you truly want to increase productivity with technology, you cannot be making decisions in a vacuum. They're the ones who are going to be affected by your choices so let them have a say in the matter.
The Arc of Change is Powerful, Indeed
Technology is a platform just as everything else. If collaboration in your workplace is slow and laborious, it just means that your platform isn't the right one for the job at the present time. With the right changes and a thoughtfully considered digital transformation strategy, there's truly no limit to what you can accomplish together.
To find out more information about how to improve your team's productivity with technology or to get answers to other essential questions you may have, contact Lanrex today.
Four ways Field Service Organisations can operate at the top of their field
By Lanrex on 24/09/18 10:41 AM
In every industry, digital transformation is rapidly shifting what’s possible for businesses. Organisations that want to operate at the very top of their field need to embrace digital change. In this blog, we’ll explore how Dynamics 365 for Field Service can help businesses to digitally evolve. We will outline how it can help you:
- Optimise resources and schedules
- Improve communications
- Use advanced tools on-the-go
- Take advantage of the Internet of Things (IoT)
Optimise Resources and Schedules
Above all, field service organisations need to be able to match the resources at hand to the organisation’s service demands. This means managing schedules, timeframes, and workloads, so that resources are utilised optimally.
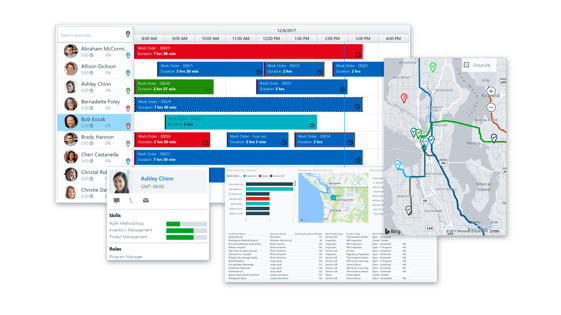 Dynamics 365 for Field Service offers resource scheduling optimisation (RSO) to make sure resources are allocated in the most effective way possible. This automated scheduling tool takes into account the skills, locations, durations, travel time, and priorities of your team and helps you schedule these so that you meet your objectives in the most efficient way. Not only does this help you fit in more appointments, you can also improve efficiency and customer satisfaction.
Dynamics 365 for Field Service offers resource scheduling optimisation (RSO) to make sure resources are allocated in the most effective way possible. This automated scheduling tool takes into account the skills, locations, durations, travel time, and priorities of your team and helps you schedule these so that you meet your objectives in the most efficient way. Not only does this help you fit in more appointments, you can also improve efficiency and customer satisfaction.
The ultimate goal is to have technicians able to assist customers on time, the first time with the right skills needed to get the job done. This is how you can deliver the most value to your customers. What’s more, drag-and-drop functionality makes it easy to manage resources and schedules in real time.
Improve Communications
Your technicians need to be able to access information and easily communicate with colleagues and customers to do the best job that they can. From accessing customer information to overcoming unexpected obstacles to crowdsourcing expert knowledge from colleagues, quick and easy communication can make the difference between a satisfied customer and a dissatisfied one.
With Dynamics 365, your technicians have access to everything they need to get the job done, including contacts, customer references, bookings, customer assets, maps, work orders, and much more. Even better, their colleagues are just a few clicks away. Technicians become much more effective this way.
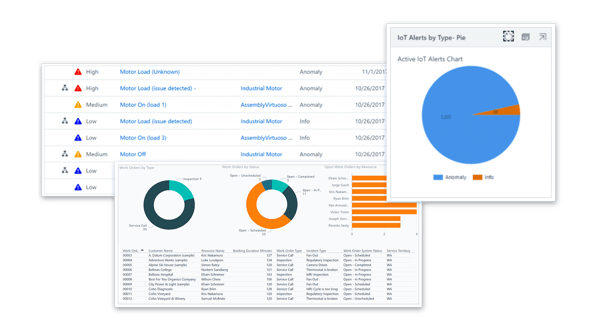
Take Advantage of the Internet of Things (IoT)
The potential of the internet of things is vast. When it comes to field services, intelligent machinery and equipment can connect and communicate with technicians and the head office via Dynamics 365 for Field Service. IoT can play a vital role for organisations that want to upgrade their costly break-fix service model and replace it with a proactive 24/7 service.
With IoT-powered machinery, the equipment you use can monitor its condition and issue an alert as soon as it notices a fault. It can even report issues before they become real problems, helping businesses avoid downtime from faulty or broken equipment.
This saves time for technicians, who no longer have to make as many trips to sites, which in turn saves money both for yourself (as technicians can work on something else instead) and for your customers (who can carry on with fully functioning equipment, avoiding downtime). Dynamics 365 can easily customise IoT alert workflows that dictate how issues are escalated at your organisation, so that you have full control over your IoT deployment.
Use Advanced Tools On-The-Go
Dynamics 365 offers field service technicians unrivalled capabilities in the field. Not only can they connect to all the information stored in the system (e.g. work orders, customer info, and more) using mobile apps, but they can leverage emerging technology such as augmented reality via the HoloLens headset.
Take Your Business to the Next Level
How your business operates is crucial. With the right technology, you can enable more efficient operations in Field Service Management. Microsoft’s Dynamics 365 brings together the functionality of both customer relationship management (CRM) systems and enterprise resource planning (ERP) systems to provide everything you need to operate at the highest level. Here is a comprehensive list of the functionality that Dynamics 365 for Field Service can offer:
- Work order management
- Schedule board and dispatch
- Resource management
- Service locations and customer assets
- Preventative maintenance
- Inventory management
- Customer billing
At Lanrex, we connect businesses with the technology they need to get ahead — and stay ahead. Our experts are focused on finding the right solutions to meet your unique business goals and requirements, so that technology becomes a business advantage.
To make the most of Dynamics 365 for Field Service, you need a partner you can trust to help you deploy the system, up-skill your staff, and offer continued support. We offer a 4-stage business diagnostic so that we can get to know your business values, long-term goals, and how your employees like to work, so that we can optimise technology solutions for you.
To find out more about Dynamics 365 for Field Service or to learn how Lanrex can help your organisation operate at the very top of your field, contact us today.
The Top Ten Technologies Transforming Field Services
By Lanrex on 21/09/18 12:07 PM
Technology and field services have always had a very close relationship, but it's also one that has certainly escalated over the last few years in particular. In an effort to increase efficiency and productivity, cut costs, and improve the quality of service that they're able to offer to their clients, many field services businesses regularly turn to modern technology to help check as many of these boxes as possible.
Along those lines, there are ten key technologies that are poised to transform field services in the not-too-distant future that are certainly worth paying attention to.
For high-performing field services organisations, these examples aren't just born out of a powerful and positive sense of disruption. Many companies are using them to grow more competitive (and more profitable) every single day and as you're about to find out, that really is just the tip of the proverbial iceberg.
1. The Era of Cloud-Based Performance Monitoring Is upon Us
Cloud-based performance monitoring, at its core, is about more than just taking a look at general metrics like productivity and efficiency. It's about bringing together both traditional and mobile tools like apps and services that your field service technicians are using, guaranteeing that they're all being used in the best ways at all times.
With cloud-based performance monitoring, not only can you instantly see trends (like technicians who are struggling to resolve problems in the field on the first try) that would have otherwise gone undiscovered, but it's also easier to uncover the best possible solution to these problems as fast as you can.
2. AI and Business Intelligence: The Perfect Match
AI-powered business intelligence solutions allow field services organisations to finally break free from the reactive, break-fix operational model they've been trapped under — taking a far more proactive approach to their daily activities than ever before. These systems automate manual, time-consuming tasks like diagnostics and data collection and identify the best solutions to issues automatically.
The types of dashboards and other reporting solutions that fall under this category don't just guarantee significant gains in terms of optimising resource management, but can also help prevent costly return visits to customers and provide stability and reliability in a way that improves that customer experience as well.
3. The Rise of Autonomous Vehicles
Autonomous vehicles becoming a ubiquitous part of our lives is a lot closer to being a reality than one might think and perhaps nobody stands to benefit from this more than field service organisations around the globe.
Autonomous cars can help boost productivity (and generate time and cost savings) with features like optimal route guidance for engineers out in the field, for example. At a certain point, it will even be possible for field service organisations to send cars with necessary equipment directly to customers for tasks that can be solved themselves — thus freeing up the time of engineers to attend to the problems that actually need them.
4. The Internet of Things Revolution
The Internet of Things, a series of countless devices that are all connected to one another and are constantly creating and sharing data over the Internet, is also poised to affect field services in a big, big way.
Not only will this allow the industry to switch from reactive to proactive repairs(when paired with the right intelligence software), but it's also a perfect opportunity to increase revenue and generate new revenue streams by allowing organisations to take advantage of opportunities in new and emerging industries. It can even enable real-time and remote diagnostics for better, more efficient services to begin with.
5. The Power of Smartphone and Tablet Software Integration
Make no mistake about it: relying on mobile technology is one of the key ways to remaining competitive for any field services organisation, which is a fact that makes smartphone and tablet software integration of paramount importance.
Embracing this trend and mobilising your field services team won't just reduce paperwork and travel time. This new level of accessibility and connectivity will allow employees the flexibility they need to better meet the needs of individual clients, will offer data insight and real-time information from any location and will again allow them to provide a better level of service to all clients, no matter what.
6. E-Payment and Billing Software: Improving Customer Experiences
E-payment and mobile billing software options are another key trend that field services organisations will want to watch out for, as they're about more than just giving technicians the ability to accept payments on-site.
They're a chance to truly revolutionise your payment collection process, allowing you to shorten payment processing time, provide more flexibility for customers, and gain better (and real-time) insight into your cash flow all in one fell swoop.
7. It's a Blockchain World
Blockchain technology, a digital ledger that records transactions in a way that is both A) visible and B) permanent, also stands to revolutionise field services sooner rather than later. This is especially true when you consider it within the context of another previously mentioned key technology, the Internet of Things.
Experts agree that blockchain will soon be critical in terms of tracking and verifying transactions that happen within IoT platforms. But with advancements like smart contracts, field service technicians can automatically execute events such as getting an engineer into the field or shipping a part, as a part of that original transaction.
8. GPS Tracking for Fleet Management: Visibility to Spare
GPS tracking is not a new concept, but many people are still unfamiliar with the major benefits it brings to the table for fleet management in particular.
GPS tracking and smart scheduling solutions with real-time traffic updates can not only guarantee your drivers are always using the most efficient routes, but this in turn lowers fuel costs, increases the overall productivity of your field services, and helps empower your bottom line — all at once.
9. The Next Step in the Evolution of Customer Relationship Management
Customer Relationship Management (CRM) solutions like Microsoft Dynamics CRM Field Service also bring with them a host of unique benefits that are far too powerful to ignore.
Not only do they offer features like intuitive, visual, and highly flexible drag-and-drop scheduling boards for resource allocation, but they again have strong mobile capabilities like native mobile apps and offer features like automated scheduling and routing optimisation for maximum efficiency. Once again, this is the perfect chance for your entire team to work "smarter, not harder" in a way that your customers (and your bottom line) will greatly benefit from.
10. ERPs: Putting the Power Back in Your Hands
Finally, we have Enterprise Resource Planning systems or otherwise known as ERPs. The goal of an ERP is to unlock total visibility across your entire field services organisation from a single, simple platform that is always available from anywhere, at any time, no exceptions.
Not only will this help streamline the day-to-day manual tasks that field techs have to go through that often prevent them from focusing on real customer issues, but all data entered into the ERP is also accessible from any device. It's again a way to support the mobility and productivity of your technicians, which itself allows them to focus as much of their attention on your actual customers as they can.
The Future is Already Here
The best part of all is that a lot of these key technologies are already here, you just need to have the right solution by your side to access them. Dynamics 365 for Field Services, for example, already offers cloud-based performance monitoring, AI and business intelligence, the Internet of Things, and sophisticated CRM and ERP capabilities all in one incredibly convenient and forward-thinking package.
Not only is a solution as robust as Dynamics 365 for Field Services your key to taking advantage of key technologies like these, but it's also your best shot at guaranteeing that you wind up exactly where you need to be once this transformation of field services is finally complete.
If you'd like to find out more information about these or other key technologies, or if you've just got any additional questions that you'd like to see answered, contact Lanrex today.
The Truth about Culture: Five Ways Technology Can Transform Your Team For the Better
By Lanrex on 25/08/18 12:55 PM
In a lot of ways, the effort to create a better, more holistic, and more positive company culture is one of the important decisions that one can make as a business professional. Immediately, it creates a ripple effect in the best possible way:
- The immediate impact is that it creates employees who are more engaged with their jobs.
- It gives way to higher levels of employee satisfaction, which makes it easier to attract and retain top employees.
- This effect flows directly into productivity, which improves not only the volume of work that your employees are able to do but the quality as well.
- The process then gives way to the most important benefit of all: significantly increased customer satisfaction.
But in the 21st century, it is critical for you to understand that positive company culture is about a lot more than just human interaction. You're not going to be able to generate these results by taking your employees out for Happy Hour a few times a month. Instead, it's all about the combination of technology and human behavior.
If your culture strategy is going to be effective in the way that you need, technology for business needs to be integrated into it on a cellular level in the way that your employees deserve. In fact, there are five core examples of the way that technology can transform your team for the better that are absolutely worth exploring.
1. Enterprise Social Networks: Your Ticket to Building Better Relationships
One of the major opportunities that technology brings with it to help transform your team for the better comes by way of enterprise social networks — a kind of social media platform that is essentially just for you and your employees. A number of companies have experimented with this technique to great effect. Atos is just one example, who deployed their network blueKiwi totally in-house across 76,000 employees and not only helped create better relationships and empower collaboration, but also helped the organisation achieve its zero email ambition as well.
But the underlying point is simple. By giving people a tool to collaborate and communicate with that resembles social services that they're already using in their personal lives, their inter-office relationships take an immediate step in the direction of intimacy and personality as a result. Not only does it bring people together by giving them an easy and efficient tool to communicate with, it literally brings them together as individuals as well.
2. Communication is King
Along the same lines, technology can have a tremendous impact on a company's culture by creating an environment where communication isn't just open and honest but also a two-way street. If organisational leaders embrace technology to empower communication, it makes employees more likely to offer their valuable insight and expertise in a wider range of situations.
This includes giving critical feedback to leaders in an environment that’s free from judgement and consequence.
- By not only enabling this criticism but also taking it in stride, leaders help empower a workforce that isn't just afraid to speak out, they also grow to accept failure as well.
- Instead of avoiding failure altogether out of fear, they begin to recognise it as an opportunity.
- Fear isn't to be avoided. It's to be embraced, as it's the foundation upon which future successes are built.
3. File Sharing and Collaboration Are the Name of the Game
As so much of our work is done digitally these days, it stands to reason that you want to make it as easy as possible for people to share files and collaborate on any projects they may be engaged in. Tools like Sharepoint are designed to do precisely that, leaning into the virtue of 21st century technology while also creating an environment where collaboration is absolutely the path of least resistance.
Essentially, file sharing and collaboration tools like Sharepoint and many others are all about breaking down the manpower silos that previously existed in most enterprises. In a lot of ways, it uses one of the tried-but-true principles of marketing that works to your immediate advantage:
- If you make it as easy as possible for someone to take your desired action, they will.
- These types of tools make collaboration among team members effortless, which not only helps people actually participate,it brings them closer together as team members and makes them want to collaborate in the first place.
4. By Enhancing the Employee Experience, You Enhance the Customer Experience As Well
Over the last few years, a massive amount of research has been conducted that all leads to the same basic point: if you focus on creating a better, more valuable, and more holistic employee experience, those same benefits will be extended towards your larger customer experience. By giving employees the technological tools they need to work "smarter, not harder”, they naturally become more engaged with their jobs as a result.
If you make an effort to create a workforce of happy, healthy employees in this regard, those benefits naturally extend to their own relationships with your customers as well. This not only leads to businesses that are more competitive than those who don't rely on technology for business in this way, but it also creates organisations that are far more profitable as well.
5. Transformation Starts With the Top and Moves Its Way Down
Finally, another one of the ways that technology can impact your team has to do with the concept of digital leadership — one of the key points to successful digital transformation and a better company culture at the same time.
Think about it like this: a digitally mature leader creates the example to follow for every member of an organisation. Leaders who define what digital innovation means and why it's so important, and who also drive their own efforts in that direction, create an environment where it's easier for employees to deliver a consistent engagement and service experience to customers regardless of channel.
- Through leading by example, these leaders help to broaden the thinking of all employees, helping them understand why digital skills are essential and how to use tools effectively.
- They use technology to improve the lives of employees exponentially by breaking down knowledge and language barriers.
- They help create clearly defined roles, which themselves bring benefits like better accountability, governance and agility.
- They don't just communicate the direction an organisation is headed in. They literally act as the light that shines the way through the darkness.
Putting the Revolution to Work For You
Despite all of this, technology for business on its own is still just a platform and just as it has always been. Without employees who are willing to leverage it, who recognise its power and who see what it can do for them as a collective, you won't be able to get anywhere near the point where you need to be to remain successful over the next decade. That in and of itself begins with your company culture and the significant, positive, and powerful impact that it can create almost immediately.
If you'd like to find out more information about how technology can transform your team for the better, or if you'd just like to discuss the benefits of a solution like Dynamics 365 with someone in a little more detail, contact Lanrex today.
Three great examples of IT Strategy (and one surprising one)
By Lanrex on 9/08/18 8:02 AM
One of the best things about modern technology is that it's malleable. The IT infrastructure at the heart of your organisation can essentially be anything you need it to be. However, this also represents one of the biggest challenges that comes with any digital transformation effort — there's truly no one-size-fits-all approach to what you're doing and the idea that there is one right way to approach these efforts is a myth.
Embarking on a digital transformation without an IT strategy is a bit like setting out for a road trip without a map — you may have a vague idea of where you want to end up, but the chances of you actually getting there in one piece are slim to none.
What is an IT Strategy?

This is, in large part, why an IT strategy roadmap is critical to your organisation's success. It's a term used to describe a very particular type of governing document that dictates in no uncertain terms how your technology will support your business strategy, and drive your business priorities, over the next few years. It includes not only a strategy statement but also key elements like:
- A timeline of initiatives and projects that you will undertake.
- A prioritised list of opportunities for improvement.
- High-level justifications for any, and all decisions.
- The estimated cost and duration for each stage of the digital transformation.
Although there is no one right way to do any of this, there are certainly a better paths to take. With that in mind, consider the following four examples of great IT strategies from organisations of all shapes and sizes. Note that these are not things that you should try to replicate literally in your own organisation, but they do provide valuable insight into the types of elements that your own IT strategy roadmap must contain.
1. The University of Oregon: A Digital Transformation in the Education Space
The focus of UO's own strategy quickly became an effort to “improve academic and research excellence”, which is noble but also required officials to totally rethink how IT services are provided across such a major educational institution in the first place.
The university's unique approach to an IT strategy was held up by four core pillars:
- Governance: They emphasised a way to not only consolidate their existing IT infrastructure, but doing so in a way that addressed the needs of individual academic areas and IT staff members as well.
- Leveraging Resources: Their strategy was built around the idea that IT resources are limited and short-term initiatives were created to help conserve those resources.
- Investments: They recognised that significant investments were critical to help guarantee that the new IT infrastructure was successful in the long-term.
- Transformation: Acknowledging that this is a long-term process, UO made sure that every element of their IT strategy was A) realistic, B) measurable, C) repeatable, and D) easy to update so that key stakeholders could track progress on a long-term basis.
In the end, The University of Oregon was left with a strategic planning process that allowed itself to be continually updated as new challenges develop, which is something that all organisations, regardless of industry, should focus on.
2. UES: Leveraging Tomorrow's Technology, Today
Another example of a terrific modern day IT strategy comes by way of UES, a company that found it increasingly difficult to manage their own in-house hardware and systems as the infrastructure around them continued to grow and evolve.
Recently, key decision makers at UES recognised that the time was right to move their own servers, many of which dated back to 2004 and ran Windows 2003 to a data center. The outdated technology they were working with, however, made this move less than successful.
- Because their technology was so outdated, certain core upgrades could not be done.
- A current version of SQL was not compatible with their existing environment.
- This had particularly challenging ramifications for their critical ERP (enterprise resource planning) system.
UES quickly decided to partner with Lanrex, who helped them migrate the entirety of their IT infrastructure to the cloud utilising not only Amazon Web Services, but also Microsoft Office 365. In the end, they were left with a solution that was 100% hosted in the cloud using Citrix XenApp technology and AWS. They were able to enjoy a number of core benefits on top of the ones they were after in the first place, including:
- Significantly lower upfront capital costs.
- A much faster setup and configuration process for their servers.
- Lower capacity risks.
- Reduced monthly maintenance costs.
3. Harvard University: Breaking New Ground Today, Tomorrow, and Beyond
Last but not least, we have another educational organisation, Harvard University. Not only is their IT strategy the perfect example to follow for businesses of all types because it was an important part of their efforts from the very beginning, but it also includes broad representation across all areas of the university.
Harvard's IT strategy was successful because it not only took a "big picture" approach by truly bringing anyone and everyone into the fold and giving them an important seat at the table, but it also had sections for elements like the following:
- Key university priorities
- Existing strengths/weaknesses to be addressed
- Trends in higher education
- Next steps that pave the way for a continued evolution moving forward
In the end, what Harvard was left with was the perfect way to both meet the demands of today and better prepare themselves for the challenges of tomorrow too, which is ultimately what any IT strategy should be able to do.
The Surprise: Beyond Bank Australia: A tech revolution for a company evolution
Since originally establishing itself as a modest credit union in July of 2013, Beyond Bank (then known as Community CPS Australia) got to a point where they knew they needed to do something different. In an ongoing effort to continue to improve the customer experience whenever possible, the organisation recently made history by being the first bank anywhere in Australia today to implement the next generation of business intelligence tools namely Dynamics 365, with its own partner, UXC Eclipse.
Robert Aitken, Beyond Bank's CIO, indicated that they needed to go above and beyond the normal. To do this, they introduced a unique group of tightly coupled business applications like Dynamics 365 to accomplish a few important goals, essentially all at the same time. The main objectives of this were:
- Finding a way to improve staff productivity
- To embrace new opportunities in order to make their own internal processes more efficient.
- Create the most exceptional customer experience in the market.
Any one of these goals would be a challenge, to say nothing of how difficult it was to tackle all of them in tandem. But with the solid foundation of Dynamics 365 upon which to build on, Beyond Bank was able to continue their digital transformation into a value-tuned business that focused equal parts on the needs of their customers and delivering an unforgettable customer experience.
Below is a screenshot of the dashboard used by Beyond bank:
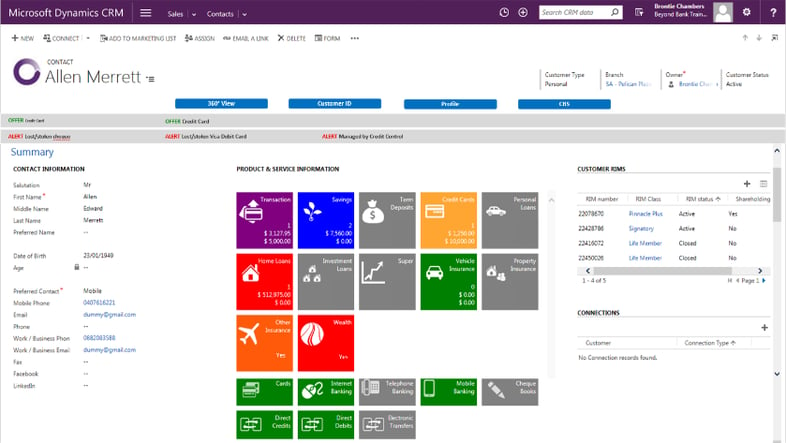
Staff members use Dynamics 365 to obtain real-time data from core banking processes and applications and now have a total 360-degree view of every customer under their care.
Want to know more about IT Strategy?
Lanrex: Your Partner in Digital Transformation
As these and other examples show, IT may be powerful, but at the end of the day, technology is just a platform. The platform itself is less important than what that platform allows you to do. Without the right IT strategy at your side, you'll never be able to break free from the myth of the one-size-fits-all approach to technology to develop something that truly meets the needs of your organisation on a cellular level, as well as acts as the engine to drive your entire business forward into the next decade and beyond.
If you'd like to find out more examples of the core elements of a great IT strategy, or if you have any additional questions that you'd like to see answered, contact Lanrex today.
Looking for a Managed Service IT Provider? Here Are 8 Questions You Need to Ask
By Lanrex on 24/07/18 8:35 AM
Business leaders are often in a bit of a precarious position when it comes to technology. On the one hand, they need to make sure that they’re giving employees access to the tools they need to do their jobs in the best possible way. On the other hand, it’s also literally their job to focus on the quantitative measures of how technology benefits their business in terms of ROI — two goals that can often seem at odds with one another.
Over the last few years, many companies have turned towards the managed service provider to meet both of these goals at the same time. They’ve found a tremendous amount of success in doing so. But just like the technology itself it’s important to understand that there is no “one size fits all” approach to this decision.
Before you make that crucial decision, here are the 8 questions you need to ask when looking for a managed service provider:
-
Is a Managed Service IT Provider the right choice for the right time?
-
What is your Engineer-to-Customer Ratio?
-
How Malleable Are the Services that You’re Offering?
-
How Long Has Your Company Been Around?
-
Do You Have Experience in My Industry?
-
What Is Your Support Process Like?
-
What Documentation Do You Provide?
-
Do You Offer Remote and On-Site Support?
- Is a Managed Service IT Provider the Right Choice for the Right Time?
Before you can get started finding the right MSP for your business, you must first make sure you understand what you stand to gain from such a relationship. As the name suggests, an MSP is a technology services provider that both manages and assumes the responsibility for providing a specific set of services to your client.
In essence, in exchange for a single predictable monthly fee, you get a defined set of network, application, system, and even e-management services piped directly to your network on a “pay as you go” basis.
It is by far a more efficient way to stay on the cutting edge of technology, but to be fair, you will be giving up a certain level of control over your environment. You’re no longer responsible for researching equipment, procuring it, installing and maintaining it — someone does all of this for you.
- What Is Your Engineer-to-Customer Ratio?
Once you’ve determined that hiring an MSP is the right step to take, this is one of the first questions you should ask. Part of what you’re paying for is dedicated support — that’s hard to do if an MSP has 200 engineers trying to provide real-time support to thousands upon thousands of customers at one time. For the best results, try to find an MSP that actually has more accredited, certified engineers than it has customers.
- How Malleable Are the Services that You’re Offering?
This essential question plays directly into why a managed service IT provider is such an attractive proposition in the first place. The right MSP won’t just provide you with a service — they’ll also help design and deploy services that are optimised with how you actually plan to use them in mind. Don’t pick an MSP that provides you with access to the public cloud and leaves you on your own. Find one who will go the extra step and help you create a solution that is built with your team in mind.
- How Long Has Your Company Been Around?
Newer MSPs tend to be smaller — pointing to a lack of business experience necessary to actually handle all your organisation’s needs. There’s nothing wrong with a young company on the rise, but depending on what you need and how you need it, this may not be the best fit for your specific business at this time.
- Do You Have Experience in My Industry?
Different industries have different rules and regulations that they must follow in terms of IT, particularly when it comes to hot-button topics like security. The MSP you’ll work with needs to not only understand how you plan to use technology but how it must be used in the industry you’re actually operating in. If you’re a healthcare organisation, don’t pick an MSP without healthcare experience.
- What Is Your Support Process Like?
When you’re talking about technology, when something goes wrong, it’s not a question of “if” but “when”. If you encounter an issue, you need to know that your MSP will be there for you regardless of the time of day. Find out how they handle after-hours support requests, whether or not they offer true 24/7 support and more.
- What Documentation Do You Provide?
Records keeping is incredibly important when it comes to IT. Always find out whether or not a particular MSP documents the work they’re doing so that you have accurate, comprehensive records to refer to should you ever need them. This not only provides visibility into your relationship, but it helps prevent recurring issues from happening in the future.
- Do You Offer Remote and On-Site Support?
Finally, always ask about whether an MSP offers both remote and on-site support should you ever need them. Certain problems will require face-to-face time with a certified IT professional — there really is no getting around that. When you find yourself in that situation, you need to know if the option is available or if you’re going to be paying an inflated price for it because it falls “outside the scope” of your agreement.
If you still have any additional questions about picking the right managed service IT provider for your business, or if you’d like to sit down and discuss with an expert whether an MSP is the right move in the first place, you’ve come to the right place. Please don’t hesitate to contact Lanrex today for more information.
The Top Trends Transforming Field Services
By Lanrex on 24/07/18 8:01 AM
On a surface level, field services can mean a large number of different things and happening all at the same time. It's about putting resources in place to guarantee better, more preventative, and more predictive maintenance for your customers. It's about assisting them with installation and commissioning wherever possible. It's about business consultation, performing an invaluable critical analysis of one's business needs and demands so that you can help people better align their technology with their own long-term goals.
But more than anything, it's also about creating a true experience for your customers — one that allows them to dwell less on their own problems so they can focus more on the solutions they're trying to create for themselves. As is true with so many others these days, it is also an industry in the brink of transformation. In fact, there are five key trends in particular that are emerging in the field services space right now that you need to be aware of moving forward.
Field Services is Experiencing a Tremendous Amount of Growth
Maybe the biggest trend in field services today is also the most important. The industry itself is growing exponentially, and showing no signs of slowing down anytime soon. In fact, one recent study predicts that by 2022, field services alone will be worth a massive $4.45 billion. To break things down a bit, a lot of this growth will come by way of two main elements: scheduling and dispatch. Based on that, it's clear that these are the parts of your own field services that you should be focusing on today to get ready to meet the challenges of tomorrow.
Field Services is More Mobile Than Ever
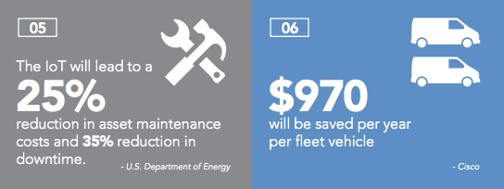
Along the same lines, it should come as no surprise that field services is getting increasingly mobile with each passing day. A lot of this is propelled by the impending onslaught of the Internet of Things (IoT) — an idea that describes a situation where nearly every device is no
t only connected to the Internet and creating data, but sharing that data with other devices. Wearable technology like smart-watches also plays a big role in this.
But even smartphones alone are making a significant impact in this area. Another study estimates that over 75% of all field services providers with more than 50 users will rely heavily on mobile apps by the end of 2020.
Field Services is Becoming More Automated
The human side of field services will always be critical. However, another recent trend has also seen the industry itself become more automated on a regular basis. Businesses that rely on automation in their field services unlock a host of different benefits and all at the same time. For starters, automation is an excellent way to reduce costs across the board.
It's also a way to empower workers, generating gains in productivity and creating more accurate and consistent experiences as well. But most importantly, automation is a perfect opportunity to free up valuable time from your employees so that they can devote their attention to more pressing, forward-thinking ventures.
Field Services is Embracing AR and VR
If you had to make a list of all the industries that have been impacted by the arrival of both augmented reality and virtual reality, field services would be right at the top. As this technology becomes both more affordable and more powerful on a regular basis, companies are making use of it in a lot of unique ways.
It's a great way to give field services employees a tangible, hands-on experience with certain environments and sites, for example, even if they never actually leave your office. This alone is a perfect opportunity to guarantee that they have the experience they need when they get into the field to ensure first-time fixes as often as possible.
Field Services is Getting Smarter
Finally, as is true with so many other industries these days, the current state of field services is absolutely empowered by smart technology and all of the benefits that it brings with it. Gone are the days where field services employees could get by with a reactive approach to their job because there will be no more situations where you can wait for something to break and then fix it.
Smart technology has allowed people to be incredibly proactive especially when it comes to the key assets they're tasked to maintain in the first place. Not only does modern technology enable better, more organic, and more predictive maintenance but the use of big data can also help with everything from resource allocation to improving the return on investment of one's own clients.
This, in turn, has created a situation where field services as a concept may be even more important to your own customers today than it was a decade ago. It's also created a perfect opportunity to help your own field services department become the true profit center that it was always meant to be.
Lanrex: Your Partner in Field Services
In so many ways, a lot of your success in terms of field services depends on your ability to stay ahead of the game. The world around us is changing all the time and you need to remain agile enough to change with it or get left behind.
At Lanrex, we're in an ideal position to help you leverage the full power of Dynamics 365 along with other aspects of your digital transformation to guarantee that your team is always at its best all day and every day — no exceptions.
If you'd like to find out more information about the emerging trends in field services, or if you have any additional questions that you'd like us to answer, contact Lanrex today.
Images courtesy of:
The 5 Step Guide to Make your Workplace Cyber Safe
By Lanrex on 17/07/18 12:48 PM
Hackers (and the tools they use to harm your business) are getting faster, smarter, more efficient, and more sophisticated all the time. This means whether you like it or not, you need to do the same.
In 2015 alone, cybercrime cost businesses a combined $3 trillion all over the world. By 2021, that number is expected to climb to more than $6 trillion, pointing to a problem that is only going to get worse before it gets better. If the best defense is a good offense, you need to take that idea to heart and take the necessary steps today to fend off disaster tomorrow.
With that in mind, there are five easy steps that you can take immediately to help guarantee that your workplace is more secure, allowing you to focus a little less on cybersecurity and more on running your organisation the way it should be.
1. Upgrade Your Existing Software Now
This piece of advice may seem simple, but its ultimate importance cannot be stated enough. Think of software updates as the digital version of a flu shot for your computer. When you get a flu shot, you're essentially upgrading your body's ability to fight off the latest (and most powerful) versions of the Influenza virus.
Software updates are no different, guaranteeing that you're equipped with all of the latest patches, bug fixes, and security upgrades necessary to ward off all the latest strains of viruses, malware, and other cyber threats. If you're using software that can no longer be updated, which means that it is no longer supported by the original developer, it's time to look for an alternative.
You always need to stay one step ahead of hackers and make no mistake, this is one of the major ways to do it.
2. Change Those Passwords
Nobody likes to have to come up with long, complicated passwords filled with numbers, letters, and special characters every couple of months. However, it's critically important since exploiting weak or compromised passwords allows hackers to gain access to your system in the first place.
Get in the habit of changing your passwords at least once every six months, and make sure that all of your employees do it, too.
Along the same lines, always incorporate two-factor authentication when possible. This will make sure that you always need two forms of input to log into your accounts, so even if your actual password is compromised you're still protected as long as your secondary device hasn't been compromised as well.
3. Set up and enforce Standard Operating Procedures
One of the most important ways to guarantee that your workplace is more secure involves coming up with standard operating procedures, or SOPs, for all of your digital devices and sticking with them above all costs. These are rules that all employees, yourself included, need to follow.
Are your employees allowed to use devices with USB sticks? What type of data are they allowed to take home with them? What are your protocols for accessing work email from home? What sites can they go on using the Internet and what sites can't they?
What happens to account authentication once an employee leaves? Your business has Wi-Fi. Do you think of yourself as a bring-your-own-device (BYOD) organisation, or aren't you?
How is device management handled in a field services situation versus when all employees are on-site? These are the types of questions that your SOPs need to answer and the consequences for breaking them need to be just as severe as the potential stakes for getting this wrong.
4. Backup Everything as Often as You Can
As a general rule of thumb, you should always backup your important data to both the cloud and to another secondary, physical form.
All of this should be set up to occur automatically, so you really don't even have to think about it. If your business gets hit by something like a ransomware attack, being able to immediately restore from a current and quality backup is one of the best (and only) chances you have of coming out of the situation unscathed.
5. It's All About Training
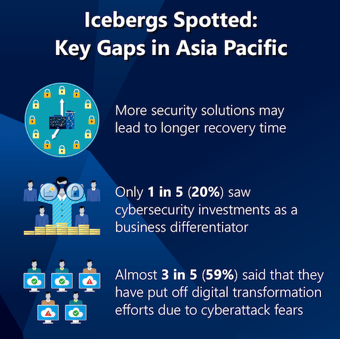
At the end of the day, one of the most important things for you to understand is that technology is ultimately only as good as the people who wield it. Therefore, it is absolutely in your best interest to make sure those people are as smart, as forward-thinking, and as experienced as possible.
Ongoing education should be a major priority for your business both in terms of making sure people actually know how to use the tools you're giving them and helping them stay ahead of all the latest threats like suspicious websites and emails. Experts even agree that ongoing employee training is one of the keys to fortifying your cybersecurity defenses, particularly since employee error is one of the major ways that networks become compromised in the first place.
If you're not already making employee education and ongoing training a priority, now would be an excellent time to start.
Lanrex: Because Cyber Security Is Too Important to Ignore
Whether you're in the middle of a major digital transformation (like switching to Dynamics 365) or just want to make sure that your organisation is protected from all of the latest threats, Lanrex is proud to stand by your side every step of the way.
We are committed to being a true security partner for your organisation in every sense of the term, doing our part to help you enjoy all of the benefits of modern technology with as few of the downsides as possible.
If you'd like to find out more information about how to guarantee that your workplace is more secure, or if you have any additional questions that you'd like to discuss, contact Lanrex today.
The Case for Servitization: Operate at the Top of your Field
By Lanrex on 26/06/18 8:08 AM
At its core, Servitization is more than just digital transformation. It's about reinventing the manufacturing business model from the ground up, using the lessons learned up to this point to build something better, meaningful, and forward thinking across the board.
It's safe to say that in an era where manufacturing equipment is getting more complicated every day, end users are turning to their dealers for expert guidance more frequently than ever. Servitization plays directly into this concept, allowing manufacturers to sell both a product and a genuine solution at the exact same time.
Dynamics 365, Microsoft's own product line of ERP and CRM applications, can help your organisation take full advantage of this trend moving forward. In fact, there are four key ways that your field services in particular will improve in a post-Dynamics 365 world that are certainly worth exploring.

It's About Building Better Relationships
There is no doubt that the growth in technology over the past decade has led to changing relationships between you and your customer. New technology now gives you a chance to guarantee the continuous interaction you need to build better customer relationships moving forward.
Gone are the days where the only time you'll interact with a customer is when it's time to upgrade or replace something you've already sold them. The rise in the Internet of Things is about to bring with it an era of ongoing communication and interaction.
With Dynamics 365, it is now possible to deploy new revenue streams like remote monitoring in a much more cost effective way. As a manufacturer, you have more visibility into the ongoing performance of your assets and your customers than ever before. Dynamics 365 can help you actually do something with that new visibility, creating new offerings that would have been unthinkable even a decade ago.
This won't just change the dynamic between you and your customer, it will strengthen it and cement it for a different generation.
Unlocking New Opportunities to Innovate
According to one recent study conducted by Aberdeen, 54% of respondents said that the Internet of Things was directly responsible for the creation of new product and service offerings for their business. This is because using solutions like Dynamics 365 makes it possible to gain valuable insight into your products in the field thanks to the real-time data you now have access to.
You're in a better position than ever to service equipment before a failure occurs. You can improve future products and services based on how your customer needs are changing, which you can see happen as it occurs. You won't have to worry about failing to recognise a trend in your industry or getting left behind because you'll see it coming as soon as possible. This won't just give you a chance to adapt, it'll present a genuine opportunity to take full advantage of it.
Dynamics 365 Can Help You Better Prepare for the Internet of Things
Part of the reason why servitization has gained such traction in such a short amount of time in the first place has to do with the Internet of Things, or the IoT for short. According to one recent study, there will be over 50 billion things connected to the IoT by as soon as 2020. In the manufacturing space, in particular, this will include industrial sensors, advanced RFID tags, beacons, and just about everything else you can think of.
All of these devices won't just be connected to the Internet, they'll be connected to one another — creating, sharing, and analysing massive volumes of data every single day. From a field services perspective, your business model is about to move from reactive to predictive, if it hasn't already. According to Microsoft, servitization and Dynamics 365 is the perfect opportunity to get ready for that, allowing you to actually process, analyse and make use of this huge influx of new information while using it to generate new service-driven revenue streams along the way.
Figuring Out What Your Customers Really Care About
But in the end, maybe the most important way that concepts like servitization and solutions like Dynamics 365 will improve your field services is in helping you discover what your own customers truly care about.
Regardless of the specific problem or challenge that a customer is facing, they want a quick, simple, and efficient solution. It is up to you to give it to them. Thanks to servitization, you're now in a better position to focus less on the product and more on the outcome that product is supposed to bring with it.
This in turn gives your field service element an opportunity to implement both the delivery model and the technology required to meet those customer needs, regardless of how they happen to change or evolve over time. In the end, this creates the most important advantage of all: a situation where your own company is always more relevant in the lives of your customer tomorrow than it was today. Rest assured, this is a very exciting position to be in moving forward.
Lanrex: Enhance Your Tech to Transform Your Business
At Lanrex, we've committed ourselves to helping businesses just like yours implement Dynamics 365 so that you can enjoy all of the benefits of the best technology.
If you'd like to find out more information about how your field services will improve with Dynamics 365, or if you'd just like to discuss the specifics of your own situation in a little more detail, contact Lanrex today.
4 Ways Dynamics 365 can Transform your Field Service Results
By Lanrex on 13/06/18 8:08 AM
At its core, Dynamics 365 is more than just another ERP or CRM tool. It's a great way to effectively break down silos that used to exist between these two disparate concepts, finally allowing them to come together to form a single and critical pillar of your organisation. It's a truly intelligent business application in every sense of the term, built to allow you to make better, more informed, and more actionable decisions on a daily basis.
It's also a tool that has a number of interesting implications for your Field Services in particular. Rest assured that if you're the type of business that has a modest focus on on-site installations, field maintenance, or any related services, there are various ways Dynamics 365 can help improve your business.
Dynamics 365 for Field Services: Improving Outcomes Across the Board
Even with a cursory glance, it's clear that Dynamics 365 may just be the solution to your Field Services problems. It's a tool built from the top down with better outcomes in mind, allowing you to not only build agility into your everyday operations in a way that allows you to organically grow and evolve over time, but also in terms of improving worker visibility across production and customer engagement, enhancing collaboration between locations and across teams and much, much more.
We at Lanrex have compiled what we believe to be the four major ways Dynamics 365 can help guarantee all of this and more for your Field Services.
1. It's About Optimising Your Resources
One of the major ways that Dynamics 365 and Field Services seem made for each other has to do with the better, more holistic way that you can now optimise your resources for the unique tasks you have at hand.
Solving a business challenge always comes down to having the right assets available for the right job at exactly the right time and with Dynamics 365, that goal is easier than ever. Drawing from the massive volumes of data that your organisation is already creating, scheduling can not only be improved, it can be almost totally automated.
This guarantees that you always dispatch the right technician to the field as quickly as possible, guaranteeing that you're getting the most value out of your resources, all while allowing you to focus more on the jobs that actually move your organisation forward.
2. The Power of a 360-Degree View
Along the same lines, once those technicians have been dispatched, Dynamics 365 provides all relevant customer information (history, preferences etc…). This allows your technicians to gain what Dynamics 365 calls “a true 360-degree view of your customers”, putting them in position to be more effective than ever.
Again, Dynamics 365 makes all data available to everyone, anywhere, at any time. This means that even in the field, your techs are in an excellent position to offer true real-time guidance to customers — improving resolution times as much as possible and earning their trust in a lasting way.
3. Your Field Service Will Be More Proactive
The 360-degree view feeds directly into another way that Dynamics 365 can help improve your Field Services: the proactive level of support and care that you're now able to provide. The Internet of Things and powerful business intelligence can now be used to gain insight into your Field Services in a much deeper way than before.
Using the myriad of different features present in Dynamics 365, your techs are now in a better position to proactively detect issues, troubleshoot those issues, and resolve problems both big and small. When taken together, this means:
-
You will now only have to dispatch a technician when it is absolutely necessary, so you'll save time and money that way.
-
Those techs will still be able to offer, better, real-time guidance to improve resolution time as outlined above.
From that perspective, you're truly dealing with something of a perfect storm. Not only are you sending out techs less frequently, but the techs you are sending out are in a position to do better work in a more effective way. It is truly a win-win scenario.
4. Everything Comes Back to Customer Engagement
But in the end, perhaps the most critical way that Dynamics 365 can help improve your Field Services is the opportunities that you now have to engage with your customers more.
Do you want to be able to provide your customers with self-service portals? Now you can. Do you want to start creating a bigger emphasis on more proactive updates? It's never been easier.
As a business leader, do you want to be able to ensure a positive experience at every step and via every interaction? Thanks to Dynamics 365 and technician tracking, all of this is available to you. Service experiences don't just become easier, they become effortless.
This is just a taste of the many different benefits that only Dynamics 365 can bring to the table in terms of your Field Services. But even when you consider these advantages alone, it's clear that this is one solution you'll soon wonder how you were ever able to get by without.
Lanrex: Your Partner in Dynamics 365
As an industry-leading provider of a wide range of Microsoft products including Dynamics 365, the team at Lanrex are prepared to do whatever it takes to bring you all of the advantages of a thoughtfully executed digital transformation with as few of the potential downsides as possible.
If you'd like to find out more information about the major advantages that only Dynamics 365 can bring to the table, or if you'd like some assistance implementing these services across your own organisation, please don't delay — contact Lanrex today.
How to prepare for Cloud Migration in 5 Simple Steps
By Lanrex on 30/05/18 8:08 AM
The many unique advantages and opportunities of migrating to the cloud are starting to be realised by small and medium-sized businesses across a broad range of industries. For starters, cloud computing allows your organisation to enjoy a significantly improved level of IT resource management almost immediately. In addition, you'll also gain access to increased mobility, a more thorough level of IT insight, and you'll have an easier time carving out a competitive advantage for yourself.
But understanding why it's important to migrate to the cloud is one thing. Guaranteeing the best possible cloud migration is absolutely possible — you just have to make sure that you're preparing it the right way to help you better tackle the types of challenges you're likely to face tomorrow.
If you're considering making the switch to a cloud-based infrastructure, here are five essential steps you should take to prepare your business for a successful cloud migration:
Step 1: Start With Your Goals and Work Your Way Back to the Cloud
When it comes to actually preparing for cloud migration, perhaps the most important thing for you to do involves getting your point-of-view in order. Simply put, technology is just a tool — even when you're talking about something as powerful and as far-reaching as the cloud, the tool itself is less important than what it is you can actually do with it.
Because of that, you cannot start with the cloud and try to build a bridge to the problems you're trying to solve or the goals you're trying to accomplish. You need to start with those challenges and those goals and work your way back to the right cloud implementation that will allow you to meet those needs in the best way possible for you and you alone.
Step 2: Choose a Quality Cloud Provider
Once you are keenly aware of what your own specific needs happen to be, you can start looking for a cloud provider that will actually be able to meet them. This involves choosing a quality cloud server, which itself requires you to keep a number of things in mind.
Microsoft Azure is one of your many available options, acting as a platform built to increase your business agility across the board. Azure has a fully integrated delivery pipeline (that includes an IDE, or integrated development environment), offers great features in terms of backup and disaster recovery and much, much more.
Amazon Web Services (or AWS) is an equally viable option for many businesses. But again, there is no objective right or wrong answer to this particular decision. It's not about choosing the best provider, it's about choosing the best provider for you at this particular moment in time.
Curious about the Cloud? Check out our free E-book:
Step 3: Backup Your Data — As Quickly as Possible
The importance of backing up all of your data before you begin your cloud migration is something that cannot be overstated enough. A cloud migration represents a significant period of change. Where there is change, there are variables that act beyond your control and those variables often lead to risks you cannot predict.
Because of that, everything should be backed up BEFORE the migration begins to guarantee that you don't lose even a kilobyte of essential data. If you do, you can ensure the data will be safe and easily retrievable. This step will also help make sure that your important business processes do not fail as the migration carries on.
Step 4: Communicate, Communicate, Communicate
Whenever your business goes through a period of change that is as significant as this one, oftentimes your ability to succeed will live and die based on your ability to properly communicate.
Every single aspect of the migration needs to be communicated clearly and often with all key stakeholders, from decision makers to employees and everyone in between. What you're doing, why it's important, what value it's supposed to generate, what you need people to do at any given moment — all of this should be crystal clear to avoid confusion, human error, and disruption.
Visualizing your infrastructure will help a great deal in this regard, as it often gives you a chance to look at the big picture approach to the migration from any given stage. It can help you better predict how your applications will actually perform in the cloud, it can help you better understand how much those applications will cost in the cloud and it can help reduce costs by as much as 48% in some situations when compared to companies that don't actually take this step.
Step 5: Know When to Partner With an MSP
Finally, in order to better prepare for cloud migration you need to be able to recognise when the time is right to enlist the help of a professional. Whether you're using a managed services provider to execute the entire transition or just want to keep them around as a backup, they can often offer solutions that are far easier (and not to mention less expensive) than doing things yourself.
Remember that when it comes to a successful cloud migration, getting it done is far less important than getting it right. Sometimes, working with an MSP will be the only way to guarantee that actually happens.
Lanrex: Your Partner in Cloud Migration
At Lanrex, we believe in the full power that only cloud migration can bring to the table — both in terms of supporting the business you're running today and with regards to allowing you to grow and evolve into the one you want to be running tomorrow. In addition to acting as a trusted MSP, we can also provide Microsoft-related services (including those associated with Microsoft Azure) and more.
If you'd like to find out more information about how to properly prepare for cloud migration, or if you have any additional questions you'd like to discuss, please don't delay — contact Lanrex today. If you're looking for a little more, feel free to sign up for your free technological consultation so that we can work towards identifying new and innovative ways that we can use to put technology to work for you.
Still Confused about the cloud? Check out our comprehensive Cloud 101 Guide:
Phishing Attacks: What They Are, Why They're Dangerous, and What You MUST Know
By Lanrex on 18/05/18 8:08 AM
Make no mistake about it: cyber crime is on the rise and this is one unfortunate trend that shows absolutely no signs of slowing down anytime soon. In 2016, there were 4,000 cyber attacks that specifically targeted businesses per day — and this only takes ransomware into consideration.
But with so many different attacks coming in various directions, it can be difficult for even the most seasoned business veterans to know where to begin in terms of cybersecurity. Oftentimes, they forget about one of the most common and dangerous types of threats currently out there — phishing.
During a phishing attack, a hacker or someone else with a malicious intent will try to obtain sensitive information about your business by pretending to be a reputable entity. Someone posing as one of your clients may send an email to one of your employees, asking them to log into a specific website, or provide their credentials for some reason. Should the employee take the bait, suddenly that hacker has access to your network — and every last kilobyte of confidential data contained within it.
But thankfully, all hope is not lost. It is possible to successfully fend off every last phishing attack that you and your team may encounter. You just have to keep a few key things in mind.
Phishing Awareness Could Not Be More Important
Because of the nature of phishing attacks, the importance of raising awareness about this technique with every last member of your workforce is something that cannot be overstated enough. These are the single most widespread, prevalent form of cyber attack in existence, and have been for eight years in a row.
Keep in mind that phishing attacks are simple, yes — but it’s brilliance also lies in that simplicity. Phishing attacks remain popular with hackers all over the world because it works impossibly well.
Consider the following statistics to get a better understanding of the situation you may now face:
- According to one recent study, phishing attempts have grown at a rate of 65% in the last year alone.
- Based on this study, it makes sense that 76% of businesses report to being a victim of phishing during the same period of time.
- According to a comprehensive study conducted by Verizon, about 30% of phishing emails get opened by the target victim. Out of those, about 12% of people actually click on the malicious attachment or link contained inside.
- Webroot Threat reports that there are almost 1.5 million new phishing sites created each and every month, all over the world.
But the most damning statistic of all is undoubtedly the following: the average cost of a phishing attack on mid-sized companies is a staggering $1.6 million. The real costs can easily run in the tens of millions of dollars — an expense that can easily drive even the strongest business straight into the ground.
Different Types of Phishing: Breaking It Down
To complicate things even further, there is no one type of phishing attack that you need to be aware of. In fact, there are many. These include:
- Spear Phishing. In this type of situation, a hacker will — including information like the victim's name, their position, your business' name, and even proper phone numbers. This is all in an attempt to trick someone into believing that they have some type of connection with the person who sent the message.
- Whale Phishing. This is a lot like spear phishing in nature, but it's almost always targeted at wealthy, powerful, or prominent individuals. If one of your employees becomes a target of a hacker, that's spear phishing. If your CEO becomes a target, that's whale phishing.
- Vishing. This is essentially the telephone version of phishing, where hackers will use social engineering techniques against you in an attempt to provide sensitive information that you would otherwise protect.
- Clone Phishing. This is what happens when someone is directed to a website that looks like a legitimate one, but that is really a carbon copy designed to steal whatever sensitive information the victim provides.
Yes, all of this is complicated and yes, none of it is good. But there is positive news about phishing that you can start putting to good use today.
Phishing is Absolutely Preventable
Phishing is absolutely preventable in the vast majority of all situations, but you need to make the most proactive effort possible in order to do so. Make employee training on phishing and other types of cyber threats a top priority. Teach them about the different types of phishing that they might encounter, how to spot a fake email, how to confirm that they're talking to who they really think they're talking to and things like that.
Every time you bring a new employee into the fold, have them go through the same training. As new types of attacks occur, make everyone go through the updated training all over again. If you give employees the skills they need to defend themselves from these threats, they will be able to do so.
Lanrex: Because Digital Transformation Shouldn't Be Dangerous
Likewise, it is important to invest in the types of cybersecurity solutions necessary to stop these attacks before they become a much bigger and more expensive problem down the road. Even if an employee opens a phishing email, downloads, and executes a rogue attachment, that shouldn't bring your entire network to its knees — and with the right cybersecurity infrastructure in place, it won't.
This is why many organisations around the world are choosing to work with managed service providers on a regular basis. Your MSP can handle all of your cybersecurity concerns and defend you and your employees against phishing, ransomware, and anything else, so that you can get back to actually running a business the way you're supposed to.
If you have any additional questions about how to defend yourself and your business against phishing attacks, or if you'd just like to talk about why partnering with an MSP might be the right move for your business in a little more detail, please don't delay — contact Lanrex today.
Why a Resistance to IT is Really a Resistance to Success
By Lanrex on 30/04/18 10:00 AM
Regardless of the type of
Many have IT systems in place, but they do not focus enough on them. They see them as a "necessary evil" instead of "necessary," plain and simple. What these people often do not realise is that this makes them far more likely to suffer from the types of inefficiencies (not to mention cyberattacks) that hold them back instead of propelling them forward.
The fact of the matter is that your IT strategy and your larger business strategy were always the same
In truth, an investment in IT is actually an investment in the current and future success of your company for a host of different reasons that are absolutely worth exploring.
You're Artificially Decreasing Your Own Efficiency
Perhaps the biggest reason why a resistance to IT may be setting your organization up for failure has to do with the natural inefficiencies that you're actually enabling as a result. In the best case scenario, your IT infrastructure should be built in such a way that allows for the natural technological automation and optimization around your core business processes.
Essentially, IT must become a strategic tool that not only allows for efficiency in a sense of working "smarter, not harder", but also in terms of creating opportunities for better and faster customer service, unlocking more actionable insight about the market you're operating in and more.
Case in point: the data silos that often exist as a result of both an over-reliance on legacy systems and a lack of integration across the board. Even when you're talking about something as simple as your sales team and your marketing team existing in two distinct silos, you're doing something greater than just making it hard for those teams to share information with one another.
You're limiting their ability to work together to organically address customer needs at all points of the sales funnel. You're locking out the insight you need to respond to changes in your market as they happen. You could be spending more money to guarantee worse results and the worst part of all is that you're happy about it because you still think that "disruption" has an exclusively negative connotation.
You're Under-Utilizing Critical IT Assets and Infrastructure
Along the same lines, another one of the major consequences of a resistance to IT has to do with the idea that you're paying more money for IT assets and infrastructure that you're only using to a fraction of their true ability.
Every year that you put off digital transformation is another year that you're paying more money for storage capacity, server performance, server capacity and much, much more. Whenever you bring new employees into the fold, you have to jump through a number of unnecessary hoops in order to add these people to your infrastructure - and the labour costs associated with this alone continue to be the single biggest issue for many organizations across the country.
You're at an Increased Risk of Cyber Security Breaches
Make no mistake about it: the digital era that we're now living in is getting more dangerous every year. There were 1,579 publicly disclosed data breaches in 2017, a massive 44.7% increase from just a year earlier. In order to protect your business, you and your IT teams need to be as proactive about cyber security as possible.
It's not enough to wait for something bad to happen and then do what you can to recover. The consequences are far too severe in an age where the average cost of a data breach has reached $3.62 million. You must work to avoid these issues altogether if you're going to survive into the next decade.
You Will Experience Major Difficulty Recovering From Those Breaches
This leads directly into the final reason why a resistance to IT is a resistance to success: you're making it harder for yourself to recover from those aforementioned data breaches.
The current environment paints a scary picture - this is no longer a matter of "if," but "when.". If you choose to resist IT and ignore implementing the right systems, you may be actually going out of your way to make this problem worse than it needs to be.
Think about it like this, even the IT environment is growing increasingly complex, which means that the number of weak points is rising. As time goes on, there are more opportunities for someone to breach your defences.
When this type of problem occurs, there is also less time between A) the occurrence of the attack or failure, and B) the impact of that event on your larger business operations. This means that you have less ability to react
All of this is a nightmare scenario for most business leaders - but it's one that you can mitigate and often outright avoid altogether if the right IT infrastructure is in place from the jump.
Lanrex: Because a Partner in IT is a Partner in Success
The fact of the matter is that IT is about more than just having access to the latest that modern technology has to offer. When your IT infrastructure is created properly, it can be utilized in a way that allows you to accomplish all of your desired business outcomes in an easier, effective and a more affordable way than ever before. IT is a platform, yes - but it's also an asset, and it's time to start treating it that way.
This, in essence, is why partnering with the right MSP to fit your needs is so critical to your long-term strategy. Whether you're looking for help with the procurement of equipment, handling connectivity issues like
If you'd like to find out more information about why an investment in IT is really an investment in your organization's success, or if you have any additional questions you'd like to see answered, please don't delay - contact Lanrex today.
Is Your IT Team Focusing on What's Important to Them Rather Than What's Important to the Business?
By Lanrex on 10/04/18 3:13 PM
If your IT infrastructure is not meeting your business needs and enabling the business objectives you're after, it can often seem like this is for a wide range of different reasons. Sometimes you feel like you've invested in the wrong solution at the wrong time. In other instances, you may feel like the assets you're working with are so new that you're just not set up to utilise them properly.
However, while these may seem like separate ideas, they're really not. In truth, they all lead back to the same basic core: a disconnect between the perceived role of IT as an 'internal utility' versus what it really is, a key player in your overall business strategy.
The Danger of Disconnection
Oftentimes, this can take the form of an additional symptom. Your IT team, the people in charge of steering the ship so to speak, are focusing too much on what is important to THEM as opposed to what is important to the business they're trying to serve.
This is nobody's fault. If anything, it's emblematic of the old-school approach to information technology that is still firmly entrenched in many businesses around the world. But if you're really going to drive the outcomes you need and empower collaboration and higher productivity while achieving other benefits along the way, you have to bridge this gap as soon as you can for the benefit of all involved. Doing so requires you to keep a few key things in mind.
The Myth of IT vs Business
There's a reason why three of the most important ingredients for a digital transformation include time, vision, and a willingness to drive necessary change in the first place. They're all required to actually integrate IT into your business, rather than simply viewing it as a new set of toys to play with.
To truly get your IT team to stop focusing on what's important to them and start thinking about what’s important to your business, you need to make sure that these two concepts are one and the same through communication and collaboration.
This type of collaborative comms generally starts at the very top of a business, with senior executives and other key stakeholders setting goals and creating strategies to make sure that an overall vision is properly communicated across an enterprise. People don't just need to know what you want them to do, they also need to know why. They need to know what benefit they'll receive and, in turn, how that funnels back into the business. This is truly how you create a viable all-hands-on-deck approach that is absolutely necessary for digital transformation.
Much of this will come down to the definition between core and non-core activities. A core IT need will vary depending on the business you're trying to run, but it ultimately leads directly into what it is that your business actually needs from IT. This is one of the major reasons that companies often choose to work with third-party providers like an MSP in the first place. By moving non-core or non-essential tasks into the cloud, the IT team is free to focus on the things that the business really needs — those that will actually move it forward instead of preserving the status quo.
Another key factor to focus on during this time comes down to a matter of perspective. Technology should be treated as a potential business growth engine, as opposed to being just an afterthought.
Both your IT and upper organisational leaders need to see a real need behind every action. All steps taken should legitimately improve a business, including the way it functions and the ease at which it connects to the world around you in a real, tangible way. Anything that doesn't meet that requirement probably shouldn't be a focus in the first place.
This is also likely going to require a major shift in your overall governance model, but rest assured that this is for the better. Make the decision points around not just emergent technology, but the strategy, the planning, and the implementation of the said technology. Again, this all feeds back into knowing what is a core or essential activity and what isn’t. This type of approach to governance will help you focus on action instead of reaction, and it will allow you to put plans in place to not just implement technology but integrate it, tackling the organisation and communication requirements necessary to integrate IT into your business instead of piling it on top.
Ultimately, this is how business outcomes aren't just generated, but guaranteed.
Lanrex: Your IT Solutions Experts
At Lanrex, we often find that the biggest hurdle when it comes to executing a successful digital transformation is ultimately one of perspective. Your IT team wants to be able to work smarter, not harder, yes — and you should want this for them. But only by making an effort to guarantee that your technological strategy is properly aligned with your long-term objectives as a business will you be able to generate the outcomes you need when you need them the most.
To find out more information about why your IT is not meeting your business needs, or to discuss some of the other challenges that you're facing in greater detail, please don't delay, contact Lanrex today.
Culture May Be Your Number One Obstacle — Does Your Team Embrace Change or Fear It?
By Lanrex on 22/03/18 9:43 AM
The importance of culture within a company is certainly not a new idea. In fact, it has the potential to affect nearly every aspect of your organisation, both positively and negatively, at a moment's notice. Take turnover rate for example. One Columbia University study shows that the turnover rate at companies with a strong culture is just 13.9% versus the 48.4% at companies without one.
Productivity is also directly affected, as the Department of Economics at the University of Warwick discovered that happy, engaged workers are 12% more productive than average employees, while those who are unhappy and disconnected are actually 10% less productive.
But it's important to understand that your company culture can be a technically strong one and still have the potential to affect your organisation in negative ways. Case in point: if you feel like your road to essential digital transformation has been a rocky one, the culture you've built is likely your number one obstacle whether you realise it or not.
Your Culture Is a Reflection
Digital transformation doesn't just rely on a willingness to change, it requires it. But if your teams don't embrace change or innovation and instead fear them, your IT infrastructure will quickly grow stagnant dragging your business along with it.
On another hand, this type of change is naturally scary; after all, something as far-reaching as digital transformation often has immediate and dramatic ramifications on the jobs your employees are doing on a daily basis. Yet at the same time, it's also exciting — or at least, that's how people should see it. This is something that you're all going through together, and it's something that will make everyone stronger both individually and as a unit.
Never forget that if you truly want to improve performance and empower growth, you need what only IT can offer you. To achieve this, you need employees who are willing to embrace technology, and understand the need for it enough to support it rather than run from it.
You need to be able to move your entire company from the former perspective to the latter as soon as you can and doing so will require you to keep a few key things in mind.
The Art of the Change Culture
To turn your company's culture from your number one obstacle into your top asset, you need to start by building a "change culture" in the first place. You need to have a vision for what your IT infrastructure looks like and what it can do for your organisation. Utilise collaborative comms to your advantage.
Share that vision far and wide and make sure that people know not just what you want to do but why you want to do it. Make them see what's in it for them and how it will allow them to do better work, spend less time focusing on administrative tasks, and be able to genuinely improve their lives each day.
But more than that, remember that one of the major reasons people fear change in the first place is because disruption has become something of a dirty word. It shouldn't be. Break your vision down into a series of smaller, more manageable chunks. Keep it simple, yet strategic. You're not trying to accomplish one goal with digital transformation, you're trying to accomplish many smaller ones.
At that point, the process itself becomes a self-fulfilling prophecy. Not only is it personal to your team, but every time one of your smaller tasks is checked off the list, the gratification that people get will generate its own momentum and will carry you all farther down the line towards completion.
Be the Change You Want to See
There are a number of additional steps that you can take to help make this transition as easy as possible. Many companies choose to partner with a managed service provider or MSP during this time. Not only can they help create a custom IT architecture to meet the specific needs of your business, they can also train employees on how to effectively engage with this new setup.
As the old saying goes, "nothing in life is to be feared, it is only to be understood." An MSP can be an invaluable partner in terms of transforming a stagnant company culture that shies away from IT disruption into one that embraces the innovation and integration that it affords.
Another key step that you can take involves looking for opportunities that you can integrate in many other different ways, too. For example, you can create an extensive internal tech setup (your MSP can also help you with this) built on the foundation of Microsoft's Enterprise offerings. Show your employees that solutions like Word, Excel, PowerPoint, Outlook, and others are all powerful individually, but they're even more important when taken together.
In a lot of ways, Microsoft's Enterprise is a perfect metaphor for everything that you're trying to accomplish in the first place. If you can get them to buy into this smaller idea, which involves equipping them with the right infrastructure and right skills, you can get them to buy into anything.
At that point, a culture that embraces change is no longer a question of ‘if but ‘when’.
Lanrex: Your Digital Transformation Partner
At Lanrex, we understand that technology is ultimately just a platform. What you choose to build with that platform is up to you, but investing in the latest in modern technology purely for the sake of it is never the way to guarantee the outcomes you need when you need them the most.
Only by approaching IT as a foundation from which to build something stronger and ultimately much more powerful, and by empowering your team to embrace digital change instead of fearing it, will you be able to create the genuine results you need moving forward.
To find out more information about why culture may be your number one obstacle on the road to digital transformation, or to get more information about how to embrace change in general, contact Lanrex today.
If You’re Standing Still, You’re Going Backwards
By Lanrex on 6/03/18 2:25 PM
Your business has stopped growing at the rate you need and you don’t know why. Your revenues have plateaued or worse— have begun to decline and you can’t reverse the trend. You’re not bringing in nearly as many new customers as you used to and the ones that you have aren’t nearly as loyal as they once were.
These are all very common business problems, especially for aging organisations. But ultimately, they’re all born out of the same place.
You’re no longer the innovator that you once were. You’ve grown complacent. Instead of doing the disruption, you’re the one being disrupted. If you don’t act fast, you might not recover.
The digital era has brought with it an almost unprecedented amount of disruption in a relatively short amount of time — and not necessarily in ways that people could have predicted a decade ago. If you told someone in 2005 that one day cell phones, digital cameras, GPS devices, digital music players, and portable computers would one day become the same device and be small enough to fit in your pocket, they would have said you were crazy. Yet here we are — in a time when most Australian adults own a smart phone.
The Internet of Things is poised to do it all over again, and sooner than you think. By as soon as 2020, there will be more than 50 billion devices connected to the Internet and the conditions are right for digital newbies to topple traditional giants in a virtual battle of David versus Goliath.
But again, there is a major difference between being disrupted and doing the disruption yourself. One of these two ideas causes all of your business problems, while the other is a sure-fire way to solve them. Understanding the differences between these two ideas is your key to surviving the next five to ten years and beyond.
The Danger of Spinning Your Wheels
If you want a clear-cut example of why you should absolutely welcome disruption with open arms, look no farther than Kodak. In 2005, Kodak essentially reached its peak — it was not only ranked number one in digital camera sales in the United States, but it had a massive 40% market share that amounted to a $5.7 billion business.
Soon, however, two incredibly important things happened and Kodak essentially tried to ignore both of them until it was far too late. First, Kodak failed to realise just how quickly digital cameras were becoming commodities with low profit margins. At one point, they were literally losing $60 on every camera sold.
Then, in 2007, Steve Jobs walked across a stage in California and introduced a little device called the iPhone to the world. Suddenly nobody wanted a standalone digital camera anymore — now they could use a mobile phone with a built-in powerful camera that they can carry around with them in their pockets at all times.
Kodak tried a number of different strategies to rebound over the next few years, but it amounted to too little, too late — the company filed for Chapter 11 bankruptcy protection in 2012.
Suddenly, a company that was once on top of the world found itself as yet another in a long line of victims of the digital era that was upon us.
Ultimately, Kodak fell into the same trap that far too many business leaders find themselves in — they were too focused on the strength of their own success as opposed to the needs of their customers. This is ultimately an efficient (and poetic) way to illustrate the difference between ‘disrupting’ and ‘being disrupted’.
Companies that pay attention to trends can hear what customers are trying to tell them and see where things are going. They can execute the often dramatic but always necessary changes to traditional business models that they need to stand the test of time.
Those who can’t usually won’t. It really doesn’t get much more straightforward than that.
The Art of Controlled Disruption
There are a few key qualities that nearly every disruptive company that you can think of shares:
- They are able to understand customer trends before they actually become fully-formed trends. After all, as Steve Jobs once said, "a lot of times, people don’t know what they want until you show it to them."
- They tend to focus on smaller markets first, serving overlooked segments while growing at a pace they need to eventually tackle larger ones.
- They always refine their business model before their product. If you focus on creating a solid business model first, you can create the products to match.
- They focus on customers in a way that turns them into loyal, passionate fans. The strength of those fans then carries them onto bigger and better things.
These four traits encompass the essential qualities of controlled disruption. To put it another way, it takes a long time to become an overnight success.
But even going beyond that, working on becoming disruptive does more than just increase your chances of success in an incredibly crowded marketplace. It can improve your overall business efficiency at the exact same time. Think back to the example of Kodak — had they focused on being disruptive, they would have seen earlier that it was a problem that they were losing $60 on every camera sold — regardless of how popular digital cameras were at the time.
Now, think about a company like Netflix. It may be hard to remember now, but Netflix originally started as a simple ‘DVD by mail’ business before pivoting into streaming content and then streaming their own content. While streaming video sites had existed before Netflix, they identified a customer need very early on in the digital age and took advantage of it at every turn.
Sure, there are a lot of streaming video sites right now, but there is only one Netflix.
You Have a Choice to Make
The most important thing to understand about all of this is that disruption does NOT have to be the dirty word that a lot of professionals seem to want to make it. With the right perspective, it isn’t only healthy for a business of any age or size — it’s practically a requirement. Make no mistake — once you’ve hit a stasis, the majority of your efforts are devoted to simply maintaining the status quo. At that point, you’re doing worse than just standing still. You’re moving backwards, whether you realise it or not.
Disruption can and should begin with taking a look at your customers, identifying the problems they face and the potential ways in which you and you alone can solve them. Provided that you’re beginning from this rock solid foundation, rest assured that the capabilities, the technology, and even the products will follow through.
Is an Archaic IT Infrastructure Hindering Your Business Success?
By Lanrex on 22/02/18 10:20 AM
Is your IT infrastructure holding your business back? In today's rapidly evolving world, asking this question is essential to growth. Having the right technological infrastructure is imperative to a business' success. Nowadays, it is no longer a viable solution for businesses to rely on rigid and uncooperative IT.
Gone are the days when using a waterfall system produced the optimal results. Instead, as IT has advanced, the time has come for businesses to move into an age where a technical architecture is both responsive and agile, so that your business can grow at the rate it needs to.
With this in mind, perhaps the right question to ask is, "how can I change my technical architecture to respond to changing or growing business needs?"
The Benefits of Choosing the Right Technical Architecture
The challenge of rigid IT is that it can cause businesses to operate at slower speeds. When your IT lacks flexibility, you are unable to reduce travel costs, eliminate hardware expenses, meet rigid compliance regulations, or achieve the mobile parameters needed for conducting business on a global scale. In short, outdated IT architectures reduce the overall ROI of your business, while simultaneously causing frustrations amongst your employees.
Fortunately, there are solutions such as Microsoft's Enterprise offerings. The Microsoft Enterprise suite is built to deliver the support and maintenance needed to deliver the optimal results for growing businesses. With the help of a Managed Service Provider (MSP) you can stop feeling as if your company's IT choices are hindering your ability to succeed. Instead, you can enjoy working with a team of experts who understand your pain, know how to implement the right solution, and can help you enjoy the following benefits of a technical architecture that is built for growth and speed.
- Improved technical migrations to provide increased efficiencies, reduced overhead, and lowered costs. As your business grows, so too will your technical needs, which is why your chosen IT architecture needs to be scalable to meet both current and future business needs.
- Quality customer support to avoid the “printer fails to print” dilemma, or the “why isn't my email syncing with my devices” conundrum.
- Speaking of email, Microsoft Office provides a fully virtualised email and file-sharing server that provides secure access via the cloud. Multiple levels of security, including the Office 365 Message Encryption, help keep your vital business communications safe from prying eyes.
- Proven disaster recovery services are automatically implemented to secure vital business data in all types of unexpected conditions.
- Achieve a higher ROI with improved business communications, courtesy of Skype for Business. Studies show that businesses can save upwards of $100,000 USD in three years when they use Skype for Business to conduct web conferences and video calls. This handy feature also has an integrated connection to a user's Outlook and SharePoint accounts to eliminate outdated and cumbersome file-sharing processes in favour of a streamlined approach that reduces meeting times and increases communication efficiencies, all to generate a higher ROI.
It isn't a secret that we live in a world where mobile is often considered the linchpin to a business' success. However, we also live in a world where digital security must be paramount, if we are to protect our vital business data from falling into the wrong hands. Office 365 leverages the power of a secure cloud-based infrastructure that is designed to give your business the flexibility that it needs to access data via a secure network from any approved device. Whether you want to use your tablet or desktop, smartphone or laptop, the cloud component of Office 365 ensures that you can streamline communications, stay up to date at all hours of the day or night, and, most importantly, maintain the security of your data.
By leveraging the right technical architecture you can move away from a rigid and uncooperative IT into a world where your IT is agile and built to respond. This transition can be aided by the Office 365 cloud-based infrastructure to result in the following benefits:
- Reduced costs associated with expensive hardware updates and maintenance.
- Lowered capital cost associated with leasing or purchasing required hardware for in-house data storage solutions.
- When compared to other data storage formats, the Office 365 secure cloud-based infrastructure shows an average of 40 percent savings over five years for most businesses.
- Lower the time, stress, cost, and operation interruptions of having an internal IT team consistently complete server refreshes.
The Bottom Line: Let an MSP Guide Your Business into the Future
Don't let a rigid and uncooperative IT infrastructure slow you and your business down. Instead, with the help of a trusted MSP, such as Lanrex, you can bring your business into the future. Enjoy all of the ROI-enhancing benefits that an agile and responsive technical architecture has to offer. Isn't it time that you stopped wondering why your current IT was slowing you down? It’s time to make a change and benefit from the efficiencies and speed that the right IT solution can provide.
Is Your Traditional Workplace Making Collaboration Slow and Laborious?
By Lanrex on 8/02/18 12:47 PM
As the owner or CFO of a small- to medium-sized business, it must be frustrating when you see how difficult it is for members of your staff to form temporary groups for collaboration on projects. At times, it seems like the process is too slow and laboured to be practical. But what other alternatives do you have?
The key to effective collaboration is open and easy communication. You can get started with collaborative comms today once you get an overview of what they mean for your business processes.
Information technology professionals use the term ‘collaborative comms’ to refer to software developed to assist a group of individuals to work together toward a common goal.
It relies on high-speed connections between computers, tablets, and smart phones and often includes a cloud-computing component. Collaborative comms are an extension of an earlier concept known as unified communications, which UC Strategies defines as “Communications integrated to optimise business processes.”
A collaborative comms solution will support your team by letting them share files and engage with one another in real time via voice calls, video conferencing, text messaging, and many other communication pathways.
Once deployed, you will witness a digital transformation in your company. With employees finding it much easier to stay on the same page and work together, they will waste less time getting together. The result is they can devote resources more quickly toward common projects, and that’s good for your company’s bottom line.
Deploying a Solution for Communication & Collaboration in Your Business
Your employees will appreciate it when they find out you’re going to adapt collaborative comms in their work environment. Depending on the demographics of your workforce, it’s possible that many younger employees are already accustomed to collaborative comms systems.
For example, according to a recent article at Real Business, “Millennials expect their employers to provide collaborative communications tools to enable them to be productive wherever they are, and our data suggests that collaborative working is something they excel at.”
Collaborative comms include virtual meetings held via videoconferencing systems. What makes them particularly useful is the inclusion of instant chat and the ability to share documents with one another. Your team can also use collaborative comms to share their screens so they can work together even when they are not in the same physical location.
For those who could not attend the meeting live, they can view recordings at their convenience as well as access notes exchanged during the conference.
If your company’s expansion plan calls for an increased number of employees working remotely and even in different countries, collaborative comms will be necessary lest you fall behind other businesses that know how to connect their workers more intelligently.
A salesperson racking up big deals on the road can continue to participate in a strategy meeting with people from headquarters and other remote locations via collaborative comms instead of having to come back early just to be in the same room as the other participants. This translates to more sales and less time wasted in conventional meetings.
Reduce Low-Level Work for Your IT Staff
You can give your IT department a break if you deploy your collaborative comms solution via cloud computing.
“Growing popularity and adoption of cloud computing is also assisting the unified communications and collaboration market growth with organisations preferring cloud-based solutions to affordably migrate their communication processes over cloud platforms,” noted a report from Global Market Insights.
Since the IT staff will no longer have to project how much server space they’ll need to accommodate growth (the cloud computing services provider will take care of this for them), they can devote themselves to more pressing concerns.
You’ll be at a competitive advantage over businesses that host their own software because they stand to lose more in terms of downtime and budgetary miscalculations about their growing hardware requirements.
A managed service provider (MSP) can also be a good alternative, especially if you think your internal IT department could be slow to transition. MSPs have industry-leading experience and will take the time to figure out your business’ unique needs. They’re usually cheaper than an internal IT department too.
Benefits of a Collaborative Comms Setup
A range of benefits will come your way once you establish your own collaborative comms system, including:
- Improved employee satisfaction - Give them better tools and morale will improve.
- Video conferencing - A picture paints a thousand words, so you can communicate more effectively when you can use gestures and facial expressions instead of just your voice.
- Find my phone - Automatically send a call to your office landline and then switch over to your smart phone if you can’t pick up within a few rings.
- Better customer service- When you can provide customers faster access to the right person in your company, you can expect them to appreciate the service and remain loyal to your brand.
Bringing Your Company into the Modern Era of Communication & Collaboration
If your organisation fails to establish a better system to allow staff to communicate freely, you cannot expect to do well in situations that call for collaboration. What’s more, if you’re not pursing a modern solution for communication, you can assume that your competitors are pulling ahead.
Instead of giving your rivals an edge, it would be prudent to build a use case now for installing collaboration tools such as Microsoft 365 and getting your team on-board to use it on a consistent basis.
To learn more about harnessing collaboration tools or to speak with experts about how collaborative comms can lead to a digital transformation of your business, get in touch with Lanrex today.
Internal Threats: Are Your Employees Emailing Data Outside?
By Lanrex on 17/10/17 9:39 AM
As you continue to adopt the new technology that barrels toward businesses of every size, you have probably started to discover the accompanying risks that tend to follow on technology’s heels.
Make no mistake: joining the digital age is vital to the success of your business, but the connectivity of technology is fraught with threats of data breaches and other risks that could cause the exposure of your company’s sensitive data — including confidential information about your customers and employees — to criminal elements.
Sometimes data breaches are strictly the work of relentless hackers from around the world. However, sometimes the threat is far closer to home. Sometimes your employees — most often unintentionally — create the very risks that might endanger your business.
Do Your Employees Understand the Risks?
Perhaps you have noticed an uptick in notifications of vulnerabilities, or your organisation has suffered a damaging data breach. Under either of those circumstances — or ideally, just as a matter of prevention — it may be time to make sure your employees understand the need to comply with appropriate email messaging practices to protect your company’s digital assets.
Developing a set of policies and guidelines, based on known risks that could lead to risking your company’s reputation and expensive legal costs, is a good way to help your employees understand the risks of emailing data outside your business and how they can help to avoid them.
Why Is It So Crucial that You Find Solutions?
Foremost, it is important to create and enforce a code of computing conduct with which everyone complies to ensure data security across the board. Besides letting you rest easier without worrying about a virus or some other systemic invasion, it is simply good business practice to lay out expectations of behaviour to employees and have them follow through.
There are a few additional key reasons to develop solutions that are unique to your organisation to allow you to optimise engagement and get your house in order so that emailing data outside is no longer a worry.
-
Numerous Vulnerabilities Lie in Wait for Your Organisation’s Computing System
Sometimes it is difficult to imagine all the possible vulnerabilities that may threaten your company’s data, particularly when the threat is on the payroll.
Think about a few of the following most commonly experienced data perils you may face when your employees let their obligations slip:
- Password Attacks. Almost 99 percent of organisations and home users continue to rely heavily on passwords as a means of authentication to allow entry to their email accounts, cites TechGenix. There are many ways that password usage may leave your business open to risks, such as through insecure maintenance of the password system, poor or insufficient password selection by employees, or the network transfer process itself.
- Data Leakage. Unencrypted and unfiltered emails can lead to data leakage, which has become a common threat in both private industry and government organisations over the past several years. It is estimated that employees unintentionally cause more than 90% of the data leakages.
- Malware. Many employees may think that malware is only a risk when visiting certain websites. However, there are a few unique ways that a virus can work its way into a computer via a rogue email. Most people are familiar with the much-publicised email attachment method, wherein the cyber-criminal attaches an executable file that, when the program is clicked to open or download, it begins to do its damage. The other way that malware poses a risk when emailing is through rich text, which may be exploited to send unauthorised messages.
- Phishing Attacks. Phishing attacks made their first appearance in 1995 and have undergone several iterations since that time, but do not be complacent; phishing is still aroundand shows no signs of disappearing. These digital data attacks prey on the trusting nature or distractedness of email recipients. These particular hackers pose as a legitimate institution when sending out an email to lure individuals into easily providing sensitive data, such as personally identifiable information (PII), banking and credit card details, and passwords.
With so many potential threats to your data, it may prove challenging to keep your employees up-to-date on the ever-evolving nature of these risks and how you can all mindfully and actively work to avoid them.
-
Some Businesses Require a Certain Level of Data Security to Engage in Business
You may have certain business associates or third-party service providers that insist on certain levels of data security, such as cloud-based insurance broking software providers. Such programs you select for your organisation may involve considerable exchanges of sensitive data via email and other methods that may leave both your business and theirs vulnerable to attacks.
Avoid losing out on valuable business associations by shoring up your emailing protocols.
How Can You Ensure Consistently Appropriate Emailing of Digital Assets Outside Your Business?
In some circumstances — and given the awful tenacity of hackers who continually search for new ways to infiltrate systems — it may seem like all the training sessions and reinforcement memos in the world may not reach certain staff when it comes to emailing data outside the firm.
There is a bold, comprehensive, and user-friendly solution available to you with Lanrex. Our 4-Stage Business Diagnostic lays out all the ways we strive to ensure the best business outcomes through a wide range of supported services.
Helping you avoid identity-based threats, identifying employees who send sensitive data outside the company via email, and developing a solid password strategy — these are only the beginning.
Contact us to let us know how we can help you improve your security, connectivity, productivity, hardware, and more.
Why Company Culture Is the Key to a Successful Digital Transformation
By Lanrex on 10/10/17 9:28 AM
Digital transformation may be a requirement in the modern era, but it’s also not something that is as easy as flipping a light switch. You can’t just decide to disrupt your organisation in such a significant way. You need a stable foundation upon which to build something stronger and more meaningful — something that addresses the challenges of today and still prepares you for the demands of tomorrow at the same time. For most businesses, company culture is that foundation in the best possible way.
Or at least, it should be. Many fail to realise that company culture and digital transformation have a symbiotic relationship — something that happens in one area has an immediate and often dramatic effect in the other. By making an effort to understand this relationship, you’re in a better position to use it to your advantage. You create a situation where each of these two essential business pillars is stronger together than either one of them could be on their own.
Company Culture: The Guiding Light through the Darkness
Digital transformation may be an uphill battle, especially for older organisations. But it’s one that company leadership can’t hope to nor expect to undergo alone. Experts agree that in many cases, a company’s biggest challenge in this regard has nothing to do with an unstable marketplace or increased competition — it’s the inner workings of the company itself.
A general lack of motivation to adapt to digital trends is the number one killer in terms of this type of mission-critical moment in time, and it’s also something that is backed up by statistics. In a recent study of over 3,700 business leaders that was reported by the Wall Street Journal, 32% of respondents said that their organisations were still “early” in terms of digital maturity. 42% said that they were “developing”, while only 26% said that they were “maturing”.
Those same respondents were then asked to rank their companies among six culture attributes like agility, risk appetite, leadership structure, and more. The results were striking:
- Companies that found themselves stuck in the ”early” stages of digital transformation were often the most risk adverse, hierarchical, and siloed
- “Maturing” stage organisations are most often nimble by design and are willing to take precise, calculated risks
- “Maturing” organisations also tend to lean heavily on collaborative workflows that actually give employees the ability to enact change when necessary
- Most interestingly, these above-mentioned culture traits were consistent across the board based on maturity stage — regardless of the size of the company you were talking about or even the industry they were operating in
Consider this from the perspective of breaking through risk aversion. It’s no secret that companies who are insistent on “standing still” are often the ones that lose the most from digital disruption. Taking risks means an incredible investment based on the size of said risk and the potential rewards at stake. It’s something that requires an “all hands on deck” approach to leadership, something that is impossible without a strong company culture at your side.
Another study revealed that more than 25% of employees said that they do not feel like they have the tools necessary to actually do their jobs. This is a large part of the reason why almost three-fourths of employees say that they’re just not fully engaged at work. This leads to diminishing returns elsewhere too — like the fact that 79% of employees said that they don’t feel strongly valued at work.
When you’re facing numbers like these, how can you expect to get everyone onboard with the way you need to digitally transform your organisation in the way the times require? The answer is clear — you can’t.
Focusing on culture is something that will affect nearly every aspect of your organisation. It improves the way that people think and feel about their jobs, which ultimately raises they’re investment level. It improves confidence in their leadership, which is essential when you come to everyone and say, ”We’re about to do something that will change the bedrock of this business, but I want you to come along with me, and I promise that things will be better on the other side.”
With a quality company culture at your side, people will actually believe grand statements like those.
Digital Transformation and Company Culture: Making the Impossible Possible
In the end, one of the most important things for you to understand is the idea that an absence of company culture will absolutely hinder successful digital transformation — end of story. Reinventing your business for the digital age is about more than just a change in direction. It comes down to more than just giving your employees the ability to work remotely or letting them collaborate on documents in the cloud.
It’s a change in mentality. It’s about a new perspective — one that acknowledges that you’re no longer operating in the world you were when you first opened your doors all those years ago. It’s a seismic disruption, but one that can generate the type of momentum that will literally carry you into the next decades and beyond — provided that you’ve got the strong, proper company culture from which to start with.
If you still have any additional questions about how to strengthen your company culture in your effort to enable digital transformation, or if you’d like to sit down and discuss your own situation with experts in the field, don’t delay — contact Lanrex today.
Are You Looking for a Managed Services Provider? Here Are the 8 Key Questions You Need to Ask
By Lanrex on 18/09/17 11:21 AM
Managed services as a concept brings with it a host of different benefits for nearly every type of business you can think of. But one thing people don’t realise until it’s far too late is that not all managed services providers are created equally.
If you really want to make sure that you’re getting the most bang for your buck and that you’re creating the best possible situation for yourself, your employees, and ultimately your brand, there are a few key questions you’ll need to ask any company that you’re thinking of partnering with.
Question 1: “What Products Do You Champion?”
One of the most important questions to ask any new managed services provider is also one of the most obvious: “Which specific products do you champion, and why?”
Are they over the moon about Microsoft’s infrastructure, or Google’s? Is it because they have a deal set up with those respective companies and make money every time they bring someone new into the fold, or do they genuinely believe that these products will help your business excel from a technological standpoint? The answers to these questions should help make your decision easier.
Question 2: “What Is Your Cloud Model?”
Another key question to ask any MSP you’re thinking about going with has to do with their existing cloud model, or lack thereof.
In the modern era, the cloud has reached an almost unparalleled level of flexibility — you can put as much or as little into the cloud as you want. However, for this to work in the way you need, your MSP must understand the benefits and intricacies of the cloud, not to mention offer a model that is up-to-date with the times.
Question 3: “Do You Have Experience in My Specific Industry?”
This is a big one, as failing to get a solid answer to this question up-front could potentially lead to disastrous consequences.
The rules governing data privacy and security vary wildly from industry to industry, and you need to make sure that your MSP is aware of this from the start. Keeping patient records private in a health care setting comes with different stipulations than managed services in the financial sector, for example, and vice versa.
You need to make sure that your MSP has experience with not only your industry’s unique needs but also its rules and regulations.
Question 4: “What Does Your Tech Support Look Like?”
This is another essential question because if anything ever goes wrong, you need to know that you have someone you can turn to 24 hours a day, seven days a week, 365 days a year.
Keep in mind that even after the initial work is completed, this is still a company that you’re going to be working with closely on a regular basis. Know its tech support model and see if they are ready and willing to help (including providing services like training and ongoing education for new users), or if they’re only going to stifle your progress and innovation (not to mention adaption).
Question 5: “Do You Have Any Awards or Certifications?”
The answer to this question will help you separate the men from the boys, so to speak.
Awards and certifications are what MSPs use to give themselves competitive advantages and to really make themselves stand out among a variety of companies all offering similar base services. Knowing if an MSP holds awards or certifications, particularly in the area of security, can help guide your decision when shopping around.
Question 6: “How Up-to-Date Is Your Knowledge?”
Along the same lines, it’s important to find out what an MSP’s own process for staying up-to-date on all the latest technologies truly is.
The tech world moves at a lightning speed, particularly when it comes to the types of services that these companies actually offer. How can you expect to leverage the power of the latest and greatest that IT has to offer if your managed services provider isn’t willing to do the same?
Question 7: “What, Exactly, Is Your Pricing Model?”
This is one of the most important questions that you can ask of any new managed services provider because price is one of the major factors that will mean the difference between getting exactly what you need and eliminating some of the cost benefits of going with an MSP in the first place.
Does an MSP charge per user or per laptop or other connected machine? Do they have a one-time cost? Are there any hidden fees or other charges that you need to know about? Based on this information, you can get an idea of what you’ll really be paying moving forward.
Question 8: “Can You Give Me What I’m Really After?”
You have a very specific goal in mind; otherwise, you wouldn’t be researching managed services providers in the first place. Are you looking to bring a newfound sense of mobility to your infrastructure? Do you want to move as much as possible into the cloud? Are you just looking to build yourself and your employees a modern workplace?
For the absolute best results (and best relationship moving forward), ask yourself these questions first and then find a managed services provider with proven experience in that particular area.
If you'd like to find out more, you can read Investing in IT Strategy: How to Drive ROI or get in touch with Lanrex today.
Trend Focus: Using the Cloud to Boost Team Effectiveness
By Lanrex on 29/08/17 10:30 AM
With the advent of cloud computing, modern small- to medium-sized businesses are now able to operate more efficiently and cost-effectively than ever before. Not only that, but using the cloud also allows them to compete technologically with their competitors who have far more resources at their disposal. But what exactly is cloud computing, and how can it be used by businesses to improve their day-to-day operations?
In this article, we’ll explore the cloud further and look at a few of the ways small- to medium-sized businesses can leverage it to boost team effectiveness.
Understanding the Cloud
Simply put, cloud computing is the process of storing, processing, and managing your business’s data on the internet rather than on a single computer or on a local server.
It’s with cloud computing that remote, third-party servers are used to store your data and you and your team are able to access it from anywhere, provided you have the right log-in information.
Team Boosting Benefits of Using the Cloud
If you already have your data stored on a local network, why move it to the cloud? It turns out that there are a number of significant benefits to using cloud computing over local data storage. These benefits include:
- Support Teamwork and Communication
The modern workplace is swiftly changing. Now, employees that you have assigned to a specific task may not necessarily be sitting across from each other in a cubicle.
Even if they are, information must constantly be transferred, files need to be shared back and forth with edits and suggestions made, and many more tasks must be carried out that require efficient digital communication. This means that the need for streamlined communication is now more important than ever in order to improve team effectiveness.
Thankfully, cloud computing and the digital workspace that it offers are excellent ways to improve the efficiency and effectiveness of your team’s communication.
By creating an interface where your entire team can work and interact while easily accessing the files and data they need to do their jobs, cloud computing makes it easy to support teamwork and communication in a modern workplace that operates much differently than it did just a few years ago.
- Enable Employees to Work from Any Device
According to one survey, 55% of employees who are working at mid-market firms require the ability to access the company’s data on a mobile device in order to do their jobs effectively. If your company’s data is stored on a local network or a single computer, though, mobile access may not be a possibility.
With cloud storage, data can be accessed and managed from any device, at any time, and from any location, provided your employees have been given the log-in information they need in order to access it. This improves business continuity and enables employees to continue working on projects they have been assigned to even if they are at home or on the field.
Not only does cloud storage increase the amount of output you receive from each employee, it also boosts their overall job satisfaction. The freedom to work remotely has become one of the most sought after aspects employees look for in a job. Should you choose to offer it, cloud computing provides that freedom.
- Increase Security
It’s hard for your team to be effective if your business’s data is stolen or otherwise compromised. In fact, data breaches and other cyber-attacks can be crippling to a small- to medium-sized business.
With data breaches on the rise, the damage they cause is becoming more and more of a concern. One study showed that there has been a 23% increase in the average cost of a data breach for a mid-market business, with each breach now averaging a price tag of almost $3.8 million.
Meanwhile, only 13% of small- to medium-sized businesses report that they are prepared to handle the security challenges they now face.
There’s a misconception, though, that cloud storage is less secure than storing your data on a local network when, in fact, the exact opposite is true. Any device or network that is connected to the internet is susceptible to being breached.
With cloud storage, though, you are able to leverage the security software and protocols of a large advanced organisation dedicated to the security of their clients’ data. This enables small businesses to enjoy the same level of security and advanced security resources as large corporations.
How to Make Use of the Cloud in Your Business IT
With the many apparent advantages of cloud computing, more and more businesses are starting to transition their data to the cloud. Thanks to a wide range of products and services related to cloud computing, this process is now more efficient than ever.
If you would like to learn more about how to make use of the cloud in your business IT and leverage it to boost team effectiveness, you can read about 10 Steps to Moving IT to the Cloud or get in touch.
How Lanrex's ISO Certification Works For You
By Lanrex on 16/08/17 11:03 AM
At Lanrex, one of the four major pillars that our business was founded on is and will always be “Innovation and Security.” We want you to be able to leverage the full might of modern technology to your advantage, but we also believe that this shouldn’t open the door to unexpected and unnecessary risk at the same time.
This is a large part of why we’ve made it our mission to go above and beyond the call of duty, providing policies and systems for clients who need to be audit ready to be “double bolted” when it comes to data security. Lanrex’s ISO certification is just one of the many ways that we work to accomplish this goal.
What Is ISO Certification?ISO certification (and specifically ISO 27001) is an international standard that governs information security management systems and related security techniques. In essence, it’s a comprehensive program that looks at nearly everything a system administrator does with the IT infrastructure of an organisation.
ISO certification is about more than just gauging risk related to your mission-critical resources — it helps you understand more about things like the likelihood of an attack or failure, the impact of these types of situations and what you can do TODAY to prevent these types of issues from arising tomorrow and beyond.
Why ISO Certification Matters
ISO certification is essential because it, like the technology you’re already using, is adaptable to your specific business. No two businesses are using technology in quite the same way, as they all have different objectives and outcomes in mind.
ISO 27001 operates on the same basic principle. It doesn’t tell you precisely how you need to implement security in your organisation, because there is no “one size fits all” approach to this goal. Instead, it tells you what objectives you need to accomplish at the organisational level to achieve the level of security you need to operate without worry.
The fact that Lanrex has obtained ISO certification means that our systems, processes, services and documentation procedures include all the requirements set forth by ISO 27001. This in turn allows you to protect your employees, your clients and ultimately your entire business from virtual harm by way of a double-bolted approach to data security.
Why Cybersecurity Is Essential for Your Business
All of this leads into one of the most essential topics of all: cybersecurity in general. Set aside the fact that the average cost of a data breach continues to grow with each passing year. The odds of your organisation actually becoming the target of a data breach are increasing too — especially in 2017 alone.
- A particularly nasty strain of ransomware called Petya recently spread to computer servers across the globe, affecting countless businesses — including those based in Australia. In a ransomware attack, all the mission-critical data on your computer’s hard drives are encrypted by hackers and held hostage until you pay up.
- A similar attack called WannaCry happened earlier in 2017, which began in Europe and quickly spread to the rest of the world. WannaCry was particularly notable both due to the technique used to penetrate machines (it exploited a vulnerability in the Windows operating system) and the scope of the eventual damage. The WannaCry outbreak was only stopped largely on accident — leaving the door open for future attacks of this nature in the future.
This is the world we’re currently living in. Technology in general brings with it so many benefits that it isn’t necessarily possible to go without it, regardless of the type of business you’re running or even the industry you’re operating in.
You can’t entirely eliminate risk — to assume you can is proof that you’re playing a game you never really understood in the first place. Instead, steps like ISO certification go a long way towards understanding, preparing for, and mitigating that risk — minimising the potential damage as much as possible and guaranteeing that you’re as protected as you can be at all times.
Lanrex: A Partnership Built on Trust
At Lanrex, we understand just how important cybersecurity is to your business. Failing to take every available precaution isn’t just putting you at a competitive disadvantage in your marketplace — it’s also potentially opening the door for the type of breach or other disaster that even the strongest business may never recover from.
As a valued partner in the future of your organisation, ISO certification is just one of the many steps that we’ve taken to craft a relationship based on trust and confidence. Without these two core qualities, even the most robust array of services in the world wouldn’t matter as it could all come crashing down at a moment’s notice. This is one situation that we do NOT want to see you find yourself in.
If you still have any additional questions about Lanrex’s ISO certification, or if you’d like to sit down and speak to someone about your cybersecurity concerns in a little more detail, contact Lanrex today.
Your IT Culture and Your Bottom Line: What You Need to Know
By Lanrex on 26/07/17 11:20 AM
Generally speaking, employees want to be actively invested in their jobs — it’s just that many of them don’t have the ability to do so. People want to see value in what they’re spending so much time doing each day. It’s part of what gives them a purpose. Out of all the ways in which the average business can achieve this, placing a high priority on positive IT culture is certainly one of the most effective.
Modern-day positions require communication, collaboration, data collection, and feedback. All of these things can be supported and driven by technology, provided that you’re coming at the situation from the right angle. Understanding just how your IT culture affects your employees and, ultimately, your bottom line is one of the keys to guaranteeing that your own business is headed in the right direction.
What Is IT Culture?
To get a better understanding of what IT culture actually is and why it’s important, it’s necessary to find out more about how it relates to your larger corporate culture in the first place.
Corporate culture is a term that simply refers to the beliefs and behaviors that determine how your company functions on a basic human level. The values that you hold dear, the ideals that you believe in, the goals that you’re trying to accomplish and how — these are all things that feed directly into your corporate culture.
IT culture is a natural extension of that. When executed properly, a healthy IT culture can actually be a great way to reinforce that larger corporate culture in a way that can’t help but improve business performance. It’s about more than just making sure that your employees have functional computers to work with each day.
It’s about giving them the tools, the resources, and the support they need to succeed on both their terms and yours whenever they’re given the opportunity to do so.
Improving Business Outcomes through IT Culture
To get a better understanding of why IT culture (and, by association, corporate culture) is so essential, consider the following statistics:
- One study estimated that companies who have high numbers of engaged employees tend to outperform those that do not by as much as 202%
- More than one in four employees who responded to another survey said that they don’t feel like they have the tools necessary to be successful in their jobs
- Because of this, as many as 71% of employees say that they are not fully engaged
- Likewise, only about 21% of employees say that they feel like they’re strongly valued at work. That leaves 79% who sadly cannot say the same thing
Consider those statistics through the funnel of a strong IT culture, which you can only achieve by making an informed, strategic investment in modern technology. When you go out of your way to give employees access to the tools they say they need to successfully do their jobs, their work becomes easier as a result.
They start to feel more engaged in not only their role but in your company, increasing their satisfaction across the board. It also helps increase the feeling that they’re strongly valued, as if you didn’t believe in their potential you wouldn’t be making such a significant investment in IT resources in the first place.
At a basic level, the right technological resources can help generate a massive boost in terms of productivity and organisation. People don’t have to sort through stacks of paper documents and spreadsheets to be productive — the data they need is always at their fingertips. People don’t have to go out of their way to communicate or collaborate with their coworkers — they can create spaces online to do that with anyone, anywhere in the world.
This creates a clear and dramatic ripple effect — one that ultimately feeds into improved business outcomes and increased productivity and quality. Remember that the University of Warwick discovered that happy workers tend to be 12% more productive than the average worker — a number that most businesses cannot afford to ignore.
Your IT Culture Is Your Business
In many ways, the major quality that IT and corporate culture share can all be boiled down to a single word: empowerment. An investment IT is more than just an investment in technology — it’s about putting the right tools in the hands of the right employees at the right times. It’s about making sure that they have what they need to work smarter, not harder. It’s about doing what you can to support the way they like to work so that, in turn, they can support you and your organisation.
But even an investment in the “latest and greatest” that IT has to offer ultimately won’t mean much without a strong IT culture at your side. Technology is an incredibly valuable business asset when done right, but failing to also emphasise IT culture could potentially limit your business outcomes before you’ve really had a chance to get started working towards them in the first place.
If you still have any additional questions about how your IT culture affects your business’s bottom line that you’d like to see answered, or if you’d like to sit down with someone and talk about your needs with true experts in the field, please don’t delay. Contact Lanrex today.
Your IT and You: Choosing the Best Options to Support Your Business
By Lanrex on 11/07/17 2:00 PM
One of the great things about technology in general is that it’s malleable — especially in the enterprise arena. If you take a look at your closest competitor, they’re probably using modern-day technology in a totally different way from your own organisation. Concepts like cloud storage, software as a service, security suites, and others transcend IT — they’re powerful tools that can be adapted in a variety of different ways depending on what you’re trying to do and how you need to do it.
Unfortunately, this can also make the process of choosing the best options to actually support your business easier said than done. There is no “one size fits all” approach to business IT, which means that there are a lot of potential mistakes that you could make if you don’t approach the situation from just the right angle.
Thankfully, this is all more straightforward than it sounds. If you’re passionate about choosing the best options to support your business, there are a few key things you’ll want to keep in mind.
It’s All about the Right Fit
In many ways, picking the best IT resources to fit your needs is a lot like shopping for a new pair of shoes. It’s all about trying to find the right fit — that perfect pair of sneakers that feel like they were custom built for your own two feet by an expert craftsman.
Case in point: one of the most important decisions you’ll make regarding IT has to do with whether to set up your own in-house IT department or to partner with an outsourced IT provider. Both have their fair share of benefits depending on the situation you find yourself in.
When you choose to go with an in-house IT department, you’ve got an almost unparalleled level of control that you’re not going to find anywhere else. Every last kilobyte of storage is yours because you purchased it outright. You know precisely how every piece of equipment in your office works because you paid someone to set it up (or did so yourself). You don’t have to worry about issues that arise from sharing resources because everything is yours and yours alone.
The flip side of this, however, is one of cost. There are more than a few internal IT costs that you’ll have to deal with. Every staff member will need a computer — something that you’ll have to pay to purchase, set up, and maintain in the long term. Software licenses aren’t getting any cheaper. HR and admin overhead costs are not insignificant. If a new piece of technology becomes available that your business needs, you’ll have to invest in not only the product but training for your IT employees.
Cost calculators, like the one on the Landrex home page, paint a clear picture of how much money you need to be willing to pay to hold on to that aforementioned level of control.
Outsourcing, on the other hand, comes with a significantly reduced price tag. IT companies can traditionally get much better rates on quality products than you can yourself. You don’t have to worry about training, maintenance, software upgrades, or troubleshooting — everything is handled by a dedicated team of providers in exchange for a predictable monthly fee.
Outsourcing is also a great way to mitigate risk — the responsibility of maintaining your environment is no longer exclusively yours. You get the opportunity to leverage the expertise of people who have been doing this for a long time to your advantage. You also get the assurance that the staff members managing your environments are exceptionally well trained. Can you say the same thing about your internal IT department?
Considerations about External Companies
If you do decide to go the outsourcing route, there are still a number of important factors to consider. What is the security expertise of the provider you’re working with, for example? Remember that the average cost of a data breach continues to rise every year — is this the type of expense you can afford to take a chance on?
You’ll also want to make sure they have experience in your particular industry. What products do a particular outsourcing provider champion? Many external companies usually offer products from a few key software vendors — are those resources aligned with your own business strategy?
Unique IT Solutions for the Unique Business
But again, it’s essential to remember that there is no right or wrong answer at play. Some businesses need the external control that only outsourcing can provide, while others can’t afford to give up the control that they would get by keeping everything in-house.
Don’t think about how your competitors are using IT. Don’t look for the one right answer to the decisions you’re being forced to make — it doesn’t exist. Assuming, it does put you in a terrific position to spend more money than you need on resources that you can’t actually use. Only by thinking about technology in the context of your organisation’s long-term goals will you be able to come up with the solution that is right for you.
If you still have additional questions about choosing the best IT options to support your business, or if you’d like to sit down with someone and discuss how IT aligns with your own long-term strategy in a little more detail, please don’t delay. Contact Lanrex today.
Empowering Your Employees with the Right IT Strategy
By Lanrex on 28/06/17 4:05 PM
Making the right IT investment can have a positive ripple effect across your entire organisation almost immediately. In terms of engaging with your clients alone, it’s difficult to find a single decision that is more valuable. Acquiring new clients, finding new ways to increase client retention through innovative experiences, and even getting a better understanding of the clients you already have are all dramatically easier with the right resources.
Real-time, actionable data insights and analytics give you powerful new opportunities to personalise client interactions, for example, gaining a 360-degree view of your client’s relationships and interactions across sales, service, marketing, and other channels.
See the Tech Maturity Model: Where Does Your Business Stand?
From an operational perspective, IT can also be a terrific way to streamline processes by reducing time spent on labour-intensive manual processes and to meet regulatory requirements at the exact same time. The modern-day IT infrastructure is built in a way that allows you to deploy new services and experiences in an organic, scalable way via either a move completely into the cloud or by integrating cloud services with your on-premises servers.
But it is mission critical for you to understand that none of this will mean anything without the right, objective-driven strategy at the heart of it all. Because IT procurement isn’t just about giving your employees access to “the best tools that modern technology has to offer.” It’s about giving them the perfect tool that they need to accomplish their objectives and to meet the requirements of today while better preparing for the challenges of tomorrow.
With the right IT strategy, you’re investing every bit as much into the future of your employees as you are into the future of your organisation as a whole. Or at least, that’s the way you should be thinking about it.
Your IT Strategy and Your Employees: What You Need to Know
With an IT strategy that aligns your hardware and software resources with the goals that matter most for your business and your employees, you’re unlocking a huge variety of different benefits you won’t find anywhere else. You’re enabling employees to get more done and achieve a much higher level of job satisfaction than ever before. You’re not making purchases for the sake of it — you’re providing your team with the tools they need to increase flexibility and encourage innovation across the board, all driven by the interpersonal interactions that are at the heart of any business.
Unified communications, enterprise social, collaborative resources — these are all tools that increase the agility of your employees, allowing them to be productive on their own terms from PCs to phones, tablets, and beyond.
The right IT strategy also goes a long way towards not just enabling teamwork from anywhere and on any device, but creating an environment where it becomes the path of least resistance by its very nature. The right IT tools deployed in the right way encourage professionals to collaborate with their peers, whether it comes to hosting online meetings or collaborating on documents in real-time and more.
It’s no secret that businesses are creating more data now than they have at any point in human history. According to Forbes, there will be 1.7 megabytes of new data created for every human being every second by as soon as 2020. IT may allow you to create and house that data, but it is your IT strategy that allows your employees to actually use it in the ways they need to do their jobs better.
Your IT strategy is the driver that allows your employees to make faster, better, and more informed decisions based on real-time communication information. Your strategy is what empowers your team members with instant access to relevant content. It’s what gives them the opportunity to analyse market and competitive data and to effortlessly create interactive visualisation to bring new trends and pressing issues to light.
All of these lead to a number of positive ramifications for the very future of your organisation. Empowering your employees with the right IT strategy lets you increase employee retention and improve morale. It’s what reduces employee turnover — remember, it costs much more money to hire a new employee than it does to retain an existing one. It strengthens workplace agility, improves business insights, and ultimately generates a seismic shift in the quality of the work that your employees are doing and the level of pride they’re able to take in it.
But without the right IT strategy, these are organisational and operational benefits that will always be slightly out of reach.
An Investment in IT Is an Investment in Your Employees
One of the biggest mistakes that business professionals make involves the assumption that IT is only about purchasing the latest and greatest equipment based on spec sheets and industry trends. At the end of the day, you’re just talking about hardware and software — powerful resources, yes, but meaningless without the right strategy at the heart of it all.
You could outspend your largest competitor significantly in terms of IT procurement, but it will ultimately mean nothing if you don’t have the unique, malleable strategy you need to bring it all together. IT resources are a means to an end — they are not the end in and of themselves.
The real reason why IT is so important is because an investment in this area is really an investment in what matters most — your employees. These are tools that they’ll be using every day to work smarter, not harder, and to accomplish essential short- and long-term business objectives. To that end, developing the unique, outcome-driven strategy that is custom-built for your business and nobody else’s is the key to all of this.
If you still have additional questions about empowering your employees with the right IT strategy, or if you’d like to get personalised recommendations from true experts in the field, don’t delay — contact Lanrex today.
The WannaCry Ransomware Attack: What Happened and What You Need to Know
By Lanrex on 15/06/17 10:19 AM
Ransomware — a specific type of computer virus that encrypts all data on an infected computer and holds it for ransom — is not a new concept. According to one study, ransomware emails spiked 6,000% in 2017 compared to one year prior. Not only did 59% of all infections come from an email, according to an Osterman Research study, but 40% of all spam email had ransomware contained inside it, according to CNBC.
But just when cyber security experts thought they had ransomware figured out from a threat perspective, something came along to act as a sobering reminder of just how devastating these types of attacks can be. On the morning of May 12, 2017, a particularly nasty strain called WannaCry infected more than 230,000 computers worldwide — and that was only the beginning.
The WannaCry Ransomware: What You Need to Know
What made the WannaCry ransomware attack so unique was how far-reaching it was — essentially overnight, it turned into a global phenomenon of the worst order that affected as many as 70 different countries over the next few days.
WannaCry actually spread in large part due to an exploit in the Windows operating system that was discovered by the National Security Agency in the United States earlier in 2017. The exploit was so great that WannaCry actually had the potential to infect all unpatched versions of Windows older than Windows 10. When you consider that Windows 7 still has a 48.5% worldwide market share, you’re talking about an attack with no equal throughout the history of cybersecurity up to this point.
When a machine became infected with WannaCry, all information on the affected device was quickly encrypted. A message appeared on screen offering to unlock compromised data for a sum of $300 to be paid only in Bitcoin.
Though the virus first made its way into the world via malicious emails, it was able to spread so quickly because it took advantage of a security loophole at the operating system level. When one machine on a network became infected, it essentially compromised all others at the same time. All hackers would need to do was infect a single device on a single LAN to bring an entire organisation to its knees.
Though the attack was eventually stopped, the damage was already done. In the end, WannaCry was more than just a nuisance — it was a startling reminder of just how far cybersecurity still has to go in the modern era.
How to Protect Yourself
An old saying tells us that “the best defence is a good offence,” which is exactly why being proactive is essential in your quest to stay protected against the WannaCry ransomware and other threats.
First and foremost, you need to be backing up your organisation’s data as often as possible to guarantee that if you are hit with a ransomware attack, the damage is mitigated. If your business’s mission-critical data is backed up regularly to a secure, off-site location, it won’t be compromised as the attack is executed. You may lose an hour’s worth of progress on that important project depending on when your last backup took place, but the entire digital fingerprint of your organisation won’t fall into the wrong hands.
It’s also essential to update all important business software and applications as soon as those updates are released. Many people don’t realise that updates do more than just add features and improve user experience — they’re also often intended to patch security holes and provide bug fixes that hackers often exploit when executing ransomware and similar types of attacks. As with backups, software updates and patches are something that can be heavily automated — especially if you choose the right provider for all your IT service needs.
Staying protected from these types of threats absolutely requires an “all hands on deck” approach — your employees need to understand that they’re the first line of defence between your business and a hacker that wants to do you harm. Because of this, you’ll need to invest in IT training — keep all your staff up-to-date on how to recognise threats, what threats are prominent right now, and what they need to do as far as best practices are concerned to stay safe moving forward.
Train all staff members not only on how to recognise suspicious emails but also in terms of the very real ramifications they may be opening themselves up to if they let their guard down for a second.
Lanrex and IT Support
At Lanrex, we believe that while the internet has undoubtedly changed the world of business in particular for all time and for the better, it’s also made it a more dangerous place too. This is why we work hard to be more than just a business IT company. Technology is just a platform — we help you leverage that technology to create better business outcomes, especially when it comes to staying protected in the digital age.
As information security experts with ISO certification, we know exactly how to put technology to work for you in a way that allows you to enjoy all the advantages with as few of the potential downsides as possible. If you’d like to find out more information about what the WannaCry ransomware means for Australian SMEs, or if you’re interested in exploring similar topics, please don’t delay — contact Lanrex today.
Investing in IT Strategy: How to Drive ROI
By Lanrex on 30/05/17 5:12 PM
According to the Pew Research Center, IT can have a positive and dramatic effect on nearly every aspect of your business. 51% of survey respondents said that IT helped them expand the number of people outside of a business they were able to communicate with.
39% of people said that it allowed them more flexibility in terms of the hours they work. 35% said that it actually increased not only the amount of hours they were able to work in a day but how productive those hours were.
But the most important thing to understand is that not all IT spending is created equally. If you really want to align your technology with your business and create the meaningful, lasting impact you desire, there are a few key things you’ll have to keep in mind.
See the Tech Maturity Model: Where Does Your Business Stand?
Understand the Business Strategy
Before you make any decision in terms of your IT investment, you must first get a deeper understanding of exactly what that investment will help you accomplish. How your IT infrastructure evolves must depend on your business strategy — where your organisation is headed, the overall goals and long-term needs, etc. This is the only way you’ll be able to drive a real return.
Consider the fact that the global market for technology spending is roughly $4 trillion per year, according to CNBC. However, 67% of business IT efforts on average end up getting scrapped due to a focus on chasing technology instead of chasing what technology can do for you.
For the best results, you need to factor in both the quantitative and the qualitative aspects of a business. Only by knowing where you’re headed can you choose the right solutions to help you get there.
Outlining the Metrics That Matter
When deployed properly, IT not only can be a conduit for running a business but also a tool to measure the ultimate success of that business as well. In terms of investing in IT, part of driving a real return comes down to identifying all the metrics you need to track the tangible benefits you’re getting moving forward.
Are you trying to increase productivity? Increase collaboration? Increase your customer lifetime value? Decrease cost of acquisition? Once you know what your goals are, you know what to measure. Once you know what to measure, you know what to deploy.
But again, even with something as seemingly specific as metrics, there is no “one size fits all” approach for IT measurement. You need to implement an iterative process optimised for your business that allows you to measure based on the criteria that matter most to you, track those measurements on a long-term basis, refine your approach as needed, and repeat as often as possible. Only then will you be able to guarantee that metrics are being used to impact the business in a positive way.
Diagnose the Status Quo
Another step you’ll need to take to guarantee a real return on your IT investment involves finding out what “normal” truly looks like. Figure out where your business currently stands on the Tech Maturity Model — you can use our free tool to accomplish precisely that.
Diagnosing where you are on the Tech Maturity Model will help make sure you know where to focus and how to properly address your IT needs. You will get superior visibility into where your business is currently, allowing you to make an educated judgement on the holes and gaps that need to be fixed as well as a set direction to focus on.
If you want to read more about the Tech Maturity Model, you can do so here.
Explore These Options
There are several IT options that depend on the needs of a business for proper application, including but not limited to ones like:
- Digital Workspaces
- Integration
- Cloud Computing and Infrastructure
- Security and Compliance
- Business Continuity and Recovery
- Help Desk Support and more
Digital workspaces powered with solutions like Office 365 can be a perfect way to allow your staff to work from the cloud, access documents anywhere, schedule video conferences and more — all from any computer or device with an active internet connection. Not every business may be ready for this type of option, but that doesn’t mean that you won’t be one day in the future.
Knowing what options are available to you puts you in the best position to see what you’ll be investing in as you move further down the line. To find out more information about your available options, please contact Lanrex today.
The Foundation of Information Technology
Your IT infrastructure is an invaluable business asset — provided that it was designed in a way that complements your actual business strategy, rather than changing that strategy to make the most of the technology you have available to you.
Understanding where technology fits in to your long-term goals, outlining the metrics that matter, diagnosing the status quo, and exploring all your options are all of paramount importance in terms of generating the type of IT ROI you need.
If you'd like to find out more about how to drive a real return when it comes to your IT investment, or if you'd like to get personalised recommendations from experts in the field, contact Lanrex today.
Is Your Internal IT Working? 4 Warning Signs You Should Be Looking For
By Lanrex on 23/05/17 9:19 AM
When your internal IT is functioning like a well-oiled machine, it doesn’t just put you in a better position to address the challenges of today, it also helps you prepare for the evolving requirements of tomorrow and beyond. If your internal IT isn’t working the way it used to, however, you’re doing far worse than just wasting time maintaining the status quo — you’re actually costing your business money in a host of different ways.
They say the first step to recovery involves admitting that you have a problem in the first place. Knowing how to identify when your internal IT just isn’t working anymore doesn’t just help you increase the efficiency of your infrastructure, it can also help lower costs across the board and increase your return on investment at the same time.
Find out how Lanrex can help your business boost efficiency and maximise ROI. Get in touch today.
You’re Spinning Your Wheels
One of the major signs that your internal IT efforts might not be generating the results you need is if you feel like you’re spending the majority of your time maintaining the status quo, as opposed to focusing on continual service improvements that allow your business to continue to grow and evolve.
Keeping everything functioning is important — but devoting so much of your time to this one core area alone isn’t going to bring in new clients, improve the products or services you’re capable of offering, or improve existing relationships.
This is an example where making the jump to external IT through something like a managed services provider actually makes a lot of sense. In addition to delivering network, application, system, and IT management services on a “pay as you go basis”, they also handle everything from network maintenance to troubleshooting to updating and more on your behalf. This frees up the time of your internal IT employees to focus on moving your business forward.
You’re Getting Hit with the Same Problems Over and Over Again
Another clear sign that your internal IT isn’t working involves recurring issues that tend to rear their ugly heads again and again. The only thing worse than the fact that you’re suffering from the same issues is the fact that your internal team has not been able to identify why.
These are the types of situations that don’t just cause headaches — they can actually be catastrophic to your ROI. Keep in mind that most experts agree downtime is the second largest cost that a business can face. Last year alone, downtime cost Fortune 1000 companies between $1.25 and $2.5 billion. One study even estimated the national average cost of downtime as $0.38 per second, $22.80 per minute, $1,368 per hour, and $32,832 per day. Are these the types of costs your business can afford?
Your Internal IT Isn’t Enabling Growth
Addressing the needs of your business as they are defined today is only one small part of what IT is supposed to do. Equally important involves the creation of a solid foundation of solutions that allow you to meet future requirements as your organisation continues to grow and evolve.
Simply put, if your current team is great at managing your existing environment but don’t have the skills or experience necessary to design IT with an eye towards the future, your internal IT isn’t working.
Having a plan for growth is one thing — having the resources in place to enable that growth, as well as the team of people you need to make sure everything is continuing to move on the right track, is another story altogether.
Your Internal IT Is Too Internal
One of the most critical signs that your internal IT isn’t working the way you need it to is if there is little or even no relevant documentation in place. Knowledge is critical when it comes to maintaining a business IT environment. But if that knowledge exists only in the heads of the team — or even within a single key person — it may as well not exist at all.
This is the type of problem that leads to slower responses to issues, increased development time, and ultimately lost revenue.
If your team discovers a valid resolution to a problem but doesn’t document it, how are you supposed to replicate that in the future? If you have one key IT person who knows pretty much everything there is to know about your environment, but at the same time nothing is written down, what are you going to do when they leave?
These are the types of questions that you shouldn’t have to ask. But if you are, your internal IT is actually too insular. It’s a sign that it may be time to step outside your comfort zone and embrace external IT with open arms.
The Lanrex Approach
At Lanrex, we pride ourselves on being more than just a business IT company. Above all else, we’re here to help our customers and their businesses perform better through the careful, calculated application of better IT — period. Technology on its own is important, but it is only one small part of a much larger story. Knowing how to leverage it is the key to generating the types of business outcomes you deserve.
If you're in or around the Sydney area and would like to find out more about how to identify when your inernal IT isn't working, or if you'd like to dicuss your situation in a little more detail, don't hesitate to contact Lanrex today.
The Tech Maturity Model: Where Does Your Business Stand?
By Lanrex on 26/04/17 9:00 AM
Far too many business leaders fail to look at their IT infrastructure in a deeper way that goes beyond simple dollars and cents. They think "If I'm spending X number of dollars on a piece of equipment, it needs to generate at least Y dollars in return to be a worthy investment." While this makes sense on paper, it fails to uncover the bigger picture: that technology is a valuable long-term business asset when executed strategically.
This is one of the many reasons why knowing where your business stands on the Tech maturity scale is so important. Remember - nobody starts out on the scale at level 3. Rome wasn't built in a day, and your foundation of optimised IT resources won't be, either. Based on how you're using IT today, the scale will give you a "bigger picture" understanding of the effects of what you've already done and, most critically, what you still have left to do to in terms of your business strategy to get where you need to be.
Maturity Level 1: Foundation
If your business falls on this first level of the IT maturity scale, you likely either have very little or no evidence of some of the following activities happening within this category. While you may have had some modest discussions with your team over how to use your IT resources and why they're important, you probably don't have any documented plans in place to back that up. You also likely lack the dedicated resources or commitments from key stakeholders to really take your IT efforts to the next level.
- Your business' use of IT is largely reactive, meaning that you're only focusing on using IT to address challenges that have already happened as opposed to mitigating future risk.
- As a result, you're only experiencing short-term gains.
- Your IT focus tends to be on urgent and reoccurring issues. You have a problem; you use IT to solve it. Rinse, repeat.
- You've only been using IT to remove immediate performance barriers. You needed to be able to share information in the cloud; you can now share information in the cloud. Very little additional thought is put into it.
- You're having a very difficult time predicting your costs. Even something like a storage upgrade comes out of the blue and is a potentially massive blow to your budget.
Maturity Level 2: Stability
If your business reaches this level of the IT maturity scale, the processes and the ways in which you're using technology are a little more defined, understood and finely implemented than before. You've begun to put a little more thought into what resources you need, what they're supposed to do and why they matter beyond simple dollars and cents.
- You've begun to take a more proactive approach to IT. You're now concerned with putting the resources in place to maintain a stable and controlled environment.
- You've started carefully planning your IT deployments in a way that guarantees reliability and predictability.
- You've begun to do more proactive maintenance on your resources, which, as a result, makes ROI easier to measure.
- You've begun a basic level of IT governance, meaning that you likely have some type of documentation over how resources can and cannot be used by employees.
- You've begun to enjoy the benefits of predictable costs. You can better anticipate what you'll be spending before you actually spend it.
- There is now some alignment with your IT resources and your larger business objectives. IT is now about more than just "getting online."
Maturity Level 3: Advantage
If you're lucky enough to reach this stage in the scale, you no longer work for your IT - your IT works for you. Thanks to a rock solid foundation of well-defined processes and inputs, you now have strong connections between IT and related business processes. You're also now likely enjoying some or all of the following benefits:
- You're in the best possible position to use IT to achieve very specific business outcomes.
- The technology you've already invested in is being actively used to give your organization a competitive advantage.
- IT governance is in place, including advanced concepts like BYOD device policies, end-user security and more.
- Not only are you enjoying predictable (and often fixed) costs, but your ROI on your technology spend has also been maximized.
- Nimble IT organization. You've reached a point where you're only paying for what you're actually using and no technological resources are wasted.
- A superior level of IT and business collaboration has begun to optimize larger business processes across the board.
- There are programs in place that allow you to systematically optimize business processes. You're using technology to automate certain menial tasks so that your employees can get back to doing the most important thing of all: driving your business forward.
Where Does Your Business Stand?
The maturity of your business IT tells you a great deal more than just how long it will be before it's time for another equipment upgrade. In many ways, it's a guide that shows you how well your existing IT resources are aligned with your current and future goals.
This is one of the many reasons why hiring IT consultants is such an important step to take. You're doing more than just selecting a solutions provider - you're generating the peace-of-mind that comes with knowing both that your technological foundation can support the business you're trying to run today AND that it will allow you to grow and evolve into the organization you hope to be spearheading tomorrow. If you want to reach level 3 on the maturity scale, hiring a consultant is the best way to do it. Take the Tech Maturity Assessment below and diagnose where your business sits.
If you'd like to find out more about the business IT maturity scale, or if you have any additional questions about IT consultations in general, please feel free to contact Lanrex today.
Technology Support and Help Desk Trends to Watch in 2017 and Beyond
By Lanrex on 12/04/17 9:23 AM
What’s new in IT? Learning more about the latest IT support trends can help you stay agile and ensure that your business is always using the best tools available. From increased reliance on AI and automation to more mobile devices in the workplace and even some growing security threats, here’s what to be ready for in 2017:
Looking for a more recent wrap up? Click here for the biggest tech trends for small businesses in 2019 and beyond.
Increased Reliance on Automation
Artificial intelligence is nothing new, but incorporating automated AI systems into your business can make things more efficient. Automating some of your processes allows projects to move along more quickly, increases productivity, and even reduces errors.
Instead of relying on a consumer to provide correct data and a human employee to interpret and enter it correctly, automation can perform tasks with more accuracy and swifter results. For businesses, this mean means more time and money saved, fewer errors, and more reliable responses.
Improved Speed and EfficiencyBusinesses need to be able to meet demands more swiftly and efficiently; your IT help desk can help you come up with custom solutions to your pressing problems and allow you to meet your goals. By finding ways to speed up your processes without sacrificing efficiency or accuracy, you can scale your business and reach out to more customers than ever before.
Growing Reliance on AnalyticsBig data is no longer just for big business and specific industries. From theme parks that place stores and shopping opportunities based on visitor data, to local governments who predict which intersections are most hazardous at specific times of day — analysis of big data is everywhere.
Understanding and analysing your sales and marketing data can help you more effectively target your prospects and ensure you are making the most from your investment and efforts. From identifying buyer personas to discovering the ways that customers use your products to solve problems, big data can reveal surprising insights into your business.
Increased InterconnectivityIncreased connectivity is not just for homes; the different components in your business need to be able to effectively communicate with one another. Your helpdesk provider can assist you with setting up an integrated, connected network that allows you to work smarter, not harder. Ideally, a diverse group of business machines will be able to work together and seamlessly connect, allowing you to work from a laptop, phone, or tablet with ease.
More MobilityDo you know anyone who does not have a smartphone? The increased use of not only mobile devices but BYOD (Bring Your Own Device) models means more challenges for the IT department. How can you separate personal data and use from business data, and how can you keep the network secure when so many devices access it daily? It may be less expensive for businesses, but the BYOD model brings many challenges to the table for IT in 2017; the helpdesk can assist with both preventative measures and problems arising from mobile use.
Heightened Security AwarenessThe growing threat of cyber attacks makes it all the more important to secure your network and educate your team about the perils of cybercrime. From setting up a secure, breach-proof network to keeping you informed about the latest threats, expect to see an increased interest in security topics in 2017.
Being aware of the latest IT trends and concerns can help you protect your business and ensure you are always able to take advantage of the latest technology. Your IT support provider can help you navigate these trends and allow you to stay on the cutting edge of technology; the right help desk provider will also be able to help you protect your business and free you up to focus on what you do best.
Lanrex doesn’t do technology solutions, we do business solutions backed by technology.
4 Signs You Need to Outsource I.T
By Lanrex on 5/04/17 10:50 AM
The Internet is filled with heaps of articles and blog posts touting the advantages of having your own in-house I.T department. They list reasons such as having more control, improved efficiency, and better customer service.
Oftentimes they give an in-depth explanation of how the ability to take advantage of the latest technology trends, such as cloud computing, artificial intelligence and big data analytics, can make a real difference for businesses.
However, what these articles don't mention are the significant disadvantages to having an in-house I.T team - disadvantages that often make outsourcing your I.T a much better option.
If you’re the owner or CFO of a small- to medium-sized company, it’s not always in your best interest to maintain an in-house I.T department that manages your technology needs. There are signs that your company may be better off outsourcing I.T, and in this article, we’ll explore four of them.
An in-house I.T department is expensive. Due to the skills shortage, I.T personnel generally demand higher salaries than other workers. Employees with certain specialisations — for example, cybersecurity or data management — often negotiate even higher remuneration. In addition, there are the costs associated with creating and implementing the infrastructure, including all hardware and software.
When you outsource your I.T function, you usually pay a pre-determined price for a service package that provides precisely the services you need. That means you’re not paying a team of employees — complete with benefits — for full-time work hours. Moreover, I.T consulting companies can get you better deals on hardware and software from reliable vendors.
Sign 2: You Don’t Train Your I.T StaffLet’s face it: we all know our employees require periodic upskilling. When it comes to I.T, however, there are so many training options out there that, unless you’re a high-level I.T professional, it’s impossible to know where to begin — so many of us just let it go. While this is understandable, it’s also a fast-track to an ineffective I.T department — and that places your company’s performance and security at risk.
If, on the other hand, you work with an I.T consulting company, you get the benefit of consultants who not only specialise in specific areas of I.T but who also stay up-to-date on developments in their specialisations with the best trainings available. Moreover, since they work in their specialisations day in and day out, they possess vast and invaluable experience.
Sign 3: Your I.T Is Not Keeping UpI.T is continuously evolving. Both employees and customers expect to be able to access companies remotely on a range of devices and operating systems. In addition, digitisation means that an increasing number of mid- to back-office functions are moving online. If you’re unable to update software and adjust configurations to allow for new or improved functionalities, it will result in impaired performance that could cause you to lose business.
An I.T consulting company is always up-to-date on the latest developments regarding infrastructure, data management, collaborative tools, VoIP systems, and any other relevant areas. It also has access to the most recent technology so your consultant will select and implement the best solutions for your company.
Sign 4: You Can’t Take the RiskIf your security system isn’t continuously updated, you’re vulnerable to cyber threats such as ransomware, zero-day attacks, and advanced persistent threats. According to a 2020 article by Zurich: Australian businesses lose up to $1 billion each year due to cyber attacks. In addition to the direct costs, the reputational damage resulting from breaches is immeasurable. These are very real risks that can cause significant, sometimes even irreparable, damage to a business.
This is where outsourcing your I.T function can make all the difference. Specialised I.T consultants have access to the latest knowledge and technology — and they know which solutions are right for your company. They also know how to consolidate multiple security applications that have been implemented over time into a single streamlined solution that provides visibility of your entire network. As the capabilities of security software advance, I.T consultants can also integrate new features such as self-learning and artificial intelligence that basically allow your security system to autonomously develop protections against sophisticated threats.
There’s also another aspect to risk, and that involves regulations and compliance. Depending on what business you’re in, you may have to comply with national or international regulations regarding communications and data protection. If you fail to comply, you could face hefty fines and reputational damage. Because of this, you need the ability to conduct audits of your infrastructure and security system, as well as generate reports of those audits.
An I.T consulting company not only reduces your risk because its consultants will ensure your network and cybersecurity measures comply with all relevant regulations, they’ll also have the expertise and technology to quickly and efficiently perform audits and generate reports.
Outsourcing Is the Smart Choice for Forward-Thinking CompaniesAgility and digitisation are prerequisites for companies to drive innovation and growth in today’s competitive market. So is having effective, affordable I.T capabilities. That’s why forward-thinking companies outsource their I.T functions to save money, eliminate inefficiencies, reduce risk, and gain the expertise they need. That way, I.T becomes a powerful tool that companies can use to support their core activities, improve their competitive positioning, and reach their business objectives.
Lanrex offers a range of business I.T solutions, including integration, security and compliance, business continuity and recovery, and help desk support. To find out how we can help your business achieve its goals, get in touch today.
10 Steps to Moving IT to the Cloud
By Lanrex on 29/03/17 3:59 PM
The cloud is quickly becoming the preferred infrastructure for companies in many industries. Moving to the cloud is usually done in stages, and there are specific steps that every business should take into account. Here are 10 steps that every company must consider when the decision for cloud migration is made.
If your business is considering moving to the cloud, why not let Lanrex guide you over the hurdles?
1 - Discover Your Deployment Model
The different forms of “aaS” (as a Service) will serve as your deployment options, and there are a growing number of options you can choose from. For instance, Infrastructure as a Service (IaaS) lets you take control of all hardware and software through the cloud. Platform as a Service (PaaS) adds development options to IaaS features. The popular Software as a Service (SaaS) option is less complicated than IaaS or PaaS, and it is often the most effective option for smaller companies.
2 - Decide the Type of Cloud Structure You Need
There are three basic cloud types that correspond somewhat to web hosting options — public, private, and hybrid clouds. A public cloud is the approximate equivalent of a shared server that is offsite. A private cloud gives a company a single tenant solution just for them. And a hybrid solution is a mix between the two.
3 - Start With Non-Mission-Critical Applications
There will be hiccups when you are first moving into the cloud. To keep your business functional while you learn how to make the move, start with smaller applications, saving customer-facing, mission-critical apps until the end of the process.
4 - Choose the Apps for the Cloud
As functional as the cloud currently is, it is not the best solution for everything just yet. For instance, if you decide on a public cloud option, then you may want to move only those apps with less of a need for security. You may also find that legacy apps are not compliant with the newer infrastructure of the cloud. You will have to update those functions before moving or decide to move into a new standard.
5 - Search Out Prospective Hosts
Once you have chosen the applications you want in the cloud and matched your general structure to those needs, it is time to see who exactly can provide those resources to you. Not all cloud hosts are the same. You may want to hold a round of RFPs or conference calls to have cloud-hosting companies explain to you firsthand what they can do for you.
6 - Perform Your Own Research
As with any other business partnership, do not rely on the word of the hosting company after presentations are made. Ideally, you want to see their solutions in action. This is easy enough to accomplish — you can find current clients and conduct interviews, peruse review sites, and even set up a test site to see firsthand how the vendor handles security and compliance issues.
7 - Consider Scaling
Although one of the biggest advantages of cloud hosting is scalability, this does not happen magically or automatically upon deployment. Any application that you are looking to eventually scale must be placed on a load balancer to respond in a timely fashion to an increased need for resources. You need to look into whether your vendor charges extra for this feature, especially if you are choosing IaaS as your infrastructure. PaaS solutions have a bit of scalability built in; however, the company behind the infrastructure is what drives the final cost.
8 - Consider Customer Service
Is your hosting company willing to guarantee a certain level of uptime? What is the restitution to you if it fails to live up to this standard? Downtime, once you move proprietary data and customer facing applications into the cloud, can be an enormous setback; and your hosting company should be more than able to provide guarantees that this will not happen. Check the automated maintenance schedule to ensure timely and proper security and software build updates.
9 - The Architecture of the Software
As alluded to before, traditional and cloud apps do not always port well into each other. Even if a traditional app can be ported, its features are not always maximized. You must check to see if your hosting will require third-party cluster equivalents, load balancers, or database replication.
10 - The Legal Hurdles
Once you virtualise your business in a global way, laws in different jurisdictions become an issue. You must work with your cloud provider to stay in compliance with municipalities and software company licenses.
Migrating to the cloud can be one of the best decisions a business ever makes. From increased efficiency and less downtime, to improved security and load balancing — the benefits of implementing a cloud IT infrastructure seem limitless. However, it’s easy to get lost along the way, and businesses really can’t afford to get it wrong.
If you’re considering moving your business to the cloud, why not get in touch with Lanrex? We understand that every business is unique, and we don’t speak geek! See what we did for our client, The Retail Council.
5 Essential Tools Top Businesses Use to Fuel Growth
By Lanrex on 23/03/17 9:12 AM
One of the most important things to understand about growth is that it isn’t about just having a plan in place to support today’s actions — it’s about making decisions today that would affect your ability to perform tomorrow, five years from now, and beyond. Every one of the core qualities that businesses in all industries are chasing — from increased efficiency to the ability to make better decisions to talent wins, and that ever-important competitive edge — are all enabled by your ability to grow and evolve.
As a result, the answer to the question “When is it the right time to grow my business?” is and will always be now. There are five core types of tools in particular that top businesses of the modern era have routinely used to fuel the type of growth you’re now trying to achieve yourself.
1. The Power of Cloud StorageTo say that cloud storage is essential to the lifecycle of the modern business is something of an understatement. Not only do services like Google Drive, Dropbox, Microsoft OneDrive, and more keep everything in one place — thus eliminating confusion about where to look for materials — but they also guarantee an almost unprecedented level of mobility. Any document can be accessed by any device on earth with an internet connection and the right credentials.
Documents are also instantly updated; meaning, there are no longer communication delays and nobody is ever waiting to receive information. This goes a long way towards increasing productivity as well. There’s a reason why the global cloud market is expected to grow to $200 billion by as soon as 2018.
2. Maximum OrganizationTools like Google Suite, Evernote, Microsoft Outlook, OneNote, and Slack can also be hugely beneficial in terms of the larger organization of your digital resources. Having a single centralised resource for everything that is highly secure and always available supports communication within a team, saves time by reducing or outright eliminating certain tedious administrative tasks, and in general, makes projects run much more smoothly than ever before.
3. The Era of Customer Relationship ManagementCustomer relationship management solutions like SalesForce, Microsoft Dynamics, and SugarCRM do a lot more than just allow you to keep track of customer interactions. While CRM options do help keep all your information on prospects in one place, they also take things one step further by allowing an incredible level of visibility over not just interactions with a prospect but a relationship as it’s being forged.
You can set your customer relationship management solution to automatically remind you about important events, for example, making sure that you’re always contacting the right person at the right time. This in turn doesn’t just make your relationship with customers easier to manage but more efficient by nature, leading to an increased win rate across the board.
In a world where 75% of all customers say they’re willing to spend more money with a company if they have a positive customer experience, it’s easy to see why CRM has such a high ROI of approximately $8.71 for every $1 spent.
4. Email Marketing for the Modern AgeSpeaking of contacting the right people at the right time, email marketing is still one of the most powerful (and valuable) ways to do precisely that. Services like MailChimp, HubSpot, Infusionsoft, and others provide a single turnkey solution for every piece of collateral that you create and distribute, no exceptions.
Not only is email marketing software a powerful tool for reaching out to both existing and potential customers, but it’s a great way to score the interactions you’re having between them. You can see who might be on the fence, who was a solid customer whom you need to re-engage, and more — allowing for a much deeper level of personalisation every time you reach out.
You can use past behaviour to quickly identify new opportunities to upsell to existing customers or to re-engage potential ones that you may have otherwise written off. All of this contributes to the type of long-term increased sales you need to sustain the growth that you’re after to begin with.
According to Campaign Monitor, email marketing comes with an incredible 3800% return on investment — you can expect to earn $38 for every $1 spent. Email marketing software is one of the best ways to help make that happen.
5. Analytics Drives Insight, and Insight Drives the FutureIn many ways, analytics is more than just a numbers game. Tools like Power BI, Google Analytics, and more are a way to reveal the story that was previously hidden beneath those numbers, providing the type of valuable insight you need in real time to make the highest quality decisions you can as quickly as possible.
Analytics solutions allow you to take the valuable data you’re already collecting and use it to discover what your most valuable lead sources are, for example. You can find out where your best sources are, where the majority of your customers come from, and more — all so that you know exactly where to hyper-focus your attention.
You can also use analytics to learn more about the way your business operates as it continues to grow. You can see staff capacity and hours in real time calculate ROI more precisely and reliably to find out what is worth your time and what isn’t, and so much more. You can even effortlessly uncover the bottlenecks that are holding up your operations and reducing efficiency, allowing you to evolve into the type of lean organisation you need to see the results you deserve.
In the EndIn many ways, these are more than just tools used to fuel growth. They’re the qualities that make up the foundation upon which every aspect of your business is built. If you don’t have a solid foundation for a house, no matter how expensive or beautiful that house ends up becoming, it’s eventually going to tumble to the ground. The same is true of your business.
Regardless of the industry you happen to be operating in, long-term and sustainable growth should always be one of your top priorities. These are the types of tools that can help get you there. An investment in them now is an investment in your own success.
The Guide to Increasing Business Productivity
By Lanrex on 8/03/17 9:00 AM
Increasing business productivity is synonymous with increasing business growth. By unlocking and addressing the challenges affecting your employees, you can improve productivity, lower operational costs and increase business performance.
To help your business out, read on to find three key ways of increasing business productivity.
- Address inefficiencies
Many employees often find that there are certain processes that slow down their ability to produce work. This is often a red flag for bottlenecks and inefficiencies that are usually the main source of employee frustration.
If you recognise any of the following in your business, it’s time to assess how you address these issues:
- Employees or management sitting around waiting for reports, data, product information, marketing metrics, or any other critical detail necessary to move forward
- Information silos that result in double-upping of tasks
- Manual admin tasks that take up time and reduce the time spent in front of clients
- Chronic late deliveries
Start your productivity assessment by creating a flowchart that shows how the operations of your business work. You might consider creating one big chart for the overall business and then breaking each segment down into smaller pieces so you get a clear picture. Note down how long each process takes and look out for areas that aren’t keeping pace.
How efficient is your current model? - Take Lanrex's Tech Maturity Test
- Eliminate the Waste
Waste is a word that can mean many different things in business. When it comes to productivity, wasted time is your biggest concern. Sales are the heart of most business revenue, so it is a practical starting point. Look closely at the various services and products your company offers and the input and output for each one.
- Input = time and money that goes into that product or service
- Output = amount of revenue it generates
The goal is the breakdown of your business to get a closer look at what works and what doesn’t.
Once you have the figures in hand, start making comparisons. You can automatically eliminate anything that costs more than it is worth — that frees up time for products that do generate income.
Follow this same strategy when assessing other elements of your business. For example, you can compare staffing in different divisions to trim waste and increase productivity. Examine your vendors the same way and look at company assets to ensure you have all the right tools in place and that they pay for themselves.
- Is your IT adding more to your bottom-line?
An IT strategy sets out the infrastructure that holds up a business’s strategy. Where productivity boils down to the company’s ability to execute a working strategy, the role of IT is to help streamline the execution to deliver results.
There are a number of ways you can use IT to improve the business flow. For instance, why not find a way to automate repetitive processes in your business? Today’s IT systems can perform many varied tasks, from smart scheduling and warehouse robots to standardising internal approval processes and comparing supplier prices.
Business technology is also the answer to faster and more effective communication. IT creates a formal framework for communication that opens up those lines while still providing a level of security. With the right communication strategies in place, you can expand your metrics to measure work performance, set up remote workspaces to reduce operation costs, and enhance employee motivation.
IT provides connectivity through employee portals to improve productivity throughout the organisation as well, resulting to zero communication delays, which cost the business time and money.
Today’s technology is the answer to:
- Connectivity throughout the business
- Information access
- Setting up the foundation for business growth
- Risk management
- Real-time metrics
- Delivering a competitive advantage
- Business transformation
- Performance analysis
- And more…
Boosting productivity means you get more out of each hour of the day — that means more revenue, more customers, and more recognition for your brand. Efficient productivity is the one thing all successful companies have in common, and this is how your business can stay a step ahead of the competition.
If you’d like to learn more about how IT can be your business’s competitive advantage, contact Lanrex today.
What you need to know about internet security
By Lanrex on 24/02/17 2:43 PM
Australia is no stranger to internet security or IT Security breaches. In recent times, David Jones, Kmart, Woolworths, and the Red Cross Blood Service have all been victims of serious ‘cyber’ attacks.
But these are just some of the cases that made the news. The fact is that most internet security breaches never get reported.
What you don’t know can’t hurt you… or can it?
Since we only ever hear about the newsworthy incidents, it’s easy for CEOs of small and medium enterprises (SMEs) to believe that cybercrime only affects the big corporations.
The problem is, this then leads to the thinking that cyber security measures are only necessary for the big corporations too. You probably have some sort of internet security system in place, but it’s not something you place too high on the priority list.
Sound familiar?
One of the most dangerous ways to think is “It’ll never happen to us”. As an SME, you may feel that you’re not a likely target due to your size and the fact that hackers couldn’t possibly be interested in what you do – but the exact opposite is true.
Cybercriminals love SMEs.
This is because businesses like yours are seen as easy targets, and can be used as a way to get to the ‘bigger prize’ if you’re working with larger organisations, like suppliers or business clients.
The 3 types of cyber attacks most common to SMEs are:
- Phishing scams
Scammers can trick you into giving out personal information such as passwords, bank account details, and credit card numbers by sending emails that appear to be from a legitimate source. - Ransomware
Sometimes a phishing email will contain malicious software which, once opened, can block access to the entire company network until a sum of money is paid. - Hack attacks
Cybercriminals can use phishing scams to gain access to the company’s network, allowing them access and exploit sensitive data, at the risk of you losing it all.
Your biggest threat isn’t who you think it is…
Don’t go beefing up the internet security budget just yet. More than anything internet security is about your people.
As you can see from the nature of the attacks listed above – cybercriminals rely on your staff’s unwariness. It’s the employee who innocently opens the email attachment from a ‘trusted source’, or responds to a request for financial details from the ‘bank’, who lets the attacker in.
Unfortunately, human error is to blame for most security breaches, so before you look at technological solutions, educate your staff on how to avoid these traps and the significance of safeguarding your business’ information.
Once your staff are up to speed, you might consider outsourcing elements of your cyber security programs to a managed IT service provider. This takes the responsibility is off you to monitor your network and detect suspicious activity, and it’s usually the most cost-effective way to go about protecting your business.
In the meantime, there are a few simple steps you can take to protect your SME.
-
Use secure passwords such as three random words
-
Install antivirus and malware software on all company devices
-
Instigate regular software updates that contain vital security upgrades
One step ahead of cybercrime
A security breach is one of the biggest kind of crises an SME can face, and unfortunately, it’s one that more and more CEOs will be facing this year.
With the increasing number of users, data, and network connections, internet security threats are only going to mount.
For SME leaders like you, this means the management of internet security risks needs to be top of mind.
Don’t allow yourself to be lulled into a false sense of security. It’s okay to hope for the best, but you need to prepare for the worst.
Who’s to say you won’t be next...
Download your free ebook today on Backup vs. Business Continuity.
2017 How to conduct a business process review in 4 steps
By Lanrex on 17/02/17 11:33 AM
To refresh your memory, a BPR evaluates current processes and identifies ways to make them more efficient, which means less wasted effort and more time spent on valuable work. A BPR needs to be completed thoroughly, so it’s best to hire an expert to do the bulk of the work for you. A consultant will ‘shadow’ each business process, and ask questions of the staff involved. This will enable them to:
-
provide an organisation-wide view
-
identify gaps and inefficiencies e.g. double-handling of data, duplicate processes
-
identify potential areas for streamlining processes or automation
-
examine which processes are not required or are not producing what they should
BPR success doesn’t come easily. It requires everyone’s involvement, and for that to happen, top management needs to be committed, employees need to feel empowered, and there needs to be strategic direction and an end goal.
So, here's how to conduct a business process review in four steps:
1. Identify and map out your current processes.
Start by defining the business process ‘as is’. This means all of the sections in a typical business process, such as:
- list of roles
- list of steps
- handoff points
- exceptions
The goal here is to understand exactly how the business process works today, kinks and all.
At this stage, the people involved in the process need to be interviewed. Prompt them by asking questions, such as:
- Why was that step taken?
- Do you need anyone else’s approval to take that step or make that decision?
- Are there any exceptions to the rule?
It’s not good enough that they just describe it – they need to show you how they do it. You also need to encourage these employees to explain any problems with the existing process.
Consider the following questions:
- What in the process is broken?
- Which steps in the process create roadblocks?
- Which step requires the most time to complete?
- Which step causes the most delays?
- Are there any steps that cause costs/resources to go up?
- Are there any steps that cause quality to go down?
It also helps to draw up a visual representation of the business process from start to finish and its interaction with people, departments, and software. This makes it easier to analyse and identify potential gaps and overload points.
2. Analyse them by talking to Stakeholders (Don't forget your customers).
Once you’ve mapped out the processes, arrange a series of meetings with staff to brainstorm why the problems exist and how to resolve them. Talking to customers will also give you great insight into where you’re going wrong.
From the findings you create a report, which should consist of a process map, with each process tied back to a detailed discussion which consists of:
- the steps in the process
- problems related to the step
- the type of problem
- the impact of the problem
- the system requirements
3. Map out your new plan and objectives.
Now comes the improvement plan – essentially an action plan to put the desired processes in place.
Here, you need to set realistic and measurable objectives that align with your overall business goals.
Include the key actions that need to be taken to get to where you want to be, how they will be achieved, and any financial and resource implications.
4. Find out how technology fits into your new plan.
Technology is the last part in all of this – the BPR should drive technology, not the other way around.
This will depend entirely on your situation, but examples of technologies that create more efficient processes are:
- Customer relationship management (CRM)
- A file sharing and project management system such as Microsoft Office
Reap the benefits:
A detailed BPR will reduce the risks, help manage the budget, and produce a successful implementation of any new systems.
It also has the added bonus of reducing silos in your organisation.
An independent and objective view obviously helps, so hiring a consultant to manage the review is your best bet.
Typically, this will be an IT partner who is experienced in this area, who will offer recommendations, advise on the technology best suited to your business’ needs, and help you implement the changes.
If you do your homework, you really can’t go wrong!
How an IT Strategy Can be your Competitive Advantage
By Lanrex on 16/02/17 9:00 AM
Cloud migration, Office 365, Dynamics, Digital Workspaces…. We know IT can feel overwhelming.
With the right implementation, IT can become your greatest advantage, helping you achieve:
- Time — The average Australian small business devotes a third of its time to administration that IT systems can take over.
- Better Communication — IT provides a number of channels for employees and managers to coordinate in real time.
- Better Storage - You can use your IT system to store and organise valuable data.
Interested? Here’s how you can optimise IT for your firm:
Step 1: Plot Your Processes
Before you implement new technology, you must first map out everything your business does. This will allow you to base your IT purchases and upgrades on your firm’s specific needs.
Begin by identifying the products and services that you provide to consumers, and then explore how all of your operations contribute to this end. When you’ve completed that, ask yourself what information is required for each step to proceed. Understanding the tasks in your business and the links between them is key to helping you fit the right IT tools into your business.
As you survey your company’s activities, take note of operations that are especially expensive or use up a particularly large amount of your employees’ time. It is in these areas that IT has the most potential to save money or boost productivity. Also pay attention to any complaints you have had from past customers, as well as products that do not sell well. Consider how IT might allow you to resolve such complaints and better produce and market such products.
Step 2: IT Investigations
Once you have a clear map of all your company’s functions, identify the role of technology at every point. Being by making a list of all the IT products you currently use, what they do, and any past issues that they have had. Then, list all the things you would like to achieve through your IT system. The goal is not to implement every item on the list but to get a range of options to improve business.
When the list is done, rank each item according to its importance. Take into account the amount of money that each change can save or generate, as well as how quickly it will accomplish that.
Step 3: Options Overview
Now that you know where you can benefit from IT, start researching the available technologies to see what your options are. Look for equipment and programs that will fulfil as many of your goals at once. More established products like Microsoft Office 365 are generally more reliable and easier to for staff to pick up, but be prepared to pay a bit more for this freedom.
It’s important to be realistic about what new technology will offer. No device or program can accomplish all your goals on its own. Weigh the cost of IT against the benefits of its capabilities. An expensive product should be able to pay for itself by reducing costs elsewhere or generating greater revenues.
Step 4: Seeking Staff Feedback
Given that the members of your staff are the ones who will be using the new technology, consult them before you make any purchases. Ask for input on what functions they need from an IT system, and make sure they are confident in their ability to learn the new products.
Step 5: Expert Engagement
Between 50 and 80 percent of large technology endeavours fail — therefore, it’s essential that you consult an expert throughout the upgrade process. A professional can use their extensive experience to illuminate exactly how IT aligns with your unique business goals. They can also help you train your staff to use the new technology, organise your information, and periodically assess the quality of your systems.
If you are interested in getting some direction or just want some more information on how you can fuel your business growth through IT, contact us here.
What leaders need to know about the Business Process Review
By Lanrex on 8/02/17 10:42 AM
Business processes are created to increase business performance, but if they’re not continuously improving they can end up creating the opposite effect for your Small or Medium Enterprise (SME).
 As your business grows, processes can become overloaded and inefficient, and when this happens, it’s tempting to ‘fix’ the problem by involving more staff or buying new technology. But that’s only going to make things worse and will cost you more in the long run.
As your business grows, processes can become overloaded and inefficient, and when this happens, it’s tempting to ‘fix’ the problem by involving more staff or buying new technology. But that’s only going to make things worse and will cost you more in the long run.
To make your processes more efficient, you first need to understand where you currently stand. This is where a Business Process Review (BPR) comes in.
A well-conducted BPR will provide insight into:
- how processes are currently performed
- what works and what doesn’t
- any potential issues or problems
- opportunities for change and improvement
A BPR involves analysing the processes used to handle the daily activities of your business in order to identify enhancements and opportunities.
How do you know if you need to do a BPR?
- There are issues with current processes, such as orders not getting processed or customers being frustrated with your business’ service
- Staff are confused about what the right process is or what steps to take in certain situations
- You want to automate or streamline your business processes, but their current state is not well understood or documented
However, there are factors that prevent BPRs from being successful in SMEs, and it’s important that you’re aware of these before you jump right in.
1. Culture
A BPR won’t work without profound cultural change.
Decision making in SMEs is often dominated by the CEO, but this can hinder a BPR project, as organisation-wide input is essential.
Any improvements to business processes as a result of the BPR involves changes to jobs and the social structure. You’re going to be dealing with people’s reactions to the likely serious organisational changes, so you need to involve them from start to finish to increase motivation, reduce stress and resistance, and improve business performance through employee empowerment.
2. Resources
A serious problem SMEs face when starting a BPR project is a lack of financial and human resources. Don’t make the mistake of overlook the costs and people power required for a thorough BPR.
Processes affect everyone in the organisation, so a BPR is going to involve everyone too, and this can be a time consuming and expensive exercise.
While growth and business performance are the main concerns for SME leaders, financial constraints may inhibit you from undertaking a BPR.
The key is to have realistic expectations. This means budgeting and developing estimates of effort.
This is a big job in itself – many SMEs will hire a consultant just for this part before the project has even kicked off.
Then, once you start working closely with vital staff during the BPR, you’ll be able to better estimate the final implementation costs and the scope of the project.
3. Technology
IT infrastructure can be a significant barrier to the options available to planning and changing business processes.
IT is an enabler in creating and maintaining flexible business networks, but if your infrastructure is old and weary, it’s not going to be able to support new systems that require fast and reliable
Have a good look at your infrastructure, and if needed, consult an IT expert to conduct a business technology assessment.
Do your homework
These factors are the difference between success and failure of your BPR, so make sure you’re in the clear before you start your project.
The sooner any potential risks to the project can be identified, the greater the chance of successfully mitigating them. Once risks have been identified, they can be better managed.
You might also like, What does Business Process Maturity mean for SMEs?
What does business process maturity mean for SMEs?
By Lanrex on 3/02/17 3:37 PM
All companies, big and small, have processes. They’re the structured business activities that produce value, serve customers, and generate income.
When they are regularly reviewed and continuously improving, your business will be functioning optimally. If not, performance will be impacted.
How important are business processes?
Your business, just like all others, is built on 3 pillars:
1. People
Having the right people, motivated and performing is naturally a key requirement to performance.
2. Technology
Providing the people with the right tools to do their jobs well is vitally important. Technology has transformed the work environment, and with digital technologies such as cloud and mobile we are all becoming much more efficient.
3. Process
Business processes are what hold everything together. They establish formal lines of communication and promote cooperation between units
Making a sale, for example, involves multiple departments, from marketing to production to accounts.
Processes are essential because they ensure that business tasks are carried out in the right way, at the right time, and by the right people.
What is process maturity?
As a small or medium enterprise (SME), growth is likely to be one of your main business goals. So, if growth has slowed and you’re falling behind your competitors, ‘immature’ processes could be to blame.
Process maturity is an indication of how close a developing process is to being complete and capable of continual improvement.
As an organisation becomes more mature, so too does its processes. But this doesn’t mean they necessarily mature at the same rate – some may still be at the lower levels.
A process’ maturity level can even drop if it’s not monitored or the documents are not updated as the business changes.
Maturity levels
There are 6 levels of maturity for business processes.
Level 0: Person-dependent
The activity being performed is not documented. It’s entirely person-dependent and the sequence, timing, and result may vary during repetition.
Level 1: Documented
There is a document that has been reviewed and approved by an authority as the standard process, but the activity being performed may not be carried out as per the document.
Level 2: Partial deployment
The documented activity is being deployed, but there are inconsistencies. For example, it may not be deployed at all the intended locations, or though all functions, or by all the intended owners, or all the activities defined in the process are not being performed.
Level 3: Full deployment
The process is consistent and shows seamless linkage between functions and other processes wherever there needs to be any interaction.
Level 4: Measured and automated
The process is measured against goals such as adherence to timelines, customer satisfaction, and cost. It is system-driven by custom-made software.
Level 5: Continuously improving
The timelines, cost targets, and satisfaction levels are being achieved consistently and performance objectives are regularly updated.
Becoming More Mature for Business Growth
So, how do you get your processes to maturity level 5?
It varies across businesses and industries. Process maturity in a fast-evolving market such as financial technology will mean something totally different from maturity in a more traditional field such as legal services.
Regardless, one thing all organisations have in common is that they should start with a business process review. In next week’s blog, we’ll run through what this involves.
Start by getting expert advice and putting the foundations in place, and you’ll set yourself up for digital success.
Find our why your companies IT Strategy is key to your business growth with our free guide below.
How to make digital transformation happen in 3 steps
By Lanrex on 27/01/17 10:35 AM
Many organisation today that are Small to Medium in size are often hesitant about digital transformation because they don’t know where to start.
There’s no need to complicate things. You just need to consider the ‘3 Cs’ – Customer, Course, and Culture.
1. Customer
Before anything else, put the customer in mind. There’s a myth that digital transformation is all about technology, but that isn’t the case. It’s not about automating processes, or making something faster. It’s about redefining a business strategy and delivering customer value, based on the potential of digital technologies.
Many digital transformation initiatives fail because they’re technology-led rather than customer-led.
It’s not enough to just sell a product or service anymore – companies in the digital age need to eat, sleep and breathe their customers. This means letting them drive your digitalisation strategy.
Start by gathering as much data from your customers as you can. You can do this by installing clever analytics behind your website to follow your customers’ browsing journey, or you can create a form for your customers to complete when they make an enquiry online.
This is the type of information you want:
- How do they prefer to get in touch with you? Email, phone, or through your website?
- Which pages are most popular on your website?
- How long do they stay on your website? At what point do they leave?
- Which types of marketing communication do they respond to best?
Responses to these questions will help you prioritise your digital tools, but don’t limit yourself to these. Collect information you don’t even think you’ll need – you might find it’s valuable down the track.
Once you start making changes based on the data, ask for guidance and feedback from existing customers as well as employees who interact with customers on a daily basis. By focusing on the customer experience, you can make the digital changes necessary to improve your business processes.
2. Course
If you’re the business owner or CEO, then it’s probably up to you to lead the transformation process. Start by drawing a digital roadmap with your executives so you have a plan and a team behind you when you address the rest of the company.
When this time comes, you can help your digitalisation strategy succeed by:
Making the transformation meaningful
You need to communicate to your team the reasons for going through the transformation. Present the roadmap to help build a collective understanding of where the company is going, and create a powerful transformation story. People will go to great lengths for a cause they believe in.
Leading by example
Rolling up your sleeves and getting personally involved goes a long way to getting your staff involved. If you model the mindset and behaviour you want to see in your team, they are more likely to cooperate.
Motivating teams
Be clear on where your company’s heading, but don’t set it in stone. Encourage your employees to explore new digital ideas and contribute to the transformation process. This gets them involved and makes them feel like they’re part of something.
3. Culture
For some SMEs, a significant cultural change is needed to become a ‘digital organisation’ – where everyone is focused on the customer experience and on board with doing things the ‘digital’ way.
Break down any siloes by opening the lines of communication. Connecting people and information leads to collaboration and transparency, and ultimately an inclusive culture that breeds innovation.
This is a critical success factor. Without it, you’ll end up with a divided company – one part moving into the future, and the other clinging on to traditional processes.
Get the ball rolling
Driving any sort of change in the organisation is not easy. That’s why digital transformation requires strong leadership and a shared vision.
The key for any business looking to make digital changes is to just get started. It’s easy to get bogged down in the details, but keep in mind that there’s no ‘right’ path to digital transformation.
If the customer experience is central to your strategy, and your team has a digital mindset – you’re well on your way there.
Start by getting expert advice and putting the foundations in place, and you’ll set yourself up for digital success.
Find our why your companies IT Strategy is key to your businesses succes, with our free guide below.
How can Businesses Overcome Barriers to Digital Transformation?
By Lanrex on 19/01/17 9:32 AM
For many Small to Medium Enterprises, digital transformation has brought new opportunities to grow, become more nimble, and turn the tables on much larger competitors.
In fact, 41% of SME’s cite their size as an advantage over larger companies that can’t take advantage of digital innovation as quickly.

More and more small business CEOs are recognising the need to ‘go digital’ to stay competitive, but even after you’ve defined what digital transformation is, it can still be difficult to know where to start.
There are a number of barriers to SMEs achieving digital transformation. Are any of these hindering your business?
Minimal knowledge
Many SME’s mistakenly think that digital transformation is just about automating what they have.
Digital transformation goes beyond simply automating existing processes. It’s about reinventing processes, which means reducing the number of steps, the number of documents, and the number of people involved. Only by doing this can you add game changing customer value.
It’s important to get informed before you go ahead with a digital transformation project, so consult a trusted IT partner who will set you on the right track.
No sense of urgency
Many SME’s assume that because they are ‘small’, they don’t need to undergo a digital transformation to stay in business.
Digital transformation is vital for every business’ survival and growth.
For SMEs in particular, digital transformation can be an opportunity to reinvent business processes and renew the customer experience.
If you’ve ever wondered whether there’s a better way of doing something, then your business can benefit from digital technologies.
Perhaps you’ve asked yourself some of the following:
- Surely there’s a better way to do expenses?
- Surely our staff should be able to work from home?
- Surely we should be able to create quotes while we are at a customer?
- Surely we should be able to track our marketing efforts centrally?
- Surely we should be able to predict when our equipment needs maintenance?
- Surely there must be a better way to manage our call queue?
Yes, there is! It’s all possible with digital technologies.
Perceived complexity
If you’re not in the business of IT, then the thought of introducing digital technologies is going to seem complex.
Here are a few ways to make the transition less overwhelming:
Map out your business priorities
What do you most want your business to achieve, and what tools could help you do this? Technology is key to digital transformation, but it’s useless if it’s not based on informed business decisions.
Have the right foundations in place
There’s not much point investing in digital tools and systems if you have a slow and creaking infrastructure underneath them. If you don’t invest in your IT systems now, they’ll only cost you more down the track.
You should also talk to your network provider to ensure you have the bandwidth in place to support your technology objectives.
Consider how your workforce will evolve
Do you have mobile workers? Could flexible working give you access to a wider talent pool?
If so, you need to make sure your employees have access to the same technologies as they do in the office. Tools such as Microsoft Office 365 give your staff the ability to securely connect and collaborate from anywhere, anytime, on any device.
Take it one step at a time
It’s not difficult to understand why digital transformation can seem overwhelming for SME leaders, but not everything has to be done at once.
Start by getting expert advice and putting the foundations in place, and you’ll set yourself up for digital success.
Find our why your companies IT Strategy is key to your businesses succes, with our free guide below.
Digital Transformation Explained
By Lanrex on 22/12/16 3:22 PM
‘Digital transformation’ is the phrase on everyone’s lips. Blogs and social networks are overflowing with posts on this topic, and CEOs are suddenly expected to be ‘in the know’ about digital strategy and to steer their companies in the right direction.
So what exactly does digital transformation mean and how do you apply it to your business? In its simplest form, digital transformation is the process of streamlining office procedures with the help of digital technologies such as cloud computing, mobility, big data, and collaboration.
Digital transformation goes beyond simply automating the existing process. Rather, it’s about reinventing the process, which means reducing the number of steps, the number of documents, and the number of people involved.
Information overload
The reason the ‘digital transformation’ phrase has generated so much buzz is because of the way digital technology has revolutionised the way we work.
We are living in a mobile-first, always switched on world, where things happen in real time and information knows no boundaries.
It’s been estimated that every two years, the world’s information doubles.
Today more than ever before it’s important that you streamline business processes, because the more streamlined they are, the quicker, easier, and cheaper they’re going to be for your business.
One example is dealing with paper. While the amount of information being managed electronically is increasing, ironically, so too is the amount of paper we’re using.
With data coming from multiple channels, businesses in every sector are now spending more time sifting through unstructured information arriving in multiple formats. This leads to decreased productivity and an increase in inefficient, manual processes.
While going ‘paperless’ is not really an option for most organisations just yet! – digital products like web conferencing and Microsoft Office 365 can assist in minimising the amount of paper processing you do.
In fact, businesses that have begun the process of converting documents into electronic formats claim they are 14% more effective.
This is because ‘digitising’ data in this way can help your business to:
- easily preserve and archive documents
- provide painless access to information from any location
- make it easy for staff to share and collaborate on files in a range of different formats
Customer first
A lot of the push for digital transformation is coming from the customers themselves as today’s consumers want a quick and easy digital experience, and they want it now.
You can blame companies like Amazon and Apple for this, because thanks to them customers now expect every organisation to deliver products and services in the same way.
They want bank loans to be approved in minutes.
They want to log in to their online electricity account and see a real-time report of their consumption.
They expect all service providers to have automated access to all the data they provided earlier and not to ask the same questions over and over again.
The way to meet their expectations is by streamlining your business processes, because you can only deliver a seamless experience on the outside if the inside is working at peak efficiency.
Keep in mind that with the amount of information available online nowadays, it’s easier to shop around. So, if your customers don’t get what they want from you, they may not wait around.
Behind the buzzword
Hopefully you’re now comforted by the fact that digital transformation isn’t as scary – or as expensive – as it’s made out to be.
However, it is just as important. So, if you’re a business leader, now’s the time to be looking into how digital technologies can help you to better streamline office processes.
Download our latest ebook, Why Your Companies IT Strategy is key to Business Success.
How can you make Office 365 tools work for your business?
By Lanrex on 16/12/16 11:22 AM
Changing your business’ technology can be a daunting prospect. The risks in changing your current technology solution may be concerning as time, money, and energy are at stake.
In this blog we discuss why efficient technology solutions, collaboration and communication are key to the success of your business and how to make Office 365 tools work for you.
The cloud along with mobile, and social technology solutions can support your business to collaborate much more efficiently. Cloud computing – accessing IT services via the internet provides businesses with the ability to use the cloud for some things and keep others on existing systms.
The popularity of Cloud computing has meant that the price of collaboration and productivity tools for many businesses has dropped considerably.
How can the new Office 365 help you achieve your business goals?
Traditionally, Microsoft Office has offered software such as Word, Excel and PowerPoint, which you purchased on a disc for a few hundred dollars and installed on your computer.
Office 365 now provides businesses with a cloud-based version which lets you pay a monthly fee instead of having to pay for it upfront.
As with all cloud services, the key benefit for your business is the cost savings, as you essentially rent the infrastructure off someone else rather than buy it outright.
Today, CEO’s are focused on more than just keeping costs under control- they want to know how a new technology can help achieve their business goals.
If you’re managing a Small to Medium Business, growth would be a top priority. A cloud-based solution such as Office 365 can facilitate growth and help you scale your business.
The new Office 2016 apps enables users to access trusted business applications across laptops, desktops, smart phones and tablets operating iOS, Android or the Windows operating system all in a secure environment.

Here’s an example of how office 365 can support business growth and goals – your business has a small number of core permanent staff, but you need to hire temporary staff for a specific project or event. The temporary staff need access to email and applications such as Word and Excel to complete their job.
In this scenario most businesses would need to buy year-long licences for Microsoft Exchange even though they are only needed for a matter of weeks. This becomes expensive and time consuming to install on individual devices.
The solution to saving time, increasing efficiency and reducing unnecessary technology costs is to move to Office 365 – it simply goes into the membership portal and adds the number of users needed for the time period required.
Having this flexibility helps you scale your business as you need to, because you’re not limited by physical technology constraints – you can add and remove uses as needed so you only pay for what your business needs at that point in time.
What are the benefits to your business?
For users
With Office 365, your staff can connect and collaborate from wherever they are working and on the device of their choice. All they need is an internet connection and their account login details.
One example is a project management tool called Microsoft Planner. This makes it easy to structure teamwork, as staff can:
- create new plans
- organise, assign and collaborate on tasks
- set due dates
- update statuses
- share files
For CEO
By improving communication and collaboration, Office 365 supports a remote workforce and preserves data while maintaining security and control.
As security threats are a concern for all businesses now more than ever, this makes Office 365 a low risk solution for your business.
In this digital and mobile era, productivity is necessary for your business to remain competitive. Office 365 provides your staff with the ability to be truly mobile and access documents and content anywhere.
Given the key benefits the new Office provides around the cloud, social, security and technology it is important to consider this solution for your business to remain competitive.
Because Office 365 is managed in the cloud, your IT department will spend less time troubleshooting problems and spend more time enabling productivity.
Download our latest ebook, Why Your Companies IT Strategy is key to Business Success.
Choosing the right Emerging Technology for your Business
By Lanrex on 8/12/16 4:30 PM
You’re ahead of the game, and you’ve just invested in what you thought was the next big thing for your Business. When all of a sudden everyone’s talking about Software as a Service, Business Intelligence, and a bunch of other things you’ve never heard of.
Maybe you were given some bad advice, or you just jumped on the bandwagon. Either way, it’s dawning on you that you were too impulsive. You can’t afford to be left behind!
If not executed correctly, IT can be expensive. Without the right support you can end up chasing new IT fads that fizzle out, investing your money in things you don’t need, and stuck in an endless cycle of constantly having to reinvent and reinvest in your systems.

While it’s easy to get lost in the headlines and the excitement about the technology, it is important to remember that ultimately it’s not about technology – it’s about business.
The right emerging technology can allow your business to:
- Run more efficiently
- Maximise profitability
- Compete with bigger businesses
What is the ‘right’ technology choice?
You might be the kind of person who likes to keep up with the latest gadgets in your personal life, but it’s an entirely different ball game in the business world.
Think of IT like fashion. Just because something’s in fashion, doesn’t mean it looks good on everyone. But many people will buy a new style because it’s ‘on trend’ – even if it doesn’t suit them. The same goes for IT. There might be a cool new technology or app that’s the talk of the town, but that doesn’t make it right for your business.
IT isn’t a one-size-fits-all. While cloud computing might suit most companies, for example, the strategy for how best to exploit it will vary.
There are also some other things to consider, such as how open your employees are to change. Sometimes, employees can be stuck in their ways and not want to change because they don't see anything wrong with the way they’re doing things now. If this is the case in your company, then you should be aware that you might experience resistance when bringing in new technology and changing processes.
Get an expert opinion
Even if you think you’re on top of emerging technology trends, it can be hard to know what they mean in ‘business’ terms. It’s a big job to sort through the noise and make clear-headed decisions about the most relevant technologies that will sustain revenue growth and enhance business operations.
There’s actually no reason to be pulling your hair – and wallet – out all the time to just keep your head above the technological waters – when someone else can do it for you.
Not sure of the impact of all this rapid change on your company? Talk to an IT provider who can provide an overview of what's going on in the IT space and suggest what will work best for your organisation.
There’s a difference in staying on top of trends and actually understanding them in the context of your business.
Without talking to the experts It’s impossible to accurately predict how every technology will impact your business or your bottom line, but it pays to be aware of this emerging technology as they occur and work proactively to respond to them before your competition does.
Business-driven technology
The Business owner who can use technology to increase efficiency and deliver better quality goods and services is more likely to succeed.
Adopting emerging technologies could be just the advantage you need to get a leg up on your competitors. But there’s no point investing in a new piece of software or hardware just because it’s "trending".
Any technology purchase needs to be part of a well thought out strategy – not just bought on impulse.
This is where an IT partner can help, as they will take the time to understand your business and make recommendations based on your needs and goals, and will explain to you what it all means in a language you can understand.
It’s all about staying flexible, and using the right emerging technologies to improve your business.
Download our latest ebook, Why Your Companies IT Strategy is key to Business Success.
The business owner’s guide to staying on top of technology trends
By Lanrex on 2/12/16 1:52 PM
Keeping up with developments in technology can seem like a full time job and you may be tempted to give it low priority. But if you’re running a small or medium enterprise (SME), you can’t afford to fall behind on advances that can save you time and help you grow.
All the tech that’s constantly coming out – and all the updates and upgrades that come along with it – can be seriously overwhelming. It can seem like a constant flow of new devices and apps, and then there’s buzzwords like cloud computing, mobility and big data to think about
How important is it to be ‘in the know’ about all the latest technology?
Put it this way – keeping ahead of technology is a necessity if your organisation is looking for:
- long term stability
- sustainable growth
- increased productivity
- more efficient business processes
- improved profitability
- competitive advantage
The problem is, most SME owners are consumed with day-to-day activities. It’s hard enough keeping things running as they are, let alone trying to grow. You keep putting off the things you should be doing for the future of your business just to take care of the daily maintenance.
If you do this for too long, eventually you’ll hit a plateau. Despite the hours you put in. If you’re not looking ahead, growth will stagnate and your revenue will stay the same – or worse – decline.
It’s at this point that you need to set up the processes that free up your time so you can focus on the future of your business.

Where do you start?
Technology may not be your forte, but small business owners should spend time understanding new developments on a regular basis either by developing the knowledge themselves or consulting an IT provider.
Try to identify the organisations in your area that are using newer technologies and spend some time with industry peers discussing what technologies they're deploying today and what they're watching for deployment tomorrow.
To start with, it’s a good idea to keep office technology under constant review. Be mindful that competitors and new entrants will more than likely be adopting new efficiency tools or hardware that makes their business run at a lower cost or deliver greater value to customers.
But with the flood of tech breakthroughs, how can you even begin to make sense of individual technologies?
If you have IT staff, this is where they can add some value. But while they may have a better understanding of technology trends, they might struggle to explain them in terms of business value. Plus, they’re most likely under the pump already, with little time to spend on other activities (especially if your IT infrastructure is not up to speed!).
What are your competitors doing?
Don’t think that your business is immune – any type of business can be affected by emerging technology.
However, just how important this technology will be to your business strategy depends on the industry you’re in. Some industries are years ahead of others in terms of technology adoption.
One example is the financial services industry, which has been rocked by the rise of financial technology – or ‘fintech’. Tasks once handled with paper money, bulky computers, and human interaction are now being completed on digital interfaces.
This has given rise to many startups who are disrupting the industry. In fact, over 20% of financial service firms are threatened by fintech startups.
Because of this, it’s never been more important – and urgent – for them to stay on top of new technology.
Get your priorities in order
In a world where the latest app or piece of time-saving software is just around the corner, staying up-to-date can be a headache.
One thing SME owners have very little of is time, and that’s exactly why you need to use it wisely.
While it’s important to be ‘in the know’ about developments in IT, outsourcing this service means you don’t have to spend your own time researching learning what may or may not work to your business.
Yes, you may have to bite the bullet and hire an IT partner to help you navigate the new technology, but isn't it worth it to see your business thrive again?
How these top 4 emerging technologies can benefit your SME
By Lanrex on 25/11/16 4:50 PM
Do you have big dreams for your business? Technology can be the key to making those dreams a reality. The words ‘small’ or ‘medium’ may accurately describe your organisation now, but they don’t describe your mindset or ambitions, but the amount of new technology is mind boggling and buzzwords like cloud, mobile and big data are probably all too familiar.
Here’s a simple run down of the top 4 of these emerging technologies, and how they are changing the way business is done.
1. Cloud & Cloud Computing
‘Cloud’ is the term used to describe the network of servers that host a business’ data, programs or services. Accessed via the internet, it’s the alternative to hosting them on your own hardware,
on-site. Learn more about the Cloud.
The cloud isn’t as foreign a concept as you might think. You probably already use some cloud services without thinking about it. For instance, when using personal email accounts such as Gmail and Outlook. Many SMEs are turning to cloud services for the cost and productivity benefits they can provide.
Offloading your infrastructure to an outsourced provider is a good way to access modern technology whilst lowering IT expenses, because economies of scale mean the cloud can store your data for a far lower unit cost than all but the largest organisations. It can also be used as a backup method, since data is stored securely in another location.
As long as you have reliable access to the internet and your network is up to scratch, you’re probably a good use case for the cloud.
2. Mobility in the Digital Workforce
Mobility refers to the shift to a flexible workforce, with more employees working out of the office and using mobile devices and cloud services to complete business tasks.
Mobile devices such as tablets and smartphones allow your team to work from anywhere. Offering remote work options can make for happier employees and help recruit future employees. If you're interested in mobility, click here to see the biggest mobility trends impacting small businesses.
The term refers not only to mobile workers and mobile devices, but also to the movement of corporate data. For example, an employee may upload a corporate presentation from his or her desktop PC to a cloud storage service, then access it from a personal device to show at a client site.
3. Productivity & Collaboration.png?width=300&name=20%20(1).png)
But it’s not just about wireless connectivity and employee demand – it’s about productivity and collaboration, and connecting in more ways than ever before. For this reason, communication solutions also come under the mobility umbrella. These include:
- Voice, video and web conferencing
- Instant messaging
- Desktop sharing
- Simultaneous document editing
Technologies such as these allow for better communication between staff, departments, vendors, and customers, which means more results for your business.
In fact, companies that prioritise collaboration are twice as likely to be profitable.
4. Big data
In a nutshell, ‘big data’ is the information owned by your company, obtained and processed through new techniques to produce value in the best way possible.
Of course, data collection is nothing new. What is new are the recent emerging technological advances in the internet, cloud computing, and our ability to store and analyse data that have changed the quantity of data we can collect.
We now have the ability to collect more information than ever before. In technical terms, this means bigger datasets, which is where the name big data comes from.
Know your customer...
But the real value lies not in the collection, but what you do with that data. Companies that are using big data to better understand their customers then target them are seeing the benefits.
A company can use the information and insights about their customers in the following ways:
- develop better products or services
- optimise business processes
- predict customer behaviour
- improve the customer experience
Big data essentially enables your business to move from being reactive to proactive.
One size does not fit all
Cloud, big data, and mobility are spoken about so much it’d be easy to think they are the solution to everything. However, like anything else in IT, there needs to be a strong, strategic case for using them.
In the end, what it really comes down to is your business’ needs and strategy.
Find out why your companies IT Strategy is Key to Business Success, with our free guide below
Insourced or Outsourced IT: What's best for your growing SME?
By Lanrex on 18/11/16 1:50 PM

As a small or medium size enterprise (SME) owner, you might find yourself stuck between a rock and a hard place. You’re at that awkward size where you need high-end IT in order to compete, but still find the cost (and effort) of hiring prohibitive.
If this sounds like you, you should consider outsourcing your IT function. This will give you access to the skills and expertise that keep a business ‘IT competitive’, without having to foot the bill for a full time team.
In fact, companies that outsource any specific technology function can reduce costs by as much as 30%. But it’s not just about saving money – it’s about taking the hassle off your shoulders so you can focus on what you do best.
To determine whether outsourcing is a good option for you, ask yourself these questions:
- Are my current IT systems reliable?
- How much time do my employees and I waste fixing both minor and major IT problems?
- Does my IT need handling in the short or long term?
- Do I have a big project coming up that may require additional IT resources?
- How much money am I spending by managing my IT in house?
- What cost savings could I make by outsourcing?
Should I outsource my IT & what should you outsource?
Handing over an aspect of your business to a someone else can be a scary prospect. Don’t worry – you don’t have to do it all at once. It may even suit your business to have a mix of both internal and external resources.
That’s the great thing about outsourcing – it can be tailored to suit your needs. A third party can act as a complete IT team, or complement the work your existing IT team does.
A good outsourced IT provider will take the time to understand your business, challenges, goals, and provide advice on which technologies are available to solve your problem.
So, the question might not be ‘Should we outsource?’ but rather ‘How much should we outsource?’
To start with, you should consider the following:
Infrastructure
Building your own IT infrastructure is neither cheap nor easy. If you’ve learned this the hard way, you’ll know that it requires not only a large budget to purchase and house the equipment, but also for IT to maintain it.
Outsourcing your IT infrastructure means someone else owns the equipment and is responsible for monitoring system performance. When you get rid of this responsibility, it frees up valuable resources that can help to grow your business. You can focus more on improving your offerings rather than maintaining a large, cumbersome system.
The Best IT Support
Computers can go down at any time. If you’re not ‘techy’ enough, or don’t have someone in your company that can help with this, you can sign up for a helpdesk service which will offer 24/7 telephone support, as well as onsite technical visits as needed.
This essentially means you have an IT team without the overhead costs. A helpdesk service will provide specialist skills when needed, and support the day to day IT demands of your business.
Backup & Recovery
The last thing you should be doing is wasting valuable time and resources cleaning up IT messes that can bring your operation to a grinding halt. Having a backup and recovery system in place is crucial for securing your data and ensuring you’re prepared if something unexpected happens.
Outsourced backups ensure that your data is safely stowed away in a place that cannot be affected by an incident at your business location – whether it’s a flood, a security breach, or just human error. It’s an extra line of defence against things that can harm your business.
A word on emerging tech...
In addition to these there are some newer technologies you may have heard about, such as cloud, mobility and big data. That’s where an outsourced provider can also help – they’ll advise you on which technologies are applicable to your business which saves you the time you’d have to spend researching. We’ll discuss these in more detail in next week’s blog.
Get back to business
Business owners know better than anyone that there’s never enough time in the day to do everything, but there’s not always enough money in the bank to hire someone to do it, either.
Outsourcing allows you to concentrate on your core business activities with the peace of mind that your IT systems are safe and secure – and you’ll save money in the process.
Isn’t it time you got back to business?
Find our why your companies IT Strategy is key to your businesses succes, with our free guide below.
4 signs your business needs an IT upgrade
By Lanrex on 14/11/16 9:23 AM

As a Small to Medium Enterprise (SME) owner, there will probably come a time when you need to take a serious look at your IT systems and make some calls about your ‘next phase’.
Every company uses some form of technology to handle business operations, whether it’s to process orders, maintain financial records, or communicate with customers and suppliers.
If you’re finding that operations are becoming less efficient as your business grows, and your staff are spending more time doing mundane tasks than important activities, it can be an indication that your technology needs an upgrade.
How can you be sure? By recognising the 4 key warning signs that your technology is creaking under the strain.
These are:
1 Your IT is Unreliable
By adding technology haphazardly, many SMEs end up with a mix of different hardware brands and software versions that don’t mesh very well together. While this patchwork approach can work for a while, eventually it’s going to cause problems. For example:
- Your systems are slow and/or crashing
- Your computers can’t handle even simple software updates
- You have regular print queue logjams
- Your network isn’t able to handle your web traffic
2 Your staff are complaining
If something about your business’ current IT setup isn’t working for your staff, they’re probably going to be vocal about it. But by the time it becomes your knowledge, they’ve probably been struggling with inefficient technology for a while.
Your staff are your best insight into the functioning of your business since they live and breathe the processes on a daily basis. If they express frustration at the hardware and software they’re using – listen!
It’s crucial for employees to be given the best tools for the job. For example, most PC equipment tends to slow down after a couple of years, so laptops and desktops should be renewed on an 18-24 month cycle.
3 You can’t do what you want with your IT
As more businesses transact on the move, you might be looking to make your workforce more mobile. A way to do this is by providing your staff with portable devices such as tablets and smartphones, but in order for these to be secure, they need to be properly supported.
This means the right IT infrastructure needs to be in place, which also enables you to add and remove users and devices with ease. It’s useless trying to use new hardware with old servers and networks.
The same goes for new software. It’s easy to get seduced into thinking that a new marketing automation platform or database for inventory is the key to selling more. But this is only true if the infrastructure that underpins the business – is sound.
There’s no point spending money on the latest cloud software if you’re going to leave employees suffering with a slow internet connection that can’t support it.
4 Your competitors are gaining ground
Keep an eye on your competitors and any new market entrants, as they’re likely to be adopting tools that make their businesses run at a lower cost or deliver greater value to customers.
This is particularly important if you compete with larger businesses, as they have more money to throw at technology, meaning your business will have to work extra hard to keep up. If you have old IT systems in place, however, you won’t have much room to move.
Slow and steady
If you’ve noticed some of these warning signs, it doesn’t mean you need to tackle everything in one go. A business IT upgrade can be very expensive – especially because fixing one component can cause a chain reaction where suddenly your entire IT infrastructure needs an overhaul.
The key is to focus on the practical aspects first. You can start by undertaking a total tech audit to understand what’s working and what’s not working. From here you can prioritise those urgent issues to ensure you have a solid foundation in place. Then you can start working to use technology to create an advantage for your business.
All you need to do is be familiar with the warning signs. If any of the above 4 symptoms arise, you know you need to take action. And when you do, your staff will thank you for it.
Find our why your companies IT Strategy is key to your businesses succes, with our free guide below.
Does your business actually need an IT strategy?
By Lanrex on 3/11/16 12:14 PM
If you run a Small to Medium Enterprise (SME), chances are you don’t have an IT strategy. Less than one third of SMEs do. And why would you have one? If it’s not your core business, IT just isn’t that important.
Many CEOs struggle to see where IT can offer added value to their business. The IT team is there to fix things when they break, or add new things just as they're needed. Having IT as part of the strategic planning process doesn’t seem necessary.

If your business has experienced growth recently, the technology systems you started out with probably aren’t serving your needs as well as they once did.
But if taking a patchwork approach to your business’ IT has worked for you so far, why change? As they say – if it ain’t broke, don’t fix it.
But if developing an IT strategy was guaranteed to save you time, money and frustrations in the long term - would you think differently?
Have you ever bought an expensive software tool only to find that no-one’s using it? Or that the impact it had on your business was not what you anticipated? This is the kind of thing you can avoid when you have an IT strategy. Any technology decisions are made to benefit the business in some way, rather than being on a reactive, ad hoc basis.
Kicking Business Goals
An IT strategy is really just about making IT work for your business, rather than alongside it. You may know how you want the technology to work for your business but don't understand how to make it actually happen, and that’s fine. All you need to do is share your business strategy with the IT department, and they’ll take care of the ‘high tech’ stuff.
For example, let’s say you’ve set yourself the goal of offering the best customer service in the industry.
Depending on your business IT might recommend:
- a simpler online interface to improve the customer journey
- a bespoke automatic marketing system on the back-end to promote cross-sell
- and a digital portal for customers to access extra information and see the progress of their project.
That’s potentially a huge step towards achieving your goal – and it came from getting IT involved at the strategy stage.
When IT understands the aims of the business, they can start to ask the right questions, and plan to build the right solutions...
If you don’t have a business strategy, it’s an opportunity to develop one involving IT. Your IT manager can assist in providing quick answers as to what may or may not be achieved and help point out any major advantages or disadvantages that IT will bring to the execution of the proposed strategy.
Unless you factor IT into your strategic planning or, even better, get the IT department involved then you’re going to be stuck trying to take over the world with the dated infrastructure you have now, with your IT team chasing and trying to build systems on the run.
No more guesswork
So, in an ideal world, what should your business technology strategy be doing for you? At its very core, the perfect IT strategy should be drawing a clear line that connects your technology and the meeting of your company’s goals.
You shouldn’t have technology for technology’s sake – your IT should be serving the needs of the organisation. A good IT strategy is driven by business requirements and future plans. Unless these are aligned, the strategy is no more than guesswork.
Technology could be your competitive advantage – or it could be your competitor’s advantage. You decide.
To understand more about IT being key to business success download the ebook, “Why your companies IT strategy is Key to business Success.”
Related articles: Business Continuity Strategy delivers a return on investment for SMEs
Business continuity strategy delivers a return on investment for SMEs
By Lanrex on 28/10/16 9:28 AM
Disruption is something every business wants to avoid, but it’s a reality many face. A disruptive event is anything that causes downtime or data loss – it could be as serious as a natural disaster or as simple as an employee deleting an important document.
Most Small to Medium Enterprise (SME) leaders understand the importance of a business continuity strategy in keeping the organisation functioning should a disruptive event occur. Yet, it can be difficult to see the value of Business Continuity Planning (BCP) beyond this point.
Unless your business experiences a crisis of some kind, it might seem that there’s no true Return on Investment (ROI). So if your business is ticking along fine, and you perceive the chances of a disruptive event occurring to be minimal, then you probably won’t make BCP a priority. Perhaps you don’t have a strategy at all.
Not just an overhead cost
Contrary to popular belief, you don’t have to experience a disaster to yield a ROI from a business continuity strategy. Reason being, BCP forces you to take a closer look at the inner workings of your organisation.
As we explained in a previous blog, planning for business continuity involves identifying your company’s RTOs and RPOs – recovery time objectives and recovery point objectives. The purpose of setting RTOs is to know the maximum time that you can be without your data before your business gets into serious trouble, whilst RPOs tell you how much data you can afford to lose without damaging your business.
Not only does this determine which processes are essential to continuing business operations, but you’re likely to discover new opportunities for cost savings or even revenue generation.

Ways a business continuity plan can deliver an ROI include:
- Identifying smarter investments – Without a deep understanding of business processes and priorities, there is a tendency to protect everything. This results in over-specified business continuity capabilities, such as the need to have ‘real time’ recovery for everything. Thorough BCP will define your organisation’s ‘risk appetite’; that is, how much risk your organisation is able to tolerate, meaning you’ll invest more where it matters, and save money where it doesn’t.
- Increasing efficiency – A coordinated approach to business continuity can help identify areas of inefficiency and overlap. Just because something ‘has always been done this way’ doesn’t make it right. BCP enables you to identify where savings could be made as well as gaps in operations or plans that may not have been revealed otherwise.
- Eliminating departmental silos – BCP will identify critical interdependencies and open the lines of communication between functions. Since successful implementation of a business continuity strategy depends on people as much as it does processes, it also doubles as a team building exercise.
- Providing a competitive edge – Being able to maintain operations no matter what will prove to be a competitive advantage in sales negotiations as well as investments. Organisations that have actionable and effective business continuity plans in place are considered to be more trustworthy and reliable. This means you’re likely to win more business because your clients trust you to deliver a product or service on a consistent basis, regardless of any business disruptions.
- Reducing insurance costs – Most SMEs have insurance policies that cover common business disruptions. With a business continuity strategy, you reduce your risks and are therefore better placed to negotiate your premiums with your insurance provider.
Start planning
The thinking that a business continuity strategy only offers value when something goes wrong means it’s not a priority for many SMEs with limited budgets.
But aside from the obvious value a business continuity strategy delivers – keeping your organisation running when disaster strikes – there are a number of indirect benefits. Neglecting business continuity planning means you’re missing out on multiple opportunities for a return on investment – regardless of whether you ever actually experience a disruptive event.
Business continuity programs should be seen as an asset to the business, not as an overhead expense. With a solid strategy in place, your business has an advantage over competitors who choose to go without. You can’t put a price on that.
Download your free eBook today on Backup vs. Business Continuity.
How SMEs can prepare for the mobile workforce
By Lanrex on 21/10/16 1:34 PM
Today’s workforce is growing much more mobile, and it’s forcing small to medium enterprises (SMEs) to re-evaluate how they interact with technology. Modern workers demand access to the corporate network on the go, and expect to be able to work anytime, anywhere. How can SMEs enable constant access to resources whilstkeeping data safe?
Mobile defined
In a report released last year, research firm Strategy Analytics estimated that 37.4% (1.32 billion) of the global workforce were considered ‘mobile’, and forecasts that this number will increase to 42% (1.75 billion) by 2020.
A mobile worker is defined as anyone who spends at least 10 hours per week away from his or her main workplace. Analyst firm IDC categorises these workers into three subgroups:
-
Office-based mobile worker: These employees spend most of their time in a company-provided office, but also sometimes work at home or in a third place.
-
Non-office-based mobile worker: These employees are more often at someone else’s office than their own. They are in the field, such as a salesperson, or working between buildings on a corporate campus, such as a project manager.
-
Home-based mobile worker: These employees spend most of the work week in a home office, but commute to the corporate workplace for meetings or collaborative work sessions.
The rise of Gen Y
While globalisation and the advancements in technology are the main drivers of mobile workforce growth, this trend is also being attributed to millennials – the digital native, mobile-first workers that make up Generation Y.
This generation of workers are used to accessing their data and communications tools on any device, anywhere, and seek out employers offering mobile working as part of the job.
New challenges
However, mobile working creates new challenges when it comes to building team relationships, shaping corporate culture, and managing people effectively.
Cloud computing is helping SMEs manage this mobile workforce and mitigate business leaders’ concerns about productivity. With a cloud model, your business’ data resides with a service provider, rather than on each desktop or somewhere on your network.
The cloud can run anything from your email to customer relationship management (CRM) software to video conferencing and store all of your documents. Employees simply log into a web-based service to access what they need, regardless of where they’re located – a sure-fire way to improve productivity and collaboration.
And because organisations don’t have to invest in IT infrastructure to support these workers, operating costs are driven down significantly.
These benefits are being realised by many Australian SMEs who are turning to cloud computing for workforce management. As reported by analyst firm Telsyte, more than half of all Australian organisations greater than 20 employees are now using the cloud for at least some part of their IT infrastructure.
The modern workforce
The way people work has changed – the workforce is no longer dominated by 40 hour-per-week employees who commute from their homes to the office and back again each day.
SMEs in turn need to make the changes necessary to compete in a rapidly changing, mobile-first world.
Allowing your employees to work flexibly will play a major role in boosting productivity, especially when you have a smaller workforce who can’t be everywhere at once. This can be achieved with the cloud, as organisations are able to improve operational efficiency and capitalise on commercial flexibility.
As millennials look to employers that accommodate their need for on-the-go access to corporate data, those organisations that embrace a cloud-based mobile strategy are the ones that will attract the best talent.
As a result, the ability to offer flexibility and collaboration – enabled by the cloud – can really set SMEs apart when it comes to recruiting top talent. So, not only does a cloud model enhance your organisation’s agility and efficiency, it also makes you an employer of choice.
Find out more about the Cloud and Cloud Computing with our free Coud 101 Guide, download below:
How SMEs use cloud computing to compete with big businesses
By Lanrex on 14/10/16 9:56 AM
Small to Medium Enterprises (SMEs) with a strong understanding of their markets are fully aware that employing technology will help them grow and compete. But when it comes to IT, SME leaders tend to think of it as a double-edged sword.
Even if you recognise that technology is critical to supporting growth, productivity and competitiveness, as a CEO you may not know how or where to integrate new technology into existing processes, or be able to justify the upfront investment required to get started.
Cloud computing offers SMEs a potential solution to this dilemma. With the ‘cloud’, smaller businesses have access to technology normally reserved for larger enterprises. This gives you the chance to gain a significant competitive edge, and allows you to compete in a much larger market space.
Size no longer matters
Bigger organisations have a lot of advantages relating to their size and scale that traditionally SMEs couldn’t match up to with limited cash and capability. One advantage is the ability to invest in strategic IT infrastructure to support business operations. If smaller businesses with little to no IT budget wanted to do the same, they had to free up – or borrow – the capital to purchase hardware and software, as well as the necessary security and maintenance, which doesn’t leave much money left over for other activities.
But the cloud has levelled the playing field. Now, SMEs can access sophisticated IT solutions as a subscription service, giving them the agility to adjust more quickly to the market and customer needs.
For many larger enterprises, this isn’t a reality. Most have already invested thousands of dollars into the development of IT systems that use ‘old style’ technology, requiring their own hardware and data centres as well as a 24/7 team of IT experts.
Many of these organisations have begun the move to cloud models, but are hindered by red tape and lengthy governance processes. In the meantime, SMEs have an invaluable opportunity to gain ground by being more agile and catering to the demands of an increasingly tech-savvy consumer. As a recent article in Business Insider Australia states, “Thanks to the cloud, small businesses are migrating to enterprise grade technologies faster than their corporate counterparts for the first time in history.”
Driving growth
At the same time, the cloud is playing an important role in helping SMEs to overcome some of the traditional barriers to growth, such as access to capital and skills, scalability and management control.
In fact, research from Google and consulting firm Deloitte found that making use of cloud technologies is the key to accelerated business growth. According to the report, ‘Small business, big technology: How the cloud enables rapid growth in SMBs’, organisations that use cloud services grow 26% faster and are 21% more profitable on average than those that don’t.
In the same study, 85% of SMEs surveyed reported that cloud technology enables them to scale and grow faster, while 66% said that the cloud allows them to outperform their competitors. It’s this ability to leapfrog other companies and scale rapidly that makes cloud an essential part of any SME’s strategy.
The SME’s time to shine
Cloud is turning out to be the ultimate equaliser – it grants smaller companies access to enterprise-level technology that would otherwise be inaccessible without substantial investment.
Now, with little to no capital expenditure, your business can have a capability rivalling that of industry leading corporations. As a matter of fact, your use of the cloud may even enable you to offer a slicker, faster and less staff-intensive service than those larger organisations can only dream of providing.
With the cloud, your organisation will be in the best position possible to overcome the odds and grow, and with the right ideas and execution, you can even be a threat to big market players.
What are you waiting for? Find out more about the Cloud now and dowonload our free eBook below. Cloud Guide 101
Cloud Computing - Are you 'Cloud Ready' for the future?
By Lanrex on 7/10/16 2:28 PM
The way people do business today has been completely transformed by the emergence of ‘the Cloud’. There is an idea that cloud computing delivers a sustainable competitive advantage for businesses and in particular Small and Medium Enterprises (SME).
This advantage can be achieved as it presents the tools to work smarter and quicker to capitalise on opportunities, utilising cloud and mobile technologies to help eliminate inefficiencies, facilitate flexibility, and ensure the agility and productivity of the organisation.
The cloud offers many benefits to organisations; however, this doesn’t mean that you are ready to transcend to cloud.
The Cloud is a broad term - in order for your business to take advantage, it is important to understand what is needed and which ‘Cloud’ service is best.
Going beyond the hype
Cloud computing’s recent emergence has only been in the commercial arena since 2006, and has become a popular technology solution. The cloud enables organisations to access on-demand IT services using internet technologies on a pay-per-use basis. This technology can provide many cost effective benefits for SME’s that typically have limitations on capital that could restrict their capability to succeed.
Owning your own on-premise IT infrastructure can be beneficial if your business system usage remains the same, however some businesses will experience periods of highs and lows which can result in expensive investments during busy periods, and wasted resources during quite periods. Cloud services can help your business scale resources as you need them, reducing capital expenses on hardware or software. Having unlimited access to cloud resources when you require them lets you get back to business.
Ensuring that your data is secure while in the cloud is also an important consideration but could mean a cost reduction as these systems are maintained by highly reputable companies with security experts. Some companies require that their system meet specific certifications and taking advantage of cloud services that already meet these standards results in reduced costs and maintenance.
Cloud technology is all about flexibility and scalability when you need it.
The cloud technologies can be combined with your existing infrastructure, expanding on the investments that you have already made for your business. There are 4 financial benefits of cloud infrastructure and these are important when making the decision to move to the cloud.
Readiness check
Before signing up for cloud services, it is necessary to first identify the needs and readiness of your organisation.
'Cloud Readiness' is a Lanrex assessment strategy which examines your businesses ability to adopt or integrate cloud services with your existing system.
A readiness assessment will determine whether moving to the cloud is financially conducive for your business in addition to identifying the return on investment of adopting the right cloud solution. Not all organisations are cloud ready and that’s OK. This assessment will help determine if a different approach may be of more benefit to the business in its current phase.
Many organisations aren't rigorous in analysing their ability to move to a cloud model, nor do they adopt comprehensive approaches for managing their engagement with cloud.
During a readiness assessment there are three key elements to consider:
1. What the business goals and models are
2. Your user base (numbers, training level, work styles etc.)
3. Existing physical infrastructure
4. Whether you prefer operational expenditure (OPEX) or capital expenditure (CAPEX)?
By taking these into consideration you will be able to decide on the right IT strategy for your business.
Do your due diligence
While cloud computing promises countless benefits to your organisation, a successful implementation from an IT managed service provider requires an understanding of the current business situation, the organisational strategy and the businesses goals.
Every business is unique and there's no one-size-fits-all cloud model. The best way for SME leaders to prepare their organisation for a potential cloud move is to engage in a cloud readiness assessment. This is guaranteed to save a few headaches in the future.
For more information about the different cloud models and services download our free Cloud 101 Guide.
The Infrastructure Advantage: How IT Gives Your Business a Competitive Edge
By Lanrex on 29/09/16 1:49 PM
Many SME leaders view technology investment as a necessary evil, so it will come as a surprise to them to learn that IT infrastructure can deliver demonstrable business value, and even a competitive advantage.
In this digital economy, business success is increasingly determined by the ability to compete in a high velocity environment. Start-ups with lean business strategies and agile methodologies are changing the competitive landscape and threatening incumbents. At the same time, technology is more affordable, accessible, and powerful than ever before, making it possible for every small to medium business owner to use tools that were previously only available to enterprise level organisations. This democratisation of technology makes SMEs a more formidable force against their larger, less nimble counterparts.
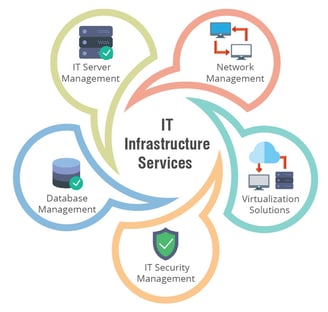
It’s high time that CEOs and managing directors got involved in the infrastructure conversation, elevating the importance of IT and making the right investments for the future of their organisations. The potential for, and magnitude of, an organisation’s success is contingent upon the quality of its foundation. If the business objective is growth, then the IT infrastructure supporting operations must be able to scale and accommodate the subsequent increase in demand. This comes down to having a solid IT strategy, which can make all the difference in delighting customers and beating the competition.
Humble beginnings
Businesses that aren’t technology-based typically start out with a ‘DIY’ infrastructure that gets the job done – they invest in basic hardware like desktop computers, laptops, a phone system, and a router for a solid internet connection. But as the company grows, the strain on the technology increases, resulting in issues around security, connectivity, and overall productivity.
When this starts to happen, businesses without an IT strategy will look for the quickest and easiest solution – which is not likely to be the best nor the most secure. As VP of research at analyst firm Gartner, Alan MacNeela, found, “SMEs are much less formalised or structured in their thinking about IT” and instead have an “opportunistic approach to IT investment”. He says, “Many SMEs have an older infrastructure and want to sweat these assets. This focus makes any new implementation of IT that would effect significant business change almost untenable”. It is this kind of thinking that hinders SMEs from reaching their full growth potential.
The empowered consumer
As is explained in a McKinsey & Co article, technology has completely changed the way consumers research and make purchasing decisions, as well as the way in which they interact with businesses. With access to more information via online and digital channels, today’s consumer is more informed, and not the passive receptors of sales messages they once were. Unlimited by geographical boundaries, they have more options available to them, and are empowered by choice.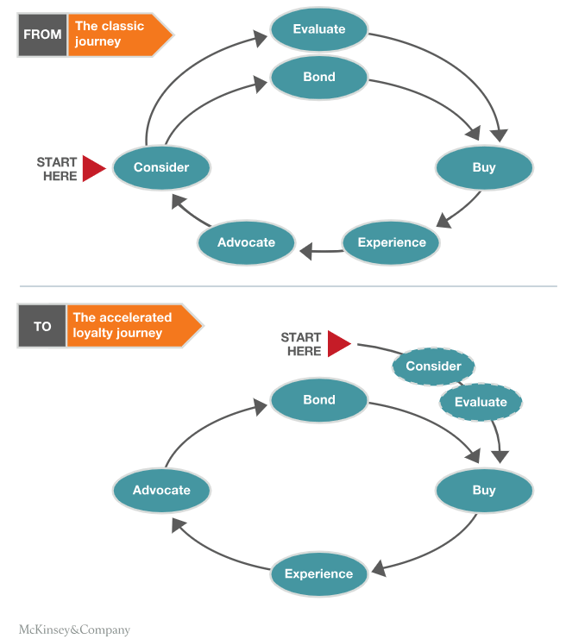
For SMEs who are doing more business online than ever, this means increased competition in domestic and global markets. These tech-savvy consumers demand that organisations cater to their mobile, connected lifestyles, and expect a seamless, omni-channel experience. For this to happen, the backend infrastructure needs to be in place, to ensure the right people, processes, and systems talk to each other, at the right time.
One of the main jobs of an IT infrastructure is to facilitate the exchange of information across the organisation. A strategic infrastructure – one that is current and reviewed – reduces the inconsistencies and communication barriers inherent in organisations, establishing cross-functional and interpersonal communications. If an organisation’s internal and external systems aren’t reviewed and optimised, efficiency and productivity suffer, and the customer experience is impacted.
In much the same way, employees are demanding a seamless user experience inside the organisation, one that is not offered by the dated or unsuitable hardware provided to them. Their preference for using familiar devices in the workplace is driving the trend towards mobile and remote working. This is something many SMEs are embracing, not only because it enables them to significantly reduce expenditure on hardware and maintenance, but it improves employee productivity and job satisfaction, as a recent TINYpulse study found. Again, however, this can only be achieved securely and be of commercial benefit to the organisation if the correct infrastructure is in place as part of a wider IT strategy.
Strategy first
The quality of an organisation’s technology determines its ability to innovate, grow and outperform the competition. To achieve business growth and competitive advantage, a strategic IT infrastructure is vital. Not only does it establish a solid foundation for growth, but it delivers a seamless experience for employees and customers, and is the catalyst for process efficiency throughout the organisation. Importantly, it addresses the needs of users today while being flexible enough to satisfy requirements as the business matures.
To understand more about IT being key to business success download the ebook, “Why your companies IT strategy is Key to business Success.”
Images courtesy of:
Fail to plan, plan to fail: why SMEs must have a business continuity plan in place
By Lanrex on 22/09/16 3:31 PM
 Business continuity planning is critical to an organisation’s ability to sustain operations during a significant business disruption.
Business continuity planning is critical to an organisation’s ability to sustain operations during a significant business disruption.
For small and medium sized businesses especially - a business continuity plan is essential. Larger enterprises can weather many storms, but it can take just one disruptive event to significantly damage a smaller organisation’s reputation and finances.
Yet in most SMEs, continuity planning is a neglected – if not omitted altogether – relegated to the bottom of the business priority list in order to make room for more ‘profitable’ activities.
Cybercrime on the rise
It’s not just natural disasters and one-off events that cause disruption to a business. Other common risks include breakdown of machinery and equipment, power outages, and theft.
Now more than ever, cybercrime and data breaches are becoming the biggest threats to SMEs’ survival. According to the 2014-2015 Australian Federal Police annual report, SMEs are more likely to suffer cyber attacks and data breaches than larger companies who typically have robust IT security systems in place.
Last year there 3,500 data breaches on average in Australia each month, and the AFP predicts that this number will rise. Ransomware in particular has become a popular attack platform in Australia. In 2015, the Australian Competition and Consumer Commission (ACCC) received over 2,500 ransomware and malware complaints, with over $970,000 reported lost by SMEs and consumers.
The financial repercussions from these attacks aren’t just limited to the immediate theft or data loss. They also include compromise to private intercompany communications and customers, vendor contract details, confidential business information and reputation, which all have an impact on future income.
For many business leaders it comes down to risk and reward. CEOs and business owners are not likely to jump at the prospect of budgeting for a ‘just in case’ plan with no apparent ROI, preferring instead to see the cash reinvested in productivity and research and development, or other growth activities.
Assessing the business impact
In many cases however, CEOs are reluctant to invest in business continuity planning because the impact to the business of potential downtime is not known. In this scenario, a Business Impact Analysis (BIA) is required to predict the consequences of disruption of a business function and process and gather the information needed to develop recovery strategies.
The first step in this process is to identify the aspects of business operations that are critical to its survival. This can range from the records and documents required daily to major business processes such as payroll.
The second step in a BIA is to determine how long the business can survive without performing these critical business activities. This means identifying an organisation’s recovery capabilities should disaster strike, defined through Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs). These are determined by reference to the impact on the organisation of interruption of business processes (and loss of recently entered data).
If an organisation has an in-house IT department, it’s important to involve them in the BIA process, as the third step is to map the outputs to IT systems. Technology is what enables the RTOs and RPOs to be achieved. Alternatively, an external IT partner can manage the entire process. This will likely be at a lower cost of managing the planning in house and has the added benefit of consultation with experts.
Fail to plan, plan to fail
Every organisation must address the need for business continuity planning, but many SME leaders don’t view it as a worthwhile investment. However, whether it’s equipment failure, theft, cybercrime, environmental impacts, or just user error, without a strategy, it may be impossible to recover.
SMEs need to invest time and resources to determine which systems and business units are most crucial to the company, and decide which people are responsible for declaring a disruptive event and mitigating its effects.
While more than anything it’s about people and processes, technology is a key component in ensuring business continuity strategies are effective. Whether engaging an IT partner or using in house resources, it’s important that business continuity challenges are faced head on to ensure the organisation is as prepared as it possibly can be.
To understand more about Business Continuity and how this differs to having a backup in place download the ebook, “Backup vs. Businesss Continuity.”
In search of enterprise social network success
By Lanrex on 19/09/16 9:00 AM

Despite early promise enterprise social networking has not yet lived up to expectations. Mostly because organisations have failed to get buy-in from all levels. New research reveals this is partially due to a level of suspicion that they will disrupt traditional hierarchies.
Back in 2012 the McKinsey Global Institute published a report The social economy: Unlocking value and productivity through social technologies. It was full of enthusiasm for the potential of social networking technologies to increase communication and collaboration in the enterprise and boost efficiency.
“The most powerful applications of social technologies in the global economy are largely untapped. By using social technologies, companies can raise the productivity of knowledge workers by 20 to 25 percent,” it said.
The report continued: “While 72 percent of companies use social technologies in some way, very few are anywhere near to achieving the full potential benefit.” McKinsey estimated that, by fully implementing social technologies, companies could raise the productivity of interaction workers — high-skill knowledge workers, including managers and professionals — by 20 to 25 percent.
So, given the pace at which digital technologies evolve and are embraced you might expect four years down that track that enterprise social networks would be a great success story, but you’d be wrong. Just last month, reporting the release of SpotCues, a new enterprise social networking product, the editor of FierceEnterprise Communications commented: “Most indicators suggest enterprises aren't using a social networking platform designed for business at this time. … Cracking the code for enterprise social networking hasn't been easy, and it seems to me that if it becomes a big thing, it's still some years away.”
This of course, is in stark contrast to the runaway success of personal social network tools such as Twitter and Facebook.
The big difference between these networks and the lukewarm reception of enterprise social networks lies in people: Facebook flourished because people wanted to communicate with friends and family. In the enterprise with its hierarchies, while increased online interaction would seem like a no-brainer as an aid to efficiency, the reality could be that those in control don’t want it.
The author of a mid 2015 Harvard Business Review article, headed “Why No One Uses the Corporate Social Network” talked of a top Silicon Valley technology firm that had installed an internal enterprise collaboration platform for its employee engagement and collaboration efforts — just the sort of organisation that you might expect to be making great use of the latest digital productivity aids.
However, she reported: “After an initial spike in adoption, usage slowly dwindled. It was a disappointing outcome and they wanted to know how to fix it, or if they should maybe just toss it out and invest in a new platform. The reason: the top executives didn’t see collaboration and engagement as a good use of their time, employees quickly learned that they shouldn’t either.” In particular: “More than anything else, [the top executives] fear that engaging will close the power distance between them and their employees, thereby lessening their ability to command and control.”
She offered senior execs some advice, and an example from none other than then Telstra CEO David Thodey. “He used it to ask, “What processes and technologies should we eliminate?” The question received over 700 responses within the first hour, and gave Thodey an immediate and intimate look into what wasn’t working at Telstra. But more importantly, Thodey and his executive team used the platform for the follow-up discussion, signalling that they were serious about creating a dialog to make making meaningful decisions in digital channels. By being responsive and closing the loop digitally, Thodey demonstrated that employee participation made a difference.”
Relationships and collaboration are fundamental elements of any business transaction. A technology platform that encourages dialogue, relationship building and collaboration has got to be a good thing? The organisations that have been able to overcome the fear of hierarchy disruption are the ones that will continue to benefit from implementing an enterprise social network.
About Lanrex
Cutting IT costs now will only cost you more in the future: Part 2
By Lanrex on 16/09/16 12:37 PM
Technology has become ubiquitous across all business functions and is critical for success.
However, as we discussed in a previous blog, many business leaders hold the outdated view that IT is a cost centre, and are blind to its potential to drive growth and business performance. And as technology becomes more available ‘as a service’ and its cost decreased, IT is being regarded and managed as a commodity.
Technology may be more essential than ever to society, but from a business leadership standpoint, it becomes invisible. As a result, when resources are tight, technology spending is often the first thing to be cut . The unwillingness to invest in IT and stress to cut IT costs can cause CEOs to make decisions that prove to be far more costly in the long run in terms of lost dollars and lost business opportunities.
Cost vs investment
With the advent of the cloud, IT components such as servers and storage have become commoditised, but for business leaders to dismiss them as such “is a mistake” according to McKinsey & Co. In an article titled ‘Where IT infrastructure and business strategy meet’, the authors explain that “…an effective infrastructure operation creates value by making sound choices about which technologies to use and how to integrate them.
A technology product purchased from a vendor may be a commodity, but the ability to bring together hardware, software, and support to provide the right combination of cost, resiliency, and features for a new application isn’t.” The article cites real life examples of organisations using IT infrastructure and digital technologies to increase efficiency, employee productivity, and speed to market, improve customer experience, and even redefine their business models.
The danger of viewing IT as a commodity is that it results in an inability to align technological resources with business objectives, preventing organisations from seeing real business gains. A weak IT strategy can be costly and wasteful, especially for resource-constrained SMBs. It also limits agility, meaning organisations aren’t able to respond to changing business requirements rapidly enough. The absence of strategic thought causes organisations to be reactive, forcing them to work in a constant state of catch-up.
Smarter spending
In most businesses, IT budget approval – if there is an IT budget at all – occurs at the CFO or CEO level. Yet, according to a Tech Pro Research survey conducted in August of last year, those approving IT budgets are focused on the return on investment and total cost of ownership (TCO) projections for the IT projects that they are considering for approval. This highlights the cost saving attitude, and when business leaders look solely to the IT function to find savings, the results are often limited. In fact, as an Economist Intelligence Unity survey of 536 business leaders found, organisations that recognise the value of their IT resources perform better in their markets. Of the 37% of CEOs who said they had a business-driven IT strategy, 47% said their company financially outperformed the competition. On the other hand, among the 20% of respondents who said the CIO had no role in business strategy, only 28% said they were performing better than industry peers.
In some cases, cutting IT spending can have dire consequences. Common IT victims in budget cuts are risk mitigation aspects of IT and IT disaster recovery. As one IT leader said to CIO Magazine, “Too many times I've seen [business continuity] initiatives slashed upon budget review, only to haunt executives months later and cost the company many ‘factors of ten’ more than the original budgeted project. Just because you have never experienced an IT disaster, does not mean you wait for one to prove the need for disaster planning and business continuity.”
While spending more on IT won’t automatically boost profits, smarter, more targeted investments will. In a January 2016 article, ‘Spend wisely, not more, on IT’, McKinsey & Co cites recent research into the banking sector, which found that, while the amount spent on general application development did not impact banks’ bottom lines, investments in areas of IT functionality, such as automation in customer analytics and big data, correlated to higher profitability.
Dollars and sense
To many SMB leaders, IT is a cost centre rather than a business enabler. As a result, they are reluctant to recognise and support the role technology can play in business transformation and growth. With technology becoming increasingly commoditised, some organisations are investing in IT, but without an understanding of how it fits into the context of what their business is trying to achieve, these investments are made in vain.Regardless of what size your business is now, a comprehensive IT strategy can help to reduce long term IT costs, increase efficiency and effectiveness, rule out the myriad of options that aren’t part of your focus, and help your team set goals and focus on the future success and profitability of your organisation. Executives should spend smarter – not necessarily more – on information technologies. For those whose core business isn’t in IT, consultancy with a technology partner is usually the best option.
To understand more about IT being key to business success download the ebook, “Why your companies IT strategy is Key to business Success.”
Cutting IT costs now will only cost you more in the future: Part 1
By Lanrex on 9/09/16 11:10 AM
Small and medium size businesses face daunting competition from larger enterprises.
We live in a world of ubiquitous connectivity, where technology permeates every aspect of our lives. The proliferation of smartphones and other mobile devices, normalisation of cloud computing, and growth of data and
analytics present opportunities and challenges for businesses of all sizes. In an increasingly competitive global market, SMBs need to work particularly hard to ensure they are getting everything out of their technology dollars.
Currently, there is a lack of understanding from CEOs and directors of IT’s commercial benefits and how it can contribute to business growth. SMBs that fail to capitalise on the strategic value of IT are those that have failed to appreciate the business’ ability to create competitive advantage. This problem is further compounded by the absence of a well communicated and clearly defined IT strategy, which increases IT costs and makes it difficult to align technological resources with the strategic objectives of the organisation. The consequences of a missing IT strategy can be huge and will often result in missed opportunities to use technology to accelerate and achieve critical business performance improvements.
The tech savvy CEO
In this market, it’s no longer acceptable for business leaders to plead ignorance about technology. Just as the CEO is expected to be across the financials, he or she must be across technological matters. This doesn’t mean becoming a technology expert; business leaders depend on a financial controller to advise them on commercial strategy, and the same goes for IT strategy. If your core business is not IT, the technical details are best left to an in house specialist or external partner, but at the very least, CEOs should have an understanding of how IT can drive business performance, operational efficiencies, and improvements in customer experience and engagement.
As PwC states in a 2015 report, “As IT knowledge is specialised, it may be impracticable for directors to have this expertise. So in order to provide boards with deeper expertise to leverage when exercising their oversight responsibilities, external consultants are often enlisted as advisors.”
CEOs and directors of larger organisations are ahead of the trend in recognising the importance of IT to long term business strategy and success. PwC’s annual study of corporate directors (the results of which are outlined in the aforementioned report) found that “Directors have become more engaged with understanding how traditional and emerging IT issues impact the company’s long term strategic goals … [which] demonstrates a commitment on the part of directors to ensure an approach that aligns technology and business strategy.”
In the survey, 83% of directors stated that they were at least “moderately” engaged with understanding the status of major IT implementations. In its assessment of smaller companies, however, PwC found that directors had “less confidence that their company’s approach to IT strategy and IT risk mitigation is supported by a sufficient understanding of IT at the board level,” with 33% of directors believing their understanding “needs improvement”. If SMBs are to be competitive in an increasingly technology-driven world, they need to follow their larger counterparts’ lead.
Partner up
CEOs need to take charge of their company’s technology agenda for growth and success, and shouldn’t be afraid to look externally first for business IT services as it’s not wise to play in a space they don’t have the expertise in. A technology partner will work to understand organisational requirements first and determine the technology that makes the most business sense. This might mean expanding on premise IT or moving to an external environment.
The starting point for any IT strategy is the availability of computing infrastructure and resources. SMBs who plan on expanding existing IT infrastructure are faced with a costly upfront investment and the use of limited capital, whereas cloud-based services are paid for via a subscription or an as needed payment model, saving capital for other key investments and activities. In addition, the ability to scale services up and down quickly enables IT to better align with real business cycles and meet fluctuations on demand.
Of course, depending on the organisation and industry, there will be some operations that are far too important not to keep on site, and it is wise to work out which resources and skills are needed to manage these systems prior to deciding on an outsourcing strategy and evaluating your IT costs. Only then can the business ensure that anything it decides to build internally and operate itself will deliver a comparable user experience, be equal or superior to the standards of an external service provider, and be delivered at a competitive cost.
Growth-driven IT
As more and more organisations compete in technology-enabled business environments, CEOs and directors must take responsibility for driving growth by leveraging technology advancements. Technology may be outside the CEO’s comfort zone, but an IT strategy needs buy in and involvement from senior management if it is to be successful. As such, it’s important for all CEOs to understand the role of technology in driving performance if they want to grow their businesses, especially in this digital era.
To help you decide if outsoucing is the right option for your business download the ebook, “Should I Outsource My IT To A Managed Service Provider.”
The importance of a digital workspace
By Lanrex on 5/09/16 9:00 AM
Drawing a connection between the sharing economy and the need for a digital workspace may seem to be stretching it a bit, but that’s exactly what consultancy ClearPeople does in its white paper Introducing the Digital Workspace. It argues that the internet has shifted our collective psychology away from attaching prestige and emotional value to ‘ownership’ to “the simplicity and freedom of borrowing and sharing.”
So how does that translate into the digital workspace?
“Individuals are feeling less attached to their desks, their tools, their intellectual property and their business functions,”
In a work context this could mean that the senior executive with his own office will be seen by his digital native subordinates as more of a digital dinosaur than a digital strategy leader.
ClearPeople defines the digital workspace as “a collection of evolving technologies that optimise employee experience and engagement with the tools and resources they require, anywhere and on any device, allowing them to be more effective.”
There is nothing in that definition that is technology-specific, which means two things: that the definition will stand the test of time; that creating the digital workspace is not a one-off project but a continuous process.
As the white paper says: “The businesses that succeed in the long term will be those that focus on the journey rather than the destination. There will never be a ‘right’ or ‘wrong’ time to invest in the digital workspace; it’s a continuous improvement on both technical and cultural levels: its implementation and evolution spans every aspect of a business.”
As Capgemini Consulting observes in its report The New Digital Workplace Employee Productivity, Brand Image, Business Value: “Transforming the traditional workplace into a digital workplace involves reinventing the working environment, taking control of the disruptive digital technologies, optimising capital costs, while providing a new end-user experience.”

It argues that the digital workplace is not just a pure IT topic. Rather “It’s an opportunity for companies to become end-user centric in order to activate new performance levels. By doing so, the digital workplace will be considered as an overall company asset, which is critical for the business just as any other core services.”
Because the implementation of a digital workspace has impacts across an organisation it’s likely to have many champions (and a few detractors) and different C level executives vying for ownership. Capgemini argues that the CIO is best placed to take this role.
Take Ownership of the Digital Workforce
“By taking ownership of the digital workplace, CIOs become enablers of the digital transformation, fostering behavioural changes of stakeholders and end users… The workplace is one of the few topics that impacts the vast majority of users in a company: it is now time to address it globally. Furthermore, without clear ownership of the digital workplace in the organisation, the CIO can leverage this opportunity to extend his/her footprint and move beyond simply implementing new IT services.”
It continues: “By embracing these new digital technologies and digital strategiesthe CIO will strengthen and develop his/her strategic position within the digital ecosystem, improving employee experience, regulating innovation intensity and optimising costs.”
Capgemini, too, makes the point that the digital workspace is a journey not a destination, and a journey that is being taken at an ever-increasing pace in line with accelerating technological evolution.
It urges every CIO to launch a technology watch program “to identify the potential value that the emerging technology such as cloud computing brings to the business and the share of users who are likely to be impacted due to the arrival of an emerging technology in their workplace.”
Use IT Managed Services
Having IT problems? Finding the best IT support and services can be hard. That is why at Lanrex we have created a range of useful online tools to help you and your business in finding the best IT Support.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
You mightt also like, Does your business actually need an IT Strategy?
Want to boost your organisations productivity with Yammer?
By Lanrex on 31/08/16 10:00 AM
Communication technologies have always been changing – we’ve used carrier pigeons, telegrams, telephone, fax, paper, email and now we have Enterprise Social Networking (ESN).
For many executives this term “social networking” does nothave a place within their business. Since the first thing that comes to mind is seeing their team engrossed in cat videos and silly jokes being passed around the workplace.
When proposing ESN often the first reaction is “We don’t need people wasting their time having unnecessary chats online”. My response is ESN is just a communication technology - rather than thinking about new conversations happening online think about all the conversations you already have in your business – then ask yourself could any of these interactions be more efficient if taken online?
Here are 8 key reasons ESN is great for your organisation and studies have shown those organisations who embrace social technologies see 20% to 25% boost in productivity*
1. Get access to experts and information fast
Traditional organisation structure is hierarchal, which means if you need to find information you may ask someone in your team, or ask your manager who may or may not ask their manager or a cross departmental head, normally with a number phone calls or emails passed around. You can spend hours waiting for information. With ESN you can access people and information much more quickly and rather than a hierarchal structure it’s a one to many.
2. Have answers ready to those questions that are being asked repetitively
There are a lot of repetitive questions being asked on a daily basis
- Where can I find the latest travel policy information?
- Who is the best person to help with this...?
- I’m new to the company where can I find…?
With ESN questions being asked and answered can be viewed by others and easily searched.
3. Share news and announcements
How many emails do you have in your inbox sent to large groups such as “allstaff”? Quite a few I’m sure and if you’re sending documents or images you’re creating multiple copies of the same information on your network. Because it’s sent to all staff you may not even be sure if everyone has read it or maybe they did read it and everyone in your organisation is also filing a copy.
With ESN when you create an announcement you’ll be sure everyone has read it and there is no need to duplicate files across the network. For general news such as a great customer experience story it creates a real buzz across the business as everyone will be aware and the same is true for something you need to act on quickly.
Too often in group emails, employees forget to hit the 'Reply All' button, this means that a large percentage of the information being shared could potentially be lost as it is not shared properly, through the use of an ESN by commenting directly on the post we can easily ensure that every member is able to access vital information.
4. Discuss major decisions and prepare for change
We all experience change and the only thing we know to be constant is change. One of the best ways to implement change successfully in your organisation is by bringing your team in and as early as possible. ESN is a great way to communicate major decisions and prepare your team for changes. By having the freedom to ask questions and have questions answered in an open forum, a lot of the anxiety about the change can be reduced.
5. Gather options and ideas from across the company
Have you ever wanted to get feedback on an idea or take a quick poll? You’ve crafted a nicely worded email and only to find your response rate is really low or worst zero. With ESN you can create a quick poll with voting buttons or response options, people can include comments and responses are shared with everyone.
6. Gain visibility and insight on what’s happening and where
Managing your email in some cases can be a full time job, especially if you’re cc’ed on multiple emails just to keep you in the loop. Reading, filing or deleting email is time consuming. What if rather than being cc’ed on all the correspondence you could digest the information across teams and departments in an easy to consume format. Wouldn’t life be great! The cool thing is you’ll be aware of questions, conversations, good news – things you may not be aware of now.
7. Introduce new hires and get them up to speed quickly
On-boarding new team members is a crucial step in their success in your organisation. You do need a plan/process and it can involve multiple people. What if you could create an on-boarding process and a place for new hires to ask questions – as each question is answered you’ll have a knowledge base or information for new hires and you’ll also know where maybe some of your on-boarding processes can be further improved.
8. Work in teams and workgroups, collaborate on ideas
Working in teams and groups is a fundamental part of doing business, having the right tools that enable us to share ideas, documents or collaborate on an idea makes a real difference. Things like plans and documents can be updated and shared very easily.
Overall how you take advantage of ESN in your business will depend on how you work today, but using the above examples I’m sure you’ve seen a few which also resinate in your business.
One example on how we at Lanrex use ESN is sharing our Core Value stories. For example we have 4 core values and each time we live and breathe our core value we’ll post the story. Sharing our positive values stories not only help to reinforce our values but creates a really positive culture where we are truly living and breathing our values on a daily basis.
With Microsoft’s ESN software Yammer included with the Office 365 subscription is makes good sense to take advantage of ESN in your business so you too can get 20% to 25% productivity improvement in your business.
* Source: McKinsey, The Social Economy
Improving results with a CRM and IT strategy implementation
By Lanrex on 31/08/16 8:30 AM
The Business Need
The SME Team within DUAL work with brokers on a day-to-day basis on new business opportunities. Prior to January 2016 a review of their current processes highlighted areas which could be improved, particularly the recording of phone conversations, email and meetings with brokers. Comprehensive reporting was required and the implementation of an efficient workflow tool.
Key Challenges
A number of issues had to be addressed—
- The ability to record and track activities done by the SME Team to realise new business opportunities
- Opportunities were recorded using Excel spreadsheets and MS Access which were not updated efficiently and were open to error.
- The lack of a centralised database containing information about all the brokers the SME Team worked with.
Solution
Lanrex were already engaged by DUAL to provide IT services and were consulted by Frances Land, the SME Team Leader for a possible solution which addressed their revised operating requirements. The SME Team needed a workflow strategy tool and Lanrex proposed Microsoft Dynamics.
Frances worked closely with Lanrex to ensure they had a thorough understanding of the issues and DUAL’s requirements. She also worked closely with Lanrex during the implementation, doing testing and quality assurance.
Frances is very satisfied with the outcome, she commented, “It is a fantastic system which meets our needs and Lanrex have provided a great response to any changes we required.”
The SME Team are now able to—
- Store and access all information about its broker firms, broker contacts and opportunities from a centralised database
- Managers are able to seamlessly assign and manage opportunities
- View the progress of opportunities online using the Dynamics dashboard and via various reports
- Record their own activities using a simple interface, which also enables them to monitor their own performance.
Key Outcomes
The solution was implemented in January 2016 and has proved to have the flexibility required to meet the needs and expectations of DUAL. The real benefit has been establishing effective workflows for the SME Team to increase their efficiency and improve their results.
The Results
Microsoft Dynamics is integrated with DUAL’s online quoting system which provides the opportunities for the SME Team to then work with the relevant brokers and track any subsequent activities.
The interaction with Office 365 has provided substantial integration of tasks, eliminating double handling and reducing operational errors.
The Dynamics dashboard with features open to all users has also stimulated healthy competition among the team members.
Frances Land complimented Lanrex on their professionalism, “Lanrex has a really good positive attitude. They are helpful and never short of a recommendation.” Frances added, “We do insurance, not IT and Lanrex has a very high level of expertise.”
The Future
Lanrex is working on a number of projects with DUAL enhancing not only IT but their overall business strategy.
About DUAL Australia
Established in 2004, DUAL Australia Pty Ltd is a specialist underwriting agency providing innovative insurance solutions for small to medium enterprise.
DUAL specialise in accident and health, financial lines, general liability and marine insurances. The agency also underwrites exclusively on behalf of certain Underwriters at Lloyd's which has an S&P rating of A+ and since the late seventeenth century, has been the name which is synonymous with insurance.
DUAL has implemented an online trading platform enabling brokers to obtain instant quotations and bindings 24 hours a day, 365 days a year. It is regularly used by over 650 broking houses across Australia and resulted in more than 30,000 policies being transacted every year.
Employing more than 80 people DUAL, has four offices across Australia in Sydney, Melbourne, Perth and Brisbane.
Related Article
Driving sales with a comprehensive CRM system
Ageing IT: Common Infrastructure Issues
By Lanrex on 30/08/16 11:55 AM

For every technology product (hardware or software) there is a point in its life beyond which it will be more cost-effective to retire and replace it than to continue using and maintaining it. The difficulty is determining that point to minimise costs and maximise operational efficiency.
-
Do technology advances in the product make it cost effective to replace one piece of hardware, or software with a new one?
-
Do software developments make it cost effective to replace aging hardware with new hardware to take advantage of those developments?
-
Old hardware fails more often. Does the cost of repair outweigh the cost of replacement?
-
What is the cost to the business of failures? That cost is likely to be much greater than the direct cost of failure, and could well present a compelling case for a hardware upgrade.
Even if you have all the data on maintenance costs, failure rates, replacement costs, business impact costs of failures, there’s some pretty serious calculations required to determine the optimal time to replace ageing infrastructure.
To some extent the answers are specific to each business, but fortunately research firm IDC has done a lot of the legwork and come out with some generalisation. For starters, IDC says, its studies of mid-sized companies show that revenue losses resulting from downtime caused by IT failures averaged $US75,000 per hour, and that the average business experienced 15-18 hours of downtime annually as a result of network, system or application failure.
In a white paper, The Cost of Retaining Aging IT Infrastructure, IDC found that, for the x86 servers at the heart of most data centres, failure rates began to climb in the fourth year of life, that upgrading resulted in a return on investment (RoI) of more than 150 percent over three years and that there was a payback period of just under one year.
According to IDC, aging software also causes problems, beyond what it says is “three-year optimal life” for which most software is designed. “Patching becomes a more frequent activity — and most companies lose interest in keeping up with the more frequent upgrades. Migrating to newer software while running on the same hardware platform creates compatibility issues and business alignment issues of its own.”
To assist organisations with the retain-or-replace decision for IT infrastructure, Gartner has developed a series of ‘Market Clocks’. According to Gartner these “explore the entire life cycle of technology assets–from introduction to replacement and obsolescence.” They are “designed primarily for buyers, to help them plan investment, and divestment, strategies for their technology portfolio.”
They also “explore relative commoditisation of asset groups, helping buyers evaluate their ability to influence price reductions.” But they don’t factor in the cost of IT failure induced downtime.
Calculate your cost of downtime with our Downtime Calculator.
You might also like, Four financial benefits of cloud infrastructure
In search of 'Edge Computing'
By Lanrex on 25/08/16 5:30 PM

In recent years there’s been a massive migration of processing and data into the cloud, but powerful though the arguments are for centralising computing and resources in large data centres, it’s not a suitable architecture for all applications.
We’re not talking here about some of the usual arguments against cloud, such as data sovereignty and control. We’re talking about issues of latency — the need to process data and make decisions on it close to its source – and the need to reduce the sheer volume of data, much of it redundant, that can be generated by some applications. Welcome to the world of cloud computing, aka fog computing.
Edge computing is very much a child of the Internet of Things. Some of these things – of which there will be billions – will generate massive amounts of data. In some cases most of it will be redundant. In some cases it will require an instant response: hence the need to decentralise compute resources to the edge of the network, near where the action is.
Fog computing is a term coined by Cisco for its version of edge computing.
It seems to have made its debut in an academic paper from 2012. Originally it was received with some scepticsm. One critic branded the concept “an ill-conceived marketing metaphor that further confuses the cloud market,” saying it represent a reason why “reporters should be trained not to parrot the marketing hype of large companies.”
However, far from clearing, the fog has thickened, with the launch in November 2015 of the Open Fog Consortium with founding members being Cisco, chipmakers ARM and Intel, Dell, Microsoft and Princeton University, through the Princeton University Edge Laboratory.
But, to get back to the more generic concept of edge computing. Fog Consortium members Intel, Dell and Microsoft all have their own implementations of cloud computing. Intel and HP announced in November 2015 that they would jointly develop cloud computing products. Akamai has teamed up with IBM. Dell announced its Edge Gateway in October 2015.
All these vendors have their own take on edge computing. If you want to get a more neutral overview, a good place to start is the white paper The Drivers and Benefits of Computing from Schneider Electric.
As a provider of data centre infrastructure, its pretty agnostic to the processing and data architectures it supports. The white paper “explains the drivers of edge computing and explores the various types of computing available.”
While cloud computing can be implemented in small devices out in the field, Schneider is in the business of supplying data centre infrastructure. So it suggests there is a whole gamut of implementations stretching from devices through localised data centres with one to 10 racks and regional data centres. It concludes an optimal architecture that “provides the deployment speed and capacity in line with future IoT application demands are the localised 1-10 rack versions.
However the model chosen will be very dependent on the number of IoT devices, the volume of data and the nature of the application.
How successful is your IT strategy? Not sure, download our Free guide below to why your companies IT Strategy is key to businesses success.
Why Data Backup alone is not enough
By Lanrex on 25/08/16 5:30 PM
For years you've been hearing about the importance of data backup - 'Just ensure your data is backed up and everything will be fine...' Well... that's not quite the case - data backup alone is not enough.
For one thing you have much more data than you used to and most likely your data is more important than ever before. Viruses, systems failures and disasters are always looming, meaning the risk of losing your data has never been higher.
What you need... a Business Continuity solution that ensures your backed up data is:
- Usable
- Non-corrupted
- Virus-free
This means when a disaster occurs and someday one will, you'll be back up and running in no time and your data will be usable and intact.
However not all Business Continuity solutions are created equal, so we’ve listed some of the things you should look for:
1. Make sure your data backups are image based
While a file-based backup handles file backups (slowly) - one file and folder at a time, image based backups take a picture of entire machines. Image based backups happen so quickly and seamlessly users won't even notice its happening and restores are fast - taking seconds not hours or days.
2. Ensure backups are stored both locally and securely in the cloud
This allows you to conveniently pull backups from an onsite device. But, let's say your office gets flooded - there goes your local backups. Having your apps, files and systems in the cloud saves you and your business. Some providers enable you to open and use your systems directly from the cloud.
3. Ensure your backed up data is tested for validity
For peace of mind you want to know your backed up data is tested for validity. A good continuity solution examines each backup automatically to ensure everything checks out. Some solutions even send screenshots of your backup verification via email.
4. Ensure your solution will grow with your business
Finally, you want to ensure your backup solution can be easily upgraded as your business grows. Don't get stuck with an expensive upgrade that requires you to lose all your backups and start over.
So while having your data backed up is a solid starting point having a Business Continutity plan will ensure your data backup is usable, non-corrupted, virus-free and quickly recoverable taking just hours, not days- Or worse not at all.
You might also like this related article, How much does your downtime affect your business?
Driving sales with a comprehensive CRM online system
By Lanrex on 22/08/16 8:00 AM
The Business Need
With a sales force located in a number of locations and supplying a wide range of products for a number of industries, UES realised they need to move beyond spreadsheets and multiple information sources to consolidate their sales data and increase efficiency.
Key Challenges
They had used a Customer Relationship Management (CRM) system in the past but it did not suit their environment, which led to frustration and staff backing away from using it. An effective salesforce, they were not IT gurus but busy technical representatives who needed to realise the benefits of a CRM Online for it to be accepted.
Reporting through various levels of management was critical, particularly given the number of office locations and product lines involved.
Solution
A system which suited the UES requirements, that was straight forward and easy to use was mandatory.
Lanrex already provided a comprehensive IT support service to UES and were approached to investigate and advise on an appropriate solution for the sales team and senior management.
It was also necessary to have appropriate fields and check boxes to enable filtering on products, clients and issues. This is where Lanrex played a key role, designing the database structure to suit UES requirements. Microsoft Dynamics CRM has been implemented to provide the required functionality.
Lanrex provided application training both face-to-face and remotely via Skype. This has since been followed up with further training and a workshop during a recent sales meeting in Sydney. This included Lanrex discussing options with the sales team and drawing up a wish list for future developments.
Peter Criddle the General Manager Sales appreciated how Lanrex took the time to understand the UES business and their requirements for a CRM. Peter said, “Jodie Korber didn’t assume she knew it all and listened to what they had to say.”
The Results
Regular reporting has now been achieved at all levels within sales from the account representatives to the branch manager and to senior management. The sales team has an effective electronic diary recording all aspects of customer contact, with alerts for follow-up and future activity.
UES staff are able to filter the data by such things as product, issue, or specialist with the ability to focus on a particular product line or market or combinations of fields.
The sales team is able to now access the CRM remotely using iPads to record meeting information as it happens, which is then available to all users for any required follow-up.
The Future
The CRM has the functionality and flexibility to enable UES to expand its use and this is on the agenda for the future.
According to Peter Criddle, Lanrex is always available and quick to respond to any issues raised. “They make recommendations, they don’t dictate on how to do things and you never feel you have to fit into a box.” “We haven’t felt we need to change our business, our way of doing things, to suit the system, it has been made to work for us.”
This has given UES the confidence to expand the use of the CRM broadening the scope of the information they will be able to achieve from their sales data.
About UES International
Established in Australia in 1904, UES International has achieved steady growth, expanding to a number of overseas markets, leading globally with its design, manufacturing and supply divisions.
UES is still an Australian family owned company, with specialist products in seating, industrial, marine and transportation hardware. Their transport business is focused on public and commercial transport, service vehicle and equipment hardware products. Specialised industrial products are used extensively in sheet metal fabrication, electrical and electronic housings to service the mining and oil and gas industries.
Offices are located in all Australian States and Territories and in New Zealand.
Related Article
Improving results with a CRM and IT strategy implementation
Increasing Retail Growth with a Cloud Infrastructure & CRM Online
By Lanrex on 16/08/16 4:30 PM
The Business Need
The Retail Council conducts industry events every year to highlight and advance its activities as an organisation. Each event involves considerable communication to ensure the participation of member organisations in those events. Previously all the management and organisation of events was done manually and at the end of each event, the data was not stored to enable general access or any guidelines for future events. Along with contact details, the activities performed to manage the events were not recorded. This resulted in every subsequent event being started from scratch.
In addition to the events, regular communication with member organisations, media agencies, suppliers and retailers also went unrecorded in a central database. With many communications being verbal, tracking and follow-up could not be consistent.
Business documents were stored in folders on hard drives without a centralised structure and without access controls. Excel spreadsheets were used to record details but this was done by individuals as required.
Key Challenges
Consistency was not guaranteed without-
- A centralised repository for storing all stakeholder details and data
- A formal record of communication and coordination activities
- Efficient reporting mechanisms for any and all campaigns.
Solution
The Retail Council CEO realised that even with a small team, a system needed to be in place to record details of all their contacts, the communications with their contacts and all event activities needed to be recorded for future reference.
Lanrex was selected to provide a solution.
All servers were decommissioned and all computing was moved to cloud infrastructure. Microsoft Office 365 was implemented for all email and office applications, together with SharePoint for all file sharing and management tasks.
Microsoft Dynamics CRM Online was also implemented to enable a centralised database for all contact information and all communications records. CRM Online also takes care of The Retail Council’s campaign management.
Migrate to Microsoft Office 365 for Email, File Sharing, Office applications
Key Outcomes
The key outcome for The Retail Council is increased efficiency and consistency in having a centralised database which contains all their contacts data.
CRM Online is not used as a sales tool by The Retail Council, due to the system’s flexibility they have been able to set up contacts by categories such as members, suppliers, non-members, general contacts and government agencies. All the categories have specific fields of data which suit the way The Retail Council needs to use a particular category. Anyone The Retail Council is in regular contact with is included in CRM Online. For The Retail Council, CRM is Contacts, Relationships, Memberships.
Lists can now be generated from the database; invitation letters to members can be created; all follow-up activity is recorded; and campaign tasks are also recorded.
A history is now available to all of The Retail Council staff online, in real time and able to be used simultaneously from anywhere.
- A centralised repository for storing all stakeholder data
- A formal record of communication and coordination activities
- Storage for all contracts and documents associated with its stakeholders, in a structured manner in SharePoint.
- Reports of the history of its communication and interactions with its stakeholders
- Efficient reporting capability in with CRM Online
- All campaign activities are stored for future reference.
The Retail Council produces a monthly economics brief for its members which is now much easier due to the centralised storage of information.
The Results
The Retail Council team no longer have any IT issues to deal with and no server hardware to manage.
Their systems are also accessible from any device in any location and any location.
Being able to key meeting notes directly to CRM Online after a meeting, even when remote from the office, meant any critical issues could be dealt with immediately and staff had immediate access to outcomes.
The Future
As with any organisation, a regular review of operations is always a positive step and The Retail Council is currently assessing its structure and its needs for the future.
While not having been with The Retail Council when Lanrex was engaged, Madeleine Lenzner, the Administration Manager is very happy with the service provided. She commented “All of our IT is done through Lanrex and includes ongoing maintenance, even our system users are set-up and maintained for us. It all just works for us.”
About The Retail Council
The Retail Council established in 2006 represents the largest of Australia’s retail companies including Bunnings and Harvey Norman. The mandate of The Retail Council is to achieve sustainable growth of retail in Australia for the benefit of the consumer, the industry and the economy.
The retail sector contributes approximately $134 billion or eight per cent of total economic activity through more than 127,000 retail operators nationwide, representing around six per cent of all businesses. With retail making up 43 per cent of total household consumption, it has an unmatched connection with Australian households.
The Retail Council representation and activities supports its members in advancing retail in Australia, fostering economic growth and supporting job creation.
Related Article
Lanrex helps Aussie engineering firm go all-cloud
Solving IT issues with a Managed Service Provider
By Lanrex on 9/08/16 9:00 AM
The Business Need
As their business expanded, DUAL’s IT Infrastructure also grew quickly. However the company didn’t have an overarching strategy to manage this growth.
As a result, their IT infrastructure became unstable and it wasn’t clear to management what work was required to rectify the issues.
DUAL received some input on the problems from their two internal IT people however management was doubtful about the validity of the advice provided.
“We came to the conclusion that managing our IT in-house no longer worked, so we needed to find a fully integrated outsourced IT solution,” Damien said. This became even more apparent when DUAL brought in a COO who reviewed the set up.
The COO looked at the IT infrastructure and realised it was a time bomb - an accident waiting to happen, Damien said, “it was like one flick of a switch and everything could blow up. I knew then that we needed to drastically change if we were to avoid a potential disaster”.
Key challenges
Without an effective IT infrastructure, there were on-going performance issues and complaints from DUAL’s staff. Problems included poor phone line quality, system freezes and kick outs, slow internet browsing and issues with documents.
There were also concerns around the overall stability of the network with frequent extended internet and phone outages. More worryingly, there were potential issues around business continuity and disaster recovery.
As problems mounted, DUAL management doubted that their own IT team had the knowledge and skills required to fix the problems. “As a CEO you need total confidence in your IT infrastructure - but I didn’t have that,” Damien explained. We needed to get clarity around the IT issues and build a robust solution.”
Solution
As a starting point, Lanrex carried out a review of DUAL’s IT systems. Findings from this review highlighted some serious risks and DUAL engaged Lanrex to resolve the critical issues immediately.
DUAL then made the decision to outsource their entire IT support system to
Lanrex under a managed services contract who subsequently:
- Upgraded voice and data network in Australia, implementing a fully redundant solution
- Virtualised and consolidated the server infrastructure (reduced number of physical servers from 14 to 3)
- Implemented a Cloud backup solution
- Upgraded the Microsoft and Citrix operating systems
DUAL also ran their own project to upgrade their business systems – the Core Insurance System.
Key outcomes
Since working with Lanrex the number of complaints from staff around IT issues has fallen significantly. DUAL’s IT Infrastructure has been stabilised and the company is confident that they have an effective Disaster Recovery plan in place.
DUAL saw the benefits of appointing Lanrex with their specialised IT team. “Lanrex provides clarity around technology issues and presents information based on facts. As a Managing Director, Jodie Korber is incredibly responsive and hands-on”, said Damien.
“We now have a full service operation for all of our seven offices across four countries. Lanrex provides a complete service solution for all the territories and has been able to respond well to a high growth business. We also have peace of mind around the ongoing upgrading of top quality software - we know everything is up-to-date and running efficiently.”
Damien continued, “Our IT function has gone from haphazard to well-planned out. It’s this structure and planning that gives me the greatest comfort. As a CEO, I don’t want to hear complaints and now I don’t – the systems are working so I don’t hear much - which is perfect!”
The results
The new system means that DUAL can easily measure response times. And when there is a complaint they now have the transparency to measure the effectiveness of Lanrex’s services.
“We can see immediately when there is a user complaint, and now we actually have the facts, the data and the structure to address these promptly,” added Damien.
The future
DUAL is about to roll out a global operating system to upgrade their business systems and will be working closely with Lanrex on this project.
Damien’s parting advice to other businesses who find them in a similar situation is: “In financial services your operating environment is as critical as your people. If your core skills are managing people and your business, then get a professional to help manage your IT – don’t try to do it on your own.”
Background
DUAL is a specialist underwriting agency committed to delivering insurance solutions to businesses in the corporate and mid-market sectors. DUAL Australia was established in March 2004 and has experienced rapid growth with offices in Sydney, Perth, Melbourne, Brisbane, New Zealand, Singapore and Hong Kong.
Related Article
CIOs urged to lead digital transformation
By Lanrex on 2/08/16 10:02 AM
Wherever you look, organisations are being told to digitally transform or be digitally disrupted, but transformation is never easy and a study by the Harvard Business Review has identified leading the transformation as a new and vital role for the CIO. The conclusions are published in the HBR study Driving Digital Transformation: New Skills for Leaders,New Role for the CIO. They are based on a survey of 436 business leaders in organisations with more than 500 employees, undertaken by Harvard Business Review Analytic Services.
Transformation the new and vital role for the CIO
HBR concluded that, in general, CEOs understand the importance of digital transformation but most have not yet built or effectively communicated a digital vision and strategy to the rest of the organisation, and this lack of leadership is holding them back. “While self-starting individuals are finding a way to gain the knowledge and skills they need to do their jobs, company leaders must do more to ensure that the entire organisation moves together into the digital age,” it says.
 The report argues that CIOs have a central role to play and that business leaders want their help to better understand digital trends. “This starts with being the voice of digital innovation—evangelising what’s possible and what business leaders’ peers in other organisations are doing. It means partnering—closely—with business colleagues to develop the right digital solutions.”
The report argues that CIOs have a central role to play and that business leaders want their help to better understand digital trends. “This starts with being the voice of digital innovation—evangelising what’s possible and what business leaders’ peers in other organisations are doing. It means partnering—closely—with business colleagues to develop the right digital solutions.”
Whole team approach required
However it says that CIOs need “a whole team” to support them. “Many IT organisations are not well-equipped to fill a teaching/coaching role.
They need to improve the way they communicate, as well as carve out the time and create the forums for digital learning.” And, it adds: “While the human resources department would seem anatural partner in this, HR leaders were rated the weakest of all the function heads when it comes to their own digital acumen.”
CIO’s need to drive learning forums for employees across the organisation
The study identified one of the biggest barriers to the spread of IT knowledge throughout an organisation as being the lack of an appropriate forum, and 34 percent of respondents said their IT leaders were too busy. “A key part of the CIO’s focus on digital leadership should include a drive to create appropriate learning forums for employees across the organisation,” it concluded.
Analytics rates as extremely important
While the focus on digital disruption has been very much on mobile, social and cloud, HBR suggests that CIOs should start their journey of digital evangelism with data. “When it comes to gaps in digital acumen, it’s all about the data,” it concluded. “Close to three-quarters [of respondents] rated analytics as extremely important to their area of the business with another 17 percent rating it as important. But only a fifth rated their own knowledge and skills in this area highly.”
The report concluded that the expectations placed on CIOs by organisations are changing and CIOs had “better prepare.” Nearly half of respondents said they would like to learn more about digital trends from their CIO, but close to two-fifths said their CIO did not seek to educate and empower line-of-business leaders around digital, and over a third said IT did not provide useful knowledge about technology or understand which digital knowledge was important to specific functions or lines of business.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
How much does downtime cost your business?
By Lanrex on 2/08/16 9:30 AM
The recovery process represents the amount of time it takes to recovery data either locally or from the cloud due to data loss (data loss could be the result of a virus, employee error, or some other type of system disruption).
CRITICAL SYSTEMS DATA: XGB
Critical system data is the amount of data lost in a scenario resulting in employee downtime.

TIME BETWEEN BACKUPS: X DAYS X HOURS X MINUTES
The interval at which your backups take place. This is used to check the Recovery Point Objective.
RECOVERY PROCESS START: X DAYS X HOURS X MINUTES
The time it takes initiate a file or system recovery. This involves alerting a Managed Services Provider and configuring the recovery point.
ESTIMATE DOWNTIME: X DAYS X HOURS X MINUTES
The amount of downtime is determined by adding the RECOVERY PROCESS START TIME to the amount of time it takes to fully recover the data lost. The speed at which the lost data is recovered is determined by whether it's being restored locally or from the cloud.
Local Speed: The default local restore speed is based on a typical gigabit connection.
Cloud: The default cloud restore speed is based on the average internet speed of businesses in Australia.
Since local recovery is faster than cloud recovery, local recovery will result in less downtime.
Example:
RECOVERY PROCESS START TIME +
LOCAL RECOVERY TIME = DOWNTIME
1HR + (100GB/LOCAL SPEED) = DOWNTIME
1HR + (819200Mb / 700Mbps*) = DOWNTIME
1HR + 1170s = DOWNTIME
DOWNTIME = 1HR 20MIN
Downtime Costs
The cost of downtime is first determined by the total cost of each employees' time. This includes the employee's wage, overhead costs (subscription costs, benefits, etc.), and revenue lost as a result of the employees not working (sales opportunity loss). It could also include an ecommerce site that is down and no longer generating sales as a result of system downtime.
Employees Affected: 10
Average Wage: $25/Hr
Overhead Costs: $100/Hr
Revenue Lost: $250/Hr Total
Cost: $600/Hr
Example:
(EMPLOYEES * WAGE) + (OVERHEAD + LOST REV) = COST OF DOWNTIME
(10 * 25/HR) + (100/HR + 250/HR) = COST OF DOWNTIME
(250/HR) + (350/HR) = COST OF DOWNTIME
COST OF DOWNTIME = $600/HR Total Cost to Business
Total Cost to Business
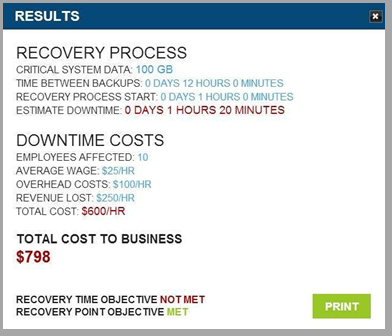
The total cost to the businesses is determined by multiplying the amount of downtime by the cost of downtime.
DOWNTIME * COST OF DOWNTIME = TOTAL COST TO BUSINESS
1 HR 20 MIN * 600/HR = TOTAL COST TO BUSINESS
1.33 * 600 = TOTAL COST TO BUSINESS
TOTAL COST TO BUSINESS = $798
Related Article:
Put your data on a platform
By Lanrex on 29/07/16 10:55 AM

There’s never a dull moment in IT. Never a day seems to go by when a new concept, accompanied by the inevitable TLA (three letter acronym) doesn’t pop up. One that has been around for at least a couple of years and is rising rapidly in the awareness rankings thanks the popularity of big data and data analytics, is ‘data management platform’.
Is it just a fancy name for a database? No it isn’t. Is it another name for a data warehouse? No it isn’t. And unlike both of those concepts, it is not application neutral: it’s a concept primarily specific to marketing and related functions.
DMP = software that sucks up, sorts and houses information
In a Gartner blog, What Does a Data Management Platform Do, Anyway?, research director, Martin Kihn, offers what he says is one of the best definitions he’s read of a DMP, attributing it to “a company called [x+1], one of the pioneering DMPs now owned by (and called) Rocket Fuel.” Here it is.
“... provides the requisite, yet somewhat unnoticed, function of data collection, translation, classification, indexing and storage. It’s the ‘plumbing’ part of data-driven marketing online.”
Quite frankly, that’s not very helpful. A much better one come comes from news site Digiday, in a rather irreverently titled article WTF is a data management platform? “It’s a piece of software that sucks up, sorts and houses information, and spits it out in a way that’s useful for marketers, publishers and other businesses.” Now that makes much more sense!
Unified Data!
Here’s another one that’s quite useful. “A data management platform, also called a unified data management platform (UDMP) is a centralised computing system for collecting, integrating and managing large sets of structured and unstructured data from disparate sources.” Note that this one is not marketing-specific.
According to Forrester Research, DMPs are now must -haves for marketers, advertisers and the like. In the Forrester Wave: Data Management Platforms, Q4 2015, it says: “As programmatic ad buying and selling become the norm, marketers and publishers are learning that harnessing their first-party data; developing single and consistent identities for their consumers across devices and systems, like email and site optimisation; and gaining access to second-party data are mission-critical and require partnership with a data management platform (DMP).”
Sixty two percent of online adults in the US are now always addressable
As Forrester explains, driving both the need for, and the usefulness of DMPs is the amount of data customers generate about themselves and their activities.
“Sixty two percent of online adults in the US are now always addressable,” Forrester claims. “They use multiple devices from multiple locations. In order to deliver meaningful and brand-consistent messages efficiently to these consumers, marketers must develop the ability to recognise individuals consistently and persistently wherever they may be, on whatever device they choose.”
Effectively used a good DMP will help marketers get to the mythical ‘segment of one’, according to Forrester. In short, DMP looks like being a pretty powerful TLA.
Can your organisation transcend data gravity?
By Lanrex on 18/07/16 2:27 PM

It’s quite a challenge. Could your organisation “analyse all relevant data and deliver actionable information” based upon it? If you could, IDC reckons that your organisation would be one of a select number enjoying its share of a total of $US65 billion in productivity benefits over your less analytically oriented peers by 2020. And that’s not a global total, it’s just Asia Pacific.
Heaven knows how IDC came with that figure. If you come down from the stratospheric heights of regional statistics to the challenges facing individual organisations it’s hard enough to quantify these predictions.
How do you determine what data is relevant and what isn’t? How do you translate analysis into action plans? How do you quantify the productivity benefits thus gained?
In short, it makes for a great headline, but it’s not very helpful, except to engender a sense of urgency about developing a better data capture regime and better data analytics capabilities, which is no bad thing. However rubbery IDC’s figures might be, there is no denying the general thrust of the argument.
According to IDC the adoption of “big data and analytics” will be accelerated by the business disruption resulting from digital transformation. (It’s generally accepted that ‘big data’ and ‘data analytics’ are alternative terms for the same concept, which makes IDC’s terminology somewhat confusing).
“With the digitalisation of everything, the ability to make smarter, quicker and more automated decisions and actions will increasingly become a competitive necessity,” IDC argues. “At the same time, barriers to entry will be lower because technology options are increasingly abundant with purpose-built tools that are designed for specific workload or use case, flexible pricing and deployment.”
That’s the good news.
The bad news is that the ‘accelerated’ adoption of big data and analytics might not produce the desired, or expected, increase in the velocity of business. These benefits, says IDC, may be counteracted by ‘data gravity’. IDC explains it thus. “The bigger the data set becomes, the greater the overhead the organisation takes on in its transport, storage, archiving, analysis and search. With small amounts of data, this overhead is not material. For larger amounts of data, the implications of data gravity become much more material. The bigger the volume, the greater the gravity and the harder it becomes to move the data.”
According to IDC’s senior market analyst for software in Asia Pacific, Chris Zang, the drive to overcome data gravity will see increased adoption of cloud-based data analytics along with SaaS-based CRM, and ERP systems.
IDC offers a few statistics on where it thinks things are going in the data analytics space in Asia Pacific. It reckons that, by 2020, 75 percent of databases (relational and non-relational) will be based on memory-optimised technology and that, by 2020, distributed micro analytics and data manipulation will be part of 80 percent of data analytics deployments.
The most staggering prediction is this one: “By 2020, data monetisation efforts will result in enterprises [that are] pursuing digital transformation initiatives increasing the marketplace's consumption of their own data by a hundred-fold or more.”
A hundred fold increase! Now that’s big data.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
Closing the virtuous circle of data
By Lanrex on 5/07/16 2:00 PM

Back in 1934 the poet TS Eliot in words for a musical play ‘The Rock’: “All our knowledge brings us nearer to our ignorance … Where is the wisdom we have lost in knowledge? Where is the knowledge we have lost in information?”
Businesses struggle to extract data insights and put it to work
What’s that got to do with data in the age of the computer? Take this quote from a report by the Economist Intelligence Unit (IEU) The Virtuous Circle Of Data: “During the last five years, companies have invested significantly in gathering and analysing vast and increasingly complex data. Yet many still struggle to extract insights and put those insights to work for their business. Part of the trouble is the speed and scale of information overload for executives today, and the rapid pace at which they must make decisions. The ability to rely on gut feel, which used to be their greatest business asset, is now greatly diminished.”
In other words, CEOs now have vast amounts of data, but the value of their wisdom and knowledge is greatly diminished, and they struggle to extract the same from the mountains of data that technology now delivers. So what’s the solution?
Harnessing those masses of data and extracting value from them is what’s needed and according to the EIU, executives cannot harness that asset alone. “They are quickly finding that they must enlist the entirety of their workforces—and that doing so is fast becoming the central challenge for businesses that aspire to be truly data-driven.”
A data-driven business needs leadership to evolve the right culture
It claims they are not going about this the right way. After interviewing a number of experts for its report the EIU concludes: “Becoming a data-driven business generally happens in three stages [but] as is often the case, what should be done first—establish a strong leadership focus on cultivating a data-centric culture—almost invariably happens last.”
Initially, the report says, “Organisations tend to focus primarily on technology and tools. Then they look to acquire the right talent and expertise.” Real success, however, rests on tackling the most critical and difficult-to-execute stage: “Evolving the right corporate culture—one in which employees embrace data and apply them day-to-day.”
But even with that leadership the journey is not easy.
Employee engagement and ease of data access are the key
“An even greater challenge—and one vital to overcome—arises in motivating and engaging employees across all levels of the organisation to use data.”
And how do they do this? “The best-performing and most data-centric companies understand the criticality of employee engagement,” the report says. “To drive more of it, they are making data universally available and easy to use; they are also linking data to day-to-day business goals and tasks. In addition, they are investing in employees by putting in place training and advancement programmes focused on data analytics, creating compensation incentives and competitive motivators, and even making data analytics fun and social.”
The report pulls no punches on the importance of achieving these goals: “The importance of data as a corporate asset cannot be overstated. Companies are increasingly closing the technology and expertise gaps, and many of them are deeply engrossed in the third stage—the cultural stage—of transforming themselves into truly data-driven businesses.”
The report closes with a comment from one of the senior executives interviewed: “The key to future success is to build an organisation that can innovate with data, … to disperse the data, democratise the tools and unleash the creativity of individual employees.”
So instead of knowledge and wisdom being lost in a mass of data, data will become the wellspring of organisational wisdom.
Unstructured Data: The hidden hero for Machine Learning
By Lanrex on 27/06/16 1:10 PM
What are the benefits of unstructured data?
By now, you’re probably well-aware that big data has been the talk of the town — and for good reason. Everywhere you turn, people just can’t seem to stop talking about big data, data analytics, or data analysis — the science and technology of extracting meaningful insights and intelligence from vast repositories of data.
But there are two kinds of Big Data: Structured and Unstructured
Structured data has been around since the dawn of IT. It’s the data that’s neatly stored in files where each file has many records and each record has many fields. Each field contains exactly the same kind of data and references the same kind of entity: the name of a customer, the date of the customer’s last purchase, the value of that purchase, for example.
But there’s another kind of data that’s becoming a big part of big data: unstructured data. IDC estimates that 60 to 80 percent of new data is unstructured. And if you want to get a sense of just how big unstructured data is, try doing a Google news search on “unstructured data” and sorting the results by date: we found 100 items in the ten days from 4 to 14 January!
Of the many articles in that short period looking at unstructured data, this one describes unstructured data as “every document, email, presentation file, or customer survey; every piece of data that doesn’t have a specific ‘home’ or purpose that is easy to articulate.”
More importantly, it adds, “While it’s tempting to dismiss this information as mere runoff, the inevitable over-wash of structured data, there is massive potential waiting to be tapped.”
In the healthcare industry alone, according to one report, there is an explosive growth of unstructured clinical data — and healthcare firms are deploying solutions to use this data for many functions, such as to retrieve patient's history, to reduce the readmission of the patients for particular diseases, and to generate reminders for the physicians.
There is also massive potential for misinterpretation, the article warns.
“Unstructured data is, by nature, outside the existing categorisation system used by your business. Tapping unstructured data, therefore, comes with inherent risk since the inherent value of any piece of information is subject to interpretation. If your company assigns high-value to a skewed survey, for example, any insight based on this data may be flawed, as well, and following this insight could be costly.”
But there are other risks associated with lack of understanding of unstructured data. In this article, Perry Dickau, director of product management at storage technology vendor, DataGravity, says: “As companies become more aware of the vast amounts of information they're storing, they're simultaneously recognising how little they know about what that information means and how ill-equipped they are to manage it effectively.”
What he’s concerned about is not that companies don’t know what they have and aren’t making full use of it. Rather, its the fact that they don’t realise the security risks they’re facing.
However, ignorance in and of itself is a business risk. As this article points out, “Organisations that realise value from their data assets faster through advanced analytics will quickly surpass their competition.”
The Benefits of Unstructured Data
The solution, according to the same article, is machine learning. “Unlike traditional analysis, machine learning thrives on growing datasets. The more data fed into the system, the more it can learn and apply the results to higher quality insights.”
About Lanrex
Our team is highly experienced in helping businesses get the most out of technology, from consulting, cloud infrastructure, and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Let Lanrex make your technology is your business advantage.
Marketeers discovering the power of IoT
By Lanrex on 21/06/16 12:37 PM
Marketing is an intensely competitive business and by nature marketeers are highly competitive individuals, always looking for new ways to gain an edge on the competition, to get greater ‘mindshare’ for their brand and products.
So they’ve always been quick to exploit new technologies for any possible edge. IT has long been a high priority, from customer relationship management systems to web advertising and smartphone apps. Now the latest IT development getting attention from marketeers is the Internet of Things (IoT). It’s particularly attractive because it enables marketeers to establish an ongoing dialogue with customers.
A recent article in Forbes Magazine How The Internet Of Things Will Transform High-Tech Marketingproclaimed: “It is estimated that by the year 2020, the Internet of Things (IoT) will consist of approximately 50 billion objects, each with its own embedded computing system, and able to interact with the existing Internet infrastructure. … This has some far-reaching implications for businesses and the marketing strategies which they should adopt in order to stay abreast of the powerful trends now underway.”
In the UK there is even a marketing consultancy, SharpEnd dedicated to exploiting IoT for marketing purposes. It is looking at connecting vodka bottles to “better serve its customers by leveraging location data, which could provide more tailored and relevant information or services.”
According to Marketing Magazine UK cosmetic company L’Oreal is exploring the idea of smart make-up that could allow it to give connectivity to dumb objects like lipstick or mascara, giving it a new way to track customers.
A survey of 500 IT and marketing professionals in large and mid-size companies, designed to assess their use of big data and IoT in support of digital marketing, reported: “Forty percent are using machine data (Internet of Things) to support digital marketing, but are in the beginning stages of doing this.
Nearly 20 percent are being very aggressive this way, and another quarter or so (27 percent) plan to begin an IoT project for digital marketing soon.”
It went on to say: “Top uses for IoT in digital marketing: better understanding of customer preferences (28 percent), to power campaigns and promotions (24 percent), to drive customer-facing web and mobile apps (14 percent). Seventy percent say they’ve been successful in meeting or exceeding their IoT-based digital marketing goals. More than half (53 percent) say it’s likely they’ll expand IoT-based digital marketing programs.
“Forty percent say cost is the biggest consideration when implementing big data and IoT-based digital marketing programs. Twenty one percent say lack of executive support is the biggest challenge (“They don’t yet see the value.”). Twenty percent say technical skills are the chief impediment — they don’t have the skills in-house
Tata Consultancy Services’ recently released a reportInternet of Things: The Complete Reimaginative Force in which it said: “The biggest product and process improvements [from IoT] reported by companies were more customised offerings and tailored marketing campaigns, faster product improvements, and more effective customer service (in part, by being able to identify product problems before customers knew about them).”
Things are moving very rapidly in the world of Internet-connected things. Expect to see many more creative applications in support or marketing initiatives in 2016.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
4 Financial Benefits of Cloud Infrastructure
By Lanrex on 16/06/16 10:30 AM
Cloud infrastructure, also known as Infrastructure as a Service (IaaS), offers businesses remote access to IT resources such as servers, CPUs, storage devices and other hardware and networking equipment.
IaaS, which can be used to run a single application or your entire organisation’s IT infrastructure, provides a cost-effective way for you to scale your operations. This is why using cloud infrastructure is widely considered a better alternative to purchasing your own infrastructure.
In this blog post, we will explore the top 4 financial benefits of cloud infrastructure:

1. No Up-Front Capital Expense
When purchasing your own hardware infrastructure, you have to estimate how much capacity you will need over the next 3 - 7 years, and most of the time you will have to pay for it all at once. This ties up a large sum of money that you could be spending on other things. Not only is it difficult to accurately estimate your usage over such a long period of time, it is not an effective use of your money.
Since global public cloud providers invest and operate at such high scale, they pay a lot less per unit than anybody else. They run their business on a high volume, low margin basis which allows them to pass signifcant savings along to you.
2. Reduced Operating Costs with Cloud Computing
Quite often, the costs of maintaining your own infrastructure are overlooked or underestimated. These costs include:
-
Power
-
Cooling
-
Data centre rental (if offsite)
-
Hardware maintenance contracts
-
Procurement costs and delays
These operating costs are included in the rental of your cloud infrastructure.
3. Pay Only for What You Use
Infrastructure from cloud technology providers can be made available in minutes and you only pay for what you use. This model allows your investment on IT to align much closer to the financial performance of your business over time.
Academics use a term called option value for which a premium is paid for flexibility. In the unlikely event that a cloud alternative may be more expensive than purchasing infrastructure for the same duration, this would be understandable, as there is no implied commitment beyond the duration.
4. Minimise Employee / Customer Dissatisfaction
Your organisation has a greater dependency on IT infrastructure than ever before. It supports your internal customers (employees) and your external customers (through your web presence). Patience for infrastructure availability is growing thin. This makes capacity planning and management very difficult. If you purchase too much infrastructure, you are wasting money. If you don't purchase enough infrastructure, your employees and customers become frustrated and dissatisfied. This is an additional cost to your business.
Overall
You should consider the key drivers and goals for your business since migrating to cloud technology isn't an all or none proposition. You can run your line of business applications on premise, while hosting others in the cloud, avoiding upfront server costs and benefiting from fast, easy scalability and simplified management.
Learn more about Cloud Computing with our easy to read 5 page Cloud 101 Guide!
You might also like this related article, Get ready for the cloud, and avoid a storm of problems
The lowdown on sales force automation software
By Lanrex on 15/06/16 12:27 PM

Sales force automation software is almost essential for any serious sales organisation. It acts as the central repository for account, lead and contact records and enables sales reps to automate key activities such as dialing leads, sending emails and logging data.
Research firm Aberdeen Group found that the leading adopters of sales force automation increased the size of deals by an average of 27 percent, decreased the sales cycle by 16 percent, cut the time-to-quota by 15 percent and cut sales administrative time by 15 percent.
But implementing an effective sales force automation system can be challenging – each organisation’s requirements are different. A survey by another research firm, Gartner, found the average time to deploy to be in excess of six months. “Implementation methods vary, ranging from self-implementation to global systems integrator-led efforts for comprehensive global, multibusiness unit implementations,” Gartner reported.
The reason for this, according to Gartner is that requirements are unique to each organisation and are a function of the maturity and culture of the organisation in its use of technology, the sophistication of sales practices and the anticipated RoI.
“Companies that have low to moderate sales process complexity and that do not need to integrate to back-end systems can self-implement,” Gartner said. However: “As a general rule of thumb, regardless of your sales process complexity, Gartner recommends that you employ an SI if you are new to the vendor's technology,” it said.
A third research firm, Forrester, says the sales force automation market is undergoing significant change with increasing emphasis on mobile sales capability, integration with other software products, real-time actionable insight and usability approaching that of consumer-grade applications.
This integration, for example, could be with mapping software to enable the territories of individual sales reps to be easily defined and managed.
Like many other kinds of business software, sales force automation is increasingly moving from on-premises to cloud based delivery. Gartner says it has spoken with many clients that are replacing their on-premises systems with SaaS-based systems, and that smartphones and tablets, are fast becoming the data-entry method of choice among its clients. By 2017, Gartner predicts that 65 percent of sales organisations will be using smartphones to drive user adoption and improve data quality for their sales force automation systems.
Sixty eight percent of respondents to a Gartner survey use tablets for both account management and sales activity tracking, and 58 percent use tablets for opportunity management.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
IT trends in human resources
By Lanrex on 6/06/16 12:18 PM
Information technology is transforming every aspect of enterprise operations and human resources is no exception. Earlier this year KPMG published its HR Transformation Survey. Eighty eight percent of respondents said they would spend the same or more on technology in 2015 than in 2014. “Organisations are replacing their core human resource management systems (HRMS) more frequently than ever before (every three to five years versus historically every five to seven years),” KPMG said.

KPMG expressed surprise that many organisations were still using paper-based systems for performance management tasks. “Seventy four percent of organisations that are currently using technology for their performance management believe this technology is effective. Yet 28 percent of these organisations still rely on paper for some performance management tasks,” it said.
It identified a number of trends common to organisations that had successfully transformed their HR function. They have introduced new types of collaboration tools for the delivery of HR services, implemented a new HR portal, re-engineered key HR processes, implemented a new core HR system and built or further invested in an HR analytics function.”
KPMG concluded: “HR is constantly pulled between serving as project leader and operator. No doubt both roles are important, but higher performing HR organisations have managed to find the appropriate balance between the two, and maximised the output from each role.”
The survey is an annual one that has been published for 18 years, it was formerly the Towers Watson HR Service Delivery and Technology Survey. This year 798 organisations across 37 countries participated, half of them global organisations.
For HR departments looking to upgrade their technology BizJournal recently offered five technologies that organisations should consider.
These five technologies were: electronic onboarding; online benefits enrolment; performance management; learning management; time and attendance.
Human Capital Media Advisory Group, the research arm of Talent Management magazine recently surveyed 127 HR professionals from companies of various sizes and industries.
It reported: “HR practitioners in the survey said they have several different types of technologies at their disposal. With a new and changing market, HR professionals must decide which technologies are worthy of investment. For example, according to the survey, companies use HR software for workforce management, recruiting, learning management, performance management, analytics, compensation management, wellness, succession planning, collaboration, onboarding, workforce planning, talent management and mobile.”
The survey showed that 58 percent of HR respondents do not have plans to invest in wellness software technology, though 14 percent said they planned to purchase and 27 percent said they already used it.
The second most popular technology was succession planning. “While more than half of respondents said they do not currently have and have no future plans to invest in succession planning software, about 20 percent already do and 23 percent plan to do so in the future.”
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
Flexible working: myth busted
By Lanrex on 26/05/16 10:54 AM

Despite all the talk about enterprise mobility, teleworking and technology-enabled location independence, it seems the Australian workforce is, to a large extent, chained to its desks.
Those are the conclusions of a survey undertaken by Galaxy Research for Citrix. Its conclusion: “Flexible working is still a privilege enjoyed by a lucky few, and not the masses.” Australian businesses, it says, are resisting the move towards flexible working arrangements, and: “This out-dated perspective of work as a place, not an activity, is potentially costing the Australian economy billions of dollars every year.”
The report estimates that if all the people who commute but would prefer to work from home could do so they would, collectively, save up to $108.7 million per week in travel costs, and cut their commuting time by 8.2 million hours a week.
The report also cites another compelling statistic associated with the concept of ‘presenteeism’, defined by the Harvard Business Review as “workers being at the office despite not fully functioning due to illness and cutting productivity considerably.”
According to the report: “A July 2011 study by Medibank estimated the total cost of presenteeism to the Australian economy to be $34.1 billion in 2009/10 with an average of 6.5 working days lost per employee annually. The researchers believed presenteeism was a longer term issue and would continue to inhibit Australia’s economic performance.”
Not surprisingly, flexible working is largely a privilege bestowed by companies at the top end of town. “While many leading enterprises in Australia boast of companywide flexible working practices … this flexibility has not filtered down to Australia’s small-medium businesses which make up the vast majority of Australia’s economy,” the survey found.
It notes that the technology to effectively (and importantly, securely) support flexible working is now widely available “Online collaboration tools, online meetings and secure file sharing technology help employees remain productive, regardless of location. Access to broadband and WiFi mean connectivity is rarely an issue and the increasing trend for business to allow BYOD, or even directly providing smartphones, laptops and tablets to employees, provides a broad range of mobile work options.”
However, it offers no real solutions as to how flexible working can be boosted. It simply urges business of all sizes to: “Seize the potential flexible working provides for both productivity gains and employee satisfaction and implement the technology and policies to allow flexible working to become ubiquitous across all Australian business, regardless of size.”
Nor does the report bring up the fact that the Federal Government seems to have abandoned its promotion of teleworking.
The Government organised a National Telework Week in November 2013 with then communications minister, Malcolm Turnbull, championing its benefits. The government even established a web site dedicated to telework (www.telework.gov.au). It has now been consigned to the digital archives.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready?
To host or to house: the PBX buyer’s dilemma
By Lanrex on 25/05/16 8:51 AM
 Do a Google search on ‘hosted vs premises PBX’ and you’ll find no end of advice favouring one or the other, and numerous comparisons that represent a fairly balanced view with roughly the same number of pros and cons associated with each.
Do a Google search on ‘hosted vs premises PBX’ and you’ll find no end of advice favouring one or the other, and numerous comparisons that represent a fairly balanced view with roughly the same number of pros and cons associated with each.
Some of the arguments often cited against premises-based PBX are rather dubious. Generally they are along the lines that the purchaser has to wear the upfront cost and is responsible for keeping the system up to date and for ongoing maintenance costs. In contrast, a hosted system is charged on a monthly fee and the provider is responsible for keeping the software up to date.
However, it’s possible to get a PBX on a rental plan bundled with call costs and even maintenance, so the argument then shifts to the ongoing operating costs of the different options and other features.
Features and functions are really what it’s all about. If you go for a hosted option you’re pretty much limited to the features that particular hosted IP telephony offers, although you can shop around for the one with the package of features best suited to your needs.
With hosted telephony the software supporting the service is dedicated to each customer, it just runs in a data centre rather than on customer’s premises and can in fact be pretty much the same software, in which case the argument of hosted v premises shifts from features to the differences that the different locations introduce.
It’s also important to make the distinction between hosted PBX or hosted IP telephony and cloud-based IP PBX/IP telephony.
In cloud IP telephony the one instance of the software supports the functionality of each customer organisation’s PBX. In hosted, each customer organisation gets a dedicated instance of the software.To make life even more complicated, there are hybrid systems that split the functionality between on-premises hardware and a cloud or hosted environment.
When it comes to the crunch the decision often has little to do with features, functions or cost. Unless a comparison of the hosted versus premises options reveals some huge disparity or the availability/lack of particular features deemed to be essential, it’s often a philosophical decision. As one comparsion site observes: “The most critical [consideration] from the point of view of implementation and future growth is whether to have a PBX system physically on your organisation’s premises and under your control or whether to have a PBX hosted externally by a service provider. For a few organisations this decision will stem from a fundamental philosophy of the business – outsourcing all functions that are not directly germane to the core business.” (their emphasis)
Later on it suggests control is the “tricky issue” that is “at the heart of a decision between a hosted or on-premise solution.” It explains: “Some organisations prefer to keep control as much as possible internally, even at the risk of added cost, work and complexity,” while at the same time: "Other organisations want to outsource as much as possible to keep internal focus on core business – even if that decision ends up costing them more.”
The bottom line: if you’ve been charged with upgrading/replacing your ageing PBX, before you devote time to researching the pros, cons and costs of the hosted and premises options, make sure your organisation’s leaders are not philosophically wedded to one option or the other.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
Beware the digital vortex
By Lanrex on 12/05/16 9:24 AM

The Digital Business Transformation Center (DBT Center), after surveying 941 business leaders around the world in 12 industries, concludes: “Digital disruption is not seen as worthy of board-level attention in about 45 percent of companies. In addition, 43 percent of companies either do not acknowledge the risk of digital disruption, or have not addressed it sufficiently. Nearly a third are taking a ‘wait and see’ approach in hopes of emulating successful competitors. Only 25 percent describe their approach to digital disruption as proactive—willing to disrupt themselves in order to compete.”
This, DBT Center argues, is not good enough, and in its reportDigital Vortex: How Digital Disruption Is Redefining Industries it uses the metaphor of the vortex to advance its argument.
A vortex pulls objects relentlessly toward its centre where their velocity increases exponentially. Vortices are highly chaotic. An object can be on the periphery of a vortex one moment and then drawn directly into the centre the next. Objects do not travel a uniform or predictable path from the outside to the centre. Objects within a vortex may break apart and recombine as they collide with one another and converge toward the centre.
For businesses this means: “Physical and digital sources are separated by the force of the vortex, creating ‘components’ that can be readily combined to create new disruptions, and blurring the lines between industries. … The centre of the digital vortex symbolises a ‘new normal’ characterised by rapid and constant change as industries become increasingly digital.” How?
DBT Center uses uses the metaphor of digital transformation being a vortex to get its argument across, to represent the level of disruption to different industries by placing them on the periphery or towards the centre of the vortex. It says: “Executives in industries on the outer edges of the digital vortex today, such as utilities, may be tempted to take comfort in the idea that their sector is among those judged to be least prone to disruption.” However, that may be cold comfort, when: “An object can be on the periphery of a vortex one moment, and then drawn directly into the centre the next.”
In short whatever spin you put on it digital disruption is inevitable, accelerating, and unpredictable.
Better to jump in now than be sucked in when you least expect to be.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
In search of digital business
By Lanrex on 10/05/16 11:47 AM
In a survey taken by Gartner in October of this year, of more than 2,900 CIO’s on the topics of platform thinking and digital transformation, their findings were that “More than half of Australian and New Zealand CIOs are leaders of digital transformation in their enterprise.” With that being said, this has surely got to be good news for most CIOs.
As with good news there tends to be the opposite and in this instance the bad news is that, progress of digital business within Australia and New Zealand (ANZ) is considerably slower than that of the global average. Gartner came to the above conclusion after surveying over 2,900 CIOs in 84 countries, 175 of the surveyed CIO’s came from Australia and New Zealand. 52 percent of ANZ CIOs were found to be leaders of digital transformation, and more than 40 percent also claimed to be leaders in innovation. These are significantly higher than the global averages of 40 percent for digital transformation and 30 percent for innovation.
According to Gartner’s vice president Graham Waller, “CIOs are being given the opportunity to lead digital transformation, but they must adapt their leadership style to exploit platform effects in leadership, building a network of digital leadership inside and outside the enterprise.” Waller is expressing the idea that in today’s business world, nothing is done without the use of technology and in order to digitally transform the business platform, CIO’s need to find a suitable way to integrate various technologies into the business mix and create a competitive platform that will ‘transform’ the way people do business.
But how exactly were the terms ‘digital’ and ‘non-digital’ differentiated in the survey? Gartner’s IT Glossary defines digital business as “the creation of new business designs by blurring the digital and physical worlds.” Whereas Gartner’s definition of digitalisation is “The use of digital technologies to change a business model and provide new revenue and value-producing opportunities; it is the process of moving to a digital business.” If placed together these definitions create a powerful concept; that in order to create a digital platform the pierces the vail of the everyday market place, you need to be prepared to lead this digital revolution.
The survey results show that opportunities to lead the digital revolution are being given to CIOs, however they are not adapting their style of leadership to suit the transformation. In fact only 9 percent of CIOs have adapted their leadership style to build and exploit digitalisation both inside and outside the organisation.
CIOs are predicting a rise in digital processes within the ANZ public sector from 38 to 79 percent (from 42 percent to 77 percent globally), and within the next five years CIOs in ANZ expects digital revenue to grow from 14 percent to 32, however globally speaking the revenues are expected to grow from 16 to 37.
With Mr. Waller stating that “digital business is a reality now, and it is expected to be a significant source of competitive advantage.” It is imperative that perhaps now is the time for a reimagined business platform that integrates more leadership in order to exploit the advantages and create a “power of platform” to information and technology and apply those platform dynamics to “create value in all aspects of the business.”
Managing Director of Lanrex an Outsourced IT Company Jodie Korber has said ‘The likely challenge will be in determining exactly what is needed to create wealth and revenue and how to push the boundaries and further engage with the marketplace, creating awareness of this new digital transformation. Digital transformation is essential and inevitable. In reality the idea that if organisations do not digitally transform their business platform there is a high chance that they are doomed to fail.’
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
CFO becomes 'chief data corralling officer'
By Lanrex on 27/04/16 9:58 AM

As enterprises struggle to cope with an increasing deluge of data, chief financial officers are taking on a role of consolidating data to provide a ‘single source of truth’ about the enterprise, which is an important contributor to success.
That conclusion comes from a global survey of 435 CFOs undertaken by Adaptive Insights, a company providing corporate performance management software. “Today’s finance leaders are facing an increasing responsibility in their organisations,” the report of the survey says. “They are pushed not only for a historical view of finance and operational data, but a forward-looking view that enables them to make informed, strategic decisions.”
This, it says “brings both opportunity and challenge to the office of the finance, as CFOs navigate the increase in and veracity of data from multiple sources and break down data silos.”
The report says that having a single source of data carries significant benefits. “The highest performing organisations rely on data to drive decisions. … Whether big or small, public or private, or for-profit or non-profit, today’s CFOs across organisations of all sizes and across all industries are requiring a single source of truth.
“[It] stops the debate over whose numbers are correct and refocuses the discussion on insights and action. Achieving a single source enables a consistent view of data across the organisation in real time, eliminates confusion among competing data sets, and encourages velocity of decision-making.”
The majority of CFOs surveyed said that keeping data siloed (69 percent) and having inaccurate data for forecasting and planning (40 percent) were among the top financial mistakes most companies make.
However achieving a single source of data is a growing challenge.
Not only are data volumes increasing but the type of data CFOs must manage is also increasing. “Non-financial data is playing a greater role for CFOs, as they are now managing data from multiple sources across the organisation,” the report says. “This requires collaboration and access to data at a level not previously experienced.”
Forty one percent of CFOs responding to the survey said they manage data from three to five source systems; another 30 percent manage data from five or more source systems.
"It is clear that CFOs are navigating through unchartered waters,” the report concludes. “Tasked with managing a deluge of data from multiple sources across the organisation, there is an expectation of CFOs and their teams that they can aggregate, accurately process, and interpret the data for actionable insights across the business.”
The report advices CFOs that want to be strategic to “evaluate the tools, processes and structures they use today and target technology that will help them thrive in this new world of data.”
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
Digital Transformation Strategies
By Lanrex on 20/04/16 11:22 AM
The mantra pervading IT today is that businesses are being rapidly and massively digitally disrupted and must undergo digital transformation into digital business to survive and prosper. That’s easier said than done, and there’s no end of advice on how to go about it. Here’s one model.
This one comes from Dell and is encapsulated in the ‘the five Rs’: recognise, rethink, render, re-organise and realise. It’s a handy way identifying and delineating all the stages of the process, but hardly revolutionary.
For example, stage 1, the Recognise phase, requires “consultants, business leaders and IT executives to work together to understand the digital possibilities present in the overall business environment.”
Once those have been identified, in the Re-think phase “the team identifies the requirements for achieving future state digital strategies and the appropriate key performance indicators for measuring success.”
Then comes the Render phase “in which the project team builds digital models and prototypes based on journey maps to begin moving from vision to reality.”
In the Re-organise phase “the project team gets ready for implementation by prioritising transformation initiatives, identifying needed skills, tools and technology resources.”
Finally comes the Realise phase in which the project team “brings its transformation vision into life by deploying and integrating the solutions it has envisioned, designed and prototyped.”
This could be summed up in one sentence using the same journey metaphor: figure out where you need to go, determine what you need for the journey, get the gear together and test it on a short trip; Gather the team and all the resources you need for the real journey and set off.
In a recent interview with WhaTech, Lanrex’s Managing director Jodie Korber noted “the brave organisations that commit to change, and make deliberate steps towards digital are the ones that get the most benefit in the long term”.
And, like any major undertaking, as the report, The road to digital transformation: turning strategy into execution, says: “Careful planning is the key to success.
"Companies that dive into digital transformation without adequate preparation are usually dissatisfied with the results, so the first steps on any digital journey should be developing a strategic vision and roadmap and balancing those plans with organisational readiness.”
Should you outsource your IT needs to a managed service provider? Download your free guide below.
You might also like, Digital Workspace, a journey NOT a destination
Why you should upgrade your technology
By Lanrex on 12/04/16 8:37 AM

Why do you need to upgrade the information technology in your business? The answer’s simple: Moore’s Law. It can be interpreted in several ways but the most relevant for this question is that it means the information technology bang you can get for your buck roughly doubles every two years – whether that’s in processing power, storage, or general functionality.
It’s not hard to see the impact of Moore’s Law. It’s all around us and in our faces every day thanks to the incessant advertising devoted to smartphones and tablets. Look at today’s devices, at what they can do, and what they cost, then think back and compare them to those that were the hottest products on the market five years ago.
Given the size of the market and the level of competition, innovation in consumer IT is probably occurring faster than in business IT, but the difference is not that great. The big difference, for many smaller businesses at least, is that innovation in business IT hardware and software is not ‘in your face’ like consumer IT. You might buy some hardware and software for your business and, so long as it keeps running, just forget about it.
That’s not surprising, after all, IT is not your business – you’re focussed on your products, your market, your competitors. But as the technology improves, you could be putting yourself at a bigger competitive disadvantage every day by not upgrading to the latest technology.
However, technology upgrading does not simply mean better, faster, cheaper, more reliable, easier to use, more secure versions of the same – although those are all good enough reasons for an upgrade. A decision to upgrade should also be an opportunity to look at different ways of doing things.
Cloud computing is a classic example. If the latest version of your customer relationship management system, or your accounting software, is proving too much for your ageing hardware, perhaps it’s time to look at putting that function in the cloud, moving to a software-as-a-service version, instead of upgrading to give your hardware more grunt.
If your PABX – your business’ telephone system - is past its use-by date, it may well be time to look at scrapping the whole thing, and taking advantage of that functionality ‘in the cloud’.
No business can afford to be complacent, to ‘fit and forget’ when it comes to information technology. Keeping up with technology is a matter of business continuity and growth, remaining competitive, agile and profitable.
As Lanrex managing director, Jodie Korber, points out: “'Technology in business has distinct advantages, ranging from operational efficiency to marketing and customer satisfaction. But littered among its advantages, when technology is left unattended, unfortunately, it does not always age gracefully - Security risks, severe data loss and/or corruption, decreased functionality, limited flexibility and poor professional engagement are just some adverse effects of outdated IT equipment.”
She adds: “With technology advancing at the rate at which it is today, it only takes one new feature to excel your business, through streamlined and automated systems. Staying on top of your technology can mean the difference between being ahead of or way behind your competition.”
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
Digital Transformation Explained: The Human Factor
By Lanrex on 4/04/16 10:57 AM
You don’t have to do a great deal of reading in the IT press these days to come across the topics of digital disruption and digital transformation. In a nutshell, the argument goes that digital technologies — specifically social networking, mobile, cloud computing and ‘big data’ — are disrupting every kind of business in every industry, spawning new startups and forcing incumbents to embrace these technologies (ie undergo digital transformation) or perish.
Much of the focus is on the digital technologies:
What it can do, how it is being used, by incumbents and newcomers alike. However, businesses are not digital, they are not run by robots (yet). They are run by humans who make and implement decisions.
So guess what?
It’s not just about the technology. “The ability to digitally re-imagine the business is determined in large part by a clear digital strategy supported by leaders who foster a culture able to change and invent the new.”
That conclusion comes from a study Strategy, not Technology, Drives Digital Transformation, produced jointly by Deloitte and MIT Sloan Management Review. Its conclusions are based on a survey of more than 4,800 business executives, managers and analysts from organisations of all sizes in 129 countries and 27 industries.
However, contrary to what that conclusion might suggest, it’s not totally clear which is the chicken and which is the egg. The study also says: “Whether culture drives technology adoption or whether technology changes the culture is still an open question.”
Your strategy matters to the digital transformation!
In other words, non-strategic adoption of digital technologies could, if a company is receptive, precipitate a ‘digital culture’ that accelerates the adoption of digital technology and that reshapes company strategy around it.
The report quotes senior executives espousing both views. Says one: “I have never seen a technology drive change on its own. Culture leads the adoption of technology. Our ability to innovate depends on the impatience of our culture.”
Another says: “Social helped get the momentum going. As more people jumped on board, social played a major part in changing the culture. I’d like to say it was thought through in advance and part of a formal culture change program. But it wasn’t. The change started with a technology experiment.”
What is common to both those stories is that the culture, whether created reactively or pro-actively, ultimately drives the digital transformation. So culture is all important, and therefore leadership is all important.
As Lanrex managing director Jodie Korber says:
“Strong leadership is important to strong strategy and a successful technology implementation.” But she makes the additional point; that no business needs to make the digital journey unsupported. “Sometimes it can help to strategise with outsourced companies.”
This aspect was only touched on in the report. It quoted Sree Sreenivasan, chief digital officer at the Metropolitan Museum of Art, saying that the chief digital officer must also be the chief listening officer with “the responsibility “to listen for new ideas, listen for talent and listen for people who can help us and work in partnership with other organisations.”
Once again, it shows that the human factor is always important!
Want to know more about digital technologies and other important tech topics you should be on top of?
Sign up to our 7 part series below!
You might also like: Digital Transformation Explained
Embrace the new age with a powerful digital strategy
By Lanrex on 31/03/16 9:58 AM
https://www.lanrex.com.au/blog/three-great-examples-of-it-strategy-and-one-surprising-one
So what are the characteristics of a digital workplace, and how can you implement them into your workforce to maximise the benefits for your money and your team.
Strategy& (an arm of PwC) sums it up in just three words, in the title of its report, Designing the digital workplace. Connectivity, communication, collaboration. In other words, a digital workplace employs digital technology to ensure that those three functions are as seamless, efficient and easy to use as the technology permits.
Strategy& expands these three broad features into five elements, which make up the digital office framework:
-
Access Devices
-
Communications Infrastructure
-
Business Applications
-
The Workplace Environment, and
-
Digital Security
And make no mistake, a digital workplace is not merely a ‘nice to have’. It’s an essential precursor to success into today’s digitally disrupted business environment.
As Strategy& says in its report, “Companies in every industry are facing real challenges in offering employees the best of the new technologies they need. But those that can see the strategic value of the working environment, and can get in front of the movement to the truly digital workplace, will have a clear advantage in productivity, innovation, and collaboration. That, in turn, will enable them to attract the talent they will need to stay competitive and to align with the social and business transformations taking place around the world.”
Closer to home and on a more down to earth level, Australian IT market research company Telsyte released in March its Australian Digital Workplace Study 2015. It covered “trends in business ICT spending and strategy and how IT and business leaders are preparing for the impact of emerging technologies.”
One trend stood out: as organisations move to create a digital workplace, a greater portion of IT expenditure will end up in the hands of business units. More than half of the 440 CIOs surveyed by Telsyte said they believe line of business IT spending will exceed central IT spending within five years.
Telsyte reported that 79% of organisations have at least one line of business – including marketing, operations and finance – with its own IT budget.
“This is up five percent from 2014 and shows a growing demand for IT services from areas of the business like marketing,” Telsyte said. “Combine this with more accessible cloud-based applications and the CIO has another information management procurement channel to deal with.”
Jodie Korber, MD of Lanrex and Sydney-based Outsourced IT provider describes the importance of a properly managed Digital workplace; ‘The digital workplace is the virtual equivalent of the physical workplace, it is a system that needs to be planned and managed coherently as it is a fundamental feature of employees’ productivity, engagement and overall job satisfaction. Managers need to address the opportunity of a digital workplace as a whole coordinating it between technology, processes and most importantly its people.’
So what should you do?
Get in touch with Lanrex, our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure, managed IT services & digital strategy.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready - Contact Lanrex today.
You might also like, Cloud Computing, are you ready for the future? .
Fun with data analytics
By Lanrex on 23/03/16 12:00 PM

“Religion”, “fun”, “social”. They’re not words you’d expect to be associated with a discussion on the importance of data to a business, and advice on how to manage, manipulate and extract maximum value from data. Nevertheless, those are the exact words the Economist Intelligence Unit (EIU) is using in its report The Virtuous Circle Of Data — Engaging employees in data and transforming your business.
In the report, the EIU argues that many companies have invested significantly in gathering vast amounts of data, yet still struggle to extract insights, put them to work for the business and create truly data-driven organisations. The report “explores how organisations can spark a chain of events through top-down leadership and bottom-up employee engagement that creates a culture with data at the centre of decision-making.” This, the EIU says, requires both top-down leadership and bottom up engagement.
The religion aspect comes in a quote from LinkedIn’s head of business-to-business products, Russell Glass, who says — in the context of achieving top down leadership: “There is no substitute for a corporate leader who has found religion in data and analytics.”
The fun and social aspects come from the EIU’s suggestions on how to motivate the rank and file employees of an organisation to recognise the importance of data.
Bottom-up engagement — motivating and engaging employees across all levels of the organisation to use data — the EIU suggests, can be achieved by “putting in place training and advancement programmes focused on data analytics, creating compensation incentives and competitive motivators, and even making data analytics fun and social.”
Making data analytics fun, it suggests can be achieved by “linking data with the basic instincts and needs all employees share: to compete, to shine and to feel happy and fulfilled at work.” In one example sales teams compete with each other on their metrics, and the winners receive a trophy and an extra day of vacation.
The EIU says that “There is no replacement for a CEO with a vision and a personal mission to inspire and instil a culture that looks for data-driven insights and works on facts-based decision-making. … It is an absolutely necessary condition for building a data-driven business.
Lanrex managing director, Jodie Korber noted that, “In our experience we have found that many companies have a great ability to collect data, but often this data is not transformed (through analytics) into meaningful information, which can be used to align business employees and the business strategy. It is vital that the data being collected is being used to make changes and used as reference points to ensure the business stays on track to accomplishing its goals and fulfil its overall strategy.“
The report from EIU offers little in the way of suggestion as to how a non-believer can be made to ‘get’ the religion of data, but says the trickier and perhaps more critical element is “engaging and motivating employees across the organisation to embrace the spirit, thinking and practices of a truly data-driven business—and to do so in a consistent, unwavering manner day in and day out.”
That will be no small feat, but even companies that feel they have made the transition to being truly data-driven won’t be able to rest on their laurels. The EIU suggests that many companies are well on their way to transforming themselves into data-driven businesses, but will need to gear up for the next stage in their evolution: “learning to be creative and innovative with data — to not only consistently use the tools that they have built and apply methods that they have learned, but to invent and create new ones all the time and to drive change without the need for top-down initiatives.”
Lanrex concur that ‘ creating a culture of change does not happen overnight, but by using meaningful information through data gathered by your business can really put the wheels in motion to see where changes need to be made and can have a pivotal impact on business success.’
It’s a great time to be in business.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
In praise of IT audits
By Lanrex on 23/03/16 11:31 AM
The word audit is usually enough to send shivers down the spine of some of the largest corporation in Australia, but the reality is, audits, especially IT audits are vital to business operations and sustainability.
In today's society with the imminent threat of security breaches from internal and external sources, it just doesn't make sense for companies leave the structural integrity of their IT infrastructure unattended, especially when IT today is so heavily relied upon by all facets of the business.
IT audits; undertaken for security, prosperity and competitive advantage are essential, done efficiently and done with an understanding of what the real objectives are.
An IT audit is defined as “the examination and evaluation of an organisation's information technology infrastructure, policies and operations.” It “determines whether IT controls protect corporate assets, ensure data integrity and are aligned with the business's overall goals.”
IT auditors “examine not only physical security controls, but also overall business and financial controls that involve information technology systems.”
According to the Infosec Institute — a US headquartered body that claims to be “the best source for high quality information security training” — “Most often, IT audit objectives concentrate on substantiating that the internal controls exist and are functioning as expected to minimise business risk. These audit objectives include assuring compliance with legal and regulatory requirements, as well as the confidentiality, integrity, and availability of information systems and data.”
While the process might be called an IT Audit, it is, according to one expert “an overall business assessment that determines the extent that the IT organisation is supporting the objectives of the business.”
He then goes on to list the six components of an IT audit. Given his view of the process, it’s hardly surprising that components one and two are business, not IT related. First comes a definition of the company’s objectives. This is followed by reviews undertaken by department heads and key managers to determine business issues, objectives, and perspectives. Only when those have been completed does attention turn to IT.
It’s at this stage that we get down to the nuts and bolts of actually auditing IT and it’s a good idea not to try and do this yourself.
It is always tempting to try and cut costs by employing internal staff to complete audits, but outsiders are more likely to spot problems by bringing a fresh eye to the exercise.
Given how critically a modern business relies on IT systems, an IT audit should not be an option. This is why Lanrex, performs them regularly for businesses as part of their Managed IT services offering. To help a business identify exactly where its IT dependencies are, quantify risks and assess the adequacy of security measures.
An Audit creates a snapshot of the current state of IT and its inter-relationship with the business. It identifies where changes need to be made, either for business security or compliance. Done regularly — with technology changing rapidly this needs to be at least annually — and audit can be used to establish a baseline from which you can measure your company’s progress (and also evaluate the professional advice you were given from the previous year).
'Lanrex are a Sydney based Managed Service provider, priding themselves in offering the best services for their clients. For a limited time, they are offering a Free Remote audit for companies interested in generating a comprehensive report to assess their current IT Infrastructure. The report is a great starting point for future IT reporting, to ensure the organisation has been creating efficient reviews and revision of their systems in the past.
For more information on the importance of IT AUDITS and how to complete a successful audit click for further reading.
How to manage a successful IT Audit: http://www.lanrex.com.au/blog/how-to-manage-a-successful-it-audit
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready?
TRACEing the path to enterprise security
By Lanrex on 17/03/16 2:12 PM
Industry research firm Frost & Sullivan has come up with what it says is “the new industry standard for holistic enterprise security,” and yet another acronym: TRACE, for ‘Threat Response Adaptive Core Ecosystem’. Here’s what it means.
Frost & Sullivan explains TRACE in a white paper. According to F&S’s senior industry analyst and the head of its cyber security practice, Charles Lim. “The inspiration behind TRACE was to create a new industry standard for the cyber security community by developing a holistic approach which includes not only security products but also the expertise required to prevent, detect and remediate threats effectively in the enterprise environment.”
F&S says the limitation of current security services and dedicated high-end appliances to handle specific tasks is pushing companies to look at a holistic approach to security that combines endpoint protection with firewall intelligence and advanced security tools. “As security vendors continue to innovate, it is vital that offerings be part of a holistic approach where management to remediation can be achieved easily and seamlessly,” it says.
T.R.A.C.E
TRACE is designed to “help enterprises evaluate the right tools for a holistic security approach.” F&S believes that adopting a platform approach can “operationalise the vision of a holistic security strategy, comprising the right balance between security mindsets, tools and skill sets.”
The approach to security set out in the TRACE white paper is designed to cover all aspects of organisational IT — access, endpoints, web assets, cloud and mobile based applications, content — along with human factor mitigation, vulnerability management and security analytics.
Lanrex managing director, Jodie Korber, said: “TRACE presents a useful shopping list not only of the security hardware and software an organisation should implement, but also of the people, policies and procedures it should put in place. And, in line with the accepted wisdom that security breaches are inevitable, the emphasis is on detection and remediation as much as prevention.”
F&S’s aim seems to be that buyers of security technologies and services will embrace TRACE and push the security industry to follow suit.
It says, “TRACE aims to provide assessors with insights into the critical features and identify future vulnerabilities to help build and deploy a holistic security strategy to tackle the ever-evolving threat landscape.”
And: “Security vendors need to consider moving their investments into establishing a more holistic approach to not only strengthen prevention tools, such as penetration testing solutions, but also develop a full detection and remediation strategy for the user.”
Finally, the white paper comes with a caveat: “The recommendations are from an analyst’s point of view and may not necessarily comply with specific security standards, such as ISO27001 or cyber security legislation of any country.”
What should you do next?
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
You might also like, Cloud Computing, Are you "Cloud Ready"
Are you cognisant of cognisant computing?
By Lanrex on 17/03/16 2:08 PM

If not, you should be. So says market research and analysis firm Gartner. "Cognisant computing — the next phase of the personal cloud movement — will become one of the strongest forces in consumer-focused IT," Gartner says. It adds that cognisant computing will "have an immense impact across a range of industries, including mobile devices, mobile apps, wearables, networking, services and cloud providers, causing major shifts in revenue and profit flows."
Gartner predicts that cognisant computing will put the importance of apps, services and cloud to the forefront making it one of the three most important components for any customer retention strategies for B2C companies over the coming five years.
So what exactly is it, and where did it come from? "Cognisant computing is a consumer experience in which data associated with individuals is used to develop services and activities according to simple rules," Gartner says. "These services include alarms, bill payments, managing and monitoring health and fitness, and context-specific ads. Cognisant systems will deliver their services across multiple devices."
As to where it came from the answer seems to be Gartner, and important as it may be in Gartner's estimation it has not yet achieved the status of an entry on Wikipedia. The term appears to have been coined by Gartner and the concept is being promoted almost exclusively by that company, but with some other followers.
However there is no doubting the validity of the phenomenon. Here is what it involves. "By amalgamating and analysing data in the cloud from many sources (including apps, smartphones and wearable devices, websites, store purchases, and social interaction), cognisant computing will provide contextual insights. This will help companies expand the lifetime value of their increasingly fickle customers, improve customer care, boost their sales channels and transform the customer relationship — by making it more personal and relevant."
Gartner adds: "In essence, this new development will help companies to innovate and create new business opportunities by creating hypercontextual services that will appeal to a dedicated individual — rather than catering to the mass market.
However, critical issues will have to be addressed including consumer privacy, quality of execution and becoming a trusted vendor."
Jodie Korber, Managing Director of cloud computing supplier Lanrex added “technologies that bring together disparate information sources to improve customers experience are set to transform many businesses. Leveraging technology to deliver new capabilities enable organisations to focus on education, relationship building and business growth“
So in essence cognisant computing is the technology that will underpin the move to put customers at the centre, to deliver more personalised services to 'a market of one'.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready? In only a few moments find out with our Cloud Ready self-assessment tool
The Internet of Things is coming. Are you ready for it?
By Lanrex on 7/03/16 11:57 AM

The internet of things (IoT) can simply be explained as the embedding of computer and communications systems into everyday objects. Enabling them to be tracked, controlled or to exchange data. Improving efficiencies and accuracy for anything from smart cars to heart monitors.
The IoT is predicted to have a massive impact on all industries. And something that IT needs to have its eyes on.
The IT departments of Australian companies are not well equipped to deal with the expected rapid growth in the Internet of Things, according to a survey undertaken by network management software company SolarWinds.
Skills shortages and concerns about cyber security were the two most frequently cited barriers to IoT by the 200 survey respondents. Concerns about the adequacy of data privacy legislation, network capacity and managing the increasing complex networks that IoT will create were also rated as significant barriers.
The study explored current level of preparedness for Australian IT departments to meet the complex challenges and opportunities created by the IoT.
About fifty percent of respondents said that more and different skills would be needed in the IT department to handle IoT. Around half of the respondents said that the workforce was able to meet the demand for IoT skills “to a limited extent”.
Strangely, while respondents rated IT departments as being not well prepared for IoT, around 50 percent also identified these departments as the business units driving IoT in the Australian workplace. Only about 10 percent saw the push for IoT as coming from the top.
However other surveys have identified IoT has being on the strategic radar for many Australian companies. In one recent survey, Australian organisations were asked “How important is IoT to your organisation’s business plans in the next 12 months?” Forty six percent said “very important”, and 77 percent said they already had an IoT strategy.
Another survey, of 500 IT and marketing professionals in large and mid-size companies reported: “Forty percent are using machine data (IoT) to support digital marketing. … Nearly 20 percent are being very aggressive this way, and another 27 percent plan to begin an IoT project for digital marketing soon.”
In contrast, only about 10 percent of respondents to the SolarWinds survey identified marketing and sales as being drivers of IoT.
What none of the surveys seem to have done is to try and elicit from respondents what they understand IoT to mean, or to try and assess their overall understanding of what is still a very young industry, and one with very many potential applications across almost every industry.
About Lanrex
Our team are highly experienced in helping businesses get the most out of technology. Consulting, cloud infrastructure and outsourced IT services.
Don't waste your budget spend on soon-to-be-obsolete technology that can't evolve with your business. Find out now if your business is cloud ready?
You might also like: Cloud Computing are you ready?
The benefits of an enterprise wide data strategy
By Lanrex on 5/01/16 10:00 AM
Research firm IDC says many organisations lack an enterprise-wide data management strategy, creating significant challenges for their IT departments.
Including impact on storage budgets, compromising their ability to harness the full value of all their data assets and leaving them unable to accurately assess the costs and risks of inadequate protection.
“C-level executives are realising that their organisation's performance and competiveness largely depend on how effectively they manage and use their data to improve decision making, balanced against their ability to protect it,” IDC says.
“Becoming a data-driven organisation is no longer a choice, but a necessity. Making decisions based on data-driven approaches not only increases the accuracy of results but also provides consistency in how the results are interpreted and fed back into the business.”

IDC’s comments come from a white paper ‘The data-driven organization: unlocking greater value from data and minimizing its associated costs and risks’, sponsored by CommVault. The white paper reported the results of a survey of 600 IT decision makers undertaken by IDC across 10 countries in Asia Pacific.
Forty percent of respondents said that their information management strategy — including backup, recovery, data protection and analytics — was managed at a departmental level. This, IDC says, is bad news.
“The lack of holistic or enterprise-wide data management strategies can have a major impact on business agility and performance. Not having access to the right data at the right time affects the organisation's ability to anticipate and respond to new market trends and address changing customer requirements. Understanding what those customers' needs are and addressing their expectations can be difficult if key customer data is spread across different applications, platforms and departments”
According to IDC, the different types of customer data managed by marketing (eg Web and social) need to be integrated (and analysed) with datasets from other departments like sales and finance to have a clearer view of customer priorities, and to deliver on those.
Similarly, finance departments require better (and increasingly real time) access to key data assets from various departments to ensure better company planning.
Organisations that want to implement an enterprise-wide data strategy face considerable challenges, not the least of which is the ever-growing volume of data such a strategy has to embrace.
However, developing and successfully implementing an enterprise-wide data strategy is not the end game. The real benefits come when an organisation leverages this resource to become data-centric and data-driven. IDC says: “Becoming a data-driven organisation is more than investing in the technology, since this transformation needs to be complemented with a cultural shift toward analytically oriented decisions and processes. Also, in a data-driven organisation, technical staff should no longer be only focused on managing the infrastructure, but instead become managers of the data.”
The benefits can be considerable. IDC says its research shows that organisations that are highly analytical are more than twice more likely to substantially outperform their peers than others. Its research also found that managers at the most competitive organisations are much more reliant on business analytics (rather than intuition) than managers at their least competitive peers.
Organisations faced with an ever-growing flood of data might be tempted to put the implementation of an enterprise wide data strategy in the ‘too-hard’ basket, but the dangers of doing so should not be underestimated.
“Data analytics as a tool for competitive advantage is still in its infancy, but is sure to grow rapidly. Those organisations still hampered by data silos will find themselves at a distinct disadvantage.”
Lanrex have made an easy to use downtime calucator to help you identify your room for growth. See below:
You might also like, 5 Key things you need for a successful sharepoint strategy
Innovation analysed from studies of successful companies
By Lanrex on 29/12/15 10:00 AM
It seems counter-intuitive – trying to put a structure around innovation, which, after all, is about creating something new; about thinking ‘outside the box’. So what is innovation analysed?
Nevertheless some academics at Cambridge University’s Judge Business School in the UK have done just that and published their results in a report sponsored by US telco giant AT&T: Six degrees of innovation: predicting transformative business models.

The author say they have identified several characteristics of successful business model innovations that occur with robust regularity and that these result from matches between technology trends and supply and demand trends give rise to “Six Degrees of Innovation”
“We can diagnose some common patterns across the successful matching of the technological and market trajectories,” they say.
They list these as being
- Tailor-made products and services that meet customers’ individual needs; such as downloading personalised apps to a mobile phone.
- Sustainability; where companies minimise waste and manage resource costs.
- Jointly owned assets; such as peer-to-peer businesses.
- Only paying for service that is used; such as car-share companies.
- Effective monitoring of supply chains; such as businesses which use handheld tracking systems to better monitor their operations.
- Using data to easily adapt to customer needs; such as clothing companies that can quickly produce new designs to meet fashion trends.
The key technologies trends identified as enabling and driving innovation are: the mobile Internet; cloud computing; the Internet of things; the connected car; process optimisation and customisation technologies and sensing/interfacing and material technologies.
The report’s co-author, Stelios Kavadias, professor of Enterprise Studies in Innovation & Growth at the Judge Business School, said: “This is the most comprehensive study we have ever undertaken on innovation. The Six Degrees of Innovation are present in successful innovators across all industry sectors. We believe this concept breaks new ground in identifying how and why transformational innovation occurs.”
The idea is that, equipped with these insights businesses will be able to be more innovative. The authors suggest that their report could provide business leaders with new tools and a practical guide to recognise opportunities for successful business transformation.
“It means that company leaders can assess their business’s propensity to innovate, and develop contingency plans that minimise the risk of disruption and failure. Moreover, by examining cases of transformational innovation business leaders can identify the required technology changes to adjust their business model along such ‘regularities’.”
Steve McGaw, Chief Marketing Officer, Business Solutions, at the study’s sponsor, AT&T, said: “The Six Degrees of Innovation is a tool for executive teams to adapt their business models and adopt the right technology to succeed.”
For a successful Change Management implementation, first consider changing the way you manage change.
By Lanrex on 22/12/15 10:00 AM

A staggering statistic is that 70% of change programs fail to achieve their goals, this can be greatly attributed to employee resistance and a lack of support by higher management.
Another statistic: Change is 30% more likely to stick when people are invested in the change.
Whilst businesses today are huge advocates for technology to improve their customer facing business, very little consider using technology to promote internal changes, yet applying digital tools to internal changes can make the whole process more meaningful for those experiencing change and those implementing it.
Businesses today are presented with a double edged sword every day, they must deliver rapid results and sustainable growth in an increasingly competitive environment. Business markets today are face based making change inevitable. Managers are forced to make decisions quickly, leaders need to react more readily to opportunities and threats and employees need to be more flexible and collaborative than ever before.
The rate at which we accept, implement and drive change in now critical to an organisations competitive advantage. We see today that many organisations no longer implement the 3 -5 year strategic plans, not because they are disorganised or lazy but because the luxury of time to test and roll out change is no longer available to the same capacity it was 10-20 years ago. New initiatives now need to be implemented in a compressed amount of time. Markets today are competitive and fast paced and companies that cannot adapt in due time, will quickly be left behind.
Digitising change can make a huge difference to the success of the change management. Five areas to start digitising change include:
1 – Personalise the experience
Like when building relationships with customers and potential customers we are told to be strong personal relationships through personalised messaging etc. personalising change internally is about filtering information that is uniquely relevant to the user. Segment information by role and contribute their role to the greater goal. Providing specific and relevant information helps workers to clarify and prioritise their activities, it also increased accountability and aims to reduce delays.
2 – Build a community of change.
Providing an outlet for colleagues to share information related to a task and provide updates on progress is important to building a strong group dynamic and group participation. Tools to allow this type of connectivity are dashboards and online forums
3 – Providing real time feedback.
Just in time feedback is designed to offer the recipient the right information when they can actually use and implement it. This allows them to change behaviours and see the effects of these judgements instantly.
4 – Demonstrate progress
Digital change tools allow the organisation to see changes in real time. This type of depiction of change can create a sense of urgency and
5 – Sidestep Hierarchy
Through digital tools used to connect people directly across the organisation, it allows them to sidestep hierarchal protocols and shorten the time it takes to get tasks done. Digital communication platforms allows employees to connect directly with other parties and employees who may assist on a issue, this assists in getting things done quickly and efficiently.
NEWS - In praise of IT audits
By Lanrex on 15/12/15 10:00 AM
The word audit is usually enough to send shivers down the spine of some of the largest corporation in Australia, but the reality is, audits, especially IT audits are vital to business operations and sustainability. In today's society with the imminent threat of security breaches from internal and external sources, it just doesn't make sense for companies leave the structural integrity of their IT infrastructure unattended, especially when IT today is so heavily relied upon by all facets of the business.'
IT audits; undertaken for security, prosperity and competitive advantage are essential, done efficiently and done with an understanding of what the real objectives are.
An IT audit is defined as “the examination and evaluation of an organisation's information technology infrastructure, policies and operations.” It “determines whether IT controls protect corporate assets, ensure data integrity and are aligned with the business's overall goals.”
IT auditors “examine not only physical security controls, but also overall business and financial controls that involve information technology systems.”

According to the Infosec Institute — a US headquartered body that claims to be “the best source for high quality information security training” — “Most often, IT audit objectives concentrate on substantiating that the internal controls exist and are functioning as expected to minimise business risk. These audit objectives include assuring compliance with legal and regulatory requirements, as well as the confidentiality, integrity, and availability of information systems and data.”
While the process might be called an IT Audit, it is, according to one expert “an overall business assessment that determines the extent that the IT organisation is supporting the objectives of the business.”
He then goes on to list the six components of an IT audit. Given his view of the process, it’s hardly surprising that components one and two are business, not IT related. First comes a definition of the company’s objectives. This is followed by reviews undertaken by department heads and key managers to determine business issues, objectives, and perspectives. Only when those have been completed does attention turn to IT.
It’s at this stage that we get down to the nuts and bolts of actually auditing IT and it’s a good idea not to try and do this yourself.
It is always tempting to try and cut costs by employing internal staff to complete audits, but outsiders are more likely to spot problems by bringing a fresh eye to the exercise.
Given how critically a modern business relies on IT systems, an IT audit should not be an option. This is why Lanrex, performs them regularly for businesses as part of their Managed IT services offering. To help a business identify exactly where its IT dependencies are, quantify risks and assess the adequacy of security measures.
An Audit creates a snapshot of the current state of IT and its inter-relationship with the business. It identifies where changes need to be made, either for business security or compliance. Done regularly — with technology changing rapidly this needs to be at least annually — and audit can be used to establish a baseline from which you can measure your company’s progress (and also evaluate the professional advice you were given from the previous year).
'Lanrex are a Sydney based Managed Service provider, priding themselves in offering the best services for their clients. For a limited time, they are offering a Free Remote audit for companies interested in generating a comprehensive report to assess their current IT Infrastructure. The report is a great starting point for future IT reporting, to ensure the organisation has been creating efficient reviews and revision of their systems in the past.
For more information on the importance of IT AUDITS and how to complete a successful audit click for further reading.
How to manage a successful IT Audit:http://www.lanrex.com.au/blog/how-to-manage-a-successful-it-audit
For more information:
Embrace the Digital Workforce for Digital Transformation
By Lanrex on 8/12/15 10:00 AM
A digital workspace is the conglomerate of digital tools provided by an organisation to its employees that allow them to complete their jobs. This include all hardware and software that is used by the organisation for example HR
systems, email, Calendaring, intranet and many more.

Lanrex like to describe the digital workspace and the virtual equivalent of the physical workplace, it is a system that needs to be planned and managed coherently as it is a fundamental feature of employees’ productivity, engagement and overall job satisfaction.
Today, employees want more freedom to work, anytime, from any place anywhere in the world. The heart of any digital workplace is the people.
Technology is advancing at a rapid rate driving changes not only in the digital workplace but also the physical workplace, managers need to address the opportunity of a digital workplace as a whole coordinating it between technology, processes and most importantly its people.
The digital workplace should be better able to facilitate innovative and flexible working practices, it should be deliberate and it should be ongoing. The most visible benefits of digital workplaces are the use of technologies and ways of working that allow people to connect, collaborate, communicate and co-operate with each other without having to be in the same place.
Digital workplaces encompass all technologies that people use to get work done, it is not just the implementation of an intranet, a social networking site or about being a social business.
Digital workplaces matter because they break up the way in which people interact with their physical place of work, successful digital workplaces free employees on how they work, how they form teams and how the organisation comes together. They (Digital Workplaces) empower your employees to be creative….wherever they are, and this is where competitive advantage is born.
**Image from Coud consulting Knoxville
Cloud 101 - What is Cloud Technology?
By Lanrex on 1/12/15 10:00 AM
The world of ‘Cloud’ can be quite confusing. Acronyms like SaaS, PaaS, IaaS, and even XaaS; terms like private and public, cropping up alongside hybrid (a word you’re probably more accustomed to being used by rose growers).
To add to the confusion, and the concern, you’ll likely hear people telling you that you’re already using cloud technology without even realising it, and in the same breath telling you that cloud is insecure.
Now there’s an easy way to dispel the confusion, and put your mind at rest. The Lanrex Cloud Guide 101 that delivers the basics about the cloud, different cloud models and services.
It explains that, in essence ‘cloud computing’ is simply having the software — operating systems and/or applications — and the data for your business running on hardware and storage located in a remote data centre and accessed over the Internet.

It explains how you are most likely already using cloud services. “For instance, when using personal mail accounts such as Gmail and Outlook.”
So what about that strange juxtaposition of cloud types: public, private and hybrid? The guide explains that, in a public cloud, your operating systems, applications and data all reside on hardware shared among many users. The big advantage is that you pay only for what you use.
With private cloud services the hardware is dedicated to you, but by locating in a purpose built data centre you take advantage of its security and redundant power supplies. And you free up space on your premises.
Hybrid cloud is simply a combination of the two.
And those acronyms: PaaS, SaaS: IaaS. They’re short for Software as a Service, Platform as a Service, and Infrastructure as a Service and they denote the different types of services that the cloud can provide.
SaaS is where all cloud computing users share the same software, such as an email system, or accounting software. With PaaS you get access to the CPU, storage and operating system and you choose what applications you run on those.
With IaaS you get the ‘bare metal’: CP and storage. The operating system and the applications are your responsibility. And XaaS? That just stands for ‘Everything as a Service’.
So what combination of public, hybrid and private and PaaS, SaaSand, IaaS is right for you?
The starting point, as the guide explains, is: “What are your business objectives and business plan?” Everything else flows from that: the type of cloud services you need, your security requirements (The guide explains that most cloud services provide a high level of security, but some organisations might be required to keep certain data in-house).
Still hesitant? You shouldn’t be. Many Australian companies have already embarked on the cloud journey.
And Lanrex can help you start your cloud journey.
You might also enjoy: Cloud Computing - Are You ready for the future?
Five reason your business cannot afford NOT to virtualise.
By Lanrex on 10/11/15 11:47 AM
Virtualisation is the act of creating a virtual version of a device or resource, such as a server or network and has paved the way for new major technologies.
 While the benefits of virtualisation are in abundance, there are still many organisations that are hesitant to embrace or implement virtualisation of business critical applications.
While the benefits of virtualisation are in abundance, there are still many organisations that are hesitant to embrace or implement virtualisation of business critical applications.
|
Benefits of Virtualization |
|
|
Fewer physical servers onsite. |
Allows business to continue using legacy software. |
|
Reduced maintenance and energy costs. |
Enables move to the cloud. |
|
Longer hardware refresh cycles. |
Instant offsite access to files and applications. |
|
Increased server efficiency |
Less downtime and fewer unplanned outages, increase Business Continuity |
|
Quicker and easier backup and disaster recovery. |
Less time spent providing desk side support. |
|
More efficient IT infrastructure. |
More efficient deployment of hardware and software installation and upgrades. |
|
Reduced operating costs. |
|
Failure to virtualise is leaving companies open to facing unnecessary high costs, greater risk to business disruption and increasingly complexed IT infrastructure. What’s more is that failures to embrace virtualisation means your company may not be establishing the right infrastructure for the future of cloud, big data and mobile movement technology is headed.
Five reasons your company cannot afford not to virtualise
Less flexible business operations
- Agility and flexibility is the key to business success in today’s working environment, no matter the size or industry your business resides. Through quick response times to customers, employees and shareholders is imperative to keep business operations moving forward. Business must be able to adjust in a moment’s notice as they learn new things about their customers’ expectations, preferences and experiences.
Virtualisation is a driving force to increased business agility as it is much easier to deploy and scale resources, all at a reduced cost.
Decreased efficiency for non-virtualised environments.Virtualising systems eliminates the need for IT workers to manually perform routine maintenance and trouble shooting. With less system downtime employees are more productive and efficient.
Increase risk of business Disruption
Often the cost of downtime in underestimated by business leaders, it is the unseen costs that can be the most crippling to a business. (If you’re interested to see how much your downtime could be costing you, click here).
Virtualised disaster recovery systems are significantly cheaper than many legacy solutions businesses employ today. Virtualised systems eliminate the need to have a mirror image of your data stored of site, rather it can be captured and stored anywhere, minimizing downtime and response times.
Significantly increased costs.
Virtualisation has a proven track record of reducing IT costs, not only for upfront capital expenditure with the need for less servers but also on-going maintenance. Combining the management of physical and virtual servers can also further reduce business costs, as the costs of support and ongoing maintenance are much lower for virtualised environments.
Not following technology trends – Insufficient platform for next generation IT initiatives.
Technology has seen significant changes and opportunities driving the next generation businesses, Cloud, mobile and big data are all easer with virtualised systems, Virtualisation provided the framework or cloud computing, a revolutionary new way of doing business. With more and more businesses today transitioning to the cloud, virtualising business critical application is a must.
Without virtualising your business you run the risk of being left behind and ‘sitting on the sidelines’ of your market, this is a risk far too big for any organisation big and small.
The benefit of virtualisation cannot be denied, but more importantly they cannot be overlooked or ignored. Businesses in today’s market simply cannot afford to not virtualise. The benefits of virtualising go beyond costs savings, they include simplifying IT, improving efficiency, increasing competitive advantage and giving your
Organisation the best chance of staying ahead with next generation IT initiatives.
If your company have not virtualised yet, it’s time to ask yourself – Why not?
Call Lanrex today to discuss your options for virtualising your business.
**Image courtesy of tsisupport.com.
Tips and tricks for an easy office relocation
By Lanrex on 3/11/15 1:47 PM
Whether you’re moving to a bigger office or expanding your current office, there are a great number of challenges that come with the task of an office relocation. The most important would be the task of minimising disruptions, it shouldn’t be a totally un-realistic expectation that your communication infrastructure is fully functional on the first day in the new office.
The most important would be the task of minimising disruptions, it shouldn’t be a totally un-realistic expectation that your communication infrastructure is fully functional on the first day in the new office.
IT infrastructure is vital to key business operations and without it functioning at its most optimal level or at any level can have dire operational and financial consequences for your business.
The key to a smooth office move is to break down the office relocation project into a series of simple tasks & checks to ensure that your office move is managed efficiently & effectively. The following tips will assist you and your designated team make your office move and relocation of IT infrastructure less stressful.
1. Make sure you have planned the move well in advance.
Giving yourself and your office at least 3 months to plan your move is a good measure of time, the more time you give yourself the less stressful it will be. Allowing for added consideration and all measures to be taken.
2. Appoint a single point of contact.
Having a single point on contact makes office relocations much simpler as it minimises the risk of instructions and other orders being ‘ Lost in Translation’ everyone knows who to answer to and who is in charge.
3. Have IT provider or in-house IT experts survey the new site.
Having your It specialist survey the new premise is a good way to assess the validity of your IT Infrastructure plans.
4. Move out of business hours.
Out of hours moves and beneficial because they minimise the risk of business downtime.
5. Update your equipment.
An Office relocation is a great time to assess the office equipment, there is not point spending money on moving old of equipment that will need to be replaces shortly after. Office moves are generally a great time to invest in new technologies and equipment to ensure all your Infrastructure is up to date.
6. Work with team leader and IT Team (External or Internal) to prepare a moving guide.
Detailed plans explaining every person’s responsibilities for the move, this will minimise the risk of employees making mistakes and everyone can be held responsible to make the move successful.
7. Have a business continuity plan in place for before, during and after the move.
Some downtime is inevitable, but putting in place a business continuity plan is a good may to minimise the amount and risk of further disruptions during the move. It is a good idea to keep some equipment online and your old office while the move is happening, this will allow some operations to run as normal and minimise disruption to daily operations.
To understand more about Business Continuity and how this differs to having a backup in place download the ebook, “Backup vs. Businesss Continuity.”
Did you know? Outdated technology could be costing you more than an upgrade
By Lanrex on 27/10/15 10:00 AM
Technology is the driving force behind business today, business resources are under constant demand to make sure our customers are getting the best experience, this often means that behind the scenes resources such as technology do not get the attention and nurturing it deserves.
Understandably, companies loath to spend hefty amounts on technology upgrades, every 12-24 months. But, unfortunately outdated technology can cause series issues for you and your customers.
Outdated technology is often the cause of a decline in productivity from your employees. This can cause severe problems for your business if your employees are not being productive it means it is costing your business more money than it should to drive sales, share information and ultimately get the job done, increasing bottom line and decreasing profits.
Technology in business has distinct advantages, ranging from operational efficiency to marketing and customer satisfaction. But littered amongst its advantages, when technology is left unattended, unfortunately it does not always age gracefully - Security risks, severe data loss and/or corruption, decreased functionality, limited flexibility and poor professional engagement are just some adverse effects of outdated IT equipment.
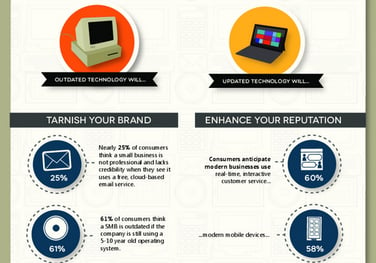 With technology advancing at the rate at which it is today, it only take one new feature to push your business to the next level, through streamlined and automated system, staying on top of your technology can mean the difference between being ahead of or way behind your competition.
With technology advancing at the rate at which it is today, it only take one new feature to push your business to the next level, through streamlined and automated system, staying on top of your technology can mean the difference between being ahead of or way behind your competition.
Time and Money are major reasons for the lack of technology updates, but the top 5 risks of using outdated technology can be much more expensive than an upgrade.
System downtime and crashes all waste time, fixing these IT issues takes away from focusing on your core business functions. System downtimes are usually much costly than we initially realise – Why not calculate the cost of your downtime with our specially designed calculator.
Increased costs of fixing old IT, as Technology infrastructure evolves and ages it becomes more expensive to fix, the money being spent on fixing broken systems and hardware is money that is being taken away from growing your business.
Productivity decreases as employees work to resolve IT problems, if systems are down work cannot be finished, wait times increase and the general day to day use of the hardware and software deteriorates as the systems near end of life. If our employees are waiting 5 minutes for files to open or 10 minutes for computers to reboot or boot up, it is predicted that outdated systems can waste up to 1 week per year in productivity, PER employee!
Outdated software is often riddled with security holes, leaving your companies sensitive data open to cyber-attacks and cyber terrorism. Data security is an increasingly sensitive topic, if your business is not seen as safe, you can be sure your customers will go elsewhere to protect their unique information.
Did you know that auditors can actually fine companies that do not transition from unsupported Software? Outdated hardware and software can run the risk of legal and regulatory compliance problem down the track.
While upgrades seem to happen more and more often with technological advancements, the cost of not upgrading can often far outweigh the cost of your upgrade. It is well worth considering a move to cloud services (Read our Cloud 101 guide for more information) and a Managed Service provider to manage these upgrade for you, this will allow you and your employees to focus on what is really important – servicing your customers to the best of your ability and business growth.
**Image courtesy of Microsoft.
Secure your Mobile Workforce – How to protect your employees on the go
By Lanrex on 20/10/15 11:00 AM
 With our workforce changing and the advent of bring your own device (BYOD) over the last decade, personal security threats are now being transferred to corporate threats.
With our workforce changing and the advent of bring your own device (BYOD) over the last decade, personal security threats are now being transferred to corporate threats.
Mobile phones are now able to seamlessly connect and disconnect from corporate systems accessing sensitive data and then connecting to less secure systems – all the while bypassing the same security measures built for Personal Computers.
When discussing mobile security, it is best to focus on five basic security flaws: architectural flaws, loss of device, platform system weaknesses, permission problemsand application software weakness.
Some of the greatest risks from having a mobile workforce or digital workspaces are: user’s willingness to tap the ‘accept’ button on whatever permissions apps request, allowing trojen and other foreign viruses into their devices.
Other large risk factors come from fragmentation of devices amongst colleagues, there are multiple versions of smart devices as a result many people within the same organisation may be using outdated software and apps that are plagued with security breaches.
The bottom line is that securing mobile devices should be top priority. Whether you have a BYOD policy or not, mobile devices are integral to business productivity and you don’t want to leave any back doors open for thieves to sneak in.
Writing a BYOD policy forces companies to think things through before they let employees loose on their secure networks.
Questions that must be settled by the organisation’s leadership during the planning stage include:
- Which web browsers should employees use?
- Which security tools offer the best protection?
- What level of technical support provided by our IT?
A companies BYOD Policy should include the following sub sections:
- Introduction
- Acceptable Use
- Devices and Support
- Reimbursement
- Security
- Risks/Liabilities/Disclaimers
For more information on acceptable security for your mobile workforce and the best way to Manage and implement your mobile workforce, Contact Lanrex today.
Determine business goals and WHY goal setting is important.
By Lanrex on 13/10/15 1:33 PM
Business goal setting is a vital activity for all organisations, it’s important because it turns aspirations into tangible and measured objects. Meeting your business goals requires commitment, action and motivation.

Goals give your business and your employee’s clear direction of where all business activities should be directed, with the understanding that if the outcome of their actions will not lead to being any closer to achieving a goal, a new action should be taken.
Achieving goals requires motivations. Goal setting and motivation are often dependent on one another. Motivation is imperative in business, it impacts the mental and physical reactions of our human employees. Staff who are highly motivated a less likely to take time off, more willing to get their job tasks done efficiently and effectively which results I higher levels of productivity, revenue and overall satisfaction.
Employees with low levels of motivation are often late to show up to work, early to leave, slower to get job tasks done and do not regard efficiently or productivity highly. Lowly motivated employees more often than not cost the company money.
The good news about lowly motivated employees is that it is often caused by a lack of direction, and goal setting is often a good may to counteract this!!
Use the questions below to determine if your business goal adheres to the SMART goal methodology
-
Is your goal specific?
A specific goal should clearly state what you want to accomplish, why it is an important goal, and how you intend to accomplish the goal. -
Is your goal measurable?
A measurable goal should include a plan with targets and milestones that you can use to make sure you’re moving in the right direction. -
Is your goal attainable?
An attainable goal should be realistic and include a plan that breaks your overall goal down into smaller, manageable action steps that use the time and resources available to you within the timeline you’ve set. -
Is your goal relevant?
A relevant goal should make sense when measured against your business model, mission statement, market, client base and industry. -
Is your goal timed?
A time-based goal is limited by a defined period of time and includes a specific timeline for each step of the process.
Goal setting helps your business achieve what it sets out to do, one step at a time. What are your campanies goals and how can you acheive them? Want to chat to someone about buisness goals contact Lanrex below:
You might also like, Strategies for the Digital Transformation
How to Guide: Developing a SharePoint business strategy.
By Lanrex on 6/10/15 2:30 PM
 SharePoint 2010 is rarely bought as a standalone software product, most often it is bundled in with a negotiated Microsoft Enterprise Agreement. Because of this many business leaders are left scratching their head – When should I use SharePoint? What should I use SharePoint for? When Shouldn’t I use SharePoint? And, what exactly is this additional extra I purchased?
SharePoint 2010 is rarely bought as a standalone software product, most often it is bundled in with a negotiated Microsoft Enterprise Agreement. Because of this many business leaders are left scratching their head – When should I use SharePoint? What should I use SharePoint for? When Shouldn’t I use SharePoint? And, what exactly is this additional extra I purchased?
In the past we have seen a ‘technology first approach’ this means implement the new technology then gather the requirements and needs for the technology later, this type of approach can often lead to displeasing and unsatisfying results in usage, engagement and efficiency.
SharePoint provides a vast number of capabilities that empower business users. SharePoint enables users to collaborate with each other, tag and rate content, self-publish, and develop their own solutions. It is because of this great power SharePoint gives users that it needs to be managed carefully before it grows quickly out of control.
Like any software, SharePoint needs to be aligned to a strategy, one common mistake we see many SMB’s make is - SharePoint is the strategy when in fact SharePoint should be used to align with your existing businesses strategy and its related areas such as HR, IT, Sales etc.
This may mean that many organisations are now faced with a need to re-architect their SharePoint environments in a way that is more conducive to reaching the business goals and strategic objectives.
Do not fret, the following article will discuss how to develop a successful SharePoint strategy whether it is for a first time implementation or to re-align your software to ensure it is working toward reaching the business vision.
Your SharePoint strategy should include the following components:
1- Who are the Stakeholders?
Stakeholders are not only the decision makers in the business, when considering implementing new software such as SharePoint you need to consider all parties involved. Depending on your reason for implementing SharePoint your stakeholders will be different for each scenario. When you look to identify stakeholders, recognize that there are different types of stakeholders, all of whom should be included in the development of your solution strategy and the ongoing governance model.
An important note to remember is that users are critical to the ultimate success of your SharePoint solution, so do not be exclusive when considering the stakeholders in your strategy. It is important that the solution is easy to use and managed, does not disrupt the flow of work and does not aggravate the end users, otherwise adoption will be unsuccessful.
2 – Define key Business objectives
As Lao Tzu once said – the journey of a thousand miles begins with one step, and the first step on the road to SharePoint success is developing a good understanding of your business objectives that you are trying to accomplish.
To increase the chances of a successful SharePoint implementation, key stakeholders need to work together to carefully address the key business objectives– it is important to remember that SharePoint should align with your key objectives and not the other way around.
An example of one Business objective may be:
Decrease amount of time spent on training and development of new starters through efficient Information sharing and training programs. Improving ‘Time to Talent’. Reducing our bottom line.
3- Does the software have capabilities that are relevant to reaching business objectives?
The IT experts you have engaged (whether they be internal or an outsourced company) will need to be included when completing this section of your strategy. It is imperative that a thorough understanding of the features SharePoint offer is utilised at this time.
By knowing all the features and capabilities of SharePoint you are able to align the SharePoint software to your previously defined business objectives (Step 1)
Take the earlier example of your business objective:
Decrease amount of time spent on training and development of new starters through efficient Information sharing and training programs. Improving ‘Time to Talent’. Reducing our bottom line.
SharePoint can enhance this Business objective through a range of features
- The People and Expertise search – Allowing your new starters to find people within the business with the expertise they are looking to develop.
- Follow people, documents and tags – this gives them greater access and proximity to power enabling them to learn faster and from more developed and seasoned staff members.
- Search – Giving them the ability to ‘look-up’ information they need, when they need it, so they can learn ‘as you go’
- Activity feeds with ‘# hashtag’ features and ‘@ mentions’ – This helps with the search refinement and also with offering praise – (Tip: mentions and praise often encourage faster development.)
By using these features of SharePoint it has the ability to reduce the amount of training time each employee needs as they can now ‘Learn on the go’ and increases their output whilst still in the early stages of their employment. This effectively meets the needs and enhances the ability of the business to achieve their business objective.
*Any easy way to display this section of your plan is in table form, with your business objectives on the left hand side and on the right the SharePoint features that can assist in achieving these on the right
**If SharePoint features cannot enhance or enable your business to reach their objectives, you should not go ahead with implementation.
4- Governance
The Governance section of our SharePoint strategic plan should be viewed as your company’s insurance policy.
When the SharePoint environment starts to expand and more sensitive data starts to be housed within it – you need to ensure you have the right team and policies in place to contain any potential disasters.
Governance is about supplying a task force that outlines and maintains all the ‘rules of the SharePoint environment’. They are used to provide a quality user experience and ensure any policy violations are dealt with and resolved quickly.
The governance committee should have clearly defined the rules and responsibilities. The SharePoint governance committee, are not only representatives from the business and IT sides of the organization, it should also include executives and organisational champions (Individuals regardless of their role within the business who act as role models)
Governance ensures that the solution system is aligned with the business objectives so that it continuously delivers business value. The governance section of your strategy plan clarifies your SharePoint usage, creates a structured framework to measure and manage the solution and outlines all policies, guidance and enforcement procedures.
5-How will your organisation define and measure success.
Defining measures of success is key to any new implementation strategy, this is the time when you test the value of your organisations investment. By setting clear lines and measures of success, a metrics program should be established so that you can demonstrate the solution is meeting the business objectives. A good metrics program includes both qualitative and quantitative measures that tie the SharePoint solution as directly possible (responsible) to the businesses successes.
Qualitative metrics can be uncovered from user feedback during any of the quality assurance testing and initial training and early stages of implementation
Quantitative costs can be measured with such defined guidelines as ‘Reduced Training costs for new starters.
To gain a deeper understanding the success of your It is always a good idea to canvass user stories and experiences that describe how using SharePoint tools (finding a person with an unknown skill, following individuals etc.) helped contribute to increased profitability, increased client output, or other metrics that are already reflected in the key performance measures for the organization.
Governance committees should continually document and measure metrics to demonstrate the extent to which their governing process is improving the overall SharePoint enterprise
Contact Lanrex today, to discuss your successful SharePoint implementation strategies.
You might also like: 5 things you need for a successful SharePoint Strategy
Office 365 for small business - Is it worth it?
By Lanrex on 29/09/15 3:00 PM
Microsoft office 2016 was released to the world on 22nd September 2015, this is almost 3 years since the last major version of Microsoft was released. Simply put, Microsoft office 2016 is a new version of Office 365 Business, but the major difference is that it is the first of its kind that has been built from for ground up for mobile and cloud.
 What is the Difference?
What is the Difference?
Office 2016 wants to connect you and your co-workers together. Collaboration in the cloud is the real difference with Office 2016. Office now encourages you to share documents online, in a collaborative workspace, gone are the days of back and forth emails and even more obsolete printing out and using pen and paper to make changes.
One of the biggest and most talked about changes is with everyone’s favourite app. Microsoft Word. Word now has ‘real time co-authoring’ this allows multiple people to edit and watch others edit a document as it is happening, this type of feature was usually reserved for online versions and most commonly seen in Google Docs.
New editions to the Office line-up are Sway and delve. Sway allows anyone to create magnificent and beautiful websites using only images and text (with very little effort). Conveniently, Sway is web based so you don’t even need an application to access it. Sway allows the user to access and insert, videos, pictures, charts and even tweets! Maybe the best part is you don’t even need Office to try it – it’s all online, free of charge. Delve is an enterprise information aggregator, it finds documents and helps you discover information that is likely to be interesting to you, faster, easier and with great precision.
Mobile and Cloud FIrst
Microsoft understand that the way in which people work has changed dramatically and that is why they have but such a strong focus on mobile first, cloud first. Office 2016 encourages its users to user Office 365, Microsoft first subscription based cloud based service.
Is Office 365 for me?
Office 2016 takes a huge step forward in the transformation of productivity applications and keeping people connected no matter the time zone, Office 2016 is created with the modern working and collaboration mind set front and centre.
Microsoft released user guides that cover the new features and user apps.
Want to know more? Check out our Top 7 Benefits to Migrating to Office 365
Managed IT Services Give Better Opportunities for Business Growth.
By Lanrex on 22/09/15 10:00 AM
It is damned near impossible to fix a problem you didn’t know you had, don’t you agree? The same paradigm applies to key business infrastructure. Without complete transparency into our businesses key infrastructure capabilities and applications we may have no idea if/when or how a breach to our security might be happening.

Breaches that could be missed can include, but are not limited to:
- A staff member downloading the complete system files onto a USB
- A User account that was disabled being re-enabled for no reason
- Accounts are accessing confidential data for extended amounts of time outside of ‘normal business hours’
Often it is the case that business owner’s aren’t sure what they are capable of auditing, and what context security breaches are happening, the examples above may be isolated activities that are within business parameters, but that is impossible to conclude if you do not understand the context in which the event is happening.
For example a contractor who worked on a project who has access to confidential data, may have had their account disabled when they finished work on the particular project. If this contractor in question begins a new project they could have their account re-enabled, (if authorised by the correct people). This event does not pose a security breach.
IT Security for Business Growth
When it comes to our businesses IT security, requirements cannot be met unless we understand the relevance of events, in relation to the activities happening in their surrounding environment. Having this related data helps us understand quicker what is happening (and why), make better decisions on whether activities can be classified as suspicious events and resolve the problems faster.
Only recently have companies big and small begun to pay more attention to the link between IT risks and business risks. To achieve a balanced and focused audit, companies should first determine the right things to audit. Key areas to consider should include:
- Business applications
- IT infrastructure ( operating systems, databases, network and data centres)
- Current projects related to IT and our businesses capital spend
- How IT is support our organisations risk management.
Today’s society calls for a stricter public policy of security and risk management, with increasing threats, vulnerabilities and regulatory compliance demands, internal IT audits have never been as necessary as they are now.
IT Audits
IT Audits are about formal verification and validation of your businesses IT systems and controls. Inefficient audits can cause distress down the track, without an appropriate IT audit scope, important IT controls within an organisation may not be fully tested (or maintained)– leading to higher levels of risk including regulatory compliance risks, especially if controls are ineffective. IT audits are a measurement of IT risk management, which translates into business risk management – which if not handled property can carry severe business impacts.
Externally managed IT services enhance a company’s top line, reduce costs and increase efficiencies for a healthier bottom line.
Some organisations enjoy an all-in approach when it comes to externally managed IT services, this is complete reliance on a third party IT consultant, to proactively enable them to drive value from their IT infrastructure.
A fully outsourced approach covers a full customer experience, including activities such as:
- Installation
- Adoption
- Help Desk Packages
- Education, Training & Development
- Change Management, Audit & Data Recovery.
This is a good option for any size business, but particularly for small to medium-sized companies that don’t have in-house resources. Lanrex lets your business focus on its core business functions, while we provides peace of mind to C-level Executives freeing them up to strategize the ‘next big thing.’
The Lanrex objective is to proactively work with and guide our clients to increase their business value and expanding their capabilities, while minimising their risk of security breaches, we do much more than simply responding to customer incidents, issues and inquiries.
Want to know why your companies IT strategy is key to business growth? Download your free guide below.
How to: Manage a successful IT Audit
By Lanrex on 15/09/15 10:00 AM
The word Audit is usually enough to send shivers down the spine of the world’s biggest and most successful organisations. But for security, prosperity and competitive advantage, audits of systems and practices needs to be done, often, efficiently and successfully.
Done properly Audits will affirm the things you are doing right and point out ways to increase efficiency and results. Audits are an eye opening examination of your organisations procedures and controls, and while the initial cost may sometimes appear expensive when weighed against the benefits the cost can easily be recouped.

Who is the one to blame if your organisation gets hacked? Even if you comply with audits, if they are not done correctly, the blame and heat will still stay with the person in control over company information and client details, websites etc.
The following article is a how to guide on managing a successful audit, by following these steps you can ensure that you get the most out of your IT audits.
Establish Security baseline.
- Businesses are built on strong security policies, but with technology changing so rapidly assessments on an annual basis minimum a necessary to ensure that your security guidelines are being met. Annual audits will establish a security baseline at which you can measure your company’s progress (and also evaluate the professional advice you were given from the previous year). The level of risk discovered should be roughly consistent with the year before or be declining over time.
If you do not have years of audits to define your baselines it is a good practice to start with have two or more separate auditors to confirm findings. - Have set and clear objectives of what you want to achieve from an audit.
Having set and clear objective for what you want to achieve, minimises the risk of a breach happening outside the scope of your audit. By setting clear guidelines, the external auditor knows exactly what they need to cover. - Be selective with who you hire to perform the audits.
It is always tempting to try and cut costs by employing internal staff to complete audits. This is not recommended – outsiders are more likely to spot problems missed as they have not worked on the systems full time.
Technical audits identify risks to the technology platform by reviewing not only the policies and procedures, but also network and system configurations. Make sure auditors rely on experience, not just checklists. - Be transparent with business managers to ensure full compliance
On-boarding unit managers, for an audit, you can minimise the risk of compliance issues, should the auditors request specific information. Set ground rules in advance of the audit and prepare your company and organisation managers for the audit.
The purpose of audits is to get an accurate snapshot of your business as it is now it determine whether IT controls protect corporate assets, ensure data integrity and are aligned with the business's overall goals.
Future proof your business with an IT infrastructure upgrade
By Lanrex on 8/09/15 10:00 AM
Lanrex actively support and work with the SMB community in Australia and surrounds – namely PNG, Singapore and New Zealand.
We understand that many organisations are hesitant when it comes to investing in new technologies. While many organises believe that their current Infrastructure is working just fine, it has proven that holding on to the past can be quite costly to. Investing in new technologies are crucial to your organisation as a whole. If used correctly it maintains and improves business competitiveness.
 While the most commonly avoided change within an organisation is an IT infrastructure upgrade, a complete overhaul of ones networks can be well worth the investment with increasing efficiencies and capabilities with the whole organisation.
While the most commonly avoided change within an organisation is an IT infrastructure upgrade, a complete overhaul of ones networks can be well worth the investment with increasing efficiencies and capabilities with the whole organisation.
Usually the main driving forces often behind IT upgrades are business expansion and the need/ desire for virtualisation.
Understanding budget constraints and network needs are critical to the success of any upgrade. Discussing expectations up front will allow businesses to prioritise what and when they upgrade certain devices. When upgrading it is important to consider the follow to strengthen core functions with their IT upgrade.
Network.
Maintaining connections is critical to any business. Most business will reach a point where there is a need to move their computing technology to the next level. This could mean an upgrade to internal networking or investing in larger internet pipelines
Backup Internet
Today, most businesses business occurs over the internet, therefore maintaining an internet connection is crucial to bottom line. Multiple internet connection minimise the risk of complete network outages.
Investing in a backup modem can further guarantee you a connection, should you lose your main connection. A backup modem ensures alternate connectivity.
While back up modems may run slower than you primary connection it is a cheap way to secure business connectivity through an emergency.
Servers
Virtualisation can have immediate positive and measurable impacts on business overall functions and efficiency. Upgrading networks can keep your organization competitive and even ultimately save you money.
Almost all organisations will at some point start to have ‘growing pains’, when this occurs they will need an upgrade or to rebuild to stay competitive and profitable. By considering the tips above and speaking to a solutions provider, you can gain valuable in0depth knowledge and expertise on a wide range of topics that are available, that you may not have been aware off or get from a retailer.
Four reasons why your company’s revenue growth may be stalled.
By Lanrex on 1/09/15 12:00 PM
Business is a fickle thing, and if you aren’t growing, you’re going backwards. Harsh words, we know. But true all the same.
Often when company growth stalls, the blames falls on C-level executives or external forces – Economic downturn, government ruling or any other excuse.
After deeper analysis, we c an see that the most common causes for growth stalls are usually preventable (for the most part).
an see that the most common causes for growth stalls are usually preventable (for the most part).
In this article we will offer advice for avoiding some common pitfalls that halt business and revenue growth.
1 – Firm Unable/unwilling to respond to new, low cost products entering the market.
By far one of the biggest reasons company’s experience growth stalls is because of their inability to remain competitive with new lower cost products entering the market. Technology has been a huge force in driving the cost of goods and services down, and for companies that do not respond in a timely manner and/or fail to understand the emerging behaviour of their customers can have detrimental effects on the business.
Often companies whom are slow to adapt are slow because they have experienced solid market share for an extended amount of time, so they are insulated longer than other companies as they have less reason to believe that their strong position in the market in under threat as historically their business model has been reliable and proven competitive.
2 – No Innovation
The second most common cause of growth stalls is a lack of innovation. This is often the cause of a managerial breakdown of business processes in charge of updating products and services and creating new product lines.
Innovation can be; a lack of Research and development to poor product commercialisation.
A break down in innovation management may look like - an over allocation in smaller incremental product opportunities at the expense of sustained Research and Development investments in larger future product platforms.
A sustained and continued lack of innovation for business (big and small) can eventually produce major revenue stalls. There are some series clues when a company is at risk, the most evident is to see where R&D money is being spent, for example: Is some portion of innovation funding allocated to creating lower cost versions of existing products and services?
Granted that Innovation is a slow and often lengthy process, fatal flaws can often be slow to surface and extremely hard to remedy.
Business leaders should actively explore the potential of new product models to rejuvenate even the most “mature” product lines.
3 – Straying from Core business function.
The third major revenue staller for business is when business abandon their core business activities, without exploiting all growth opportunities in this area. This could be in the form of a merger or acquisition of another business that is not directly related to your business core function, customer base, product line or channel.
It is important for business to look at growth opportunities as markets change, but more importantly before devising your new next-level growth strategy, make sure that your current growth strategy is being adequately executed.
Often technologies can offer solace when seeking growth opportunities, diversification of business core functions can often lead to customer confusion and abandonment.
4- Out-dated technology
The fourth major staller of company revenue growths is often out-dated technology that is an inefficient use of your time. You may think that your technology works just fine, but you could be missing out on capabilities that fuel business success. A study by the Boston consulting group (BCG) found that companies that were technologically savvy grew 15 percent faster than technology laggards (they also created more jobs)
The right technology can boost business productivity and employee satisfaction (for more information on the importance of technology and attracting top talent)
Technology today allows companies to expand their business beyond geographical boundaries, it can keep company data safe and allow faster easier and more effective communication between customers and employees.
These are just four of the most common causes of growth stalls. Whatever concerns may arise during strategy discussions with higher management, growth stalls should be right at the top.
Lanrex offer tools to enable executive teams to continually monitor and test their accuracy and flag any flawed systems they jay have in place, which may trigger a stall in the future.
Are you a small to medium enterprise? Check out our free 7 series of IT Topics every SME needs to know below.
You might also like, Managed IT services give businesses better growth
How to access the hidden talent pool and improve employee engagement by leveraging technology
By Lanrex on 25/08/15 10:00 AM
As an owner of a Small to Medium sized business, it is understood you want to attract top talent to your business, too often we stress and wonder how can we compete with our big business competitors in attracting and sustaining our top talent candidates.
"A great culture provides the context for people to deliver their best work."
The good news - with today’s technology boom, SME are able to compete with big businesses like never before – as long as we are ‘on trend’ with technology. Studies have estimated that the financial impact of hiring a top performer is 10 – 100x the person’s compensation. Therefore, hiring a single top performer at $100,000 per annum salary has the potential for adding $1 million to $10 million to a company’s revenue each and every year that the new hire remains with the firm. (Adler, L 2012)
Employees today increasingly see the benefits of working for Start-ups and Small-Medium businesses. Amongst some of the benefits the most promising are - The ability for role flexibility, closer mentoring from Senior Executives and faster career progression prospects.
Technology has the capabilities to automate recruiting and staffing activities which can lead to improved candidate quality through stringent application processing, efficient hiring processes, increased workforce productivity, and importantly technology assists with better business performance.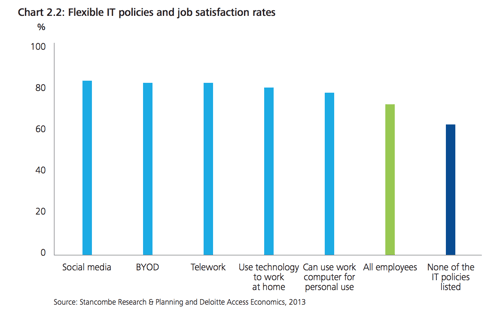
More than ever top candidates are quick to walk away from job opportunities that offer ‘awkward technology’ such as unclear processes and a disengaged working culture.
Managed IT Services - A Solution
With software solutions and applications having moved to a new model —software as a service (SaaS)—organisations of all sizes can take advantage of these sophisticated features and functions that were once upon a time only available to large enterprises.
SaaS technology can now be used as a foundation for several functions of the HR department. Corresponding costs and resources have now been removed from the equation, because the investment in infrastructure is no longer needed with Cloud Technologies—the internet is now the infrastructure.
Use Technology to CONNECT People, Places & Ideas
Employees like the fact that technology can be used to connect people, places, and ideas through meetings, events and interactive media. A study by CISCO showed that companies that have moved to flexible and mobile workplace strategies are seeing improvements in productivity and up to 20% in cost savings.
It is believed that companies which have a high degree of employee engagement have a 37% lower absenteeism rate than other companies, driving down costs and increasing profits.
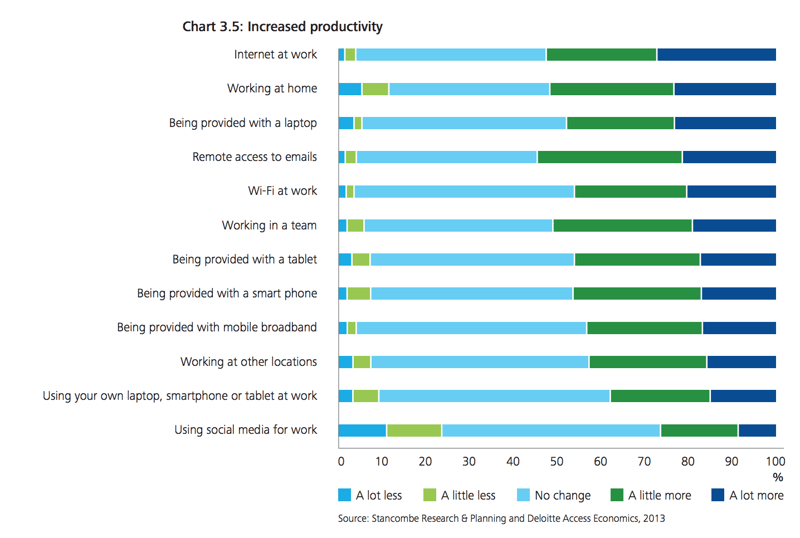
With workplace demographics changing – Employees are demanding more flexibility, mobility (work anywhere, anytime), the ability to easily collaborate with their team members and share information both internally and externally are all huge factors when top talent are deciding which job offer to take.
So what can I do for my small business IT support?
It is now easier than ever for SMB’s to compete with big business competitors by leveraging technology. SMB's can offer great benefits such as greater role flexibility, superior mentoring, additional promotions (praise) for good work and a strong technological infrastructure.
Find out how your business can leverage technology and increase your chances of attracting top talent.
Just remember, what can be measured can be improved.
Get in touch with the best IT support in Sydney today, to start leveraging technology to increase your employee engagement.
You might also like to see how one of our customers turned completely cloud!
4 Questions CEO’s should ask for the best technology position.
By Lanrex on 18/08/15 10:00 AM
The following article is designed to help CEO’s seamlessly merge business and technology discussion to produce winning results and be in the best technology position!
These four questions are designed to bring the ‘debate’ out of the tactical arena and move it more into a discussion about increased performance and driving innovation. These four questions shift the ‘technology discussion’ from ‘necessary cost’ to business capabilities.
Question 1 – Are we behind our competition?
We have seen over time that it is common for leadership teams in businesses to be unaware of how their technological capabilities (combination of business processes and supporting systems) fall in comparison to their competitors. A rigorous benchmarking of the businesses technology performance relative to competitors gives the CEO an opportunity to see where their investment budget is being consumed by ongoing maintenance and enhancements to sustain the status quo, rather than support new functionality.
While CEOs do not need to know all the ground level details of the companies IT, a totally hands off approach can lead to a poor review of the risks associated with serious competitive blind spots. Completing an annual review of IT capabilities including topics such as Operational basics, market intelligence on competitors of technology, analysis of competitive gaps that might affect the company’s market share and financial performance
Questions 2 – How can we leverage technology to change the ‘game’?
While some companies are enjoying a strong technological position today, tech-enabled competitors and new entrants are always preparing to strike. This is why it is important for Executives to know where technological threats are emerging and how they are best to respond or stay ahead of them.
Threats can come from a variety of sources, for example over the last 10 years some of the most influential threats have been the exponential growth of Social media, smart phones and other mobile devices, The ‘Internet of things enabling new level of automation and Cloud has allowed companies to become agile and scalable in an instance.
Another area that is seeing huge growth opportunities is ‘data’ – this is a growing focus for companies (and should be for your company), with the evolving nature of the way we interpret and analyse data it has the capacity to change the terrain of a business, creating competitive advantage for proprietary information.
Questions 3 – How can we implement strategies used by other industries, where can we learn?
Looking beyond your industry to proven technology leaders is always a good way to ‘shake up your thinking’. Whilst this may seem like an obvious and simple idea, many business leaders never venture out of their own industry for new technological insights and more importantly opportunities.
Seeking to understand what makes other businesses ‘tick’ is the foundation of strong innovation. Using companies that are unrelated to your business can prove to spur useful insights into improvements and business functionality.
Question 4 – How can we sustain a funnel and culture of change over time?
This question is more organisational specific and can be directly related to the company’s culture, Mannagement and competitive situation. Many CEOS have created a ‘mindset shift’ by including technology strategy as a core element in the business reviews of each division.
The radical changes taking place with technology today are creating more opportunities than ever before. These opportunities extend far further than ‘traditional IT’ and as a result of these increased opportunities available CEOs need to tackle technology today more than ever, rather than letting it ‘be someone else’s problem’, In order to step ahead of competition and become a market leader and ‘expert’ in their field CEOs need to pay more importance to how technology can impact the core business functions and leverage its transformative capabilities.
Enter Lanrex - Best Managed IT Services
At Lanrex we love technology and we love business, and we absolutely love when the two meet and work harmoniously together.
With over 30 years in the business we understand that as a CEO getting a handle on where to focus, and how much to invest on opportunities and threats is an increasingly frequent item on meeting agendas. The most challenging part is often ‘Where to start’.
In our experience CEOs need to jump into the technology discussions and shape the debate more which for most is often a difficult task.
What are you waiting for, contact Lanrex today!
3 Technology trends businesses are using to stay ahead of their competition.
By Lanrex on 11/08/15 11:30 AM
Technology is driving business today, and just as the right technology can drive businesses forward, increase profitability, decrease costs and maximise efficiencies, the wrong technology can quickly drive your business into the ground, the following article will look at three technology trends that can help your business stay competitive. 
- Good Design.
Every business knows the importance of a good design, good design can help improve bottom line. Well-designed technology can make every job easier- The jobs of employees and the jobs of customers purchasing goods online, over the phone or even in store making your business more effective.
Good example of well-designed technology driving business is Amazon with its one click shopping experience.
Perhaps the biggest barrier to innovation is knowing what it is that actually needs to be innovated upon. Insight into improving something that is already functional proves difficult and all too often is ignored by business owners, The ‘if it’s not broken, don’t fix it mentality’ - this could be hindering your business growth.
Considering the following three major points will open up more avenues to see where improvements can be made.
- Consideration 1 – Revenue –High level discussions need to take place to understand where your business will receive the greatest short-term financial value. For example: If most of the businesses revenue comes from upselling to existing customers, attention should on any innovations related to customer retention.
- Consideration 2- Numbers: Decide where these innovations could be benefitted most - Whether its customer facing or internal employee facing. Can you improve your highly repetitive systems so that you reduce digital fatigue, this will improve customer retention.
- Consideration 3- Line of Sight: Improving technologies around areas that you engage with the external environment, stakeholders, and current and potential customers such as campaigns, company website, Just-In-Time (JIT) stock control.
- Data Analytics
With the amount of data that is being created daily, analysing it all has become a fine art, and the masters of this art are reaping the benefits. Data driven insights go beyond google analytics. The most competitive businesses today combine internal and external data sources to follow trends, make better choices and lead them in a direction of growth, focus and strategic business thinking.
Data Analytics is less about relying on gut feeling decisions and more about piecing together seemingly unrelated information to formulate sound, informed decisions.
Data Analysis is a highly skilled exercise that involves extraordinary discipline, the best businesses use Data Analysis and the resulting insights to assist them in becoming impervious to the ups and down of business flows. When embarking on Data Analysis strategy remember these three important steps.
Step 1 – Capture- It is important to capture as much data as possible about your organisation.
Step 2 – Collaborate and warehouse- Over time you will acquire large databases of information, much of which will not ‘play well’ with other databases (meaning it will seem that all the data is unrelated). It is your job to collaborate and collate data when and where you can.
Warehousing data that has been analysed and turned into information so you can access it from a single source is ideal.
Step 3 – Calculate – Using members of your team (ideally, who are familiar with statistical analysis) increases your chances strongly of piecing together seemingly random parts of data to make astounding discoveries that can help your business innovate more and make informed decisions that address and tackle specific problems rather than treating symptoms, you ‘think’ you have.
Through calculations, you are able to hold tangible and visual evidence of where your business may have room for improvement, taken to management this type of evidence is irrefutable.
- Become a SaaS Business.
SaaS (aka Software as a Service) is a hot new term that lets you ‘Pay as you go’ service – pay companies subscription fees to rent their services, while this is a new digital term the thinking behind the service has been around for a number of years – Think Netflix and DVD rental.
The essence of SaaS is that companies allow your business to rent out tools (Software) they own, this leaves your business free from worry about the logistics of hosting, maintaining and troubleshooting these software tools. SaaS does not require an overhaul of the business model but you will need to employ a new way of business thinking. It is best practice to think about and follow these three parts:
Part 1 – Package – How is your business packaged to sell to its customers? Packing business products into segments of ‘value- adds’ is essential for customers to quickly assess the value of their purchase. An example of value adds is ‘Free Shipping’ or ‘Quick Delivery’.
Part 2 – Platform – SaaS encourages you to take on a greater load of customers, (usually requiring some sort of cloud software). With the automation and flexibility of your services you can manage more requests.
Part 3 - Process - With automated tasks you can ensure there is not wasted effort on servicing customers, you will be able to take on a higher customer load without having to increase employee labour costs – this increases efficiency.
By following these instructions literally and continuously you can take control over your business and innovation, increasing your competitive advantage, expanding capabilities and improving your overall business strategy.
If you're interested in learning more about the biggest technology trends affecting small businesses, click here to check out our tech trends infographic.
5 key things you need for a successful Sharepoint strategy
By Lanrex on 4/08/15 10:00 AM
SharePoint 2010 is rarely bought as a standalone software product, most often it is bundled in with a negotiated Microsoft Enterprise Agreement, for this reason many business leaders are left scratching their heads wondering – 'When should I use SharePoint? What should I use SharePoint for? When Shouldn’t I use SharePoint? And, what exactly is this additional extra I purchased?'
In this article we outline the 5 things you need for a successful SharePoint strategy:
- Define key business objectives
- Identify who the stakeholders are
- Determine whether the software have capabilities relevant to reaching your business objectives
- Integrate the software with your governance policy
- Identify and determine measures of success
 In the past we have seen a ‘technology first approach’ this means implement the new technology then gather the requirements and needs for the technology later, this type of approach can often lead to displeasing and unsatisfying results in usage, engagement and efficiency.
In the past we have seen a ‘technology first approach’ this means implement the new technology then gather the requirements and needs for the technology later, this type of approach can often lead to displeasing and unsatisfying results in usage, engagement and efficiency.
SharePoint provides a vast number of capabilities that empower business users, SharePoint allows users to collaborate with each other, tag and rate content, self-publish, and develop their own solutions, but as we know with great pwoer, comes great responsibility - SharePoint needs to be managed carefully before it grows quickly out of control.
Like any software, SharePoint needs to be aligned to a strategy. One common mistake many SMB’s make is - SharePoint is the strategy, when in fact SharePoint should be used to align with your businesses existing strategy and its related areas such as HR, IT, Sales etc.
This may mean many organisations are now faced with a need to re-architect their SharePoint environments in a way that is more conducive to reaching the businesses goals and strategic objectives.
Do not fret, the following article will discuss how to develop a successful SharePoint strategy whether it is for a first time implementation or to re-align your software to ensure it is working toward reaching the business vision.
Your SharePoint strategy should include these five key components:
Define key Business objectives
As Lao Tzu once said – the journey of a thousand miles begins with one step, and the first step on the road to SharePoint success is developing a good understanding of your business objectives that you are trying to accomplish.
To increase the chances of a successful SharePoint implementation, key stakeholders need to work together to carefully address the key business objectives– it is important to remember that SharePoint should align with your key objectives and not the other way around.
An example of one Business objective may be
'Decrease amount of time spent on training and development of new starters through efficient Information sharing and training programs. Improving ‘Time to Talent’. Reducing our bottom line.'
Identify who the stakeholders are
Stakeholders are not only the decision makers in the business, when considering implementing new software such as SharePoint you need to consider all parties involved. Depending on your reason for implementing SharePoint your stakeholders will be different for each scenario. When you look to identify stakeholders, recognize that there are different types of stakeholders, all of whom should be included in the development of your solution strategy and the ongoing governance model.
An important note to remember is that users are critical to the ultimate success of your SharePoint solution, so do not be exclusive when considering the stakeholders in your strategy. It is important that the solution is easy to use and managed, does not disrupt the flow of work and does not aggravate the end users, otherwise adoption will be unsuccessful.
Determine whether the software have capabilities relevant to reaching your business objectives
The IT experts you have engaged (whether they be internal or an outsourced company) will need to be included when completing this section of your strategy. It is imperative that a thorough understanding of the features SharePoint offer is utilised at this time.
By knowing all the features and capabilities of SharePoint you are able to align the SharePoint software to your previously defined business objectives (Step 1)
Take the earlier example of your business objective.
Decrease amount of time spent on training and development of new starters through efficient Information sharing and training programs. Improving ‘Time to Talent’. Reducing our bottom line.
SharePoint can enhance this Business objective through a range of features
- The People and Expertise search – Allowing your new starters to find people within the business with the expertise they are looking to develop.
- Follow people, documents and tags – this gives them greater access and proximity to power enabling them to learn faster and from more developed and seasoned staff members.
- Search – Giving them the ability to ‘look-up’ information they need, when they need it, so they can learn ‘as you go’
- Activity feeds with ‘# hashtag’ features and ‘@ mentions’ – This helps with the search refinement and also with offering praise – (Tip: mentions and praise often encourage faster development.)
By using these features of SharePoint it has the ability to reduce the amount of training time each employee needs as they can now ‘Learn on the go’ and increases their output whilst still in the early stages of their employment. This effectively meets the needs and enhances the ability of the business to achieve their business objective.
*Any easy way to display this section of your plan is in table form, with your business objectives on the left hand side and on the right the SharePoint features that can assist in achieving these on the right
**If SharePoint features cannot enhance or enable your business to reach their objectives, you should not go ahead with implementation.
Integrate the software with your governance policy
The Governance section of our SharePoint strategic plan should be viewed as your company’s insurance policy.
When the SharePoint environment starts to expand and more sensitive data starts to be housed within it – you need to ensure you have the right team and policies in place to contain any potential disasters.
Governance is about supplying a task force that outlines and maintains all the ‘rules of the SharePoint environment’. They are used to provide a quality user experience and ensure any policy violations are dealt with and resolved quickly.
The governance committee should have clearly defined the rules and responsibilities. The SharePoint governance committee, are not only representatives from the business and IT sides of the organization, it should also include executives and organisational champions (Individuals regardless of their role within the business who act as role models)
Governance ensures that the solution system is aligned with the business objectives so that it continuously delivers business value. The governance section of your strategy plan clarifies your SharePoint usage, creates a structured framework to measure and manage the solution and outlines all policies, guidance and enforcement procedures.
Identify and determine measures of success
Defining measures of success is key to any new implementation strategy, this is the time when you test the value of your organisations investment. By setting clear lines and measures of success, a metrics program should be established so that you can demonstrate the solution is meeting the business objectives. A good metrics program includes both qualitative and quantitative measures that tie the SharePoint solution as directly possible (responsible) to the businesses successes.
Qualitative metrics can be uncovered from user feedback during any of the quality assurance testing and initial training and early stages of implementation
Quantitative costs can be measured with such defined guidelines as ‘Reduced Training costs for new starters.
To gain a deeper understanding the success of your It is always a good idea to canvass user stories and experiences that describe how using SharePoint tools (finding a person with an unknown skill, following individuals etc.) helped contribute to increased profitability, increased client output, or other metrics that are already reflected in the key performance measures for the organization.
Governance committees should continually document and measure metrics to demonstrate the extent to which their governing process is improving the overall SharePoint enterprise.
Disaster Recovery or Business Continuity? What's more important?
By Lanrex on 21/07/15 10:00 AM
There is no truer saying than ‘Failing to plan, is planning to fail’ when it comes to Disaster recovery and your business. Disaster Recovery is the Insurance of the IT world. IT is investing in something you hope you will never need.
What is the difference between Disaster Recovery & Business Continuity?
The following article will discuss the difference between Disaster Recovery and Business Continuity and also explain the equal importance of each and best methods of implementation.
%20is%20no%20longer%20an%20optional%20extra,%20having%20reliable%20IT%20is%20a%20fundamental%20component%20of%20any%20business%20strategy..png?width=439&name=IT%20disaster%20recover%20planning%20(and%20Business%20Continuity)%20is%20no%20longer%20an%20optional%20extra,%20having%20reliable%20IT%20is%20a%20fundamental%20component%20of%20any%20business%20strategy..png) Disaster recovery (DR) refers to your company’s ability to restore the data and applications that run your business, should a data centre, server or infrastructure become damaged/ destroyed or terminate.
Disaster recovery (DR) refers to your company’s ability to restore the data and applications that run your business, should a data centre, server or infrastructure become damaged/ destroyed or terminate.
Arguably one of the most important points when discussing disaster recovery is ‘How quickly, can we recover and restore the data?’
Business Continuity Planning (BCP) takes into consideration a broader scope of contributing factors, such as technology, people and processers to a business’s functionality. BCP is about getting your business up and running with minimal (if any downtime) should disaster strike.
Now that you know the difference between the two, it is important to put in place a holistic strategy that encompasses both DR and BCP.
The algorithm to align both your DR policy and your BCP policy should be the sum of: Your Company’s urgency for time to restore full function against your company’s budget available to fund protection.
In almost all cases, outsourcing to managed service providers to accomplish DR and BCP result in lower costs and usually higher performance –simply put : less waiting time for a lower cost.
IT disaster recover planning (and Business Continuity) is no longer an optional extra, having reliable IT is a fundamental component of any business strategy.
If you decide your organisations does not need third party Disaster Recovery insurance- you should ensure your plan has these vital dimensions.
Disaster Identification and Notification
- Detection
- Warning
- Communication
Disaster Preparation
- DR team : Responsibilities in the event of disaster
- Non-DR Team: Training of procedures in event of disaster
IT Service Analysis and Reactivation
- Service Identification
- Service Priority
- Service Risks
Recovery
- Procedures
Offsite Storage
- Portability
- Offsite backup and locations
Maintenance
- Testing and Updating Plan
- Synchronization: Making sure business continuity and Disaster Recovery plan are in synergy.
Management have overall responsibility for the creation of a Business Continuity plan. Managers need to fund, manage, review and maintain this critical business planning and functionality tool.
Best practice to keep these plans relevant include – Adoption, Regular Risk assessment checks on current IT infrastructure and review of plan with testing and evaluation.
When contemplating recovery strategies Managers will (should) be looking to strategize and implement the best options for efficient recovery from an event. (Hint: It is a good idea to get some strong ideas from Disaster Recovery vendors or other companies that specialise or have specific DR tools.)
Recovery plans should thoroughly document the businesses plans for relocating and recovering its critical business processes and data recovery based on your recovery time objectives (identified during the business impact analysis process.)
While all of this sounds very difficult and time consuming, Disaster recovery, Business continuity and Data Backup planning is done by many outsourced IT companies (and at a lower cost than trying to do it yourself)..
Remember 'a good plan implemented today is BETTER than a perfect plan implemented tomorrow.'
Do you want to calculate the cost a disaster may have on your business? Download our Free Disaster Recovery Calculator.
5 IT trends to pay attention to in the next 10 years.
By Lanrex on 14/07/15 10:00 AM
Technology is changing at an astronomical pace, and the adoption rate is even more impressive. Consider the fact that the worlds data amounts are doubling and the number of devices connected to the internet has reached nearly 12 billion. In this day and age if your website isn’t mobile phone friendly it won’t even show up in google

If you're interested in IT trends, check out our tech trends for small business infographic!
This article analyses 5 trends that have either grown in importance over the last 3-5 year and new emerging trends that have developed tremendous growth and traction all of which are predicted to be big business for the next decade.
1 and 2: Data and Advanced Analytics are two trends that have stormed the business world, offering a huge competitive advantage to organisations. These two trends need to be deeply embedded across functions and operations that enable managers to have a better basis for understanding markets and making business decisions.
Data and analytics as part of a new foundation for competitiveness. Global data volumes are doubling faster than ever before. The power of analytics is rising while costs are falling and data visualization, wireless communications, and cloud infrastructure are extending the power and reach of information, enabling businesses to access privileged information that was once unavailable – or available at a high cost.
The abundance of data from multiple touch points combined with new analytic tools, we see companies are getting better and better at customizing products and services through the creation of consumer microsegments.
3 and 4: Social technologies and the Social Matrix are becoming key component in organisational infrastructure, connecting employees, customers and suppliers like we have never seen before. Check out how Social networks can increase your businesses productivity for 20-25% (link to social networks increase productivity article) Social networks have become a business phenomenon changing the environment in which business is conducted. We have seen an increase with organisations taking on ‘distributed problem solving’, tapping the brain power of customers and experts for breakthrough thinking.
In Today’s day and age, social perceptions are one of the most pivotal factors when our customers are deciding on a product to purchase, no social engagement or following can be detrimental to your business.
5: Cloud – Everything is a service whilst not a ‘new’ trend, it is a trend that is taking off and causing major disruptions to the IT stratosphere. The cloud has the ability to deliver digital power at low cost and in small increments, is not only changing the profile of corporate IT departments but also helping to spawn a range of new business models by shifting the economics of “rent versus buy” trade-offs for companies and consumers.
Cloud is attractive because it allows investors to replace the big capital investments experienced with traditional IT with strategic and flexible incremental payment plans.
For more interesting articles on all topics IT, read our Lanrex Blog with weekly updates. Please feel free to leave a comment in the below section and tell us what you think we can do better and what you would like to learn more about.
TIP if you want to check how your site runs on google mobile: Run your site through the Mobile-Friendly Test (https://goo.gl/Zm0lgu)
6 things you should include in your backup policy
By Lanrex on 7/07/15 10:30 AM
When there is data there is a data backup policy, whether your company chooses to write everything down with pen and paper, you need to have some sort of back up policy in place, in order to recovery your data should something go wrong.
One of the most critical functions of any organisations is their ability to recover, restore and retrieve data that is lost/damaged/compromised. An organisation without data or the ability to protect its data faces serious issues with longevity and validity.
Considering the ever growing risk of cyber security threats that face all businesses today big and small, there is critical need for a well thought out, efficient, and reliable backup policy. Costs of data loss can range from $500-$50,000, and this doesn’t include lost productivity, sales, reputation and client goodwill that can be damaged when a company can’t operate or fulfil on its promises due to technical problems.
A backup policy is a pre-defined, set schedule whereby information from business applications such as Oracle, Microsoft SQL, email server databases and user files are copied to disk and/or tape to ensure data recoverability in the event of accidental data deletion, corrupted information or some kind of a system outage. The policies will typically have a default protection scheme for most of the servers in the environment, with additional policies for certain critical applications or data.
Simply put, data in any format should be regularly copied and archived for use in the event data recovery or restoration should become necessary. While this process sounds straightforward, many organisations today are not following through with these simple steps.
Here's the 6 things to include in your backup policy:
- Back up all mission-critical data during organisations off -peak hours this helps to avoid performance delays during office hours.
- All backups to be stored off-site, not be located at your businesses primary location. For example in the Cloud.
- Make sure all backups are encrypted (to protect data from falling into wrong hands.) (Your cloud vendor can ensure this for you)
- Only allow small number of trusted employee’s access to backups, this is a measure, to avoid unwanted intrusions.
- Ensure your Vendor (if you have one) offers 24×7 support, this is essential in case an incident occurs outside of normal business hours. Cyber-attacks are usually random
- Work with a reputable cloud vendor that has been properly vetted to ensure the security and accessibility of business data.
- Accidental deleting files / formatting drives
- Viruses and Malware
- Damage or loss of computers / Hard drives
- Power failures
- Fire/ Natural disasters.
A data backup policy will help your organisation determine, what information is backed up, when and how often. It describes how backups are administered and maintained, and details who is responsible for their management.
It is always best practice to have a designated team to run your business back-ups, these will be the employees or contractors you call on when you encounter a problem.
For more information on Data Back-ups and Disaster recovery read the Lanrex White paper on the difference between Disaster Recovery and Business Continuity, or continue reading our blog for more interesting articles.
3 simple ways to cut down your IT costs?
By Sarika Vatner on 30/06/15 11:00 AM
We all want to think we have put in place the best practices to support our organisation but sometimes just because systems appear to be working on the outside, behind the scenes the story could be very different.
Running inefficient technology, can be extremely costly in the longer term and it can also have terminal follow on effects to your business should something go wrong. Even though some may try, it's not possible to cut down your IT costs by simply letting your IT get old.
Most businesses are oblivious to mounting technology debt as the problems associated with it don't suddenly appear, but creep up over time. So you need to look out for the telltale signs that those IT quick fixes are no longer working.
Here are 3 simple ways to cut down your IT costs:
1. Upgrade your aging hardware
While this might sound a bit contradictory, hear me out for a minute - if you’re still using a generation 1 Macintosh PC or a 10-year-old backup system, the chances are, you're spending too much money keeping it up and running. The older your hardware, the slower it is, the more likely it is to develop faults, and the less likely it is to run modern software efficiently (if at all).
Older hardware is also often less energy-efficient and this will drive up power bills. Old hardware is also costlier to fix, due to sourcing of end of life replacement parts (if you can get them at all).
This doesn’t mean you need to buy new hardware every single year — best practice of a 3 to 5 year refresh is still valid in this instance.
Don’t make the mistake of thinking “it’s still working, so I can keep it forever”. As we learned last year when Windows XP ended support, trying to keep old machines running forever can be frighently expensive.
2. Audit all software licences
In business we often see staff coming and going, it is a good idea to conduct an audit of your company’s software licences and work out whether you’re actually making use of all that software and not paying for licences you’re not using.
 This is just as relevant for companies now using methods such as software-as-a-service (SaaS), which typically charges on a per-user, per-month basis. Even though costs can be relatively low, it can still add up over long periods of time and the number of redundant licences you are hosting. Make sure your taking advantage of the SaaS advantage of scalability and pay only for what you use.
This is just as relevant for companies now using methods such as software-as-a-service (SaaS), which typically charges on a per-user, per-month basis. Even though costs can be relatively low, it can still add up over long periods of time and the number of redundant licences you are hosting. Make sure your taking advantage of the SaaS advantage of scalability and pay only for what you use.
Through thorough auditing you may be able to increase profits my minimising costs and eliminating waste.
3. Update aging software
Upgrading your business' software is more than just an economic business decision. It is a matter of security, productivity, lower costs, and employee morale. Typically more recent versions of software are safer from security standpoint. By minimising risk of downtime caused by security threats it is possible for companies to increase productivity and employee morale, who may become frustrated with constant breaches due to outdated software. If you want to know exactly how to calculate the cost of downtime for your business - you can access our easy to use online calculator.
More cost benefits of upgraded software include:
- More streamlined software increasing productivity.
- Outdated software is expensive to maintain – Especially with SaaS such as Office 365 available today.
It’s not hard to cut the cost of technology. With small changes and modern technology, your business can start seeing cost savings today. Is your business spending money on outdated technology?
If you enjoyed this article and want to read more on the importance of auditing, you might also like …. Or feel
free to just browse our Blog Library, Leave a comment if there is anything you would like us to write about, or
just want to share your feelings on what you have read so far.
Should I outsource my IT to a Managed Service Provider?
By Lanrex on 8/11/14 11:00 AM
Running a small to medium-sized business is a constant juggle between getting the work in, getting it done and getting paid for it. Even for SMEs in the thick of the digital economy, the focus is (understandably) about doing core business, not on IT.
Which means once initial IT systems are set up, they often get looked at only when so mething goes wrong, or a new user joins the team. While this approach is fine as long as the headcount stays within the designed limits of the system, its reactive nature means that little thought is given to how IT can be used to stay competitive over time.
mething goes wrong, or a new user joins the team. While this approach is fine as long as the headcount stays within the designed limits of the system, its reactive nature means that little thought is given to how IT can be used to stay competitive over time.
Whether it's competitive developments in the IT marketplace, or the growth of a business, there comes a point when an SME needs to seriously look at its IT setup and make some calls about their 'next phase'.
So the obvious questions are, how do you know when you're at that point, and what are the options available?
Knowing when it's time to change
Stepping up to the next level of IT is a performance and competitive issue as much as a headcount one. The trick is being able to see whether you are suffering while you're 'living inside' your IT ecosystem. Simply growing out of the designed system size (either with the number of users or locations), is one obvious pointer. Here are a few others:
- Your IT is beginning to run slower, or slower than you'd like
- You're getting complaints from staff (or even worse, from customers!)
- You can't do things with your IT you'd like to be able to do
- A competitor is doing things you can't match, or better
- Problems occur that can’t be clearly explained
- Security and redundancy aren't sitting with best practice or compliance
As mentioned, it can be hard to tell whether you're ahead of or behind, but if you notice even one of these issues, chances are it'll need further looking at, and potentially an upgrade.
So what are the options?
Keep things just as they are
Holding out with what you've got is definitely the easiest and cheapest option. If your business runs close to the line you'll always want to consider it. Who knows? In the short term, it could be okay.
But do it for too long and those small recurring issues won't stay small. A continually patched-up IT setup will eventually hold a business back. Simply adding on users, and then more users to an already-straining system makes it slower and more failure prone for everyone. Over time, this 'technology debt' takes the business further from its goals by being more costly to fix – in terms of up-front expense and opportunity cost.
Furthermore, technology itself has become a key differentiator for many businesses. And as it's being continually improved upon, the systems and applications that once made your business competitive may be the things holding it back only a few of years down the line.
If whoever's managing your current IT is spending most of their time just keeping things running, you can be pretty sure that this reactive approach is not helping your business get ahead. The question is (and the answer's different for each business), how far is it leaving you behind?
Staffing up internally
If you already have internal IT staff, this might seem like a logical development. The advantages are that the IT function stays in-house, with someone always close by, and there's someone there with history of the current setup.
But to take the IT up to 'the next stage' may require completely re-looking at the way things are. From the systems and procedures themselves, to the approach taken toward them. Then you've got to ask yourself whether the current team are right for that, or do they need some help?
In all likelihood the latter will be the case. New staff will need to be added, whose specialisations complement the ones you already have. Only then will you have the full suite of skills needed – from the day-to-day operations through to the strategic and pro-active thinking.
In large companies with the critical mass to justify a full team working in-house, this is what would happen. However it’s a different question for growing SMEs – still at that awkward size where they need high-end IT in order to compete, but still find the cost (and the effort) of hiring prohibitive.
Outsourcing to an IT Managed Services provider
While staff mightn't work 'in-house', outsourcing your IT function can be the best solution for growing SMEs. It gives access to the full suite of skills that keeps a business 'IT competitive', without having to foot the bill for a full-time team.
Outsourcing also allows a business to draw on a managed service provider's experience. They should be already delivering best practice solutions to real-world challenges, so would have developed a standardised set of processes and systems that can be fine-tuned for an individual business's needs, rather than having to build them from scratch.
The right Managed Service provider should also be able to evaluate your IT needs based on your business goals, not just your current situation, so they can build a system that'll make you competitive and keep you there even as your business develops. TProviding the right IT support service
And because they can deliver performance, security and stability to your business now and for the future, you can confidently focus on doing business.
As for cost, outsourcing companies will work around your needs – whether you'd prefer the security and stability of a fixed monthly cost, or to pay by use. Either way, the long-term costs of using an IT Managed Service provider's proactive approach will be lower than if your business had remained reactive.
 A quick word about cloud computing
A quick word about cloud computing
Cloud computing is spoken about so much it'd be easy to think it was the solution to everything. And it can help some issues. However, just because it’s 'new' doesn't make moving to the cloud right answer for every business (it requires your network being up to scratch for starters). Like anything else in IT, there needs to be a strong, strategic case for using it – no matter who's suggesting it. Discover your cloud computing strategy with Lanrex today.
How to use technology to grow your business?
If you think your IT isn't doing what it should or could, speak to a managed IT service here in Sydney. As specialists in providing outsourced IT managed services for small to medium-sized businesses (generally from 20 to 150 staff), we're in a good position to help you find out where you are at, where you could be, and how much it would cost. And finding out won't cost you a cent.
You might also like:
Why IT Strategy should be part of your Business Strategy
By Lanrex on 12/09/14 9:00 AM
For many small to mid-sized businesses, the IT department is there to fix things when they break, or add new things just as they're needed. Having digital strategies as part of the planning process isn't deemed necessary.
To an extent you can see why. By going the 'quick fix' route there's often less of an up-front investment to make in time and money. And you'll more or less get what you've asked for.
But there's also a cost. By keeping your IT Strategy in the dark, you're also keeping them from setting up the best infrastructure for what's planned ahead. And when those quick fixes become permanent fixtures, problems can creep in as a business begins to incur a 'technology debt'.
The term 'technology debt' was originally coined to describe a quick-fix approach to developing computer code that ignored the big picture, to the long-term detriment of a project. The more the quick fixes were left unchecked, the more difficult and expensive it would be to pull back, look at the big picture and re-do things properly.
As such, technology debt works in exactly the same manner when looking at an IT system in its entirety. Particularly when a business experiences growth. Daisy chaining network switches is a common example. A little like multiple double adaptors for electricity, each additional switch fixes a short-term growth problem, but also impacts the overall operational efficiency of the network.
Are you incurring debt?
Most businesses are oblivious to mounting technology debt as the problems associated with it don't suddenly appear, but creep up over time. So you need to look out for the telltale signs that those IT quick fixes are no longer fixing:
- The more successful the business, the slower the systems seem to run.
- You want to add new functionality, but are told by IT it’s going to be a huge investment, take a long time or not be possible at all.
- Your competitors are offering products and services you’re unable to offer because of IT limitations.
- Your team has become frustrated and unhappy about IT.
Ironically, even the monetary cost of all the quick fixes can make a patchwork IT more expensive than one that's thought out for the long term. Which means you're down on both cost and performance.
To get things working the way you want, the technology you should choose, how you should use it and the network platform you need is 100% dependant on your business plan and digital strategy.
Want to know how your IT stacks up?
If you're wondering whether your current IT is helping or hurting your business strategy, have a chat to the team at Lanrex. As IT specialists for SMEs, we're in an excellent position to help you understand where your capabilities sit in the competitive landscape and how to best leverage technology.
Best thing is, finding out from the best IT support in sydney won't cost you a cent!
Contact Lanrex today!
Get Cloud ready, and avoid a storm of problems
By Lanrex on 8/08/14 1:00 PM
For many businesses, migrating their data to the cloud is seen as (or sold as) a silver bullet to their IT woes. It's not hard to see why. Precious data is consolidated on to up-to-date servers, allowing secure access with incredible flexibility and scalability.
But what if you migrate to the cloud, but things don't run nearly as fast as they should?
Blame the cloud!
It would be easy to blame the cloud itself. After all, that's where all the data's gone. But the cloud doesn’t operate in isolation. And anything that block or slows down access to data held there will be felt immediately.
That could of course mean your network. It should be 'cloud ready' before any migration takes place, so that you see the improvements in performance you (and your staff) are looking for.
No! Blame the….um…er…
The trouble is that it's not always easy to diagnose whether a network is cloud ready, and resolve any issues if it isn't. Without specialist diagnostic equipment, training and procedures, IT departments can only make educated guesses as to what’s holding things up.
The result is that there's a risk of spending up big trying to 'fix' things that have little or no impact on the desired outcomes.
So the problem doesn't go away, even though the money's spent.

No need to cast a dark shadow
The good news is that it doesn’t' have to be this way. Specialist IT consultants have the diagnostic tools and processes in place to find out what's wrong – and right – about a network, before committing money to fixing the problems.
They use monitoring software that produces facts, not guesswork, making them are far more able to correctly identify the Single Points Of Failure' (SPOFs) that impact network performance.
And once they've correctly identified the problem, they'll be able to develop clear strategies and executions to ensure the issues are correctly addressed – whether it's a switch or cabling issue, or optimising the MIS configuration, or a redundancy strategy – clearly laying out the risk and benefits each step of the way.
Put your staff on cloud nine
The advantage of getting an accurate 'big picture' view of your network before migrating to the cloud is that potential problems are dealt with before they occur.
Which means when you do head off to the cloud, everyone will be happy.
Find out more about the Cloud with our Cloud 101 Guide, free download below.
You might also like, Cloud Cloud Computing & Cloud Readiness, Are you Ready for the Future?
Enjoy the Benefits of Exceptional Performance –
All While Keeping Costs Down.





























![Lanrex's Biggest Tech Trends for Small Businesses in 2019 [INFOGRAPHIC]](https://www.lanrex.com.au/hubfs/Screen%20Shot%202018-12-18%20at%2011.23.23%20am.png)






















































































.png?width=1024&name=CAMPING%20WALKTHROUGHS%20NO.%206%20(1).png)